Chapter 2
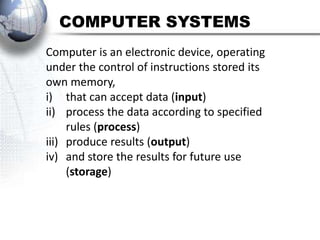
- 1. COMPUTER SYSTEMS Computer is an electronic device, operating under the control of instructions stored its own memory, i) that can accept data (input) ii) process the data according to specified rules (process) iii) produce results (output) iv) and store the results for future use (storage)
- 2. INPUT Input is any data and instructions entered into the memory of a computer. There are four types of input which are: text, graphics, audio and video.
- 3. OUTPUT Output is data that has been processed into a useful form called information.
- 4. STORAGE Storage is a location in which data, instructions, and information are save for future use. E.g. CD ROM, diskette, hard disk, pen drive, memory card.
- 5. INPUT DEVICE Input device is any hardware component that allows users to enter data and instructions into a computer. e.g. keyboard, mouse, scanner, barcode reader Also pointing devices: mouse, joystick, trackball, touch screen, pointing stick and graphic tablet.
- 7. JOYSTICK
- 12. OUTPUT DEVICE Output device is any hardware component that present information (processed data) to one or more people. E.g. Speaker, monitor, LCD projector, printer and plotter.
- 23. PROCESSOR • The functions of Processor –To control and coordinates operations in a computer system. –To manage main memory - example: Intel Pentium IV, AMD Athlon, G4
- 25. THE BLOCK DIAGRAM OF INFORMATION PROCESSING CYCLE Input Process Output Storage User will input the data to be processed by the processor. The storage hold databases, files and programs. The output devices present the processed data as useful information products for the user.
- 26. LCD Liquid crystal display
- 27. CD Compact disk
- 30. ICT
- 31. Function of CPU (Processor) • To control and coordinates operations in a computer system. • To manage main memory. • Fetch a program instructions or data item from memory • Decode the program instructions into signals that computer can execute. • Execute the instructions. • Store (Return) the result of instructions to the memory.
- 32. INFORMATION PROCESSING CYCLE PROCESS • The processing unit controls all activities within the system. For every instruction, the control unit repeats a set of four basic operation called the machine cycle(fetch, decode, execute and store).
- 33. MACHINE CYCLE Fetching Storing Decoding Executing
- 34. MACHINE CYCLE • Fetching: the processes of obtaining a program instructions or data item from memory. • Decoding: the process of translating a program instruction into signals that the computer can execute. • Executing: the process of implementing the instructions in a program. • Storing: the process of writing the result to the storage of memory.
- 35. • The central processing unit consists of two parts: the control unit (CU) and the arithmetic logic unit (ALU). Each part has specified function. The control unit tells the rest of the computer system how to carry out a program’s instructions. It directs the movement of electronic signals between memory, which temporarily holds data, instruction and processed information, and the arithmetic-logic unit. It also directs these controls signals between the CPU and input and output devices.
- 36. • Arithmetic-logic unit performs two types of operations: arithmetic and logical. Arithmetic operation are fundamental math operations: addition, subtraction, multiplication and division. Logical operations consist of comparisons. That is, two pieces of data are compared to see whether one is equal to, less than or greater than.
- 37. • The storage is a location in which data, instructions and information are saved for future use. Every computer uses storage to hold system software and application software. There are two type of storage, which are primary storage and secondary storage. A storage device is the computer hardware that records or retrieve item to and from storage media.
- 38. • Output is data that has been processed into a useful form, called information. There are four types of output, which are texts, graphics, audio and video.
- 39. 1.4 DATA REPRESENTATION: BIT, BYTE AND CHARACTER BIT • Bit: A bit (short for binary digit) is the smallest unit of data the computer can process. The binary system is a number system that has just two unique digits, 0 and 1 called bits. A bit is represented by the numbers 1 and 0. These number represent the binary system. They correspond to the states of on and off, true and false, or yes or no.
