Infographic: Security for Mobile Service Providers
•
3 j'aime•4,612 vues
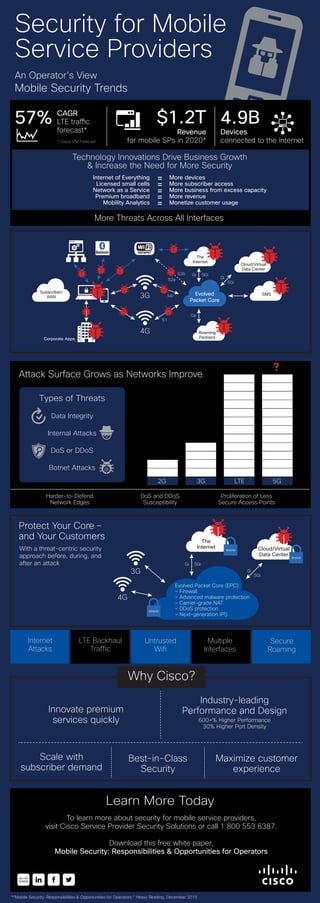
This infographic offers an operator's view on mobile security trends, such as the technology innovations driving business gowth and security threats. It also suggests how you can protect customers.
Signaler
Partager
Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
Contenu connexe
Tendances
Tendances (20)
Challenges and Solution to Mitigate the cyber-attack on Critical Infrastruct...

Challenges and Solution to Mitigate the cyber-attack on Critical Infrastruct...
eSentinel™ – 360° Cybersecurity Platform Simplified

eSentinel™ – 360° Cybersecurity Platform Simplified
Cyber Ethics: Cyber Security Services | VAPT and WAPT

Cyber Ethics: Cyber Security Services | VAPT and WAPT
Symantec Webinar | Implementing a Zero Trust Framework to Secure Modern Workf...

Symantec Webinar | Implementing a Zero Trust Framework to Secure Modern Workf...
Navigating the Zero Trust Journey for Today's Everywhere Workplace

Navigating the Zero Trust Journey for Today's Everywhere Workplace
Micro segmentation and zero trust for security and compliance - Guardicore an...

Micro segmentation and zero trust for security and compliance - Guardicore an...
Proteja sus datos en cualquier servicio Cloud y Web de forma unificada

Proteja sus datos en cualquier servicio Cloud y Web de forma unificada
En vedette
En vedette (14)
Cisco ISE Reduces the Attack Surface by Controlling Access

Cisco ISE Reduces the Attack Surface by Controlling Access
Identify Zero-Day Breaches with Cognitive Threat Analytics on Cisco Web Secur...

Identify Zero-Day Breaches with Cognitive Threat Analytics on Cisco Web Secur...
Defending the Data Center: Managing Users from the Edge to the Application

Defending the Data Center: Managing Users from the Edge to the Application
Inside NetQin Mobile Inc. (NYSE: NQ) - By iChinaStock

Inside NetQin Mobile Inc. (NYSE: NQ) - By iChinaStock
andrew milroy - top security trends and takeaways for 2013

andrew milroy - top security trends and takeaways for 2013
Similaire à Infographic: Security for Mobile Service Providers
Cisco Connect 2018 Thailand - Cisco SD-WAN next generation wan to power your ...

Cisco Connect 2018 Thailand - Cisco SD-WAN next generation wan to power your ...NetworkCollaborators
Similaire à Infographic: Security for Mobile Service Providers (20)
Transform your enterprise branch with secure sd-wan

Transform your enterprise branch with secure sd-wan
Security course: exclusive 5G SA pitfalls and new changes to legislation

Security course: exclusive 5G SA pitfalls and new changes to legislation
Scaling Mobile Network Security for LTE: A Multi-Layer Approach

Scaling Mobile Network Security for LTE: A Multi-Layer Approach
A Different Approach to Securing Your Cloud Journey

A Different Approach to Securing Your Cloud Journey
Cisco Connect 2018 Thailand - Cisco SD-WAN next generation wan to power your ...

