2014 ieee project dotnet titles
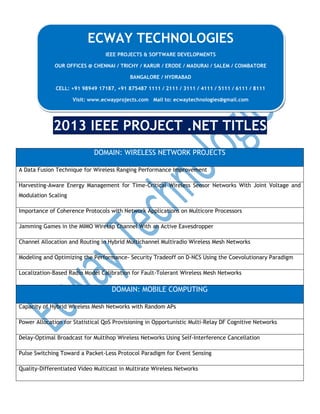
- 1. ECWAY TECHNOLOGIES IEEE PROJECTS & SOFTWARE DEVELOPMENTS OUR OFFICES @ CHENNAI / TRICHY / KARUR / ERODE / MADURAI / SALEM / COIMBATORE BANGALORE / HYDRABAD CELL: +91 98949 17187, +91 875487 1111 / 2111 / 3111 / 4111 / 5111 / 6111 / 8111 Visit: www.ecwayprojects.com Mail to: ecwaytechnologies@gmail.com 2013 IEEE PROJECT .NET TITLES DOMAIN: WIRELESS NETWORK PROJECTS A Data Fusion Technique for Wireless Ranging Performance Improvement Harvesting-Aware Energy Management for Time-Critical Wireless Sensor Networks With Joint Voltage and Modulation Scaling Importance of Coherence Protocols with Network Applications on Multicore Processors Jamming Games in the MIMO Wiretap Channel With an Active Eavesdropper Channel Allocation and Routing in Hybrid Multichannel Multiradio Wireless Mesh Networks Modeling and Optimizing the Performance- Security Tradeoff on D-NCS Using the Coevolutionary Paradigm Localization-Based Radio Model Calibration for Fault-Tolerant Wireless Mesh Networks DOMAIN: MOBILE COMPUTING Capacity of Hybrid Wireless Mesh Networks with Random APs Power Allocation for Statistical QoS Provisioning in Opportunistic Multi-Relay DF Cognitive Networks Delay-Optimal Broadcast for Multihop Wireless Networks Using Self-Interference Cancellation Pulse Switching Toward a Packet-Less Protocol Paradigm for Event Sensing Quality-Differentiated Video Multicast in Multirate Wireless Networks
- 2. Evaluating Temporal Robustness of Mobile Networks SinkTrail A Proactive Data Reporting Protocol for Wireless Sensor Networks Target Tracking and Mobile Sensor Navigation in Wireless Sensor Networks A Resource Allocation Scheme for Scalable Video Multicast in WiMAX Relay Networks Toward Privacy Preserving and Collusion Resistance in a Location Proof Updating System SSD: A Robust RF Location Fingerprint Addressing Mobile Devices’ Heterogeneity An Investigation on LTE Mobility Management On Exploiting Transient Social Contact Patterns for Data Forwarding in Delay-Tolerant Networks On the Real-Time Hardware Implementation Feasibility of Joint Radio Resource Management Policies for Heterogeneous Wireless Networks Simple Hybrid and Incremental Postpruning Techniques for Rule Induction Supporting Search-As-You-Type Using SQL in Databases Reinforced Similarity Integration in Image-Rich Information Networks Autonomous Sensing Order Selection Strategies Exploiting Channel Access Information Mobile Relay Configuration in Data-Intensive Wireless Sensor Networks Toward a Statistical Framework for Source Anonymity in Sensor Networks On Centralized and Localized Approximation Algorithms for Interference-Aware Broadcast Scheduling Model-Based Analysis of Wireless System Architectures for Real-Time Applications Successive Interference Cancellation: Carving Out MAC Layer Opportunities Vampire Attacks: Draining Life from Wireless Ad Hoc Sensor Networks Group-Based Medium Access Control for IEEE 802.11n Wireless LANs Discovery and Verification of Neighbor Positions in Mobile Ad Hoc Networks A Secure Payment Scheme with Low Communication and Processing Overhead for Multihop Wireless Networks
- 3. A Scalable Server Architecture for Mobile Presence Services in Social Network Applications Secure Communication Based on Ambient Audio Successive Interference Cancellation: Carving Out MAC Layer Opportunities Cross-Layer Design of Congestion Control and Power Control in Fast-Fading Wireless Networks Coloring-Based Inter-WBAN Scheduling for Mobile Wireless Body Area Networks Cluster-Based Certificate Revocation with Vindication Capability for Mobile Ad Hoc Networks Analysis of Distance-Based Location Management in Wireless Communication Networks Gaussian versus Uniform Distribution for Intrusion Detection in Wireless Sensor Networks Fast Channel Zapping with Destination-Oriented Multicast for IP Video Delivery Exploiting Ubiquitous Data Collection for Mobile Users in Wireless Sensor Networks Dynamic Coverage of Mobile Sensor Networks In-Network Estimation with Delay Constraints in Wireless Sensor Networks Microarchitecture of a Coarse-Grain Out-of-Order Superscalar Processor Jamming Games in the MIMO Wiretap Channel With an Active Eavesdropper IDM: An Indirect Dissemination Mechanism for Spatial Voice Interaction in Networked Virtual Environments EMAP Expedite Message Authentication Protocol for Vehicular Ad Hoc Networks Channel Assignment for Throughput Optimization in Multichannel Multiradio Wireless Mesh Networks Using Network Coding Receiver-Driven Adaptive Enhancement Layer Switching Algorithm for Scalable Video Transmission Over Link-adaptive Networks DOMAIN: NETWORK SECURITY PROJECTS Distance Bounding A Practical Security Solution for Real-Time Location Systems EAACK—A Secure Intrusion-Detection System for MANETs