- 40. BYTE • Byte: Byte is a unit of information built from bits. When 8 bits are grouped together, as a unit, they form a byte. Bits and bytes are the basis for representing all meaningful information and programs on computers.
- 41. CHARACTER • One byte is equals to 8 bits. One byte represents a single character such as number, letter, or symbol. For example, the capital letter F is represented by binary code 01000110 that can be understood by the computer system.
- 42. • Computer does not understand letters or numbers or pictures or symbols. Computer uses a binary system to count as it only recognizes two states that are 0 and 1. Number 9 is represented by binary code 00111001. Eight bits grouped together as a unit are called a byte. A byte represents a single character in the computer.
- 43. ASCII/EBCDIC 1 byte = 8 bits = 1 character • There are three character codes or coding schemes to represent characters which are ASCII, EBCDIC and Unicode. Each eight byte contain eight bits. A byte provides enough different combination of 0s and 1s to represent 256 characters. ASCII is the most widely used binary code for microcomputers (Personal Computer). EBCDIC was developed by IBM and is used primary for large computer – mainframe and high end server.
- 44. • The combination of 0s and 1s are defined by patterns. These patterns are called coding system. The 256-character capability of ASCII and EBCDIC is too small to handle the characters that are used by other languages such as Arabic, Japanese and Chinese. The Unicode coding scheme is designed to solve this problem. It uses two bytes (16 bits) to represent one character. This gives it the capability of representing 65, 536 different character. This can cover all the world’s languages. Unicode is downward-compatible with ASCII, meaning that Unicode can recognizes ASCII character.
- 45. Unicode 2 bytes = 16 bits = 1 character
- 46. INTRODUCTION TO BINARY CODING What is ASCII? • ASCII (pronounce as-key) is an acronym for American Standard Code for Information Interchange used in most computers to represent letters, numbers and other characters.
- 47. ASCII Code Symbol ASCII code Symbol ASCII Code Symbol 00110000 0 (48) 01000001 A() 00100001 !( ) 1 (49) 01000010 B( ) ? (63) 2 (50) C (67) @ (64) 3 ( 51) D (68 ) $ ( 36) 4 ( 52 ) E (69) % ( 37) 5 ( 53 ) F ( 70) & (38) 6 ( 54 ) 01000111 G( ) * (42)
- 48. 27 26 25 24 23 22 21 20 128 64 32 16 8 4 2 1 A 0 1 0 0 0 0 0 1 64 1 65 0 1 0 0 0 1 1 1 71 64 4 2 1 G
- 49. 1.5 The Function of ASCII Code 1. Coding scheme such as ASCII make it possible for humans to interact with a digital computer that processes only bits. When you press a key on a keyboard, the electronic signal is converted into a binary form the computer can process and is stored in memory. Every character is converted to its corresponding bytes. Software converts the byte into a human recognizable number, letter of the alphabet that is displayed on a screen or is printed.
- 50. 2. ASCII was established to achieved compatibility between various types of data processing equipment making it possible for components to communicate with each other successfully.
- 51. 1.6 UNITS OF DATA MEASUREMENT KILOBYTE (KB) In mathematics, 1 KB = 1000 bytes. In computer, 1 KB = 1024 bytes or can be said as: 1 KB = 210 bytes This is how we get the calculation for 1024 bytes .
- 52. Why is 1024 bytes = 1KB? 20 = 1 21 = 2 22 = 4 23 = 8 24 = 16 25 = 32 26 = 64 27 = 128 28 = 256 29 = 512 210 = 1024
- 53. MEGABYTE (MB) 1 MB = 1 048 576 bytes or it can be said as: 1 MB = 220 bytes GIGABYTE (GB) 1 GB = 1 073 741 824 bytes or it can be said as: 1 GB = 230 bytes TERABYTE (TB) 1 TB = 1 099 511 627 776 bytes or it can be said as: 1 TB = 240 bytes
- 54. 1.7 CLOCKSPEED OF MEASUREMENT Megahertz (MHz) & Gigahertz (GHz) • When people talk about a computer’s “speed”, they mean how fast it can process data. In other words, this means the speed the computer can turn data into information. Every microprocessor contains a system clock. • The clock speed unit is measured in hertz. A hertz is one cycle per second.
