Consolidated Assessment and Action Items for Improving IT Security Across Hosted Systems
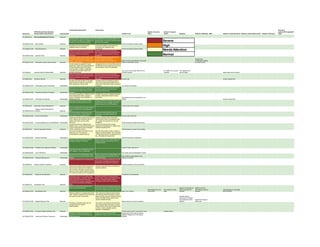
- 1. Consolidated Assessment Action Items General IT HIPAA Security Rule Standard Hosted in Security Hosted in Surgical systems(PCs/Laptops/M Section No. Implementation Specification Implementation Hosted in Lab Office Center Sleeplab Hosted in Radiology EMS Hosted in Computer Room Hosted in Internal Data Center Hosted in Pharmacy obile) 164.308(a)(1)(i) Security Management Process Required Company Name conducts regular security Consolidate all risk analysis reports into a risk analysis to analyze and mitigate risks shared folder. Continue to conduct annual involved in new technology adoption. technical risk analysis. Severe 164.308(a)(1)(ii)(A) Risk Analysis Required Vendor Supported Orchard system Identified risks are prioritized and mitigated based on exposure Ensure risk analysis action items are completed and update the plan High accordingly. 164.308(a)(1)(ii)(B) Risk Management Required Clearly documented sanction policy was Develop Company Name information Vendor Supported Orchard system Needs Attention not found. Need to be included as part of security policy which encompasses dept. 164.308(a)(1)(ii)(C) Sanction Policy Required master information security policy document sec. policies and general info. security guidelines. Normal Information system activity review is not Exception based reporting needs to be consistently happening on all key ePHI sent to department heads for Novarad has systems. Also need to be maintain logs of weekly/monthly review and sign-off Report could be generated to do periodic configuration settings 164.308(a)(1)(ii)(D) Information System Activity Review Required system activity review. review of information access to control access Security leads are assigned for each Designated Security Person/Roles Need to department. Roles and responsibilities of be Defined for each department and a key the security leads need to be clearly security officer need to be appointed. communicated. However, designated corporate security officer need to be Yes, Lynn is the security officer for LIS, Dr. Gatliff is the security Yes, Debbie is the 164.308(a)(2) Assigned Security Responsibility Required formally announced. Orchard Systems manager security officer Alaine takes care of security Clearly documented sanction policy was Develop Company Name information not found. Need to be included as part of security policy which encompasses dept. master information security policy sec. policies and general info. security 164.308(a)(3)(i) Workforce Security Required document guidelines. Security role Access request form - All users who have access to Company If remote users are accessing systems Name ePHI are onsite and supervised. other than business associates need to Didn't identify any remote users. ensure their information access procedure 164.308(a)(3)(ii)(A) Authorization and/or Supervision Addressable is secure. Yes, access is managed Confirmed by Company Name employees Revisit the hiring procedure and ensure that background checks and reference the latest criminal, court records are checks are done before actual hiring of examined before hiring. 164.308(a)(3)(ii)(B) Workforce Clearance Procedure Addressable workforce. Termination procedure is initiated by HR to Validate this process is diligently followed all the department heads. Access to for every employee/contractor access system is disabled once notification is termination. Terminated users are removed from the 164.308(a)(3)(ii)(C) Termination Procedures Addressable received from HR. system. Access request form - Need to be included as part of master Company Name information access policy information security policy document requires new hire's manager to provide access request to key HER systems. 164.308(a)(4)(i) Information Access Management Required Policies need to be reviewed This is not applicable as Company Name Isolation Health Clearinghouse doesn't process any outside agencies 164.308(a)(4)(ii)(A) Functions Required ePHI Almost all systems have granular level This access authorization process is user control which is implemented for managed by individual systems and 164.308(a)(4)(ii)(B) Access Authorization Addressable authorization and access to ePHI approvers. Security officer approves Clearly documented access policy was not Develop Company Name information found. Need to be included as part of security policy which encompasses dept. master information security policy sec. policies and general info. security 164.308(a)(4)(ii)(C) Access Establishment and Modification Addressable document guidelines. All lab