Cisco Connect 2018 Thailand - Cisco SD-WAN next generation wan to power your ...
How to deal with the impact of digital transformation on networks 

How to deal with the impact of digital transformation on networks
Cisco Connect 2018 Malaysia - Secure data center and mobility solutions

Cisco Connect 2018 Malaysia - Secure data center and mobility solutions
WatchGuard: Bring Your Own Device or Bring Your Own Danger

WatchGuard: Bring Your Own Device or Bring Your Own Danger
SecurityGen's OSS/BSS Solutions: Navigating the Complexity of Modern Operations

SecurityGen's OSS/BSS Solutions: Navigating the Complexity of Modern Operations
Plus de Cisco Security
Plus de Cisco Security (16)
Incident Response Services Template - Cisco Security

Incident Response Services Template - Cisco Security
Infonetics Network and Content Security Vendor Scorecard

Infonetics Network and Content Security Vendor Scorecard
Gartner Newsletter: Cisco TrustSec Deployed Across Enterprise Campus, Branch ...

Gartner Newsletter: Cisco TrustSec Deployed Across Enterprise Campus, Branch ...
The Evolution of and Need for Secure Network Access

The Evolution of and Need for Secure Network Access
City of Tomorrow Builds in Next-Generation Security

City of Tomorrow Builds in Next-Generation Security
Laser Pioneer Secures Network End-to-End to Protect Assets

Laser Pioneer Secures Network End-to-End to Protect Assets
Leveraging Context-Aware Security to Safeguard Patient Data

Leveraging Context-Aware Security to Safeguard Patient Data
Secure, Automated Network Access for Any Device on Campus

Secure, Automated Network Access for Any Device on Campus
Dernier
Dernier (20)
Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365

Tech-Forward - Achieving Business Readiness For Copilot in Microsoft 365
Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...

Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...
Boost PC performance: How more available memory can improve productivity

Boost PC performance: How more available memory can improve productivity
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...

Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024

#StandardsGoals for 2024: What’s new for BISAC - Tech Forum 2024
Handwritten Text Recognition for manuscripts and early printed texts

Handwritten Text Recognition for manuscripts and early printed texts
Kalyanpur ) Call Girls in Lucknow Finest Escorts Service 🍸 8923113531 🎰 Avail...

Kalyanpur ) Call Girls in Lucknow Finest Escorts Service 🍸 8923113531 🎰 Avail...
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
Infographic: Security for Mobile Service Providers
- 1. Security for Mobile Service Providers An Operator’s View Mobile Security Trends Evolved Packet Core Roaming Partners SMS The Internet Cloud/Virtual Data Center 4G 3G Corporate Apps Subscriber/ RAN SGi Gi SGi Gi Gp S2b S2a lub S1 57% CAGR LTE traffic forecast* * Cisco VNI Forecast $1.2T Revenue for mobile SPs in 2020* 4.9B Devices connected to the internet More Threats Across All Interfaces 2G 3G LTE 5G ? Attack Surface Grows as Networks Improve More devices More subscriber access More business from excess capacity More revenue Monetize customer usage Internet of Everything Licensed small cells Network as a Service Premium broadband Mobility Analytics = = = = = Types of Threats Data Integrity Internal Attacks DoS or DDoS Botnet Attacks Harder-to-Defend Network Edges DoS and DDoS Susceptibility Proliferation of Less Secure Access Points 4G 3G Evolved Packet Core (EPC) - Firewall - Advanced malware protection - Carrier-grade NAT - DDoS protection - Next-generation IPS Cloud/Virtual Data Center SGi Gi SGi Gi www www The Internet www Protect Your Core – and Your Customers With a threat-centric security approach before, during, and after an attack Industry-leading Performance and Design 600+% Higher Performance 30% Higher Port Density Technology Innovations Drive Business Growth & Increase the Need for More Security Innovate premium services quickly Maximize customer experience Best-in-Class Security Scale with subscriber demand *“Mobile Security: Responsibilities & Opportunities for Operators,” Heavy Reading, December 2015 Learn More Today To learn more about security for mobile service providers, visit Cisco Service Provider Security Solutions or call 1 800 553 6387. Download this free white paper, Mobile Security: Responsibilities & Opportunities for Operators Why Cisco? Internet Attacks LTE Backhaul Traffic Untrusted Wifi Multiple Interfaces Secure Roaming
