Cryptography
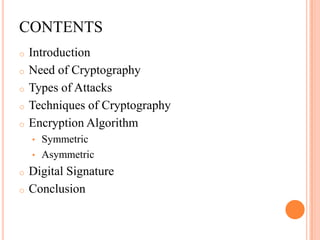
- 1. CONTENTS o Introduction o Need of Cryptography o Types of Attacks o Techniques of Cryptography o Encryption Algorithm • Symmetric • Asymmetric o Digital Signature o Conclusion
- 2. INTRODUCTION What is Cryptography? “Hidden Writing” Mainly used to protect Information. Goal of Cryptography Ensure security of communication over insecure medium Communicate even with possibility of adversary
- 3. NEED OF ENCRYPTION Confidentiality Integrity Authentication Nonrepudiation Access Control Availability
- 4. TYPES OF ATTACKS A General View A Technical View A Practical Side of Attacks Programs that Attack
- 5. PLAIN PLAIN TEXT TEXT ENCRYPTION DECRYPTION CIPHER TEXT SENDER RECEIVER BASIC BLOCK DIAGRAM
- 6. BASIC TERMINOLOGIES Encryption Encryption is the process of encoding a message so that its meaning is not obvious Decryption Decryption is the reverse process, transforming an encrypted message back into its normal, original form Cryptosystem A system for encryption and decryption is called a cryptosystem.
- 7. BASIC TERMINOLOGIES Plaintext Cipher text Key – key refers to a sequence of symbols or a numerical value used by an algorithm to alter information & making that information secure Encryption algorithm The cryptosystem involves a set of rules for how to encrypt the plaintext and how to decrypt the cipher text. Cryptanalysis Cryptanalysis is an attempt to break the cipher text.
- 8. TECHNIQUES OF CRYPTOGRAPHY Substitution Technique Caesar Cipher Monoalphabetic Cipher Homophonic Cipher Polyalphabetic Cipher Transposition Technique Rail Fence Technique Vernam Cipher(One -time Pads) Simple Columnar Cipher
- 9. ENCRYPTION ALGORITHM Symmetric Same key for encryption and decryption Key distribution problem Asymmetric Key pairs for encryption and decryption Public and private keys
- 10. SYMMETRIC ALGORITHM It is also called as Secret Key Cryptography Single key used for both encrypt & decrypt Key must be known to both the parties Key Original Plaintext Ciphertext Plaintext Encryption Decryption Symmetric Cryptosystem
- 11. ASYMMETRIC ALGORITHM Private keys are used for decrypting. Public keys are used for encrypting encryption plaintext ciphertext public key decryption ciphertext plaintext private key
- 12. COMPARISON Secret Key (Symmetric) Public Key (Asymmetric) Number of Key 1 2 Protection of Key Must be kept secret One key must be kept secret & other can be freely exposed Best Uses secrecy and integrity of Key exchange, authentication data Key Distribution Problematic Safer Speed Fast Slow; typically, 10,000 times slower than secret key
- 13. SYMMETRIC ALGORITHM Data Encryption Standard (DES): 56 bits key Advance Encryption Standard (AES): 128, 192 or 256 bits key International Data Encryption Algorithm(IDEA): 128 bits key
- 14. DATA ENCRYPTION STANDARD Developed by IBM and it is known as the Data Encryption Standard It is also known as Data Encryption Algorithm The DES algorithm is a careful and complex combination of two fundamental building blocks of encryption: Substitution and Transposition DES uses only standard arithmetic and logical operations on numbers up to 64 bits long
- 15. Plain text (64 bits) Initial Permutation (IP) LPT RPT key 16 rounds 16 rounds key Final Permutation Cipher text (64 bits) BROAD LEVEL STEPS IN DES
- 16. DATA ENCRYPTION STANDARD 1st 64 bit plain text is handed over to initial permutation function. IP is performed over the plain text. IP produces two halves of the permuted blocks left plain text (LPT) & right plain text (RPT). Now LPT & RPT goes 16 rounds of encryption process, each with its own key. Now LPT & RPT are rejoined and FINAL PERMUTATION (FP) is performed on the combined block. The result is 64 bit cipher text.
- 17. DETAILS OF ONE ROUND IN DES Key Transformation Expansion Permutation S- box Substitution P- box Permutation XOR and Swap
- 18. ADVANTAGES OF DES: o DES is also an ANSI and ISO standard - anybody can learn the details and implement it. o Since DES was designed to run on hardware, it is fast in hardware. o Hard to crack. DISADVANTAGES OF DES: o Hardware implementations of DES are very fast; DES was not designed for software and hence runs relatively slowly.
- 19. ASYMMETRIC ALGORITHM Rivest Shamir Adleman (RSA) Encryption: Based on factoring the product of large prime numbers. Knapsack Algorithm: If M1,M2…., Mn are given values & S is the sum, S=b1M1+b2M2….+bnMn where, bi can be 0 or 1
- 20. RSA It is named after its three inventors Rivest Shamir and Adleman This algorithm was introduced in 1978 and to date remains secure. RSA has been the subject of extensive cryptanalysis, and no serious flaws have yet been found. The encryption algorithm is based on the underlying problem of factoring large numbers.
- 21. RSA p and q are two large prime numbers n=p.q m = (p-1)(q-1) a is such that 1 < a < m and gcd (m , a) = 1. b is such that ( a. b) mod m = 1
- 22. RSA ENCRYPTION & DECRYPTION Message M < n. Encryption key = (a , n). Decryption key = (b , n). Encrypt => E = Ma mod n. Decrypt => M = Eb mod n.
- 23. Advantage Individuals can post their public key on their Web site. The number of the keys is only twice of the number of user. Disadvantage It is slower than symmetric algorithms. The cipher text may be larger than plain text.
- 24. DIGITAL SIGNATURE When an author signs a document, it cannot be changed. When you send a document electronically, you can also sign it. Digital signature can be done in two ways: You can sign the whole document You can sign a digest of the document
- 25. Signing the whole document You can not provide these aspects of security using the secret key. The method provides authentication & non-repudiation.
- 26. Signing the digest The two most common hash functions are: Message digest 5 (MD5) Secure hash algorithm (SHA-1) The properties of hash function One-way: the digest can only be created from the message, but not vice versa One-to-one: be very difficult to find two messages that create the same digest.
- 27. Sender site
- 28. Receiver site
- 29. APPLICATIONS OF ENCRYPTION Cryptographic Hash Function Digital Signature Certificate Secure electronic transactions Office equipment
- 30. CONCLUSION RSA finds its strongest application when parties who have no prior relationship want to share sensitive data with each other. Thus , even though slower as compared to symmetric algorithms it is & will be widely used as it can be used in digital signature for long haul transmission.