processing people need access Though the training is happening at Conduct and log periodic security different levels, no documented evidences awareness training(online or offline) for all to show users/admins have undergone workforce handling ePHI 164.308(a)(5)(i) Security Awareness Training Required HIPAA awareness training. Training frequency need to be updated Structured reminders and alerts are not Security best practices video or article or being sent out. This could be training for all employees with a checklist compensated by periodic training of things that they are not supposed to do, etc., will satisfy this requirement 164.308(a)(5)(ii)(A) Security Reminders Addressable Security reminders is happening Kaseya remote management software Need to ensure this is implemented on all manages updated AV software laptops/desktops that handles ePHI for Company Name 164.308(a)(5)(ii)(B) Protection from Malicious Software Addressable Central IT team rolls out AV Only internal users are allowed to critical ePHI systems. This not applicable. 164.308(a)(5)(ii)(C) Log-in Monitoring Addressable Yes, report could be generated to review Password control is implemented using Need to ensure this is implemented on all Microsoft AD and individual ePHI system laptops/desktops that handles ePHI for Pwd. Profile is setup based on the 164.308(a)(5)(ii)(D) Password Management Addressable settings. Company Name settings in Orchard Incident procedures are not implemented This is an important requirement as OCR audit calls out specific procedures to be developed if any incident is suspected. 164.308(a)(6)(i) Security Incident Procedures Required Incident procedure to be documented Clearly documented incident procedures Develop a team(part-time) to handle any was not found. Need to be included as security incidents. part of master information security policy document. Also, training needs to include the incident procedures and management 164.308(a)(6)(ii) Response and Reporting Required Procedures to be developed Contingency plan is not in place locally Anything outside of Company Name's hosted applications. However, Company direct control need to be verified with the Name has outsourced lot of hosting vendors. Internally hosted systems' functionalities to business associates who contingency plan need to be updated. should have documented contingency 164.308(a)(7)(i) Contingency Plan Required plans. Backup for all key ePHI systems are in Ensure you account all backup tapes are place occurring periodically. accounted. Most of the breaches reporting Backup not required as Backed up to the is due to lost backup tape not encrypted. Data backed up in the Yes, backed up daily data is moved to CD Utah backup center of Data backed up in two tapes 164.308(a)(7)(ii)(A) Data Backup Plan Required Daily 3 a.m. backup main server twice regularly Novarad and encrypted Backups created on a regular basis will be This could be as simple as documenting used. However, disaster recovery planning that Company Name will switch to paper- and exercise need to take place. based records during the disaster recovery Desktop support period and offsite backup tapes will be outsourced to Cadwell used for disaster recovery. and replace the entire Tapes from Novarad 164.308(a)(7)(ii)(B) Disaster-Recovery Plan Required Backup tape to be used for restoring desktop will be sent. Emergency operations plans are not This could be as simple as documenting thought about and need to that Company Name will switch to paper- document/plan. based records during the emergency plan so that no need to specific security operation considerations. 164.308(a)(7)(ii)(C) Emergency Mode Operation Plan Required Printed copies of last 2 years will be used Printed records Stringent contingency planning is not However, for any internally hosted Backup tape will be used as backup applicable as most of the services are applications testing need to be conducted. validation happens thru' the backup 164.308(a)(7)(ii)(D) Testing and Revision Procedures Addressable hosted elsewhere. software
