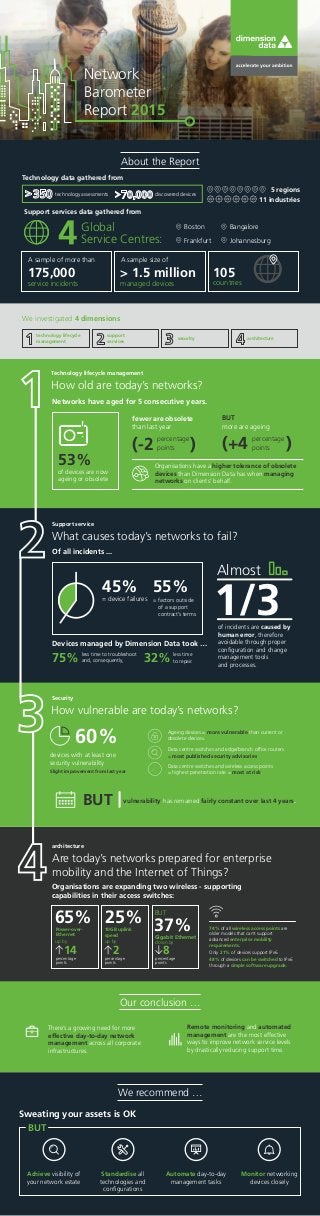
Network Barometer Report 2015 key findings
- 1. Our conclusion … We recommend … Ageing devices = more vulnerable than current or obsolete devices. Data centre switches and edge/branch office routers = most published security advisories. Data centre switches and wireless access points = highest penetration rate = most at risk. Network Barometer Report 2015 Technology data gathered from technology assessments discovered devices Boston Frankfurt Bangalore Johannesburg Support services data gathered from Global Service Centres: service incidents managed devices A sample of more than A sample size of 175,000 > 1.5 million countries 105 technology lifecycle management support services security architecture We investigated 4 dimensions About the Report 11 industries 5 regions Networks have aged for 5 consecutive years. of devices are now ageing or obsolete fewer are obsolete than last year BUT more are ageing 53% Organisations have a higher tolerance of obsolete devices than Dimension Data has when managing networks on clients’ behalf. (-2 ) percentage points )(+4 percentage points Technology lifecycle management Support service Security architecture How old are today’s networks? What causes today’s networks to fail? How vulnerable are today’s networks? Are today’s networks prepared for enterprise mobility and the Internet of Things? Of all incidents ... Devices managed by Dimension Data took … less time to repair.75% less time to troubleshoot and, consequently, 32% 55% = factors outside of a support contract’s terms = device failures 45% of incidents are caused by human error, therefore avoidable through proper configuration and change management tools and processes. Almost 1/3 60% BUT devices with at least one security vulnerability Slight improvement from last year vulnerability has remained fairly constant over last 4 years. Organisations are expanding two wireless - supporting capabilities in their access switches: 74% of all wireless access points are older models that can’t support advanced enterprise mobility requirements. Only 21% of devices support IPv6. 48% of devices can be switched to IPv6 through a simple software upgrade. 10GB uplink speed up by 2 25% percentage points up by Power-over- Ethernet 14 65% percentage points down by 8 Gigabit Ethernet BUT 37% percentage points Remote monitoring and automated management are the most effective ways to improve network service levels by drastically reducing support time. There’s a growing need for more effective day-to-day network management across all corporate infrastructures. Sweating your assets is OK Achieve visibility of your network estate Standardise all technologies and configurations Automate day-to-day management tasks Monitor networking devices closely BUT
