Exploit Kits In A Post-Angler Era
•
0 j'aime•597 vues
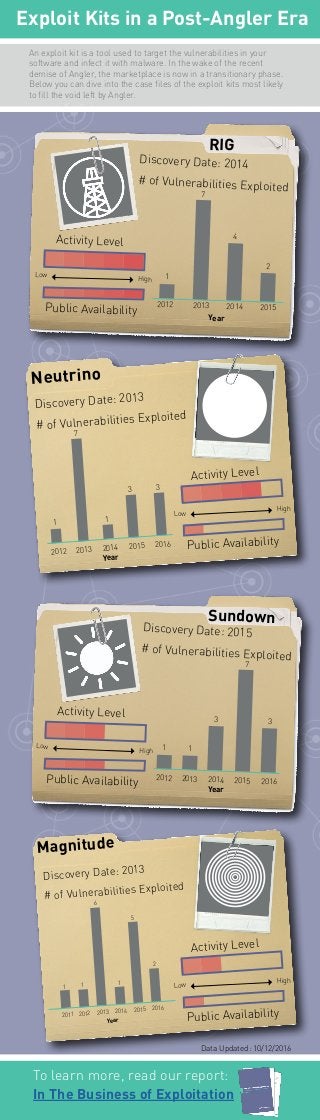
Dive into the case files of the exploit kits most likely to fill the void left by Angler. Get full report on exploit kits: http://ow.ly/lJue3057k5Z
Signaler
Partager
Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
Recommandé
Contenu connexe
En vedette
En vedette (8)
Tema 2 la península ibérica en la edad media al andalus

Tema 2 la península ibérica en la edad media al andalus
Alternative Financing Solutions for SME by Xavier Corman - FinTech Belgium Su...

Alternative Financing Solutions for SME by Xavier Corman - FinTech Belgium Su...
5 Programming Languages And Tools Data Scientists Use Now

5 Programming Languages And Tools Data Scientists Use Now
Plus de Digital Shadows
Plus de Digital Shadows (20)
Digital Shadows and the NIST Cyber Security Framework

Digital Shadows and the NIST Cyber Security Framework
Mapping the ASD Essential 8 to the Mitre ATTACK™ framework

Mapping the ASD Essential 8 to the Mitre ATTACK™ framework
Mitre ATT&CK and the Mueller GRU Indictment: Lessons for Organizations

Mitre ATT&CK and the Mueller GRU Indictment: Lessons for Organizations
Mitre ATTACK and the North Korean Regime-Backed Programmer

Mitre ATTACK and the North Korean Regime-Backed Programmer
Digital Shadows and Demisto Enterprise Integration Datasheet

Digital Shadows and Demisto Enterprise Integration Datasheet
Digital Shadows and Palo Alto Networks Integration Datasheet

Digital Shadows and Palo Alto Networks Integration Datasheet
Energy and Utilities Firm Increases Productivity by Reducing False Positives

Energy and Utilities Firm Increases Productivity by Reducing False Positives
Source Code and Admin Password Shared on Public Site by Developer

