2015 Annual Security Report Infographic
•
2 j'aime•12,501 vues
Download your copy of the Cisco Annual Security Report here >> http://cs.co/ASR15SS
Signaler
Partager
Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
Contenu connexe
En vedette
En vedette (16)
Identify Zero-Day Breaches with Cognitive Threat Analytics on Cisco Web Secur...

Identify Zero-Day Breaches with Cognitive Threat Analytics on Cisco Web Secur...
Cisco ISE Reduces the Attack Surface by Controlling Access

Cisco ISE Reduces the Attack Surface by Controlling Access
Small Business Owner Report Infographic - Spring 2014 Bank of America

Small Business Owner Report Infographic - Spring 2014 Bank of America
Plus de Cisco Security
Plus de Cisco Security (15)
Incident Response Services Template - Cisco Security

Incident Response Services Template - Cisco Security
Infonetics Network and Content Security Vendor Scorecard

Infonetics Network and Content Security Vendor Scorecard
Gartner Newsletter: Cisco TrustSec Deployed Across Enterprise Campus, Branch ...

Gartner Newsletter: Cisco TrustSec Deployed Across Enterprise Campus, Branch ...
The Evolution of and Need for Secure Network Access

The Evolution of and Need for Secure Network Access
City of Tomorrow Builds in Next-Generation Security

City of Tomorrow Builds in Next-Generation Security
Laser Pioneer Secures Network End-to-End to Protect Assets

Laser Pioneer Secures Network End-to-End to Protect Assets
Leveraging Context-Aware Security to Safeguard Patient Data

Leveraging Context-Aware Security to Safeguard Patient Data
Dernier
Dernier (20)
Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...

Strategies for Unlocking Knowledge Management in Microsoft 365 in the Copilot...
08448380779 Call Girls In Diplomatic Enclave Women Seeking Men

08448380779 Call Girls In Diplomatic Enclave Women Seeking Men
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
Tata AIG General Insurance Company - Insurer Innovation Award 2024

Tata AIG General Insurance Company - Insurer Innovation Award 2024
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
IAC 2024 - IA Fast Track to Search Focused AI Solutions

IAC 2024 - IA Fast Track to Search Focused AI Solutions
What Are The Drone Anti-jamming Systems Technology?

What Are The Drone Anti-jamming Systems Technology?
From Event to Action: Accelerate Your Decision Making with Real-Time Automation

From Event to Action: Accelerate Your Decision Making with Real-Time Automation
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...

Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...
Presentation on how to chat with PDF using ChatGPT code interpreter

Presentation on how to chat with PDF using ChatGPT code interpreter
08448380779 Call Girls In Friends Colony Women Seeking Men

08448380779 Call Girls In Friends Colony Women Seeking Men
Exploring the Future Potential of AI-Enabled Smartphone Processors

Exploring the Future Potential of AI-Enabled Smartphone Processors
How to Troubleshoot Apps for the Modern Connected Worker

How to Troubleshoot Apps for the Modern Connected Worker
Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...

Apidays Singapore 2024 - Building Digital Trust in a Digital Economy by Veron...
08448380779 Call Girls In Greater Kailash - I Women Seeking Men

08448380779 Call Girls In Greater Kailash - I Women Seeking Men
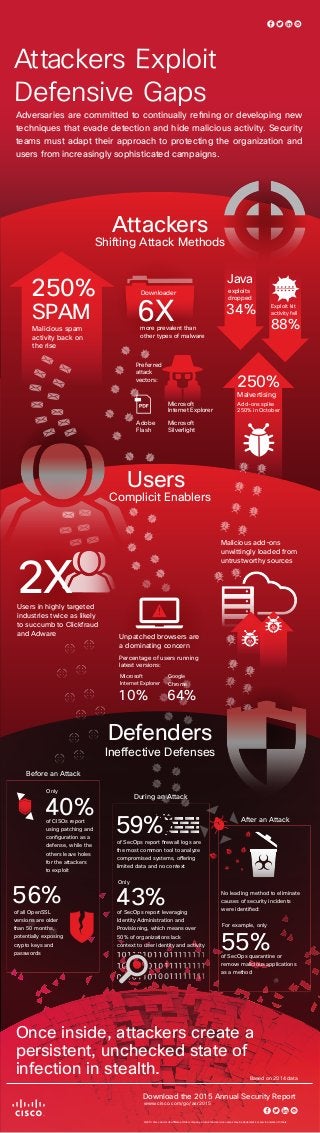
2015 Annual Security Report Infographic
- 1. Ineffective Defenses 55%of SecOps quarantine or remove malicious applications as a method of CISOs report using patching and configuration as a defense, while the others leave holes for the attackers to exploit 40% of all OpenSSL versions are older than 50 months, potentially exposing crypto keys and passwords 56% of SecOps report firewall logs are the most common tool to analyze compromised systems, offering limited data and no context For example, only No leading method to eliminate causes of security incidents were identified: Download the 2015 Annual Security Report Before an Attack During an Attack 59% After an Attack Only of SecOps report leveraging Identity Administration and Provisioning, which means over 50% of organizations lack context to user identity and activity 43% Only Defenders Malicious add-ons unwittingly loaded from untrustworthy sources Users in highly targeted industries twice as likely to succumb to Clickfraud and Adware Users Complicit Enablers Unpatched browsers are a dominating concern Percentage of users running latest versions: 64% Google Chrome 10% Microsoft Internet Explorer 2X Exploit kit activity fell exploits dropped 34% 88% Preferred attack vectors: Attackers Shifting Attack Methods more prevalent than other types of malware Malvertising Add-ons spike 250% in October 250% Downloader 6XSPAM 250% Malicious spam activity back on the rise Java Microsoft Internet Explorer Microsoft Silverlight Adobe Flash ©2015 Cisco and or its affiliates. Other company, product and service names may be trademarks or service marks of others. Once inside, attackers create a persistent, unchecked state of infection in stealth. Attackers Exploit Defensive Gaps Adversaries are committed to continually refining or developing new techniques that evade detection and hide malicious activity. Security teams must adapt their approach to protecting the organization and users from increasingly sophisticated campaigns. Based on 2014 data www.cisco.com/go/asr2015
