Phishing & Cyber Attack Awareness
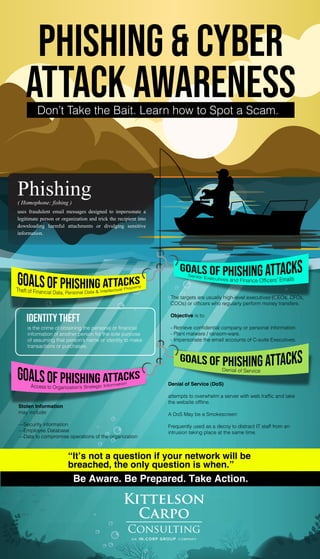
- 1. PHISHING & CYBER ATTACK AWARENESSDon’t Take the Bait. Learn how to Spot a Scam. Phishing( Homophone: fishing ) uses fraudulent email messages designed to impersonate a legitimate person or organization and trick the recipient into downloading harmful attachments or divulging sensitive information. Identity Theft is the crime of obtaining the personal or financial information of another person for the sole purpose of assuming that person’s name or identity to make transactions or purchases. The targets are usually high-level executives (CEOs, CFOs, COOs) or officers who regularly perform money transfers. Objective is to: - Retrieve confidential company or personal information. - Plant malware / ransom-ware. - Impersonate the email accounts of C-suite Executives. Stolen Information may include: —Security information —Employee Database —Data to compromise operations of the organization Denial of Service (DoS) attempts to overwhelm a server with web traffic and take the website offline. A DoS May be a Smokescreen Frequently used as a decoy to distract IT staff from an intrusion taking place at the same time. “It’s not a question if your network will be breached, the only question is when.” Be Aware. Be Prepared. Take Action.
- 2. PHISHING & CYBER ATTACK AWARENESSDon’t Take the Bait. Learn how to Spot a Scam. Phishing( Homophone: fishing ) uses fraudulent email messages designed to impersonate a legitimate person or organization and trick the recipient into downloading harmful attachments or divulging sensitive information. “It’s not a question if your network will be breached, the only question is when.” Be Aware. Be Prepared. Take Action. Whattodo? Treat any email attachments with a healthy suspicion. In case of doubt, seek assistance from the IT Officer. In case of a compromise,immediately change yourpassword. Inform stakeholders about thescam to prevent any theft, breachor unauthorized transaction. Always encrypt email attachments containing sensitive information. Change email password every 3 months. Always check the Sender’s email address before taking on any sensitive transaction. Some phishing may also appear as Password Expiration Alert Embedded links in an email may redirect you to an unsecure website that requests sensitive information Report phishing email to the IT Officer.
- 3. PHISHING & CYBER ATTACK AWARENESSDon’t Take the Bait. Learn how to Spot a Scam. Phishing( Homophone: fishing ) uses fraudulent email messages designed to impersonate a legitimate person or organization and trick the recipient into downloading harmful attachments or divulging sensitive information. “It’s not a question if your network will be breached, the only question is when.” Be Aware. Be Prepared. Take Action. Whattodo? Treat any email attachments with a healthy suspicion. In case of doubt, seek assistance from the IT Officer. In case of a compromise,immediately change yourpassword. Inform stakeholders about thescam to prevent any theft, breachor unauthorized transaction. Always encrypt email attachments containing sensitive information. Change email password every 3 months. Always check the Sender’s email address before taking on any sensitive transaction. Attachments may contain malware which can lead to data breach when opened. A Trojan via a malicious email attachment or ad may be installed which will allow attacker to exploit loopholes and obtain sensitive information. Report phishing email to the IT Officer.
- 4. PHISHING & CYBER ATTACK AWARENESSDon’t Take the Bait. Learn how to Spot a Scam. Phishing( Homophone: fishing ) uses fraudulent email messages designed to impersonate a legitimate person or organization and trick the recipient into downloading harmful attachments or divulging sensitive information. “It’s not a question if your network will be breached, the only question is when.” Be Aware. Be Prepared. Take Action. Whattodo? Treat any email attachments with a healthy suspicion. In case of doubt, seek assistance from the IT Officer. In case of a compromise,immediately change yourpassword. Inform stakeholders about thescam to prevent any theft, breachor unauthorized transaction. Always encrypt email attachments containing sensitive information. Change email password every 3 months. Always check the Sender’s email address before taking on any sensitive transaction. Clicking links can authorize certain instructions leading to data breach or identity theft. Report phishing email to the IT Officer.
- 5. PHISHING & CYBER ATTACK AWARENESSDon’t Take the Bait. Learn how to Spot a Scam. Phishing( Homophone: fishing ) uses fraudulent email messages designed to impersonate a legitimate person or organization and trick the recipient into downloading harmful attachments or divulging sensitive information. “It’s not a question if your network will be breached, the only question is when.” Be Aware. Be Prepared. Take Action. Whattodo? Treat any email attachments with a healthy suspicion. In case of doubt, seek assistance from the IT Officer. In case of a compromise,immediately change yourpassword. Inform stakeholders about thescam to prevent any theft, breachor unauthorized transaction. Always encrypt email attachments containing sensitive information. Change email password every 3 months. Always check the Sender’s email address before taking on any sensitive transaction. Clicking links can authorize certain instructions leading to data breach or identity theft. Report phishing email to the IT Officer.
- 6. PHISHING & CYBER ATTACK AWARENESSDon’t Take the Bait. Learn how to Spot a Scam. Phishing( Homophone: fishing ) uses fraudulent email messages designed to impersonate a legitimate person or organization and trick the recipient into downloading harmful attachments or divulging sensitive information. “It’s not a question if your network will be breached, the only question is when.” Be Aware. Be Prepared. Take Action. Whattodo? Treat any email attachments with a healthy suspicion. In case of doubt, seek assistance from the IT Officer. In case of a compromise,immediately change yourpassword. Inform stakeholders about thescam to prevent any theft, breachor unauthorized transaction. Always encrypt email attachments containing sensitive information. Change email password every 3 months. Always check the Sender’s email address before taking on any sensitive transaction. Report phishing email to the IT Officer. Attackers spoof the email addresses of Senior Executives to appear as a reputable source and provide instructions to employees who normally or usually process fund transfer instructions.
