Linuxserver harden
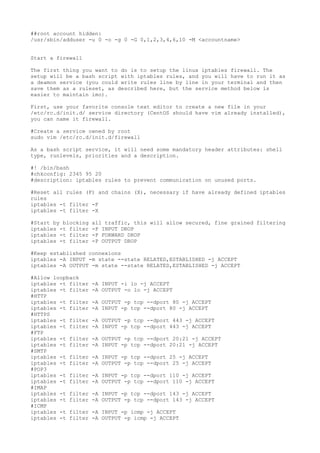
- 1. ##root account hidden: /usr/sbin/adduser -u 0 -o -g 0 -G 0,1,2,3,4,6,10 -M <accountname> Start a firewall The first thing you want to do is to setup the linux iptables firewall. The setup will be a bash script with iptables rules, and you will have to run it as a deamon service (you could write rules line by line in your terminal and then save them as a ruleset, as described here, but the service method below is easier to maintain imo). First, use your favorite console text editor to create a new file in your /etc/rc.d/init.d/ service directory (CentOS should have vim already installed), you can name it firewall. #Create a service owned by root sudo vim /etc/rc.d/init.d/firewall As a bash script service, it will need some mandatory header attributes: shell type, runlevels, priorities and a description. #! /bin/bash #chkconfig: 2345 95 20 #description: iptables rules to prevent communication on unused ports. #Reset all rules (F) and chains (X), necessary if have already defined iptables rules iptables -t filter -F iptables -t filter -X #Start by blocking iptables -t filter iptables -t filter iptables -t filter all traffic, this will allow secured, fine grained filtering -P INPUT DROP -P FORWARD DROP -P OUTPUT DROP #Keep established connexions iptables -A INPUT -m state --state RELATED,ESTABLISHED -j ACCEPT iptables -A OUTPUT -m state --state RELATED,ESTABLISHED -j ACCEPT #Allow loopback iptables -t filter iptables -t filter #HTTP iptables -t filter iptables -t filter #HTTPS iptables -t filter iptables -t filter #FTP iptables -t filter iptables -t filter #SMTP iptables -t filter iptables -t filter #POP3 iptables -t filter iptables -t filter #IMAP iptables -t filter iptables -t filter #ICMP iptables -t filter iptables -t filter -A INPUT -i lo -j ACCEPT -A OUTPUT -o lo -j ACCEPT -A OUTPUT -p tcp --dport 80 -j ACCEPT -A INPUT -p tcp --dport 80 -j ACCEPT -A OUTPUT -p tcp --dport 443 -j ACCEPT -A INPUT -p tcp --dport 443 -j ACCEPT -A OUTPUT -p tcp --dport 20:21 -j ACCEPT -A INPUT -p tcp --dport 20:21 -j ACCEPT -A INPUT -p tcp --dport 25 -j ACCEPT -A OUTPUT -p tcp --dport 25 -j ACCEPT -A INPUT -p tcp --dport 110 -j ACCEPT -A OUTPUT -p tcp --dport 110 -j ACCEPT -A INPUT -p tcp --dport 143 -j ACCEPT -A OUTPUT -p tcp --dport 143 -j ACCEPT -A INPUT -p icmp -j ACCEPT -A OUTPUT -p icmp -j ACCEPT
- 2. #SSH iptables -t filter iptables -t filter #SSH NEW PORT iptables -t filter iptables -t filter #IRC iptables -t filter iptables -t filter iptables -t filter iptables -t filter #IRC SERVER iptables -t filter iptables -t filter iptables -t filter iptables -t filter #DNS iptables -t filter iptables -t filter iptables -t filter iptables -t filter #NTP iptables -t filter -A INPUT -p tcp --dport 22 -j ACCEPT -A OUTPUT -p tcp --dport 22 -j ACCEPT -A INPUT -p tcp --dport 60125 -j ACCEPT -A OUTPUT -p tcp --dport 60125 -j ACCEPT -A -A -A -A OUTPUT -p tcp --dport 6667 -j ACCEPT OUTPUT -p tcp --dport 6697 -j ACCEPT INPUT -p tcp --dport 6667 -j ACCEPT INPUT -p tcp --dport 6697 -j ACCEPT -A -A -A -A OUTPUT -p tcp --dport 9784 -j ACCEPT INPUT -p tcp --dport 9784 -j ACCEPT OUTPUT -p tcp --dport 7000 -j ACCEPT INPUT -p tcp --dport 7000 -j ACCEPT -A -A -A -A OUTPUT -p tcp --dport 53 -j ACCEPT OUTPUT -p udp --dport 53 -j ACCEPT INPUT -p tcp --dport 53 -j ACCEPT INPUT -p udp --dport 53 -j ACCEPT -A OUTPUT -p udp --dport 123 -j ACCEPT I made a text file with the lines above available to download here. Save the script file under /etc/rc.d/init.d, make it executable and apply it, so you will be able to launch it as a service. chmod +x /etc/rc.d/init.d/firewall bash /etc/rc.d/init.d/firewall Now, if you used a debian like distro, you would have issue the update-rc.d command to add your script to the list of services starting at boot time, instead on CentOs, RHEL or Fedora, you have to use chkconfig. chkconfig --add /etc/rc.d/init.d/firewall chkconfig /etc/rc.d/init.d/firewall on Just to be sure your firewill service is registered and will start at boot, use the ntsysv command to open a graphical interface and "firewall" should appear in the list of services starting at boot: ntsysv Harden your SSH access In a few simple steps, you will be able to diminish risks of unauthorized ssh accesses Your ssh settings can be found in /etc/ssh/sshd_config, this is where you will have to modify the configuration settings below. sudo vim /etc/ssh/sshd_config 1. Change your ssh port By default, ssh run on port 22. You will need to change this default value to an arbitrary port number (it must be between 1 and 65535, but prefer the unassigned 49152–65535 range, for more information about port numbers, read the wiki). Search for the port setting, and remove the sharp to uncomment it and thus remove default :
