Architectural Layers for Security
•Download as PPTX, PDF•
1 like•385 views
Group output generated out of the Microsoft UK Architect Council Meeting at Bletchley Park
Report
Share
Report
Share
Recommended
More Related Content
Similar to Architectural Layers for Security
Similar to Architectural Layers for Security (20)
Compliance standards interoperability - Zoltan Precsenyi

Compliance standards interoperability - Zoltan Precsenyi
HighCloud Security CSA LA and Seattle chapter presentation

HighCloud Security CSA LA and Seattle chapter presentation
LASCON 2014: Multi-Factor Authentication -- Weeding out the Snake Oil

LASCON 2014: Multi-Factor Authentication -- Weeding out the Snake Oil
Security threats with Kubernetes - Igor Khoroshchenko

Security threats with Kubernetes - Igor Khoroshchenko
MongoDB World 2019: New Encryption Capabilities in MongoDB 4.2: A Deep Dive i...

MongoDB World 2019: New Encryption Capabilities in MongoDB 4.2: A Deep Dive i...
More from ukdpe
More from ukdpe (20)
Mike Ormond: Silverlight for Windows Phone 7 (UK TechDays)

Mike Ormond: Silverlight for Windows Phone 7 (UK TechDays)
Windows Phone 7: How (Not) to Fail Marketplace Ingestion

Windows Phone 7: How (Not) to Fail Marketplace Ingestion
Microsoft UK TechDays - Top 10 ASP.NET 4.0 Features

Microsoft UK TechDays - Top 10 ASP.NET 4.0 Features
Mike Taulty MIX10 Silverlight 4 Patterns Frameworks

Mike Taulty MIX10 Silverlight 4 Patterns Frameworks
Mike Taulty MIX10 Silverlight 4 Accelerated Fundamentals

Mike Taulty MIX10 Silverlight 4 Accelerated Fundamentals
Mike Taulty TechDays 2010 Silverlight and Windows Phone 7 CTP

Mike Taulty TechDays 2010 Silverlight and Windows Phone 7 CTP
Mike Taulty TechDays 2010 Silverlight 4 - What's New?

Mike Taulty TechDays 2010 Silverlight 4 - What's New?
Mike Taulty DevDays 2010 Silverlight 4 - What's New Part 2

Mike Taulty DevDays 2010 Silverlight 4 - What's New Part 2
Mike Taulty DevDays 2010 Silverlight 4 - What's New Part 1

Mike Taulty DevDays 2010 Silverlight 4 - What's New Part 1
Mike Taulty MIX10 Silverlight Frameworks and Patterns

Mike Taulty MIX10 Silverlight Frameworks and Patterns
How Microsoft Secures its Online Services [WHITEPAPER]![How Microsoft Secures its Online Services [WHITEPAPER]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![How Microsoft Secures its Online Services [WHITEPAPER]](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
How Microsoft Secures its Online Services [WHITEPAPER]
Recently uploaded
Recently uploaded (20)
WhatsApp 9892124323 ✓Call Girls In Kalyan ( Mumbai ) secure service

WhatsApp 9892124323 ✓Call Girls In Kalyan ( Mumbai ) secure service
Beyond Boundaries: Leveraging No-Code Solutions for Industry Innovation

Beyond Boundaries: Leveraging No-Code Solutions for Industry Innovation
Factors to Consider When Choosing Accounts Payable Services Providers.pptx

Factors to Consider When Choosing Accounts Payable Services Providers.pptx
Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...

Transforming Data Streams with Kafka Connect: An Introduction to Single Messa...
The 7 Things I Know About Cyber Security After 25 Years | April 2024

The 7 Things I Know About Cyber Security After 25 Years | April 2024
Integration and Automation in Practice: CI/CD in Mule Integration and Automat...

Integration and Automation in Practice: CI/CD in Mule Integration and Automat...
Handwritten Text Recognition for manuscripts and early printed texts

Handwritten Text Recognition for manuscripts and early printed texts
FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi

FULL ENJOY 🔝 8264348440 🔝 Call Girls in Diplomatic Enclave | Delhi
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
Enhancing Worker Digital Experience: A Hands-on Workshop for Partners

Enhancing Worker Digital Experience: A Hands-on Workshop for Partners
Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...

Neo4j - How KGs are shaping the future of Generative AI at AWS Summit London ...
Injustice - Developers Among Us (SciFiDevCon 2024)

Injustice - Developers Among Us (SciFiDevCon 2024)
Architectural Layers for Security
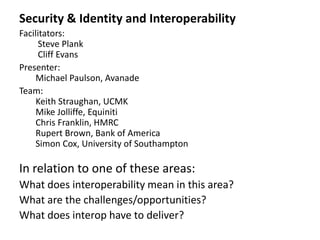
- 1. Security & Identity and Interoperability Facilitators: Steve Plank Cliff Evans Presenter: Michael Paulson, Avanade Team: Keith Straughan, UCMK Mike Jolliffe, Equiniti Chris Franklin, HMRC Rupert Brown, Bank of America Simon Cox, University of Southampton In relation to one of these areas: What does interoperability mean in this area? What are the challenges/opportunities? What does interop have to deliver?
- 2. Security is “Enabling entities to interact by providing a control framework that delivers confidentiality, integrity and availability” Identity is A set of claims made by one subject about another subject
- 3. Architectural Layers Layers Interoperability characteristics Business Examples: Risk Management: • Consistent view of the “role” of participants and entities” •C2B •B2B • “non-repudiation” • Regulatory Compliance •“Secure” Payments Application •Context between entities • Sometimes you want privacy • The notion of “wrappers” • Standards • WS-Security Infrastructure/ • STANDARDS! Technology • X.509 • Kerberos • PayPal • Consistency: •AuthN • AuthZ • Encryption