- 55. 1 Hz = 1 cycle 1 second 1 000 000 cycle 1 MHz = 1 second 1 000 000 000 cycle 1 GHz = 1 second
- 56. • Mega is a prefix that’s stands for million. A computer that operates at 933 MHz (megahertz) has 933 million clock cycles in one second. One way of comparing the performance of personal computers is by comparing their microprocessor speeds. A CPU with a higher clock speed can process more instructions per second that a CPU operating at 800 MHz. The speed of the system clock affects only the CPU. It has no effects on peripherals such as a printer or disk drive.
- 57. • The combination of speed and number of paths determines the total processing speed or channel bandwidth. This is because different processors often use different architectures. For this reason, a 1.4 GHz Pentium 4 performs better that a 1.4 GHz Pentium 3, but it is not as fast as a 1.4 Ghz Power PC G4 processor.
- 58. 2.3 THE COMPUTER PORT • There are different kinds of port in a system unit. The ports are: – Serial port – Parallel port – Universal Serial Bus (USB) – Firewire port • Special purpose port – MIDI port – SCSI port – IrDA port
- 59. Serial port • A serial port is a socket on a computer used to connect a modem, data acquisition terminal or other serial devices via slow-speed serial interface. • A serial port is used to connect a device to the system unit by transmitting data one bit at a time.
- 60. Parallel Port • A parallel port is a socket on a computer used to connect a printer or other parallel devices via the computer's parallel interface. • Unlike a serial port, a parallel port is an interface that connects devices by transferring information more than one bit at a time. Originally, parallel ports were developed as an alternative to the slower speed serial ports. Many printers connect to the system unit using a parallel port.
- 61. • This parallel port can transfer eight bits of data (one byte) simultaneously through eight separate lines in a single cable. An example of a parallel port is the printer port.
- 62. USB Port • . A USB port, short for universal serial bus port, can connect up to 127 different peripherals together with a single connector. • It's used to connect all kinds of external devices, such as external hard drives, printers, mouse and scanner. It can transfer data to a speed of 12 megabits per second.
- 63. FIREWIRE PORT • Previously the FireWire port is called IEEE 1394 port, a personal computer (and digital audio/video) serial bus interface standard. • FireWire is similar to a USB port in that it can connect multiple types of devices that require faster data transmission speeds. Usually camcorders and other video equipment use this port to transmit data on a computer. Data can move across the port at up to 400 megabits per second.
- 64. STORAGE PRIMARY SECONDARY STORAGE STORAGE MAGNETIC OPTICAL FLASH RAM ROM MEDIUM MEDIUM MEMORY RAM – random access memory ROM – read only memory
- 65. PRIMARY STORAGE • There are two types of primary storage which are RAM and ROM. RAM is an acronym for Random-Access Memory which means the data and program in RAM can be read and written. ROM is an acronym for Read-Only Memory which means the data or program in ROM can just be read but cannot be written at all.
- 66. Function of RAM 1. RAM is the main memory in a computer. The data in RAM can be read (retrieved) or written (stored). 2. It stores data and programs that can be accessed directly by the processor. 3. RAM holds temporary instructions and data needed to complete tasks. This enables the computer’s CPU to access instructions and data stored in the memory very quickly. 4. RAM stores data during and after processing.
- 67. FUNCTION OF ROM 1. ROM is another type of memory permanently stored inside the computer. ROM is non-volatile. It holds the programs and data when the computer is powered off. 2. Programs in ROM have been pre-recorded. It can only be stored by the manufacturer; once it is done, it cannot be changed. 3. Many complex functions, such as start up operating instructions, translator for high- level languages and operating systems are placed in ROM memory.
