OCR HHS HIPAA HITECH Audit Advisory Template
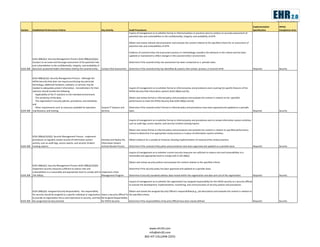
- 1. The New Trend in Healthcare IT Implementation HIPAA Section Established Performance Criteria Key Activity Audit Procedures Specification Compliance Area Inquire of management as to whether formal or informal policies or practices exist to conduct an accurate assessment of potential risks and vulnerabilities to the confidentiality, integrity, and availability of ePHI. Obtain and review relevant documentation and evaluate the content relative to the specified criteria for an assessment of potential risks and vulnerabilities of ePHI. Evidence of covered entity risk assessment process or methodology considers the elements in the criteria and has been updated or maintained to reflect changes in the covered entity's environment. §164.308(a)(1): Security Management Process §164.308(a)(1)(ii)(a) - Conduct an accurate and thorough assessment of the potential risks Determine if the covered entity risk assessment has been conducted on a periodic basis. and vulnerabilities to the confidentiality, integrity, and availability of §164.308 electronic protected health information held by the covered entity. Conduct Risk Assessment Determine if the covered entity has identified all systems that contain, process, or transmit ePHI. Required Security §164.308(a)(1)(i): Security Management Process - Although the HIPAA Security Rule does not require purchasing any particular technology, additional hardware, software, or services may be needed to adequately protect information. Considerations for their Inquire of management as to whether formal or informal policy and procedures exist covering the specific features of the selection should include the following: HIPAA Security Rule information systems §164.306(a) and (b). -Applicability of the IT solutions to the intended environment; -The sensitivity of the data; Obtain and review formal or informal policy and procedures and evaluate the content in relation to the specified -The organization's security policies, procedures, and standards; performance to meet the HIPAA Security Rule §164.306(a) and (b). and -Other requirements such as resources available for operation, Acquire IT Systems and Determine if the covered entity's formal or informal policy and procedures have been approved and updated on a periodic §164.308 maintenance, and training. Services basis. Required Security Inquire of management as to whether formal or informal policy and procedures exist to review information system activities; such as audit logs, access reports, and security incident tracking reports. Obtain and review formal or informal policy and procedures and evaluate the content in relation to specified performance criteria to determine if an appropriate review process is in place of information system activities. §164.308(a)(1)(ii)(D): Security Management Process - Implement procedures to regularly review records of information system Develop and Deploy the Obtain evidence for a sample of instances showing implementation of covered entity review practices activity, such as audit logs, access reports, and security incident Information System §164.308 tracking reports. Activity Review Process Determine if the covered entity policy and procedures have been approved and updated on a periodic basis. Required Security Inquire of management as to whether current security measures are sufficient to reduce risks and vulnerabilities to a reasonable and appropriate level to comply with § 164.306(a). Obtain and review security policies and evaluate the content relative to the specified criteria. §164.308(a)(1): Security Management Process §164.308(a)(1)(ii)(b) - Implement security measures sufficient to reduce risks and Determine if the security policy has been approved and updated on a periodic basis. vulnerabilities to a reasonable and appropriate level to comply with § Implement a Risk §164.308 164.306(a). Management Program Determine if security standards address data moved within the organization and data sent out of the organization. Required Security Inquire of management as to whether the organization has assigned responsibility for the HIPAA security to a Security Official to oversee the development, implementation, monitoring, and communication of security policies and procedures. §164.308(a)(2): Assigned Security Responsibility - the responsibility Obtain and review the assigned Security Official's responsibilities(e.g., job description) and evaluate the content in relation to for security should be assigned to a specific individual or organization Select a Security Official To the specified criteria. to provide an organization focus and importance to security, and that Be Assigned Responsibility §164.308 the assignment be documented. for HIPAA Security Determine if the responsibilities of Security Official have been clearly defined. Required Security www.ehr20.com info@ehr20.com 802-HIT-CALL(448-2255)