Request For Comments (RFC)
•
0 j'aime•68 vues
Did you know about April RFCs?
Signaler
Partager
Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
LCNA14: Why Use Xen for Large Scale Enterprise Deployments? - Konrad Rzeszute...

LCNA14: Why Use Xen for Large Scale Enterprise Deployments? - Konrad Rzeszute...The Linux Foundation
Contenu connexe
Similaire à Request For Comments (RFC)
LCNA14: Why Use Xen for Large Scale Enterprise Deployments? - Konrad Rzeszute...

LCNA14: Why Use Xen for Large Scale Enterprise Deployments? - Konrad Rzeszute...The Linux Foundation
Similaire à Request For Comments (RFC) (20)
Kernel Recipes 2015: Kernel packet capture technologies

Kernel Recipes 2015: Kernel packet capture technologies
Inria Tech Talk : RIOT, l'OS libre pour vos objets connectés #IoT

Inria Tech Talk : RIOT, l'OS libre pour vos objets connectés #IoT
Dataplane programming with eBPF: architecture and tools

Dataplane programming with eBPF: architecture and tools
LCNA14: Why Use Xen for Large Scale Enterprise Deployments? - Konrad Rzeszute...

LCNA14: Why Use Xen for Large Scale Enterprise Deployments? - Konrad Rzeszute...
Advanced TCP/IP-based Industrial Networking for Engineers & Technicians

Advanced TCP/IP-based Industrial Networking for Engineers & Technicians
Cisco Live! :: Introduction to IOS XR for Enterprises and Service Providers

Cisco Live! :: Introduction to IOS XR for Enterprises and Service Providers
Plus de Subhajit Sahu
Plus de Subhajit Sahu (20)
DyGraph: A Dynamic Graph Generator and Benchmark Suite : NOTES

DyGraph: A Dynamic Graph Generator and Benchmark Suite : NOTES
A Dynamic Algorithm for Local Community Detection in Graphs : NOTES

A Dynamic Algorithm for Local Community Detection in Graphs : NOTES
Scalable Static and Dynamic Community Detection Using Grappolo : NOTES

Scalable Static and Dynamic Community Detection Using Grappolo : NOTES
Application Areas of Community Detection: A Review : NOTES

Application Areas of Community Detection: A Review : NOTES
Dynamic Batch Parallel Algorithms for Updating PageRank : POSTER

Dynamic Batch Parallel Algorithms for Updating PageRank : POSTER
Abstract for IPDPS 2022 PhD Forum on Dynamic Batch Parallel Algorithms for Up...

Abstract for IPDPS 2022 PhD Forum on Dynamic Batch Parallel Algorithms for Up...
Fast Incremental Community Detection on Dynamic Graphs : NOTES

Fast Incremental Community Detection on Dynamic Graphs : NOTES
Can you fix farming by going back 8000 years : NOTES

Can you fix farming by going back 8000 years : NOTES
Basic Computer Architecture and the Case for GPUs : NOTES

Basic Computer Architecture and the Case for GPUs : NOTES
Dynamic Batch Parallel Algorithms for Updating Pagerank : SLIDES

Dynamic Batch Parallel Algorithms for Updating Pagerank : SLIDES
Taxation for Traders < Markets and Taxation : NOTES

Taxation for Traders < Markets and Taxation : NOTES
A Generalization of the PageRank Algorithm : NOTES

A Generalization of the PageRank Algorithm : NOTES
ApproxBioWear: Approximating Additions for Efficient Biomedical Wearable Comp...

ApproxBioWear: Approximating Additions for Efficient Biomedical Wearable Comp...
Youngistaan Foundation: Annual Report 2020-21 : NOTES

Youngistaan Foundation: Annual Report 2020-21 : NOTES
Dernier
call girls in Anand Vihar (delhi) call me [🔝9953056974🔝] escort service 24X7![call girls in Anand Vihar (delhi) call me [🔝9953056974🔝] escort service 24X7](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![call girls in Anand Vihar (delhi) call me [🔝9953056974🔝] escort service 24X7](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
call girls in Anand Vihar (delhi) call me [🔝9953056974🔝] escort service 24X79953056974 Low Rate Call Girls In Saket, Delhi NCR
Dernier (20)
Abu Dhabi Escorts Service 0508644382 Escorts in Abu Dhabi

Abu Dhabi Escorts Service 0508644382 Escorts in Abu Dhabi
2nd Solid Symposium: Solid Pods vs Personal Knowledge Graphs

2nd Solid Symposium: Solid Pods vs Personal Knowledge Graphs
Best SEO Services Company in Dallas | Best SEO Agency Dallas

Best SEO Services Company in Dallas | Best SEO Agency Dallas
"Boost Your Digital Presence: Partner with a Leading SEO Agency"

