Weaponized malware comparison
•
0 j'aime•463 vues
Weaponized malware comparison
Signaler
Partager
Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
Contenu connexe
Tendances
Tendances (20)
Art integrated project of computer science class 12

Art integrated project of computer science class 12
Cyber Crime and Security (Ways to protect yourself on the internet)

Cyber Crime and Security (Ways to protect yourself on the internet)
En vedette
NTXISSACSC2 - Advanced Persistent Threat (APT) Life Cycle Management Monty Mc...

NTXISSACSC2 - Advanced Persistent Threat (APT) Life Cycle Management Monty Mc...North Texas Chapter of the ISSA
En vedette (20)
Advanced Persistent Threats (Shining the Light on the Industries' Best Kept S...

Advanced Persistent Threats (Shining the Light on the Industries' Best Kept S...
NTXISSACSC2 - Advanced Persistent Threat (APT) Life Cycle Management Monty Mc...

NTXISSACSC2 - Advanced Persistent Threat (APT) Life Cycle Management Monty Mc...
Introduction to Advanced Persistent Threats (APT) for Non-Security Engineers

Introduction to Advanced Persistent Threats (APT) for Non-Security Engineers
Models of Escalation and De-escalation in Cyber Conflict

Models of Escalation and De-escalation in Cyber Conflict
From data to numbers to knowledge: semantic embeddings By Alvaro Barbero

From data to numbers to knowledge: semantic embeddings By Alvaro Barbero
The Rise of Engineering-Driven Analytics by Loren Shure

The Rise of Engineering-Driven Analytics by Loren Shure
Common Techniques To Identify Advanced Persistent Threat (APT)

Common Techniques To Identify Advanced Persistent Threat (APT)
ICT Security: Defence strategies against targeted attack

ICT Security: Defence strategies against targeted attack
From data to AI with the Machine Learning Canvas by Louis Dorard Slides

From data to AI with the Machine Learning Canvas by Louis Dorard Slides
Finding the needle in the haystack: how Nestle is leveraging big data to defe...

Finding the needle in the haystack: how Nestle is leveraging big data to defe...
Plus de Bill Hagestad II
Plus de Bill Hagestad II (17)
Chinese Uses of Big Data Cloud Security 漫步在雲端資安新戰場 

Chinese Uses of Big Data Cloud Security 漫步在雲端資安新戰場
China's People's Liberation Army force distribution 2015 中国人民解放军陆军

China's People's Liberation Army force distribution 2015 中国人民解放军陆军
China’s clandestine services red dragon rising copyright 2015 

China’s clandestine services red dragon rising copyright 2015
s4x15whychinaoriranwouldtargetusnationalcriticalinfrastructure

s4x15whychinaoriranwouldtargetusnationalcriticalinfrastructure
'The How & Why China & Iran Would Successfully Target US Critical Infratsruct...

'The How & Why China & Iran Would Successfully Target US Critical Infratsruct...
高技术战争 Gaojishu People's Liberation Army high tech war in 2014

高技术战争 Gaojishu People's Liberation Army high tech war in 2014
Red Dragon Rising Understanding the Chinese Cyber Scenarios 02 march 2014

Red Dragon Rising Understanding the Chinese Cyber Scenarios 02 march 2014
解放軍网络对抗技术 Chinese Military Network Warfare Technology DDoS

解放軍网络对抗技术 Chinese Military Network Warfare Technology DDoS
Red Dragon's CYBER Security RSS Feed .docx version

Red Dragon's CYBER Security RSS Feed .docx version
Dernier
Hot Service (+9316020077 ) Goa Call Girls Real Photos and Genuine Service

Hot Service (+9316020077 ) Goa Call Girls Real Photos and Genuine Servicesexy call girls service in goa
Rohini Sector 26 Call Girls Delhi 9999965857 @Sabina Saikh No Advance

Rohini Sector 26 Call Girls Delhi 9999965857 @Sabina Saikh No AdvanceCall Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
Dernier (20)
Call Girls Service Chandigarh Lucky ❤️ 7710465962 Independent Call Girls In C...

