Microsoft Intune y Gestión de Identidad Corporativa
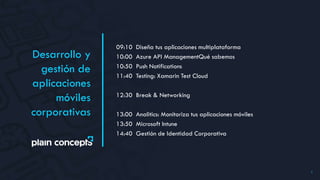
- 1. 1 09:10 Diseña tus aplicaciones multiplataforma 10:00 Azure API ManagementQué sabemos 10:50 Push Notifications 11:40 Testing: Xamarin Test Cloud 12:30 Break & Networking 13:00 Analitics: Monitoriza tus aplicaciones móviles 13:50 Microsoft Intune 14:40 Gestión de Identidad Corporativa Desarrollo y gestión de aplicaciones móviles corporativas
- 2. INTUNE (EMS) José María Genzor jmgenzor@plainconcepts.com Enterprise Team lead Enterprise Mobility + Security
- 3. Go mobile. Stay in control. José María Genzor Enterprise Team lead Enterprise Mobility + Security
- 4. Enterprise Mobility + Security Basic identity mgmt. via Azure AD for O365: • Single sign-on for O365 • Basic multi-factor authentication (MFA) for O365 Basic mobile device management via MDM for O365 • Device settings management • Selective wipe • Built into O365 management console RMS protection via RMS for O365 • Protection for content stored in Office (on-premises or O365) • Access to RMS SDK • Bring your own key Azure AD for O365+ • Advanced security reports • Single sign-on for all apps • Advanced MFA • Self-service group management & password reset & write back to on- premises, • Dynamic Groups, Group based licensing assignment MDM for O365+ • PC management • Mobile app management (prevent cut/copy/paste/save as from corporate apps to personal apps) • Secure content viewers • Certificate provisioning • System Center integration RMS for O365+ • Automated intelligent classification and labeling of data • Tracking and notifications for shared documents • Protection for on-premises Windows Server file shares Advanced Security Management • Insights into suspicious activity in Office 365 Cloud App Security • Visibility and control for all cloud apps Advanced Threat Analytics • Identify advanced threats in on premises identities Azure AD Premium P2 • Risk based conditional access Information protection Identity-driven security Managed mobile productivity Identity and access management
- 5. Mobile-first, cloud-first reality Data breaches 63% of confirmed data breaches involve weak, default, or stolen passwords. 63% 0.6% IT Budget growth Gartner predicts global IT spend will grow only 0.6% in 2016. Shadow IT More than 80 percent of employees admit to using non-approved software as a service (SaaS) applications in their jobs. 80%
- 6. Is it possible to keep up? Employees Business partners Customers Is it possible to stay secure? Apps Devices Data Users Data leaks Lost device Compromised identity Stolen credentials
- 7. Is it possible to keep up? Employees Business partners Customers The Microsoft vision Secure and protect against new threats Maximum productivity experience Comprehensive and integrated Apps Devices Data Users
- 8. Protect your data Enable your users Unify Your Environment Devices Apps Data Help organizations enable their users to be productive on the devices they love while helping ensure corporate assets are secure
- 9. Manage mobile productivity and protect data with Office Mobile apps for iOS and Android Manage policy for existing iOS line of business apps (so called “app wrapping”) Managed browser and PDF/Audio/Video viewers Provide access to Exchange and OneDrive for Business resources only to managed devices Deny access if a device falls out of compliance Enable IT to bulk enroll corporate-owned task-worker devices Support for Apple Configurator Manage mobile productivity without compromising compliance Conditional Access Policy to Email and Documents Enroll and Manage Corporate-owned Devices Manage Mobile Productivity and Protect Data with Office Personal Corporate
- 12. Layer 2 – Application and data containers (aka “managed mobile productivity”) Protects corporate data by… Gaps it leaves open Preventing apps from sharing data with other apps outside of IT control Preventing apps from saving data to stores outside of IT control Encrypting app data to supplement device encryption Only protects corporate data that resides on devices. Cannot protect data beyond a device. Applies same protection to all data that an app touches. Does not allow for specific protection per document. Layer 3 – Data wrapping Protects corporate data by… Gaps it leaves open Protecting data wherever it resides Providing granular, content specific protection – e.g. time bomb vision docs Requires enlightened applications Requires all data to be protected if not complemented by Layers 1 and 2 Native E-mail Managed Browser LoB Layer 1 – Mobile device lockdown via MDM Protects corporate data by… Gaps it leaves open Restricting device behaviors: PIN, encryption, wipe, disable screen capture and cloud backup, track compliance, etc. Provisioning credentials that enable corporate resource access control Apps may share corporate data with other apps outside IT control Apps may save corporate data to consumer cloud services LoB