- 68. FUNCTION OF ROM 4. All the contents in ROM can be accessed and read but cannot be changed.
- 69. DIFFERENCES BETWEEN RAM & ROM RAM Differences ROM Stores data Data and Stored by during and after program manufacturer processing Stores Content Stores information information temporarily permanently Vey fast, but uses Processing Time Fast, but uses a lot of power very little power Volatile Volatality Non-volatile
- 70. SECONDARY STORAGE • Secondary storage is another alternative storage to keep your work and documents. It is very useful to store programs and data for future use. It is installed externally. It is non- volatile, which means it does not need power to maintain the information stored in it. It will store the information until it is erased.
- 71. THREE MAIN TYPES OF SECONDARY STORAGE SECONDARY EXPLANATION STORAGE Magnetic Magnetic medium is a non-volatile storage medium medium. Magnetic disks use magnetic particles to store items such as data, instructions and information in disk’s surface. It can be any type of storage that utilizes magnetic patterns to represent information. The devices use disks that are coated with magnetically sensitive materials.
- 72. SECONDARY EXPLANATION STORAGE Magnetic The examples of magnetic storage are: medium Magnetic disk such as floppy disk, hard disk, zip disk. Magnetic tape such as video cassette, tape.
- 73. THREE MAIN TYPES OF SECONDARY STORAGE SECONDARY EXPLANATION STORAGE Optical Optical medium is a non-volatile storage Medium media that consists of a flat, round, portable disc made of metal and plastic that is written and read by a laser. These media include various types of Compact Disc, Digital Versatile Discs and Blu- Ray Disc.
- 74. SECONDARY EXPLANATION STORAGE Optical These following forms are often commonly medium used: 1. CD, DVD and BD: Read only storage, used for distribution of digital information such as music, video and computer programs. 2. CD-R and DVD-R: Write once storage, the data cannot be erased or written over once it is saved. 3. CD-RW, DVD-RW and DVD RAM. It allows data have been saved to be erased and rewritten.
- 75. SECONDARY EXPLANATION STORAGE Flash Flash memory is a solid-state media which memory means they consists entirely of electronic components and contains no moving parts. There are two type of flash memory: 1. Memory Memory card: It is used with digital cellular card phones, MP3 players, digital video cameras and other portable digital devices. Examples of memory cards such as Compact Flash, xD-picture card, memory stick, secure digital card, multimedia card, pc card and smart media.
- 76. SECONDARY EXPLANATION STORAGE 2. Flash drive Flash drive: It also called USB drives, thumb drives or pen drives.
- 77. COMPUTER SOFTWARE SYSTEM APPLICATION SOFTWARE SOFTWARE OPERATING UTILITY WORD SYSTEM SOFTWARE PROCESSING SPREADSHEET PRESENTATION GRAPHIC EDITOR
- 78. WHAT IS OPERATING SYSTEM (OS)? • An operating system is a set of programs containing instructions that coordinate all the activities among computer hardware resources. • Types of OS: – Stand-Alone Operating System (Windows XP, Vista, Mac OS, LINUX, DOS) – Network Operating System (Windows NT, Windows Server 2000, Linux, UNIX, Solaris) – Embedded Operating System (Windows CE, Palm OS, Symbian OS, Embeded Linux)
- 79. DIFFERENT PLATFORM OF OS PC PLATFORM APPLE CROSS OS PLATFORM OS PLATFORM OS Microsoft Mac OS LINUX Windows XP Mac OS X UNIX Microsoft Windows Vista
- 80. THE FUNCTION OF OS • The functions of OS: – Starting a computer – Provide a user interface – Managing program – Managing memory – Configuring devices
- 81. STARTING A COMPUTER • When we start a computer, it loads the operating system into the computer's memory. This process is called booting. Booting means to load and initialize the operating system on a computer machine. It can happen in two ways: warm boot or cold boot.