Call Girls Service Chandigarh Lucky ❤️ 7710465962 Independent Call Girls In C...
Russian Call Girls in Kolkata Ishita 🤌 8250192130 🚀 Vip Call Girls Kolkata

Russian Call Girls in Kolkata Ishita 🤌 8250192130 🚀 Vip Call Girls Kolkata
AlbaniaDreamin24 - How to easily use an API with Flows

AlbaniaDreamin24 - How to easily use an API with Flows
GDG Cloud Southlake 32: Kyle Hettinger: Demystifying the Dark Web

GDG Cloud Southlake 32: Kyle Hettinger: Demystifying the Dark Web
VIP Kolkata Call Girl Alambazar 👉 8250192130 Available With Room

VIP Kolkata Call Girl Alambazar 👉 8250192130 Available With Room
Russian Call girls in Dubai +971563133746 Dubai Call girls

Russian Call girls in Dubai +971563133746 Dubai Call girls
Call Girls In Model Towh Delhi 💯Call Us 🔝8264348440🔝

Call Girls In Model Towh Delhi 💯Call Us 🔝8264348440🔝
Delhi Call Girls Rohini 9711199171 ☎✔👌✔ Whatsapp Hard And Sexy Vip Call

Delhi Call Girls Rohini 9711199171 ☎✔👌✔ Whatsapp Hard And Sexy Vip Call
Call Girls In Defence Colony Delhi 💯Call Us 🔝8264348440🔝

Call Girls In Defence Colony Delhi 💯Call Us 🔝8264348440🔝
Hot Service (+9316020077 ) Goa Call Girls Real Photos and Genuine Service

Hot Service (+9316020077 ) Goa Call Girls Real Photos and Genuine Service
'Future Evolution of the Internet' delivered by Geoff Huston at Everything Op...

'Future Evolution of the Internet' delivered by Geoff Huston at Everything Op...
Rohini Sector 26 Call Girls Delhi 9999965857 @Sabina Saikh No Advance

Rohini Sector 26 Call Girls Delhi 9999965857 @Sabina Saikh No Advance
VIP Kolkata Call Girls Salt Lake 8250192130 Available With Room

VIP Kolkata Call Girls Salt Lake 8250192130 Available With Room
VIP Kolkata Call Girl Salt Lake 👉 8250192130 Available With Room

VIP Kolkata Call Girl Salt Lake 👉 8250192130 Available With Room
Moving Beyond Twitter/X and Facebook - Social Media for local news providers

Moving Beyond Twitter/X and Facebook - Social Media for local news providers
Call Girls In Sukhdev Vihar Delhi 💯Call Us 🔝8264348440🔝

Call Girls In Sukhdev Vihar Delhi 💯Call Us 🔝8264348440🔝
FULL ENJOY Call Girls In Mayur Vihar Delhi Contact Us 8377087607

FULL ENJOY Call Girls In Mayur Vihar Delhi Contact Us 8377087607
VIP Kolkata Call Girl Kestopur 👉 8250192130 Available With Room

VIP Kolkata Call Girl Kestopur 👉 8250192130 Available With Room
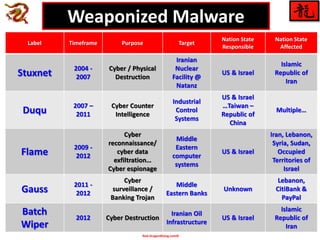
Weaponized malware comparison
- 1. Red-DragonRising.com© Label Timeframe Purpose Target Nation State Responsible Nation State Affected Stuxnet 2004 - 2007 Cyber / Physical Destruction Iranian Nuclear Facility @ Natanz US & Israel Islamic Republic of Iran Duqu 2007 – 2011 Cyber Counter Intelligence Industrial Control Systems US & Israel …Taiwan – Republic of China Multiple… Flame 2009 - 2012 Cyber reconnaissance/ cyber data exfiltration… Cyber espionage Middle Eastern computer systems US & Israel Iran, Lebanon, Syria, Sudan, Occupied Territories of Israel Gauss 2011 - 2012 Cyber surveillance / Banking Trojan Middle Eastern Banks Unknown Lebanon, CitiBank & PayPal Batch Wiper 2012 Cyber Destruction Iranian Oil Infrastructure US & Israel Islamic Republic of Iran Weaponized Malware
