ATUS - A Toolkit for Usable Security
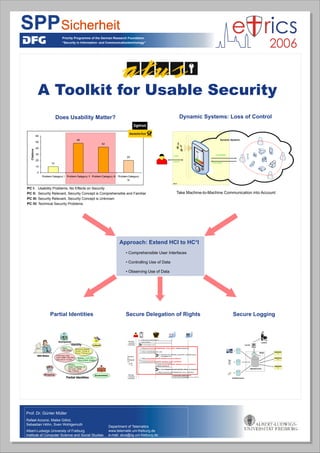
With the increasing use of information and communication technology (ICT) and the transformation of economic activities in computer networks, IT security is becoming more and more important. The use of secure IT systems are the basis for a user to protect his privacy, i.e. his right to informational self-determination. However, users can only work safely, secure, and protect their privacy, when the ICT systems are usable according to the user's expertise and preferences. The team ATUS (A Toolkit for Usable Security) argues that security and usability needs to be extended from HCI to HCI+ with comprehensive user interfaces and security mechanims for control and transparency of personal data processing. Identity management as a security application assists users in enforcing their balanced security requirements. It allows a context-dependent actions under different roles. The project team ATUS presents with the iManager a prototype for identity management on a mobile personal device of the user.
Recommended
Recommended
More Related Content
Similar to ATUS - A Toolkit for Usable Security
Similar to ATUS - A Toolkit for Usable Security (20)
More from Sven Wohlgemuth
More from Sven Wohlgemuth (20)
Recently uploaded
Recently uploaded (20)
ATUS - A Toolkit for Usable Security
- 1. Priority Programme of the German Research Foundation “Security in Information- and Communicationtechnology” 10 48 42 20 0 10 20 30 40 50 60 Problem Category I Problem Category II Problem Category III Problem Category IV Citations Prof. Dr. Günter Müller Rafael Accorsi, Maike Gilliot, Sebastian Höhn, Sven Wohlgemuth Albert-Ludwigs University of Freiburg Institute of Computer Science and Social Studies A Toolkit for Usable Security Department of Telematics www.telematik.uni-freiburg.de e-mail: atus@iig.uni-freiburg.de Secure Delegation of RightsPartial Identities HC+I control Dynamic Systems Controllability Observability observe Does Usability Matter? Dynamic Systems: Loss of Control Take Machine-to-Machine Communication into Account • Comprehensible User Interfaces • Controlling Use of Data • Observing Use of Data Approach: Extend HCI to HC+I PC I: Usability Problems, No Effects on Security PC II: Security Relevant, Security Concept is Comprehensible and Familiar PC III: Security Relevant, Security Concept is Unknown PC IV: Technical Security Problems Secure Logging 13: Show one-show credential(attributes, proxy, restrictions) 12: Request patents, establish pseudonym12: Request patents, establish pseudonym 9: Show proxyCredential(TID, attributes, proxy, restrictions), establish pseudonym 11: Return one-show credential(attributes, proxy, restrictions) 10: Verify delegation(proxyCredential, policy), log delegation 4: Request proxyCredential(attributes, proxy, policy), establish pseudonym 5: Show credential(attributes, user) 7: Return proxyCredential(TID, attributes, proxy, restrictions) 8: Forward proxyCredential(TID, attributes, proxy, restrictions) 2: Query for attributes 3: Decide delegation request 1: Request patents, establish pseudonym iManager + anonyme Credentials Alternative zur Weitergabe von kMaxkMax 6: Add entry (TID, attributes, pseudonym, credential, policy) to delegation list iManager + anonyme Credentials