- 82. • WARM BOOT A warm boot means restarting a computer that is already on. It normally happens after installing a new software or hardware or after an application crashes or stops working. COLD BOOT • A cold boot means starting a computer that is already off. It happens when we turn on a computer that has been completely powered off.
- 83. PROVIDE A USER INTERFACE • We interact with software through its user interface. That is, user interface controls how you enter data and instructions and how information is displayed on the screen. Three types of user interface are – Command Line Interface – Menu Driven Interface – Graphical User Interface
- 84. COMMAND LINE USER INTERFACE • The command-line user interface requires a user to type commands or press special keys on the keyboard to enter data and instructions that instruct the operating system what to do. It has to be typed one line at a time. For example, if we want to rename a filename from ABC.txt to DEF.txt we use the following command. • C:>rename abc.txt.def.txt
- 85. Command line user interface
- 86. MENU DRIVEN INTERFACE • Menu driven user interface enables the user to avoid memorizing keywords such as copy, paste and syntax. On screen, menu-drive interface provide menus such as means entering commands. It shows all the options available at a given point a form of text-based menu.
- 88. GRAPHICAL USER INTERFACE (GUI) • Graphical user interface makes use of the computer’s graphics capabilities to make operating system and programs easier to use, which is also called ‘user-friendly’. • Graphical user interface interact with visual images such as buttons, icons and other graphical objects to issue commands. On the desktop, we can initiate many actions by clicking icons that represent computer resources such as files, programs and networks connections.
- 89. INDIVIDUAL TASK state the differences between command line interface & graphical user interface COMMAND LINE INTERFACE GRAPHICAL USER INTERFACE (DOS) (Windows/Linux)
- 90. GRAFICAL USER INTERFACE (GUI)
- 91. Command Line Menu Driven Graphical User Interface (CLI) Interface Interface (GUI) Command Menu Driven Icon Driven Driven Interface Interface Interface
- 92. MANAGING PROGRAM • Some operating systems support a single user and only one running program at a time. Other’s support thousands of runners multiple programs.
- 93. MANAGING MEMORY • The computer’s operating system is responsible for managing memory such as: (a) Allocating data and instruction to an idea of memory while being processed (b) Monitoring the contents of memory
- 94. CONFIGURING DEVICES • A driver, short for device driver, is a small program that tells the operating system how to communicate with specific device. Each device on a computer, such as mouse, keyboard, monitor, printer, digital camera, card reader and scanner, has its own specialized set of commands and thus requires its own specific driver.
- 95. UTILITY PROGRAM • A utility program which is also called a utility is a type of system software that allows a user to perform maintenance-type tasks usually related to managing a computer, its devices or its programs.
- 96. ANTIVIRUS • Antivirus is a program that protects a computer against viruses by identifying and removing any computer viruses found in a memory or storage media or in incoming files.
- 97. DIAGNOSTIC UTILITY • Diagnostic utility is a utility program that compiles technical information about a computer’s hardware and certain system software programs and then prepares a report outlining any identified problems.
- 98. FILE MANAGER • File manager is a utility program that performs functions related to files and disk management.
- 99. SCREEN SAVER • Screen saver is a utility program that enables a display device’s screen to show a moving image or blank screen if no mouse activity occurs for a specified time.
- 100. APPLICATION SOFTWARE • Application software is a computer program or a suite of computer programs that performs a particular function for the user. Application software includes all programs that perform specific tasks such as word processing, spreadsheet, database, presentation, e-mail and Web browsing
- 101. COMMON TYPES OF APPLICATION SOFTWARE Word Processing • Word Processing an office application that enables user to create, edit, format and print textual document. Spreadsheet • A program that processes information in the form of tables. Tables cells can hold values or mathematical formula.
