More Related Content
More from Kate Carruthers
More from Kate Carruthers (20)
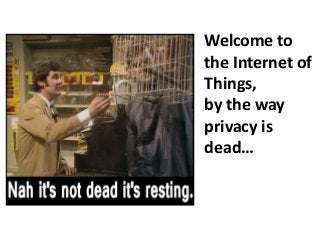
Welcome to the internet of things
- 2. Agenda
• What is the Internet of Things (IoT)
• Business models & potential market size
• Drivers for IoT
• Security and Privacy
Feb 2015 © Kate Carruthers | katecarruthers.com 2
- 3. Feb 2015 © Kate Carruthers | katecarruthers.com 3
Objects are becoming
embedded with sensors
and gaining the ability to
operate & communicate
independent of human
intervention.
- 4. Feb 2015 © Kate Carruthers | katecarruthers.com 4
The resulting information
networks promise to
create new business
models and disrupt
existing business models.
- 6. Feb 2015 © Kate Carruthers | katecarruthers.com 6
Connected devices are
transformed from a single
purchase product into a service
that generates recurring income.
IoT value is not in the devices,
but in new services related to
the devices.
- 7. New business models
• Open models
• Collaboration & loose confederations
• Agile, change ready organisations
• Restructured supply chain
• Mergers & acquisitions
Feb 2015 © Kate Carruthers | katecarruthers.com 7
- 9. Cisco says US$14 trillion IoE value
1) asset utilization (reduced costs) of $2.5 trillion
2) employee productivity (greater labor
efficiencies) of $2.5 trillion
3) supply chain and logistics (eliminating waste) of
$2.7 trillion
4) customer experience (addition of more
customers) of $3.7 trillion
5) innovation (reducing time to market) of $3.0
trillion
Feb 2015 © Kate Carruthers | katecarruthers.com 9
CISCO White paper: Embracing the Internet of Everything for your Share of $14 trillion
- 10. Market signals - 2014
• Google bought Nest for US$3.2B Jan 2014
• Google & Nest bought Dropcam for US$555M
• Samsung bought SmartThings for US$200M
• Vodafone bought Cobra Automotive for
£115M
• Zebra Technologies bought a unit of Motorola
for US$3.45B
Feb 2015 © Kate Carruthers | katecarruthers.com 10
- 11. Market signals - 2014
• global survey of 1400 software
developers
• 17.1% working on IoT apps
• 23% expect to begin work in
next 6 months
Feb 2015 © Kate Carruthers | katecarruthers.com 11
Evans Data Corporation Survey July 2014
- 12. Driven by convergence
• Ubiquitous comms
networks
• Mobile connectivity
• 3D printing
• Sensor networks
• Big data > drawing
useful inferences
• Peer to peer
networks
• Cloud computing
• Artificial intelligence
• Commodity sensors
• Software defined
networks
Feb 2015 © Kate Carruthers | katecarruthers.com 12
- 13. Fuelled by app ecosystem
“Between 2008 and 2017,
Google Play and Apple’s App
Store will be responsible for a
mind-blowing number of
mobile app downloads: 350
billion.”