- 14. Enterprise Mobility Lifecycle Manage and Protect Measure device and app compliance Block access if policy violated (eg: jailbreak) Contain data to prevent leaks Self service portal for users Retire Revoke company resource access Selective wipe Audit lost/stolen devices etc Employees Enroll Enroll devices in AD and MDM Block email/SharePoint etc until enrolled Customizable Terms & Conditions Simple end user experience Provision Provision access to corporate resources Install VPN, Wifi, Certificates Deploy device security policy settings Install mandatory apps Deploy app restriction policies Deploy data protection policies
- 16. Intune web console Mobile devices and PCs ConfigMgr console Microsoft Intune Mobile devices System Center ConfigMgr Domain joined PCs ConfigMgr integrated with Intune (hybrid)Intune standalone (cloud only) Microsoft Intune System Center 2012 R2 Configuration Manager with Microsoft Intune Build on existing Configuration Manager deployment Full PC management (OS Deployment, Endpoint Protection, application delivery control, rich reporting) Deep policy control requirements Scale to 100,000 devices Extensible administration tools (RBA, PowerShell, SQL Reporting Services) Cloud-based Management Microsoft Intune No existing Configuration Manager deployment Simplified policy control PC+MDM: 4K users, 6K PCs, and 7K devices MDM Only: 25k users and 50k mobile devices Simple web-based administration console
- 17. The End User Experience Family
- 18. Gestión identidad José María Genzor Enterprise Team lead Enterprise Mobility + Security
- 20. Identity is the foundation for enterprise mobility IDENTITY – DRIVEN SECURITY Single sign-onSelf-service Simple connection On-premises Other directories Windows Server Active Directory SaaS Azure Public cloud CloudMicrosoft Azure Active Directory
- 21. 1000s of apps, 1 identity Provide one persona to the workforce for SSO to 1000s of cloud and on-premises apps with multifactor authentication. Manage access at scale Manage identities and access at scale in the cloud and on-premises Enable business without borders Stay productive with universal access to every app and collaboration capability and self service capabilities to save money Identity at the core of your business IDENTITY – DRIVEN SECURITY
- 22. Shadow IT Data breach IDENTITY – DRIVEN SECURITY Employees Partners Customers Cloud apps Identity Devices Apps & Data Transition to cloud & mobility New attack landscape Current defenses not sufficient Identity breach On-premises apps SaaS Azure
- 23. IntelligentInnovativeHolistic Identity-driven Addresses security challenges across users (identities), devices, data, apps, and platforms―on-premises and in the cloud Offers one protected common identity for secure access to all corporate resources, on- premises and in the cloud, with risk-based conditional access Protects your data from new and changing cybersecurity attacks Enhances threat and anomaly detection with the Microsoft Intelligent Security Graph driven by a vast amount of datasets and machine learning in the cloud. IDENTITY – DRIVEN SECURITY
- 24. IDENTITY – DRIVEN SECURITY 1. Protect at the front door Safeguard your resources at the front door with innovative and advanced risk-based conditional accesses 2. Protect your data against user mistakes Gain deep visibility into user, device, and data activity on- premises and in the cloud. 3. Detect attacks before they cause damage Uncover suspicious activity and pinpoint threats with deep visibility and ongoing behavioral analytics.
- 25. Conditions Allow access Or Block access Actions Enforce MFA per user/per app Location Device state User/Application MFA Risk User IDENTITY – DRIVEN SECURITY
- 26. IDENTITY – DRIVEN SECURITY Azure Information Protection Classify & Label Protect How do I control data on-premises and in the cloud Monitor and Respond Microsoft Intune How do I prevent data leakage from my mobile apps? LOB app protection DLP for Office 365 mobile apps Optional device management Cloud App Security Risk scoring Shadow IT Discovery Policies for data control How do I gain visibility and control of my cloud apps?
