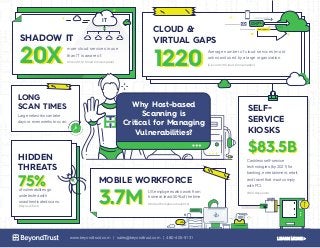
Why Host-Based Scanning is Critical for Managing Vulnerabilities [Infographic]
•
0 j'aime•102 vues
Check out this infographic to grasp why host-based scanning is a critical capability for managing vulnerabilities. Learn more: https://www.beyondtrust.com/resources/data-sheet/retina-host-security-scanner/ https://www.beyondtrust.com/products/retina/
Signaler
Partager
Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
Recommandé
Contenu connexe
En vedette
En vedette (14)
Entity provider selection confusion attacks in JAX-RS applications

Entity provider selection confusion attacks in JAX-RS applications
PBISE : Installation and Administration Guide v7.5

PBISE : Installation and Administration Guide v7.5
Linux host orchestration with Foreman, Puppet and Gitlab

Linux host orchestration with Foreman, Puppet and Gitlab
Eyes Wide Shut: What Do Your Passwords Do When No One is Watching?

Eyes Wide Shut: What Do Your Passwords Do When No One is Watching?
Puppet Camp DC 2014: Managing Puppet with MCollective

Puppet Camp DC 2014: Managing Puppet with MCollective
CfgMgmtCamp 2015 - Managing the Content Lifecycle with Katello

CfgMgmtCamp 2015 - Managing the Content Lifecycle with Katello
Plus de BeyondTrust
Plus de BeyondTrust (20)
The 5 Crazy Mistakes IoT Administrators Make with System Credentials

The 5 Crazy Mistakes IoT Administrators Make with System Credentials
10 Steps to Better Windows Privileged Access Management

10 Steps to Better Windows Privileged Access Management
Tips to Remediate your Vulnerability Management Program

Tips to Remediate your Vulnerability Management Program
Sudo Mode (part 2): How Privilege Mistakes could Dismantle your Entire Enterp...

Sudo Mode (part 2): How Privilege Mistakes could Dismantle your Entire Enterp...
Unearth Active Directory Threats Before They Bury Your Enterprise

Unearth Active Directory Threats Before They Bury Your Enterprise
8-step Guide to Administering Windows without Domain Admin Privileges

8-step Guide to Administering Windows without Domain Admin Privileges
Securing DevOps through Privileged Access Management

Securing DevOps through Privileged Access Management
Crush Common Cybersecurity Threats with Privilege Access Management

Crush Common Cybersecurity Threats with Privilege Access Management
Active Directory Auditing Tools: Building Blocks or just a Handful of Dust?

Active Directory Auditing Tools: Building Blocks or just a Handful of Dust?
Avoiding the 10 Deadliest and Most Common Sins for Securing Windows

Avoiding the 10 Deadliest and Most Common Sins for Securing Windows
Unix / Linux Privilege Management: What a Financial Services CISO Cares About

Unix / Linux Privilege Management: What a Financial Services CISO Cares About
Why Federal Systems are Immune from Ransomware...& other Grim Fairy Tales)

Why Federal Systems are Immune from Ransomware...& other Grim Fairy Tales)
The Hacker Playbook: How to Think like a Cybercriminal to Reduce Risk

The Hacker Playbook: How to Think like a Cybercriminal to Reduce Risk
Hacker techniques for bypassing existing antivirus solutions & how to build a...

Hacker techniques for bypassing existing antivirus solutions & how to build a...
How Federal Agencies Can Build a Layered Defense for Privileged Accounts

How Federal Agencies Can Build a Layered Defense for Privileged Accounts
Using Advanced Threat Analytics to Prevent Privilege Escalation Attacks

Using Advanced Threat Analytics to Prevent Privilege Escalation Attacks
Prevent Data Leakage Using Windows Information Protection (WIP)

Prevent Data Leakage Using Windows Information Protection (WIP)
Enemy from Within: Managing and Controlling Access

Enemy from Within: Managing and Controlling Access
Dernier
This book is written based on the author's over 10 years of experience in Digital Marketing and IT. It aims to provide readers with insights into the benefits of marketing technology (MarTech), its categories, how to choose the right tools, and a summary of interesting trends in each yearMarTech Trend 2024 Book : Marketing Technology Trends (2024 Edition) How Data...

