Red Flag Rules Compliant? Maybe Not...!
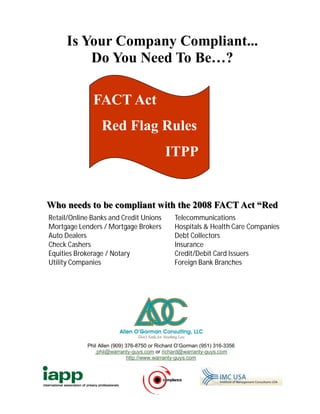
- 1. Is Your Company Compliant... Do You Need To Be…? FACT Act Red Flag Rules ITPP Who needs to be compliant with the 2008 FACT Act “Red Retail/Online Banks and Credit Unions Telecommunications Mortgage Lenders / Mortgage Brokers Hospitals & Health Care Companies Auto Dealers Debt Collectors Check Cashers Insurance Equities Brokerage / Notary Credit/Debit Card Issuers Utility Companies Foreign Bank Branches Phil Allen (909) 376-8750 or Richard O’Gorman (951) 316-3356 phil@warranty-guys.com or richard@warranty-guys.com http://www.warranty-guys.com
- 2. Red Flag Compliance Simplified…! FACT Act Do you have a written Identity Theft Prevention Program? Red Flag Rules Do you have a clearly defined written process for the relevant staff to follow that is based on your organizations particular needs? ITPP Does the process take into consideration both manual detection processes and the use of a third party electronic ID verification service? NOTE: If you use an electronic verification service and it was not Identity Theft Prevention Program available is your staff trained well enough for you to know without a doubt they could detect a red flag? The final regulations list the four basic elements Have you completed a risk assessment that includes - work flow, that must be included in the Program of a financial past history of ID theft issues, current organization structure and institution or creditor. determination of relevant staff? The Program must contain ‘‘reasonable policies Have your relevant staff and management been trained on all and procedures’’ to: Red Flags and those specific to your industry and organization? Identify relevant Red Flags for covered Have they signed a training log and agreement to comply with accounts and incorporate those Red Flags into Red Flag Rules to protect your organization? the Program; If you are using a third party or are relying on a automated third Detect Red Flags that have been incorporated party provider such as electronic ID verification services to into the Program; detect customer Red Flags and the provider was no longer available - Is the process you are using and support material Respond appropriately to any Red Flags that good enough that you could still manually detect Red Flags and are detected to prevent and mitigate identity still be compliant with Red Flag legislation on your own? theft; and Would you be considered a low, medium, or high risk Ensure the Program is updated periodically, to organization based on a risk assessment? reflect changes in risks to customers or to the safety and soundness of the financial institution or (DEPENDING ON HOW YOUR SALES PROCESS WORKS YOU creditor from identity theft. COULD BE ANY ONE OF THOSE.) The regulations also enumerate certain steps For example; Most automotive dealers would be considered high risk that financial institutions and creditors must take - yet in a small 4 store group - 2 were considered low risk and 2 were to administer the Program. still high risk. Same dealer group. Same management. Virtually all major providers of Red Flag programs are template based that re- These steps include; quire you to follow their lead and make your own risk assessment, provide your own training or listen to a canned general training on- Obtaining approval of the initial written Program line. by the board of directors or a committee of the board A financial institution or creditor is ultimately responsible for complying with the final rules and guidelines even if it out- Ensuring oversight of the development, implemen- sources an activity to a third-party service provider. Thus, a fi- tation and administration of the Program. nancial institution or creditor that uses a service provider to open accounts will need to provide for the detection, prevention, Training staff, and and mitigation of identity theft in connection with this activity, even when the service provider has access to the information of Overseeing service provider arrangements. a person who is not yet, and may not become, a ‘‘customer.’’
- 3. Red Flag Rules Compliant…? Maybe — Maybe Not! Let me ask you a question. Are you compliant? Before you answer that … If you haven’t tested, updated and trained and retrained your staff, the odds are that your Information Security Program isn’t up to date. Statically the odds at this moment are 94% that your organization isn’t compliant with GLB Safeguards. Red Flag Rules pick up where GLB Safeguards left off. It takes both processes done properly, working together, to protect customer nonpublic personal information. Dealerships are more a target today than ever before. In the ten years from 1999 to 2008 Identity Theft and Fraud has grown more than 1400% and has reached epidemic proportions. Identity Theft has been the #1 concern of consumers for the last 9 years. Let me give you the good news first. The odds of you ever having an FTC audit or receiving an audit letter are slim to none (and Slim done left town). Let me give you the bad news … It is a virtually certainty that if someone files a complaint directly with the FTC you will be contacted and secondly – if it gets on the local news, the FTC will come a-calling. Let me ask you again! Are you absolutely certain that all customer information is properly secured and protected in accor- dance with your Information Security Plan (ISP)? Is your ISP in writing, does it contain a risk assessment, have you made the corrections the risk assessment found and did you document them and has it been updated on a periodic basis? Has your staff been trained? Have you been testing the processes you put in place? When the Red Flag audits take place they will look at GLB Safeguards compliance for “financial institutions” and HIPAA compliance for Healthcare. The odds are you are using a privacy statement and it states that you don’t share customer infor- mation with other than necessary staff and that you maintain physical, electronic, and procedural safeguards. If you are, it is a “legal time bomb” for you. Not a matter of if it will happen – only when it will happen. (Or as we have discovered many times – it has already happened and you didn’t know it.) Your thinking – this guy is full of bull. He is just trying to scare me into compliance and to spend money I don’t want to spend right now. You are 100% right and 110% wrong. Every word and every statistic you have read is correct. These are the facts – there is no sugar coating in this mes- sage for you. As a third party vendor – it is my only job to protect you. Not a second, third or fourth job descrip- tion. I have no problem playing favorites or letting someone slide. I am the guy that tells it like it is – who pulls customer information out of drawers and unlocked file cabinets and can hack your computers and find the weakness in your physical, electronic and procedural security. But I do it FOR you. I do it TO protect you. I am your unbiased, independent, get-you-compliant-now guy. In Star Wars – Yoda said, “Do it or not, there is no try.” Compliance is an always thing – not just when you feel like it. Even if you do it right you are at risk – but a far less risk than if you are not compliant and making the effort to stay there. With the new Red Flag Rule – there will be audits and they will look at both Red Flag and GLB Safeguards. Red Flags pick up where GLB Safeguards leave off … to have effective systems you must have both compliance rules working together. Lee Holden Compliance Coach, Consultant, & Trainer Allen O’Gorman Consulting, LLC “Don’t Settle for Anything Less”