- 2. Applications and Data Criticality Key ePHI systems are identified in the Vendor support takes care of change 164.308(a)(7)(ii)(E) Analysis Addressable inventory sheet. management and analysis Next HIPAA assessment need to be scheduled somewhere around late spring Vendor is responsible for security 164.308(a)(8) Evaluation Required of 2013 evaluations Yes. Business Associate Contracts and Other Updated BA contracts need to be signed 164.308(b)(1) Arrangements Required with all vendors who're handling ePHI Need to be reviewed Novarad HealthEMS Risk assessment questionnaire need to be Ensure updated BA agreements is signed completed with key business associates with all business associates. With level 1 business associates please ensure risk assessment questionnaire is completed 164.308(b)(4) Written Contract Required and reviewed as well. Need to be reviewed Access is restricted only to key individuals Only handful assigned people have 164.310(a)(1) Facility Access Controls Required on reason to know basis. access to internally hosted systems. Only selected people Contingency plan to restore systems and applications will be primarily expected from business associates hosting IT systems 164.310(a)(2)(i) Contingency Operations Addressable Security office is working on updating the Ensure physical security policy is updated. 164.310(a)(2)(ii) Facility Security Plan Addressable security policy doc. Access Control and Validation Yes, this control is primarily managed by 164.310(a)(2)(iii) Procedures Addressable facility security and CIO. Access to the data center is restricted only to selected individuals who has the key. 164.310(a)(2)(iv) Maintenance Records Addressable So, this risk is not applicable. This is going to be included as part of Ensure physical security policy includes Pwd. Protection every 15 164.310(b) Workstation Use Required facility security policy. how to secure laptops/workstations. Central IT team manages desktop seconds is an issue Desktops/Laptops storing ePHI locally Consider laptop lock like Kensington or need to be protected with a physical Targus. 164.310( c ) Workstation Security Required security. Secured access External media usage is restricted. Though USB ports are locked there's still several other ways ePHI can be leaked. Ensure workforce is aware of the ePHI 164.310(d)(1) Device and Media Controls Required policy. Disposal of hard drives and other materials Need to ensure with Cogentes that the HD need to follow industry standards. degaussing or proper disposal procedures 164.310(d)(2)(i) Disposal Required are used. Reuse of hard disks and other data need Need to ensure with Cogentes that there's 164.310(d)(2)(ii) Media Reuse Required to follow industry standards. no media reuse Individuals are responsible for their workstation and admins are resp. for IT 164.310(d)(2)(iii) Accountability Addressable assets Proper backup procedures are being used before moving from one location to another 164.310(d)(2)(iv) Data Backup and Storage Addressable location Yes, being backed up on tape Access to ePHI is managed by multi-factor 164.312(a)(1) Access Control Required authentication. Access control in place All system users have individual account access 164.312(a)(2)(i) Unique User Identification Required Yes Emergency access procedure need to be Break-the-glass type of admin accounts developed required to manage emergency access procedures or printer paper record need to 164.312(a)(2)(ii) Emergency Access Procedure Required be used for emergency access. Yes Automatic timeout is not applicable everywhere as the timeout will enforce 164.312(a)(2)(iii) Automatic Logoff Addressable users to reenter the data. Yes, automatic logoff is enabled Data at rest and in transit is encrypted in Few areas we have requested the dept. most of the high risk areas heads to verify the data is encrypted. Once that verification is positive Company Name database and need to continuously monitor for application encrypted on 164.312(a)(2)(iv) Encryption and Decryption Addressable unencrypted data. Need to confirm with the vendor Macpractice Clear login information and logs are 164.312(b) Audit Controls Required generated by the systems. Yes Security controls and group level assignment ensures only the right people have access to the right info. To maintain 164.312( c)(1) Integrity Required integrity. Yes, thru' security control The key ePHI systems leverages leading Mechanism to Authenticate Electronic authentication process to provide access Security admin role is Different users have 164.312( c)(2) Protected Health Information Addressable to ePHI Not applicable here. used for staff different level of access Two factor authentication is used to provide access to ePHI Orchard centralized control and web 164.312(d) Person or Entity Authentication Required portal All transmitted data to outside the agency use https or other secure protocol to 164.312(e)(1) Transmission Security Required transmit the data IT question All transmitted data to outside the agency use https or other secure protocol to 164.312(e)(2)(i) Integrity Controls Addressable transmit the data Local access or secured web access Data is encrypted at rest by the vendors 164.312(e)(2)(ii) Encryption Addressable Check with Vendor Backup Disks(CD) need to be encrypted