MarTech Trend 2024 Book : Marketing Technology Trends (2024 Edition) How Data...Jittipong Loespradit
Model Call Girl Services in Delhi reach out to us at 🔝 9953056974 🔝✔️✔️
Our agency presents a selection of young, charming call girls available for bookings at Oyo Hotels. Experience high-class escort services at pocket-friendly rates, with our female escorts exuding both beauty and a delightful personality, ready to meet your desires. Whether it's Housewives, College girls, Russian girls, Muslim girls, or any other preference, we offer a diverse range of options to cater to your tastes.
We provide both in-call and out-call services for your convenience. Our in-call location in Delhi ensures cleanliness, hygiene, and 100% safety, while our out-call services offer doorstep delivery for added ease.
We value your time and money, hence we kindly request pic collectors, time-passers, and bargain hunters to refrain from contacting us.
Our services feature various packages at competitive rates:
One shot: ₹2000/in-call, ₹5000/out-call
Two shots with one girl: ₹3500/in-call, ₹6000/out-call
Body to body massage with sex: ₹3000/in-call
Full night for one person: ₹7000/in-call, ₹10000/out-call
Full night for more than 1 person: Contact us at 🔝 9953056974 🔝. for details
Operating 24/7, we serve various locations in Delhi, including Green Park, Lajpat Nagar, Saket, and Hauz Khas near metro stations.
For premium call girl services in Delhi 🔝 9953056974 🔝. Thank you for considering us!CHEAP Call Girls in Pushp Vihar (-DELHI )🔝 9953056974🔝(=)/CALL GIRLS SERVICE

CHEAP Call Girls in Pushp Vihar (-DELHI )🔝 9953056974🔝(=)/CALL GIRLS SERVICE9953056974 Low Rate Call Girls In Saket, Delhi NCR
Abortion Pill Prices Tembisa [(+27832195400*)] 🏥 Women's Abortion Clinic in Tembisa ● Abortion Pills For Sale in Tembisa ● Tembisa 🏥🚑!! Abortion Clinic Near Me Cost, Price, Women's Clinic Near Me, Abortion Clinic Near, Abortion Doctors Near me, Abortion Services Near Me, Abortion Pills Over The Counter, Abortion Pill Doctors' Offices, Abortion Clinics, Abortion Places Near Me, Cheap Abortion Places Near Me, Medical Abortion & Surgical Abortion, approved cyctotec pills and womb cleaning pills too plus all the instructions needed This Discrete women’s Termination Clinic offers same day services that are safe and pain free, we use approved pills and we clean the womb so that no side effects are present. Our main goal is that of preventing unintended pregnancies and unwanted births every day to enable more women to have children by choice, not chance. We offer Terminations by Pill and The Morning After Pill.” Our Private VIP Abortion Service offers the ultimate in privacy, efficiency and discretion. we do safe and same day termination and we do also womb cleaning as well its done from 1 week up to 28 weeks. We do delivery of our services world wide SAFE ABORTION CLINICS/PILLS ON SALE WE DO DELIVERY OF PILLS ALSO Abortion clinic at very low costs, 100% Guaranteed and it’s safe, pain free and a same day service. It Is A 45 Minutes Procedure, we use tested abortion pills and we do womb cleaning as well. Alternatively the medical abortion pill and womb cleansing !!!Abortion Pill Prices Tembisa [(+27832195400*)] 🏥 Women's Abortion Clinic in T...![Abortion Pill Prices Tembisa [(+27832195400*)] 🏥 Women's Abortion Clinic in T...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Abortion Pill Prices Tembisa [(+27832195400*)] 🏥 Women's Abortion Clinic in T...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Abortion Pill Prices Tembisa [(+27832195400*)] 🏥 Women's Abortion Clinic in T...Medical / Health Care (+971588192166) Mifepristone and Misoprostol tablets 200mg
Dernier (20)
%in Bahrain+277-882-255-28 abortion pills for sale in Bahrain

%in Bahrain+277-882-255-28 abortion pills for sale in Bahrain
call girls in Vaishali (Ghaziabad) 🔝 >༒8448380779 🔝 genuine Escort Service 🔝✔️✔️

call girls in Vaishali (Ghaziabad) 🔝 >༒8448380779 🔝 genuine Escort Service 🔝✔️✔️
MarTech Trend 2024 Book : Marketing Technology Trends (2024 Edition) How Data...

