SPENTREP - New Crime by Group 4 (2013.Sep.9)
•
0 j'aime•286 vues
SPENTREP - New Crime by Group 4 (2013.Sep.9)
Signaler
Partager
Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
Recommandé
CHIME LEAD New York 2014 "Case Studies from the Field: Putting Cyber Security Strategies into Action"
Learn from those in the trenches who have deployed effective cyber strategies in their organizations, foiled attacks and managed breach situations. Learn approaches for success and pitfalls to avoid by exploring the experience of others with deployment and management of cyber security strategies and plans.
Learning Objectives:
Identify successes, challenges and lessons learned with implementation of cyber strategies
Identify success strategies for gaining the C Suite support and ways cyber security can be integrated into the organization's culture and work processes.
Identify best practices with anticipating new and emerging threats and ways to maintain a proactive position instead of reactive
Identify approaches for breach preparation and breach management
Featured Speakers:
Neal Ganguly, MBA, FCHIME, FHIMSS, CHCIO
VP & CIO
JFK Health System
Miroslav Belote
Director of IT – Infrastructure and Information Security Officer
JFK Health System
Nassar Nizami
CISO
Yale-New Haven Health SystemCHIME LEAD New York 2014 "Case Studies from the Field: Putting Cyber Security...

CHIME LEAD New York 2014 "Case Studies from the Field: Putting Cyber Security...Health IT Conference – iHT2
LILAC 2014 Keynote SpeakerWhat value and benefits do we add? Why information professionals are essentia...

What value and benefits do we add? Why information professionals are essentia...IL Group (CILIP Information Literacy Group)
Webinar Next Week: Beyond Online Intake: Looking at Triage and Expert Systems

Webinar Next Week: Beyond Online Intake: Looking at Triage and Expert SystemsLegal Services National Technology Assistance Project (LSNTAP)
The Digital Marketing tech stack is expending every day. With so many tools at our fingertips we have the potential to accomplish more than ever before. But hidden issues with the people, processes, and technology in your dept can lead too lost time, lost opportunity, and invalid decisions. Using real world examples from leading companies around the globe, we'll teach you how to identify gaps in your data landscape, find solutions, and turn them into opportunities using resources you already have.How to Master your Marketing Data - Cody Crumrine, Data Aptitude

How to Master your Marketing Data - Cody Crumrine, Data AptitudeDigiMarCon - Digital Marketing, Media and Advertising Conferences & Exhibitions
Contenu connexe
Similaire à SPENTREP - New Crime by Group 4 (2013.Sep.9)
CHIME LEAD New York 2014 "Case Studies from the Field: Putting Cyber Security Strategies into Action"
Learn from those in the trenches who have deployed effective cyber strategies in their organizations, foiled attacks and managed breach situations. Learn approaches for success and pitfalls to avoid by exploring the experience of others with deployment and management of cyber security strategies and plans.
Learning Objectives:
Identify successes, challenges and lessons learned with implementation of cyber strategies
Identify success strategies for gaining the C Suite support and ways cyber security can be integrated into the organization's culture and work processes.
Identify best practices with anticipating new and emerging threats and ways to maintain a proactive position instead of reactive
Identify approaches for breach preparation and breach management
Featured Speakers:
Neal Ganguly, MBA, FCHIME, FHIMSS, CHCIO
VP & CIO
JFK Health System
Miroslav Belote
Director of IT – Infrastructure and Information Security Officer
JFK Health System
Nassar Nizami
CISO
Yale-New Haven Health SystemCHIME LEAD New York 2014 "Case Studies from the Field: Putting Cyber Security...

CHIME LEAD New York 2014 "Case Studies from the Field: Putting Cyber Security...Health IT Conference – iHT2
LILAC 2014 Keynote SpeakerWhat value and benefits do we add? Why information professionals are essentia...