"Boost Your Digital Presence: Partner with a Leading SEO Agency"
Top profile Call Girls In Dindigul [ 7014168258 ] Call Me For Genuine Models ...![Top profile Call Girls In Dindigul [ 7014168258 ] Call Me For Genuine Models ...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![Top profile Call Girls In Dindigul [ 7014168258 ] Call Me For Genuine Models ...](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
Top profile Call Girls In Dindigul [ 7014168258 ] Call Me For Genuine Models ...
20240508 QFM014 Elixir Reading List April 2024.pdf

20240508 QFM014 Elixir Reading List April 2024.pdf
call girls in Anand Vihar (delhi) call me [🔝9953056974🔝] escort service 24X7![call girls in Anand Vihar (delhi) call me [🔝9953056974🔝] escort service 24X7](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![call girls in Anand Vihar (delhi) call me [🔝9953056974🔝] escort service 24X7](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
call girls in Anand Vihar (delhi) call me [🔝9953056974🔝] escort service 24X7
Tadepalligudem Escorts Service Girl ^ 9332606886, WhatsApp Anytime Tadepallig...

Tadepalligudem Escorts Service Girl ^ 9332606886, WhatsApp Anytime Tadepallig...
APNIC Policy Roundup, presented by Sunny Chendi at the 5th ICANN APAC-TWNIC E...

APNIC Policy Roundup, presented by Sunny Chendi at the 5th ICANN APAC-TWNIC E...
Russian Call girls in Abu Dhabi 0508644382 Abu Dhabi Call girls

Russian Call girls in Abu Dhabi 0508644382 Abu Dhabi Call girls
20240507 QFM013 Machine Intelligence Reading List April 2024.pdf

20240507 QFM013 Machine Intelligence Reading List April 2024.pdf
Mira Road Housewife Call Girls 07506202331, Nalasopara Call Girls

Mira Road Housewife Call Girls 07506202331, Nalasopara Call Girls
best call girls in Hyderabad Finest Escorts Service 📞 9352988975 📞 Available ...

best call girls in Hyderabad Finest Escorts Service 📞 9352988975 📞 Available ...
20240510 QFM016 Irresponsible AI Reading List April 2024.pdf

20240510 QFM016 Irresponsible AI Reading List April 2024.pdf
Request For Comments (RFC)
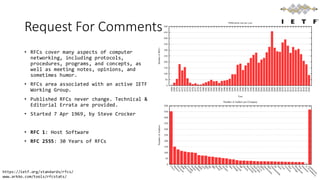
- 1. Request For Comments • RFCs cover many aspects of computer networking, including protocols, procedures, programs, and concepts, as well as meeting notes, opinions, and sometimes humor. • RFCs area associated with an active IETF Working Group. • Published RFCs never change. Technical & Editorial Errata are provided. • Started 7 Apr 1969, by Steve Crocker • RFC 1: Host Software • RFC 2555: 30 Years of RFCs https://ietf.org/standards/rfcs/ www.arkko.com/tools/rfcstats/
- 2. IETF Working Groups • Applications & Real-Time area (29) • General area (2) • Internet area (17) • Operations & Management area (14) • Routing area (24) • Secutiry area (25) • Transport area (11) https://ietf.org/standards/rfcs/ https://datatracker.ietf.org/wg/ www.arkko.com/tools/rfcstats/
- 3. April RFCs • RFC527:ARPAWOCKY (1973) Beware the ARPANET, my son; The bits that byte, the heads that scratch; Beware the NCP, and shun the frumious system patch, • RFC7511: Scenic Routing for IPv6 (2015) This document specifies a new routing scheme for the current version of the Internet Protocol version 6 (IPv6) in the spirit of "Green IT", whereby packets will be routed to get as much fresh-air time as possible. • RFC2549: IP over AvianCarriers withQuality of Service (1999) The following quality of service levels are available: Concorde, First, Business, and Coach. Concorde class offers expedited data delivery. One major benefit to using Avian Carriers is that this is the only networking technology that earns frequent flyer miles, plus the Concorde and First classes of service earn 50% bonus miles per packet. Ostriches are an alternate carrier that have much greater bulk transfer capability but provide slower delivery, and require the use of bridges between domains. IPoAC: IP over Avian Carriers RFC 3514 The Security Flag in the IPv4 Header 1 April 2003 The bit field is laid out as follows: 0 +-+ |E| +-+ Currently-assigned values are defined as follows: 0x0 If the bit is set to 0, the packet has no evil intent. Hosts, network elements, etc., SHOULD assume that the packet is harmless, and SHOULD NOT take any defensive measures. (We note that this part of the spec is already implemented by many common desktop operating systems.) 0x1 If the bit is set to 1, the packet has evil intent. Secure systems SHOULD try to defend themselves against such packets. Insecure systems MAY chose to crash, be penetrated, etc.