Source Code and Admin Password Shared on Public Site by Developer
Dernier
💉💊+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHABI}}+971581248768
+971581248768 Mtp-Kit (500MG) Prices » Dubai [(+971581248768**)] Abortion Pills For Sale In Dubai, UAE, Mifepristone and Misoprostol Tablets Available In Dubai, UAE CONTACT DR.Maya Whatsapp +971581248768 We Have Abortion Pills / Cytotec Tablets /Mifegest Kit Available in Dubai, Sharjah, Abudhabi, Ajman, Alain, Fujairah, Ras Al Khaimah, Umm Al Quwain, UAE, Buy cytotec in Dubai +971581248768''''Abortion Pills near me DUBAI | ABU DHABI|UAE. Price of Misoprostol, Cytotec” +971581248768' Dr.DEEM ''BUY ABORTION PILLS MIFEGEST KIT, MISOPROTONE, CYTOTEC PILLS IN DUBAI, ABU DHABI,UAE'' Contact me now via What's App…… abortion Pills Cytotec also available Oman Qatar Doha Saudi Arabia Bahrain Above all, Cytotec Abortion Pills are Available In Dubai / UAE, you will be very happy to do abortion in Dubai we are providing cytotec 200mg abortion pill in Dubai, UAE. Medication abortion offers an alternative to Surgical Abortion for women in the early weeks of pregnancy. We only offer abortion pills from 1 week-6 Months. We then advise you to use surgery if its beyond 6 months. Our Abu Dhabi, Ajman, Al Ain, Dubai, Fujairah, Ras Al Khaimah (RAK), Sharjah, Umm Al Quwain (UAQ) United Arab Emirates Abortion Clinic provides the safest and most advanced techniques for providing non-surgical, medical and surgical abortion methods for early through late second trimester, including the Abortion By Pill Procedure (RU 486, Mifeprex, Mifepristone, early options French Abortion Pill), Tamoxifen, Methotrexate and Cytotec (Misoprostol). The Abu Dhabi, United Arab Emirates Abortion Clinic performs Same Day Abortion Procedure using medications that are taken on the first day of the office visit and will cause the abortion to occur generally within 4 to 6 hours (as early as 30 minutes) for patients who are 3 to 12 weeks pregnant. When Mifepristone and Misoprostol are used, 50% of patients complete in 4 to 6 hours; 75% to 80% in 12 hours; and 90% in 24 hours. We use a regimen that allows for completion without the need for surgery 99% of the time. All advanced second trimester and late term pregnancies at our Tampa clinic (17 to 24 weeks or greater) can be completed within 24 hours or less 99% of the time without the need surgery. The procedure is completed with minimal to no complications. Our Women's Health Center located in Abu Dhabi, United Arab Emirates, uses the latest medications for medical abortions (RU-486, Mifeprex, Mifegyne, Mifepristone, early options French abortion pill), Methotrexate and Cytotec (Misoprostol). The safety standards of our Abu Dhabi, United Arab Emirates Abortion Doctors remain unparalleled. They consistently maintain the lowest complication rates throughout the nation. Our Physicians and staff are always available to answer questions and care for women in one of the most difficult times in their lives. The decision to have an abortion at the Abortion Cl+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...?#DUbAI#??##{{(☎️+971_581248768%)**%*]'#abortion pills for sale in dubai@
Dernier (20)
Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood

Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...
CNIC Information System with Pakdata Cf In Pakistan

CNIC Information System with Pakdata Cf In Pakistan
Apidays New York 2024 - APIs in 2030: The Risk of Technological Sleepwalk by ...

Apidays New York 2024 - APIs in 2030: The Risk of Technological Sleepwalk by ...
Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...

Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...
Spring Boot vs Quarkus the ultimate battle - DevoxxUK

Spring Boot vs Quarkus the ultimate battle - DevoxxUK
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
Modular Monolith - a Practical Alternative to Microservices @ Devoxx UK 2024

Modular Monolith - a Practical Alternative to Microservices @ Devoxx UK 2024
Rising Above_ Dubai Floods and the Fortitude of Dubai International Airport.pdf

Rising Above_ Dubai Floods and the Fortitude of Dubai International Airport.pdf
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
EMPOWERMENT TECHNOLOGY GRADE 11 QUARTER 2 REVIEWER

EMPOWERMENT TECHNOLOGY GRADE 11 QUARTER 2 REVIEWER
ICT role in 21st century education and its challenges

ICT role in 21st century education and its challenges
Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME

Cloud Frontiers: A Deep Dive into Serverless Spatial Data and FME
Exploit Kits In A Post-Angler Era
- 1. Exploit Kits in a Post-Angler Era Magnitude Discovery Date: 2013 # of Vulnerabilities Exploited Year 20122011 2013 2014 2015 2016 6 1 1 1 5 2 Neutrino Discovery Date: 2013 # of Vulnerabilities Exploited Activity Level 2013 Year 2012 2014 2015 2016 7 1 1 3 3 RIG Sundown Activity Level Low High Discovery Date: 2014 # of Vulnerabilities Exploited An exploit kit is a tool used to target the vulnerabilities in your software and infect it with malware. In the wake of the recent demise of Angler, the marketplace is now in a transitionary phase. Below you can dive into the case files of the exploit kits most likely to fill the void left by Angler. Year 1 2012 2013 2014 2015 7 4 2 Discovery Date: 2015 # of Vulnerabilities Exploited 2013 Year 2012 2014 2015 2016 1 1 3 3 7 To learn more, read our report: In The Business of Exploitation Data Updated: 10/12/2016 Public Availability Low High Public Availability Activity Level Low High Public Availability Activity Level Low High Public Availability