- 102. COMMON TYPES OF APPLICATION SOFTWARE Presentation • An application software that allows a user to create visual aid for presentation to communicate ideas, messages and other information to a group. • Graphics Editing Program that can edit digital representation or non-text information such as drawing, charts and photograph. • Web browser Examples: Internet explorer, Google Chrome, Mozilla Forefox
- 103. TYPES OF EXAMPLES SOFTWARE PROPRIETARY OPEN SOURCE MICROSOFT WORD KWORD WORD COREL WORD OPEN OFFICE WRITE PROCESSING PERFECT MICROSOFT EXCEL KSPREAD SPREADSHEET COREL QUATTRO PRO OPEN OFFICE CALC MICROSOFT AGNUBIS PRESENTATION POWER POINT COREL OPEN OFFICE PRESENTATION IMPRESS GRAPHIC ADOBE PHOTOSHOP GIMP EDITOR COREL DRAW INKSCAPE
- 104. Exercise ASCII Code Symbol 00100001 !( ) ? (63) @ (64) $ ( 36) % ( 37) & (38) * (42)
- 105. PROPRIETARY AND OPEN SOURCE SOFTWARE • Proprietary software is also called closed source software. The closed source software or proprietary software offers a stable system with support if the software fails or malfunctions. • Examples: Windows XP, Windows 7, Microsoft Office
- 106. Open source software is: • software provided for use, modification and redistribution • software that any programmer can download from the Internet for free and modify with suggested improvements. • the only qualification is that changes can't be copyrighted, • Examples: OpenOffice.org, PHP-Nuke,The GIMP, Mozilla, ClamAV,OpenLDAP, Audacity and RedHat.
- 107. THE ADVANTAGES OF USING PROPRIETARY SOFTWARE • The software offers a stable system support if it fails or malfunction. • The software is safe and guaranteed to be safe from dubious threats like programming bugs and viruses thus providing ease of mind for the user. • The software is easier to install and used as the production is planned and extensive research is carried out to ensure users purchase only the best. • Furthermore, free updates and latest information on the software are usually provided to the user.
- 108. DISADVANTAGES TO USERS OF USING PROPRIETARY SOFTWARE ARE: • Users need to spend a long time downloading and installing security patches to fix bugs announced by the manufacturer. • Any improvements would usually require fees, which is often expensive. • Users are not allowed to describe and share the software as that are licenced. • Customising the software is nearly impossible because when users buy proprietary software will receive binary version of the program, not the code as the code is the maufacturer’s trade secret.
- 109. PROPRIETARY AND OPEN SOURCE SOFTWARE • Proprietary Software (Closed Source Software) means the company that developed the software owns the software, and no one may duplicate it or redistribute it without that company’s permission. Users have to pay to the software company if they want to use the proprietary software. • Examples of proprietary software are Microsoft Office 2007, Windows 7, Corel Office X3.
- 110. ADVANTAGES OF OPEN SOURCE SOFTWARE • The source code are available to users and they have the rights to modify them. • This will allow improvements to the software without having to invest large sum of money in research and development. • The modified and improved source codes can be freely redistributed.
- 111. DISADVANTAGES OF OPEN SOURCE SOFTWARE • The codes are too complicated for novice users to understand. • There is no particular official monitoring the works of a programmer improving the codes. This is because anyone is free to use, modify or even distribute the codes.
- 112. • Open Source Software is a software that is free to use and which provides the original source code used to create it so that advanced users can modify it to make work better for them. • Examples of open source software are Linux, GIMP, Blender, Inkscape, Mozilla Firefox 3.0, OpenOffice.org, KOffice.
- 113. THE DIFFERENCES BETWEEN PROPRIETARY AND OPEN SOURCE SOFTWARE OPEN SOURCE SOFTWARE PROPRIETARY SOFTWARE LINUX Ubuntu Windows Vista OpenOffice.org Microsoft Word 2007 GIMP Adobe Photoshop CS3 Purchased with its source code Purchased without its source code User can get open source software User must pay to get the for free of charge proprietary software Users can modify the software Users cannot modify the software Users can install software freely into User must have a license from any computer vendor before install into computer No one is responsible to the software Full support from vendor if anything happened to the