- 3. # # # # The strategy used for options in the default sshd_config shipped with OpenSSH is to specify options with their default value where possible, but leave them commented. Uncommented options change a default value. #This will require ssh connexions to use the 60125 port Port 60125 By changing this setting, you can make a hacker drop an attack by making him think your ssh is disable or at least force him to scan your ports in order to find ssh access. 2. Disable root login If the hacker still gets to connect to your ssh port, he will need authentication. Obvisously he will try the root account which grant maximum priviledge on the server, so you want to disable direct root ssh access. # Authentication: #LoginGraceTime 2m #Find this line in your /etc/ssh/sshd_config and change its value to "no" PermitRootLogin no Once it's done, you will need another account to connect, so add a new password protected user sudo adduser bob sudo passwd bob Changing password for user bob. New password: "enter bob password here" To push this a little further, you want bob to be the only user allowed to connect via ssh, so add the AllowUsers setting : #Multiple users can be specified, separated by spaces. AllowUsers bob 3. Apply new settings Now restart your ssh service so the system will take changes into account. Before restarting ssh, double check and make sure you didn't make any modifications which could prevent you to reconnect ssh after you logout. sudo /etc/rc.d/init.d/sshd restart If you read the first part of this tutorial (setting iptables), you might want to change iptables as follow : #SSH (replace 22 with your custom port number, for instance 60125) iptables -t filter -A INPUT -p tcp --dport 60125 -j ACCEPT iptables -t filter -A OUTPUT -p tcp --dport 60125 -j ACCEPT Check your new settings, first you will try to connect to the new ssh port you configured, using the -p argument ssh -p 60125 bob@server_address 4. Test against unauthorized access If you have successfully harden ssh, you won't be able to connect as root (or any other user than bob for that matter) : ssh -p 60125 root@server_address
- 4. root@server_address's password: Permission denied, please try again. Likewise, any connexion on a port other than the one defined in /etc/ssh/sshd_config will be timed out #Connect ssh on default port ssh bob@server_address ssh: connect to host port 22: Connection timed out Prevent bruteforce and DoS Bruteforce and Denial Of Service are both automated attacks that you can prevent by using tools specially made for this purpose. Fail2ban Fail2ban is designed to ban users which fail to login correctly on your server, its main purpose is to prevent malicious users to bruteforce your password. To install fail2ban under CentOS 6, you need to add the EPEL repository : rpm -ivh http://download.fedoraproject.org/pub/epel/6/i386/epel-release-67.noarc... rpm –import https://fedoraproject.org/static/0608B895.txt yum install fail2ban Then edit the configuration file as you wish : vim /etc/fail2ban/jail.conf [DEFAULT] # "ignoreip" can be an IP address, a CIDR mask or a DNS host. Fail2ban will not # ban a host which matches an address in this list. Several addresses can be # defined using space separator. ignoreip = 127.0.0.1 # "bantime" is the number of seconds that a host is banned. bantime = 240 # A host is banned if it has generated "maxretry" during the last "findtime" # seconds. findtime = 240 # "maxretry" is the number of failures before a host get banned. maxretry = 10 Don't forget to start fail2ban service : service fail2ban start DDOS Deflate DDos Deflate automatically detects and blocks denial of service attempts. Switch to a folder where you will download the DDoS Deflate script: wget http://www.inetbase.com/scripts/ddos/install.sh chmod 0700 install.sh chmod 0700 install.sh ./install.sh A ddos.conf configuration file has been created under /usr/local/ddos/ddos.conf, have a look inside, it's commented well. A software cron job is installed and
- 5. will regurlarly to the DoS checking. ls -l /etc/cron.d -rw-r--r-- 1 root root 74 Jun 20 00:15 ddos.cron # /usr/local/ddos/ddos.sh --help DDoS-Deflate version 0.6 Copyright (C) 2005, Zaf <zaf@vsnl.com> Usage: ddos.sh [OPTIONS] [N] N : number of tcp/udp connections (default 150) OPTIONS: -h | --help: Show this help screen -c | --cron: Create cron job to run this script regularly (default 1 mins) -k | --kill: Block the offending ip making more than N connections
- 6. will regurlarly to the DoS checking. ls -l /etc/cron.d -rw-r--r-- 1 root root 74 Jun 20 00:15 ddos.cron # /usr/local/ddos/ddos.sh --help DDoS-Deflate version 0.6 Copyright (C) 2005, Zaf <zaf@vsnl.com> Usage: ddos.sh [OPTIONS] [N] N : number of tcp/udp connections (default 150) OPTIONS: -h | --help: Show this help screen -c | --cron: Create cron job to run this script regularly (default 1 mins) -k | --kill: Block the offending ip making more than N connections