- 4. Security Analysis of a Single Sign-On Mechanism for Distributed Computer Networks DOMAIN: DATA MINING (Data Engineering) Ontology Matching: State of the Art and Future Challenges A Fast Clustering-Based Feature Subset Selection Algorithm for High-Dimensional Data A System to Filter Unwanted Messages from OSN User Walls A Survey of XML Tree Patterns Automatic Semantic Content Extraction in Videos Using a Fuzzy Ontology and Rule-Based Model Distributed Processing of Probabilistic Top-k Queries in Wireless Sensor Networks Distributed Web Systems Performance Forecasting Using Turning Bands Method Evaluating Data Reliability An Evidential Answer with Application to a Web-Enabled Data Warehouse Maximum Likelihood Estimation from Uncertain Data in the Belief Function Framework Ranking on Data Manifold with Sink Points Region-Based Foldings in Process Discovery Relationships between Diversity of Classification Ensembles and Single-Class Performance Measures T-Drive Enhancing Driving Directions with Taxi Drivers’ Intelligence The Generalization Ability of Online Algorithms for Dependent Data Clustering Sentence-Level Text Using a Novel Fuzzy Relational Clustering Algorithm A Graph-Based Consensus Maximization Approach for Combining Multiple Supervised and Unsupervised Models Large Graph Analysis in the GMine System Nonadaptive Mastermind Algorithms for String and Vector Databases, with Case Studies A Rough-Set-Based Incremental Approach for Updating Approximations under Dynamic Maintenance Environments
- 5. A Proxy-Based Approach to Continuous Location-Based Spatial Queries in Mobile Environments A Generalized Flow-Based Method for Analysis of Implicit Relationships on Wikipedia AML: Efficient Approximate Membership Localization within a Web-Based Join Framework Event Tracking for Real-Time Unaware Sensitivity Analysis Detecting Intrinsic Loops Underlying Data Manifold Clustering Large Probabilistic Graphs Anonymization of Centralized and Distributed Social Networks by Sequential Clustering Minimally Supervised Novel Relation Extraction Using a Latent Relational Mapping Finding Rare Classes: Active Learning with Generative and Discriminative Models Fast Activity Detection: Indexing for Temporal Stochastic Automaton-Based Activity Models DOMAIN: CLOUD COMPUTING QoS Ranking Prediction for Cloud Services Scalable and Secure Sharing of Personal Health Records in Cloud Computing Using Attribute-Based Encryption Mona: Secure Multi-Owner Data Sharing for Dynamic Groups in the Cloud On Data Staging Algorithms for Shared Data Accesses in Clouds Optimal Multiserver Configuration for Profit Maximization in Cloud Computing DOMAIN: PARALLEL & DISTRIBUTED COMPUTING Network Traffic Classification Using Correlation Information Scalable and Secure Sharing of Personal Health Records in Cloud Computing Using Attribute-Based Encryption Adaptive Network Coding for Broadband Wireless Access Networks Detection and Localization of Multiple Spoofing Attackers in Wireless Networks
- 6. Online Real-Time Task Scheduling in Heterogeneous Multicore System-on-a-Chip MIN-MAX: A Counter-Based Algorithm for Regular Expression Matching Binary Tree Slotted ALOHA for Passive RFID Tag Anticollision Covering Points of Interest with Mobile Sensors Topology Abstraction Service for IP-VPNs Thermal and Energy Management of High-Performance Multicores: Distributed and Self-Calibrating ModelPredictive Controller High Performance Resource Allocation Strategies for Computational Economies Strategies for Energy-Efficient Resource Management of Hybrid Programming Models DOMAIN: MULTIMEDIA & IMAGE PROCESSING Mining Semantic Context Information for Intelligent Video Surveillance of Traffic Scenes An Access Point-Based FEC Mechanism for Video Transmission Over Wireless LANs Interactive Segmentation for Change Detection in Multispectral Remote-Sensing Images Reversible Data Hiding With Optimal Value Transfer Query-Adaptive Image Search With Hash Codes Reversible Watermarking Based on Invariant Image Classification and Dynamic Histogram Shifting Noise Reduction Based on Partial-Reference, Dual-Tree Complex Wavelet Transform Shrinkage LDFT-Based Watermarking Resilient to Local Desynchronization Attacks Image Size Invariant Visual Cryptography for General Access Structures Subject to Display Quality Constraints Secure Watermarking for Multimedia Content Protection: A Review of its Benefits and Open Issues Robust Face Recognition for Uncontrolled Pose and Illumination Changes