What value and benefits do we add? Why information professionals are essentia...IL Group (CILIP Information Literacy Group)
Webinar Next Week: Beyond Online Intake: Looking at Triage and Expert Systems

Webinar Next Week: Beyond Online Intake: Looking at Triage and Expert SystemsLegal Services National Technology Assistance Project (LSNTAP)
The Digital Marketing tech stack is expending every day. With so many tools at our fingertips we have the potential to accomplish more than ever before. But hidden issues with the people, processes, and technology in your dept can lead too lost time, lost opportunity, and invalid decisions. Using real world examples from leading companies around the globe, we'll teach you how to identify gaps in your data landscape, find solutions, and turn them into opportunities using resources you already have.How to Master your Marketing Data - Cody Crumrine, Data Aptitude

How to Master your Marketing Data - Cody Crumrine, Data AptitudeDigiMarCon - Digital Marketing, Media and Advertising Conferences & Exhibitions
Similaire à SPENTREP - New Crime by Group 4 (2013.Sep.9) (20)
[AIIM16] How Regulatory Data Can Set the Narrative for an Analytics Opportunity![[AIIM16] How Regulatory Data Can Set the Narrative for an Analytics Opportunity](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[AIIM16] How Regulatory Data Can Set the Narrative for an Analytics Opportunity](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[AIIM16] How Regulatory Data Can Set the Narrative for an Analytics Opportunity
London School of Hygiene - Maximising self-service success and user engagement

London School of Hygiene - Maximising self-service success and user engagement
Enhancing the Prospect, Student and Alumni Experience with Communities

Enhancing the Prospect, Student and Alumni Experience with Communities
Enhancing the Prospect, Student and Alumni Experience with Communities

Enhancing the Prospect, Student and Alumni Experience with Communities
7 summits student lifecycle communities salesforce.org

7 summits student lifecycle communities salesforce.org
Simple and Cost Effective Electronic Tools for Research with Youth

Simple and Cost Effective Electronic Tools for Research with Youth
CHIME LEAD New York 2014 "Case Studies from the Field: Putting Cyber Security...

CHIME LEAD New York 2014 "Case Studies from the Field: Putting Cyber Security...
Your AI and ML Projects Are Failing – Key Steps to Get Them Back on Track

Your AI and ML Projects Are Failing – Key Steps to Get Them Back on Track
What value and benefits do we add? Why information professionals are essentia...

What value and benefits do we add? Why information professionals are essentia...
FINAL PowerPoint internship project presentation .ppt

FINAL PowerPoint internship project presentation .ppt
ZoomPowee 2019: INSZoom Product Roadmap 2020 Secrets Revealed

ZoomPowee 2019: INSZoom Product Roadmap 2020 Secrets Revealed
Webinar Next Week: Beyond Online Intake: Looking at Triage and Expert Systems

Webinar Next Week: Beyond Online Intake: Looking at Triage and Expert Systems
How to Master your Marketing Data - Cody Crumrine, Data Aptitude

How to Master your Marketing Data - Cody Crumrine, Data Aptitude
SPENTREP - New Crime by Group 4 (2013.Sep.9)
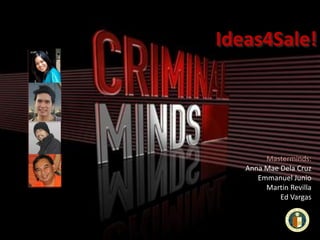
- 1. Ideas4Sale! Masterminds: Anna Mae Dela Cruz Emmanuel Junio Martin Revilla Ed Vargas
- 2. Background Crime Yield • Illegal disbursement or dissemination of business/corporate private or confidential information through MBA programs • Pilfered Ideas • Cheaper and easier means to gain access to competitor POC • Provides vantage point to competitor aspirants
- 3. Modus Operandi Mechanics Tools and Technologies • Criminals and accessories to the crime use MBA networks as means on collecting internal private or confidential information • Perpetrators collect papers, reports, assignments from MBA programs • Often these papers or reports contain confidential or private information that should not be released to the public (but students don't bother to get NDA thinking that this is only for classroom activity) • Perpetrators build a network of contacts and use or sell the information underground • Internet (as headquarters and channel for the activity) • Email (public/free) • Websites (underground/public/free) • MBA classroom or online programs • Term Papers, Assignments, etc • Database of information
- 4. Appendix (other nominated crimes) Centavo Heist Big Value Zero Description • Cashiers, due to lack of pennies, etc, does not give the exact change; when transactions are amassed, the heist turns into thousands or millions in amount Description • Employee pads a blank OR, or adds digits to the OR amount and reimburses the bogus amount to the company Modus Operandi • Companies encourage cashiers not to give exact change by not providing sufficient centavo coins • Buyers forgo obtaining the exact change, and the transactions get done • Companies earn from the accumulated centavo coins • In financial reports, the heist is not reflected, and taxes are not paid Modus Operandi • The crime is done in cahoots with teller or cashiers, or the like • This crime is effective with maximum benefit and lower risks when done in small amounts, and in multi-transactions that unsuspecting employers hardly notice