Feb 2015 © Kate Carruthers | katecarruthers.com 13
Source: http://www.mobilemarketingwatch.com/the-decade-of-350-billion-app-downloads-26932/
- 14. Feb 2015 © Kate Carruthers | katecarruthers.com 14
Allflex DNA tags
- 15. Feb 2015 © Kate Carruthers | katecarruthers.com 15
- 17. Feb 2015 © Kate Carruthers | katecarruthers.com 17
Driverless trucks the next big thing in WA's Pilbara, ABC 25 Apr
2014, 3:13pm
- 19. Feb 2015 © Kate Carruthers | katecarruthers.com 19
- 20. Feb 2015 © Kate Carruthers | katecarruthers.com 20
Bloomberg, Data Breaches in the US, at 4 Sep 2014
- 21. Feb 2015 © Kate Carruthers | katecarruthers.com 21
• 3rd party HVAC
firm attack
vector
• Security
software
disabled
• PCI DSS didn’t
save them
- 22. Feb 2015 © Kate Carruthers | katecarruthers.com 22
Bloomberg, Oct 2014
- 23. JP Morgan
• Sarbanes-Oxley Act (SOX)
• Payment Card Industry Data Security Standard
(PCI DSS)
• Gramm-Leach-Bliley Act (GLB) Act
• Electronic Fund Transfer Act, Regulation E (EFTA)
• Free and Secure Trade Program (FAST)
• Fair and Accurate Credit Transaction Act (FACTA),
including Red Flags Rule
• Federal Rules of Civil Procedure (FRCP)
Feb 2015 © Kate Carruthers | katecarruthers.com 23
- 24. Feb 2015 © Kate Carruthers | katecarruthers.com 24
Traditional approach to perimeter security
- 25. Feb 2015 © Kate Carruthers | katecarruthers.com 25
Bot-herders can
launch DDoS attacks
from dryers,
refrigerators, other
Internet of Things
devices
Network World Sep 2014
- 26. Feb 2015 © Kate Carruthers | katecarruthers.com 26Proofpoint Uncovers Internet of Things (IoT) Cyberattack, January 16, 2014
“The global attack campaign
involved more than 750,000
malicious email
communications coming
from more than 100,000
everyday consumer gadgets
…”
- 27. Feb 2015 © Kate Carruthers | katecarruthers.com 27Proofpoint Uncovers Internet of Things (IoT) Cyberattack, January 16, 2014
“… such as home-
networking routers,
connected multi-media
centers, televisions and at
least one refrigerator”
- 28. Feb 2015 © Kate Carruthers | katecarruthers.com 28
It’s “often impossible to
patch the software or
upgrade the components
to the latest version.”
Bruce Schneier, The Internet of Things Is Wildly Insecure - And Often Unpatchable, Wired, Jan
2014
- 29. Feb 2015 © Kate Carruthers | katecarruthers.com 29
“Often, the complete
source code isn’t available.
Yes, they’ll have the source
code to Linux and any other
open-source components.”
Bruce Schneier, The Internet of Things Is Wildly Insecure - And Often Unpatchable, Wired, Jan
2014
- 30. Feb 2015 © Kate Carruthers | katecarruthers.com 30
“But many of the device
drivers and other
components are just
‘binary blobs’ - no source
code at all.”
Bruce Schneier, The Internet of Things Is Wildly Insecure - And Often Unpatchable, Wired, Jan
2014
- 31. Feb 2015 © Kate Carruthers | katecarruthers.com 31
“That’s the most pernicious
part of the problem: No
one can possibly patch
code that’s just binary.”
Bruce Schneier, The Internet of Things Is Wildly Insecure - And Often Unpatchable, Wired, Jan
2014
- 32. Privacy
“If it was dead, they
wouldn't be fighting so hard
to kill it, all over the world.”
- Peter Watts
Feb 2015 © Kate Carruthers | katecarruthers.com 32
- 33. Feb 2015 © Kate Carruthers | katecarruthers.com 33
http://www.abc.net.au/news/2014-11-04/berg-the-jig-is-up-on-data-retention-plans/5864432
http://www.theguardian.com/uk-news/2015/jan/22/snoopers-charter-changed-version-pass-before-election
- 34. Privacy
Privacy by Design:
embedding privacy into IT, business
practices and networked
infrastructures right from the
outset
https://www.privacybydesign.ca
Feb 2015 © Kate Carruthers | katecarruthers.com 34
- 35. Consumer privacy
• Pervasive computing
• Personalisation
• Customisation
• Convenience
• Lack of understanding
• Meaningful consent
Feb 2015 © Kate Carruthers | katecarruthers.com 35
- 36. Oops we spied on your wifi
Feb 2015 © Kate Carruthers | katecarruthers.com 36
http://www.cnet.com/news/google-oops-we-spied-on-your-wi-fi/
- 37. Feb 2015 © Kate Carruthers | katecarruthers.com 37
Time, Sep 2014
- 38. Spy TVs…
Feb 2015 © Kate Carruthers | katecarruthers.com 38
http://www.tomsguide.com/us/lg-tvs-spying-confirmation,news-17887.html
- 39. Feb 2015 © Kate Carruthers | katecarruthers.com 39
- 40. Feb 2015 © Kate Carruthers | katecarruthers.com 40
“We tend to
overestimate the effect
of a technology in the
short run and
underestimate the effect
in the long run.”- Amara's law