MarTech Trend 2024 Book : Marketing Technology Trends (2024 Edition) How Data...
%+27788225528 love spells in Huntington Beach Psychic Readings, Attraction sp...

%+27788225528 love spells in Huntington Beach Psychic Readings, Attraction sp...
CHEAP Call Girls in Pushp Vihar (-DELHI )🔝 9953056974🔝(=)/CALL GIRLS SERVICE

CHEAP Call Girls in Pushp Vihar (-DELHI )🔝 9953056974🔝(=)/CALL GIRLS SERVICE
Introducing Microsoft’s new Enterprise Work Management (EWM) Solution

Introducing Microsoft’s new Enterprise Work Management (EWM) Solution
OpenChain - The Ramifications of ISO/IEC 5230 and ISO/IEC 18974 for Legal Pro...

OpenChain - The Ramifications of ISO/IEC 5230 and ISO/IEC 18974 for Legal Pro...
Devoxx UK 2024 - Going serverless with Quarkus, GraalVM native images and AWS...

Devoxx UK 2024 - Going serverless with Quarkus, GraalVM native images and AWS...
Architecture decision records - How not to get lost in the past

Architecture decision records - How not to get lost in the past
%in Stilfontein+277-882-255-28 abortion pills for sale in Stilfontein

%in Stilfontein+277-882-255-28 abortion pills for sale in Stilfontein
Shapes for Sharing between Graph Data Spaces - and Epistemic Querying of RDF-...

Shapes for Sharing between Graph Data Spaces - and Epistemic Querying of RDF-...
WSO2CON 2024 - Cloud Native Middleware: Domain-Driven Design, Cell-Based Arch...

WSO2CON 2024 - Cloud Native Middleware: Domain-Driven Design, Cell-Based Arch...
WSO2Con2024 - WSO2's IAM Vision: Identity-Led Digital Transformation

WSO2Con2024 - WSO2's IAM Vision: Identity-Led Digital Transformation
Abortion Pill Prices Tembisa [(+27832195400*)] 🏥 Women's Abortion Clinic in T...![Abortion Pill Prices Tembisa [(+27832195400*)] 🏥 Women's Abortion Clinic in T...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Abortion Pill Prices Tembisa [(+27832195400*)] 🏥 Women's Abortion Clinic in T...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Abortion Pill Prices Tembisa [(+27832195400*)] 🏥 Women's Abortion Clinic in T...
Right Money Management App For Your Financial Goals

Right Money Management App For Your Financial Goals
%+27788225528 love spells in Boston Psychic Readings, Attraction spells,Bring...

%+27788225528 love spells in Boston Psychic Readings, Attraction spells,Bring...
Why Host-Based Scanning is Critical for Managing Vulnerabilities [Infographic]
- 1. SELF- SERVICE KIOSKS $83.5B$83.5B Cashless self-service technologies (by 2021) for banking, entertainment, retail, and travel that must comply with PCI. (BCC Research) CLOUD & VIRTUAL GAPS 12201220 Average number of cloud services (most unknown) used by a large organization. (Cisco 2016 Cloud Consumption) Large networks can take days or even weeks to scan. LONG SCAN TIMES US employees who work from home at least 50% of the time MOBILE WORKFORCE 3.7M3.7M (Global Workplace Analytics) of vulnerabilites go undetected with unauthenticated scans. HIDDEN THREATS 75%75% (BeyondTrust) IT SHADOW IT 20X20X more cloud services in use than IT is aware of. (Cisco 2016 Cloud Consumption) Why Host-based Scanning is Critical for Managing Vulnerabilities? www.beyondtrust.com | sales@beyondtrust.com | 480-405-9131 LEARN MORE >