- 27. IDENTITY – DRIVEN SECURITY Microsoft Advanced Threat Analytics (ATA) Behavioral Analytics Detection of known malicious attacks Detection of known security issues On-premises detection Cloud App Security + Azure Active Directory Premium Behavioral analytics Detection in the cloud Anomaly detection Security reporting and monitoring
- 28. Enterprise Mobility +Security IDENTITY - DRIVEN SECURITY Microsoft Intune Azure Information Protection Protect your users, devices, and apps Detect threats early with visibility and threat analytics Protect your data, everywhere Extend enterprise-grade security to your cloud and SaaS apps Manage identity with hybrid integration to protect application access from identity attacks Microsoft Advanced Threat Analytics Microsoft Cloud App Security Azure Active Directory Premium
- 29. Information protection Identity-driven security Managed mobile productivity Identity and access management Azure Information Protection Premium P2 Intelligent classification and encryption for files shared inside and outside your organization (includes all capabilities in P1) Azure Information Protection Premium P1 Encryption for all files and storage locations Cloud-based file tracking Microsoft Cloud App Security Enterprise-grade visibility, control, and protection for your cloud applications Microsoft Advanced Threat Analytics Protection from advanced targeted attacks leveraging user and entity behavioral analytics Microsoft Intune Mobile device and app management to protect corporate apps and data on any device Azure Active Directory Premium P2 Identity and access management with advanced protection for users and privileged identities (includes all capabilities in P1) Azure Active Directory Premium P1 Secure single sign-on to cloud and on-premises apps MFA, conditional access, and advanced security reporting EMS E3 EMS E5
- 31. www.plainconcepts.com MADRID Paseo de la Castellana 163, 10º 28046 Madrid. España T. (+34) 91 5346 836 BILBAO Nervión 3 , 6º 48001 Bilbao. España T. (+34) 94 6008 168 BARCELONA Av. Josep Tarradellas 10, 6º 1ª 08029 Barcelona. España T. (+34) 93 3607 114 SEVILLA Avenida de la innovación s/n Edificio Renta Sevilla, 3º A 41020 Sevilla. España DUBAI Dubai Internet City. Building 1 73030 Dubai. EAU T. (+971) 4 551 6653 LONDON Impact Hub Kings Cross 24B York Way, N1 9AB London. UK SEATTLE 1511, Third Ave Seattle WA 98101. USA T. (+1) 206 708 1285
Editor's Notes
- 63% of confirmed data breaches involve weak, default, or stolen passwords (Verizon 2016 Data Breach Report) 70% of the 10 most commonly used devices have serious vulnerabilities (HP 2014) More than 80% of employees admit using non-approved SaaS apps for work purposes (Stratecast, December 2013) 33% of user breaches come from user error (VansonBourne February 2014) 88% organizations who are no longer confident in their ability to detect and prevent threats to their sensitive files and emails 0.6% http://www.gartner.com/newsroom/id/3186517
- IT cannot afford to live in the past. Successful businesses of today (and tomorrow) realize the power of mobility to support employee productivity and collaboration. You need to prepare to mitigate the risks of providing freedom and space to your employees. You need to meet compliance and regulatory standards, maintain company security policies and requirements, and detect threats — all the while giving workers a better and more productive experience, so that they’re motivated to follow protocol. You need an enterprise mobility partner that can help you achieve all of this, so that everyone is a winner, and your business stays out of the headlines. Microsoft’s vision includes management and protection across four key layers: users, device, app, and data – for both your employees, business partners, and customers. Our strategy is to ensure management across these layers while ensuring your employees, business partners, and customers by providing access to everything they need from everything; protecting corporate data across email and collaboration apps all while integrating these new capabilities with what customers already have like Active Directory and System Center.
- 63% of confirmed data breaches involve weak, default, or stolen passwords (Verizon 2016 Data Breach Report) 200+ days. That’s the average amount of time that attackers reside within your network until they are detected, gathering classified data and information, waiting to strike at just the right moment. Microsoft helps you identify breaches and threats using behavioral analysis and provides a clear, actionable report on a simple attack timeline.
- Microsoft has a solution for this [Click] Traditional identity and access management solutions providing sing-sign on to on-premises applications and directory services such as Active Directory and others are used from the vast majority of organizations and huge investments were made to deploy and maintain them. These solutions are perfect for the on-premises world. [Click] Now, as we have discussed, there are new pressing requirements to provide the same experience to cloud applications hosted in any public cloud. [Click] Azure Active Directory can be the solution to this new challenge by extending the reach of on-premises identities to the cloud in a secure and efficient way. [Click] In order to do that, one simple connection is needed from on-premises directories to Azure AD. [Click] and everything else will be handled by Azure AD. Secure single sign-on to thousands of SaaS applications hosted in any cloud by using the same credentials that exist on-premises [Click] And we don’t forget the users. Azure AD provides Self-service capabilities and easy access to all the application, consumer or business, they need. in the cloud but on-premises too (Application Proxy)
- Safeguard your resources at the front door. Our solution calculates risk severity for every user and sign-in attempt, so risk-based conditional access rules can be applied to protect against suspicious logins. Protect your data against users mistakes: Gain deeper visibility into user, device, and data activity on-premises and in the cloud to create more effective, granular-level policies. Classify and label files at creation, track their usage, and change permissions when necessary. Detect attacks before they cause damage: Identify attackers in your organization using innovative behavioral analytics and anomaly detection technologies – all driven by vast amounts of Microsoft threat intelligence and security research data.
- Microsoft’s enterprise & security solutions provide a holistic framework to protect your corporate assets across, on prem, cloud and mobile devices Advanced Threat Analytics helps IT detect threats early and provide forensic investigation to keep cybercriminals out Azure Active Directory Premium security reports help identify risky log ins. That paired with Azure Active Directory Identity Protection gives IT the ability to automatically block access to apps based on real time risk scoring of identities and log ins. Microsoft Cloud App Security provides deep visibility and control of data inside cloud applications Microsoft Intune manages and secures corporate data on mobile devices and collaborated within corporate apps. Azure Information Protection helps keep data secure and encrypted throughout a customers environment and extends security when data is shared outside the organization.
