SSI Trillion Dollar Business Opportunity
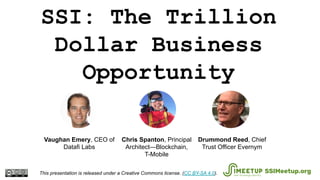
- 1. SSI: The Trillion Dollar Business Opportunity This presentation is released under a Creative Commons license. (CC BY-SA 4.0). SSIMeetup.org Drummond Reed, Chief Trust Officer Evernym Chris Spanton, Principal Architect—Blockchain, T-Mobile Vaughan Emery, CEO of Datafi Labs
- 2. 1. Empower global SSI communities 2. Open to everyone interested in SSI 3. All content is shared with CC BY SA SSIMeetup.org Alex Preukschat @SSIMeetup @AlexPreukschat Coordinating Node SSIMeetup.org https://creativecommons.org/licenses/by-sa/4.0/ SSIMeetup objectives
- 3. SSI: The Trillion Dollar Business Opportunity This presentation is released under a Creative Commons license. (CC BY-SA 4.0). SSIMeetup.org Drummond Reed, Chief Trust Officer Evernym Chris Spanton, Principal Architect—Blockchain, T-Mobile Vaughan Emery, CEO of Datafi Labs
- 4. 4 ssimeetup.org · CC BY-SA 4.0 International
- 5. ssimeetup.org · CC BY-SA 4.0 International
- 6. ssimeetup.org · CC BY-SA 4.0 International
- 7. Digital Identity Is Needed 7 Current state of Information Technology: ● User Id and passwords are too easily compromised ● The global datashere is growing faster each year ● The number of connected devices increasing 1 IDC Global DataSphere Reports ssimeetup.org · CC BY-SA 4.0 International
- 8. Digital Identity Is Needed - The Data Problem 8 175 billion terabytes of new data created annually by 2025 1 1 IDC Global DataSphere Reports We Are Here ssimeetup.org · CC BY-SA 4.0 International
- 9. Digital Identity Is Needed - The Data Problem 9 2018 Enterprise Datasphere by Industry (Exabytes) Annual Data Growth Rate of The Top Five Industries 1 IDC Global DataSphere Reports ssimeetup.org · CC BY-SA 4.0 International
- 10. Digital Identity Is Needed - The Device Problem 10 150 billion endpoints connected and accessing this data by 2025 Things Contributing To The Data Growth 1 1 IDC Global DataSphere Reports “That’s about ~20 connected devices per person” ssimeetup.org · CC BY-SA 4.0 International
- 11. Data and Identity Theft Increasing 11 12,499 Data Breaches reported in 2018 - this is 424% increase over 2017 1 1 4iQ Identity Breach Report 2019 World’s Biggest Data Breaches & Hacks: http://informationisbeautiful.net ssimeetup.org · CC BY-SA 4.0 International
- 12. Data and Identity Theft Increasing 12 14.9 Billion Identity Records circulating on the dark web - this is a 71% increase over 2017 1 4iQ Identity Breach Report 2019 ssimeetup.org · CC BY-SA 4.0 International
- 13. Where Do We Go From Here 13 The use of Digital Identities is viewed by many as one of the primary methods to counter the cybersecurity trends 1 4iQ Identity Breach Report 2019 ssimeetup.org · CC BY-SA 4.0 International
- 14. SSI in 3 Easy Steps
- 15. #1: Centralized Identity OrgYou Account ssimeetup.org · CC BY-SA 4.0 International
- 16. #2: Federated Identity OrgYou Identity ProviderAccount ssimeetup.org · CC BY-SA 4.0 International
- 17. #3: Self-Sovereign Identity (SSI) PeerYou Blockchain Connection ssimeetup.org · CC BY-SA 4.0 International
- 18. #3: Self-Sovereign Identity (SSI) Blockchain Connection Digital Wallet w/ Private Keys & Credentials Digital Wallet w/ Private Keys & Credentials Your Agent Peer Agent Public Key Public KeyDIDDID ssimeetup.org · CC BY-SA 4.0 International
- 19. Solves the decentralized PKI (public key infrastructure) problem #3: Self-Sovereign Identity (SSI) Blockchain Connection Digital Wallet w/ Private Keys & Credentials Digital Wallet w/ Private Keys & Credentials Your Agent Peer Agent Public Key Public KeyDIDDID ssimeetup.org · CC BY-SA 4.0 International
- 20. In essence, SSI is… 20 ssimeetup.org · CC BY-SA 4.0 International
- 22. W3C Verifiable Credentials Ecosystem Holder/ Prover Issuer Verifier Issues Credential Presents Proof Decentralized Identifiers (DIDs) Public Blockchain or other DID Network Signs Credential Verifies Signature Wallet Requests Credential Requests Proof ssimeetup.org · CC BY-SA 4.0 International
- 23. The Trust Triangle ssimeetup.org · CC BY-SA 4.0 International
- 24. Governance Frameworks ssimeetup.org · CC BY-SA 4.0 International
- 25. The SSI Stack
- 28. The Hyperledger Greenhouse ssimeetup.org · CC BY-SA 4.0 International
- 30. Questions? ssimeetup.org · CC BY-SA 4.0 International Drummond Reed, Chief Trust Officer Evernym Chris Spanton, Principal Architect—Blockchain, T-Mobile Vaughan Emery, CEO of Datafi Labs
