Artificial intelligence bsc - iso 27001 information security
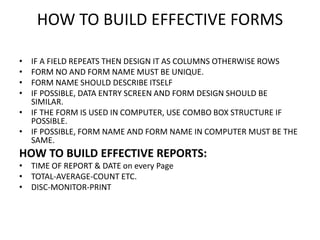
- 1. HOW TO BUILD EFFECTIVE FORMS • IF A FIELD REPEATS THEN DESIGN IT AS COLUMNS OTHERWISE ROWS • FORM NO AND FORM NAME MUST BE UNIQUE. • FORM NAME SHOULD DESCRIBE ITSELF • IF POSSIBLE, DATA ENTRY SCREEN AND FORM DESIGN SHOULD BE SIMILAR. • IF THE FORM IS USED IN COMPUTER, USE COMBO BOX STRUCTURE IF POSSIBLE. • IF POSSIBLE, FORM NAME AND FORM NAME IN COMPUTER MUST BE THE SAME. HOW TO BUILD EFFECTIVE REPORTS: • TIME OF REPORT & DATE on every Page • TOTAL-AVERAGE-COUNT ETC. • DISC-MONITOR-PRINT
- 2. What is BALANCED SCORECARD?
- 4. Don’t forget to read the following paper ! • Cebeci, U. (2009). Fuzzy AHP-based decision support system for selecting ERP systems in textile industry by using balanced scorecard. Expert Systems with Applications, 36(5), 8900-8909.
- 5. ARTIFICIAL INTELLIGENCE • EXPERT SYSTEMS-(Chess Game, DIAGNOSIS • FUZZY LOGIC • PATTERN RECOGNITION • ROBOTICS • MACHINE LEARNING • NATURAL LANGUAGE PROCESSING • SEARCH ENGINES • NEURAL NETWORKS • GENETIC ALGORITHMS
- 6. TG4.1 Introduction to Intelligent Systems Intelligent systems Artificial intelligence (AI) © Luis Alonso Ocana/Age Fotostock America, Inc.
- 7. TG 4.2 Expert Systems Expertise Expert systems (ESs)
- 8. Expertise Transfer from Human to Computer Knowledge acquisition Knowledge representation Knowledge inferencing Knowledge transfer
- 9. The Components of Expert Systems Knowledge base Inference engine User interface Blackboard Explanation subsystem
- 11. TG 4.5 Genetic Algorithms Genetic algorithms have three functional characteristics: • Selection • Crossover: • Mutation:
- 12. TG 4.6 Intelligent Agents Information Agents Monitoring-and-Surveillance Agents User Agents
- 13. Fuzzy Logic • By using fuzzy logic, we can convert some linguistic variables to numbers so that we can process the values in computers. • Define membership function : to be tall for turkish boys • (Example: To be old)
- 15. Information Security Management System (ISMS) ISO 27001 Standard
- 16. What is ISMS? • That part of the overall management system, based on a business risk approach, to establish, implement, operate, monitor, review, maintain and improve information security. (ISO/IEC 27001:2005 Clause 3.7)
- 17. INFORMATION SECURITY MANAGEMENT Factors affecting ISMS Escalating Risk Globalization Legislation Government NGOs Competition - cost Corporate culture Employee Union Corporate vision & policy Shareholder Customer requirements Consumer Competition- business Neighbor Societal values Risk tolerance Insurance
- 18. Compatibility with other standards • ISO 9001 Quality Management Systems – requirements • ISO 14001 Environmental Management Systems – specification with guidance for use
- 19. PURPOSE OF ISO 27001
- 20. Benefits of ISMS • To protect an organization’s information assets in order to: ensure business continuity, minimize business damage, and maximize return on investments • Internationally recognized, structured methodology • Defined process to evaluate, implement, maintain, and manage information security, • Tailored policies, standards, procedures, and guidelines
- 21. Benefits of ISMS • Efficient and effective security planning and management • Increased credibility, trust and confidence of partners and customers • Compliance to all relevant commitment • Compatibility with other standards
- 23. Plan-Do-Check-Act cycle & Continual Improvement Take actions to continually improve process performance – effectiveness and efficiency Establish objectives necessary to deliver results in accordance with customer requirements and the organization’s policies Implement the processesMonitor and measure processes and product against policies, objectives and requirements
- 24. PDCA Model applied to ISMS processes
- 27. ISO 27001 Requirements • 1 Scope – 1.1 General – 1.2 Application • 2 Normative References • 3 Term and definitions • 4 Information security management system – 4.1 General requirements – 4.2 Establishing and managing the ISMS – 4.3 Documentation requirements
- 28. ISO 27001 Requirements • 5 Management Responsibility – 5.1 Management commitment – 5.2 Resource management • 6 Internal ISMS audits • 7 Management review of the ISMS – 7.1 General – 7.2 Review input – 7.3 Review output
- 29. ISO 27001 Requirements • 8 ISMS Improvement – 8.1 Continual improvement – 8.2 Corrective action – 8.3 Preventive action
- 30. Audit / Certification Process Pre-assessment (Optional) Stage 1: Desk Study Stage 2: Certification Audit Surveillance 1 Surveillance 2 Surveillance 3 Surveillance 3 Surveillance 5 Stage 1: Desk Study •Evaluate the location and site- specific conditions •Collection of information regarding the scope of supply chain SMS, information about risk assessment performed and processes •Relevant ISMS documentation and records •Previous audit reports Stage 2: Certification Audit •Obtain information and evidence about conformity to all requirements of the applicable normative document •Operational control •Internal auditing and Management review Surveillance Audits •Maintenance visits •Verify continuous implementation of the system in accordance with the requirements of the standard •Evaluation of the effectiveness of corrective action implementation to previously raised NCs
- 31. Failure Mode and Effects Analysis Technique for Information Security
- 32. • Fill the second line above (fire risk) for the company