OWASP - Security Awareness Presentation for Bitcoin Wednesday Amsterdam
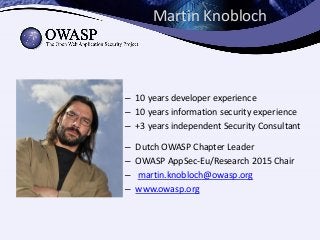
- 1. Martin Knobloch – 10 years developer experience – 10 years information security experience – +3 years independent Security Consultant – Dutch OWASP Chapter Leader – OWASP AppSec-Eu/Research 2015 Chair – martin.knobloch@owasp.org – www.owasp.org
- 4. Enter the rest of OWASP • Free Chapter Meetings • Free Local Events • Conferences • ... People • Webgoat • Zed Attack Proxy (ZAP) • ESAPI • ... Tools • Requirements list • CLASP • SAMM • ... Guides 6
- 5. Your security “perimeter” has huge holes at the application layer |7 Firewall Hardened OS Web Server App Server Firewall Databases LegacySystems WebServices Directories HumanResrcs Billing Custom Developed Application Code APPLICATION ATTACK You can’t use network layer protection (firewall, SSL, IDS, hardening) to stop or detect application layer attacks Network Layer Application Layer
- 6. 8 An Attacker has 24x7x365 to Attack Scheduled Pen-Test Scheduled Pen-Test Attacker Schedule The Defender has 20 man days per year to detect and defend
- 7. Tools – At Best 45% • MITRE found that all application security tool vendors’ claims put together cover only 45% of the known vulnerability types (695) • They found very little overlap between tools, so to get 45% you need them all (assuming their claims are true)
- 8. 10
- 9. Content
- 11. Insecure? Insecure? Functional Specification Technical Implementation An application is secure if it acts and reacts, as it expected, at any time! Secure
- 17. Threat Modeling – The Basics Asset: Valuable resource Vulnerability: Exploitable weakness Threat: Causes harm Risk: Chance of harm occurring ? Countermeasure: Reduces risk
- 18. Why start again? Asset Threat Risk is low Countermeasure Dependency Dependency’s Countermeasure Dependency’s Threat
