Breaches Without Borders: 2015 Year in Review from IBM X-Force
•
3 j'aime•3,132 vues
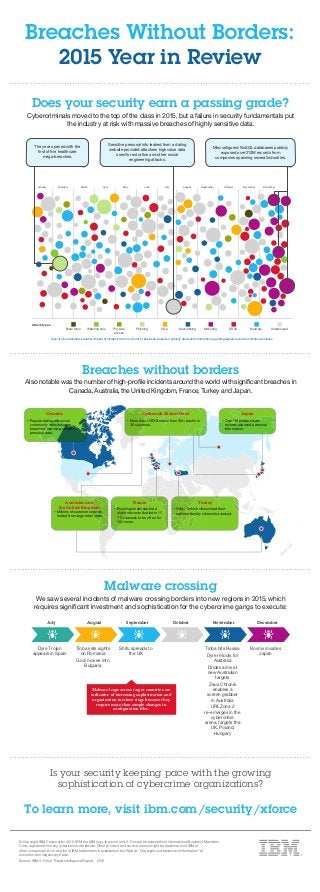
From healthcare mega-breaches to the growing sophistication of malware, cybercriminals moved to the top of the class in 2015. Failures in security fundamentals put the industry at risk with massive breaches of highly sensitive data, showing a need to return to the basic best practices. Get the high level overview of 2015 security trends in this infographic from the latest IBM X-Force Threat Intelligence Report.
Signaler
Partager
Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
Recommandé
Contenu connexe
Plus de IBM Security
Plus de IBM Security (20)
How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration

How to Build a Faster, Laser-Sharp SOC with Intelligent Orchestration
Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence

Orchestrate Your Security Defenses to Optimize the Impact of Threat Intelligence
Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...

Your Mainframe Environment is a Treasure Trove: Is Your Sensitive Data Protec...
Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...

Meet the New IBM i2 QRadar Offense Investigator App and Start Threat Hunting ...
Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...

Understanding the Impact of Today's Security Breaches: The 2017 Ponemon Cost ...
How to Improve Threat Detection & Simplify Security Operations

How to Improve Threat Detection & Simplify Security Operations
Orchestrate Your Security Defenses; Protect Against Insider Threats 

Orchestrate Your Security Defenses; Protect Against Insider Threats
Ponemon Institute Reviews Key Findings from “2017 State of Mobile & IoT Appli...

Ponemon Institute Reviews Key Findings from “2017 State of Mobile & IoT Appli...
See How You Measure Up With MaaS360 Mobile Metrics

See How You Measure Up With MaaS360 Mobile Metrics
Nowhere to Hide: Expose Threats in Real-time with IBM QRadar Network Insights

Nowhere to Hide: Expose Threats in Real-time with IBM QRadar Network Insights
Safeguard Healthcare Identities and Data with Identity Governance and Intelli...

Safeguard Healthcare Identities and Data with Identity Governance and Intelli...
Cybersecurity In The Cognitive Era: Priming Your Digital Immune System

Cybersecurity In The Cognitive Era: Priming Your Digital Immune System
Dernier
Dernier (20)
Tata AIG General Insurance Company - Insurer Innovation Award 2024

Tata AIG General Insurance Company - Insurer Innovation Award 2024
IAC 2024 - IA Fast Track to Search Focused AI Solutions

IAC 2024 - IA Fast Track to Search Focused AI Solutions
[2024]Digital Global Overview Report 2024 Meltwater.pdf![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[2024]Digital Global Overview Report 2024 Meltwater.pdf](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
[2024]Digital Global Overview Report 2024 Meltwater.pdf
2024: Domino Containers - The Next Step. News from the Domino Container commu...

2024: Domino Containers - The Next Step. News from the Domino Container commu...
TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments

TrustArc Webinar - Stay Ahead of US State Data Privacy Law Developments
Exploring the Future Potential of AI-Enabled Smartphone Processors

Exploring the Future Potential of AI-Enabled Smartphone Processors
The Codex of Business Writing Software for Real-World Solutions 2.pptx

The Codex of Business Writing Software for Real-World Solutions 2.pptx
Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...

Raspberry Pi 5: Challenges and Solutions in Bringing up an OpenGL/Vulkan Driv...
08448380779 Call Girls In Civil Lines Women Seeking Men

08448380779 Call Girls In Civil Lines Women Seeking Men
The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf

The Role of Taxonomy and Ontology in Semantic Layers - Heather Hedden.pdf
Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024

Bajaj Allianz Life Insurance Company - Insurer Innovation Award 2024
Understanding Discord NSFW Servers A Guide for Responsible Users.pdf

Understanding Discord NSFW Servers A Guide for Responsible Users.pdf
Factors to Consider When Choosing Accounts Payable Services Providers.pptx

Factors to Consider When Choosing Accounts Payable Services Providers.pptx
Scaling API-first – The story of a global engineering organization

Scaling API-first – The story of a global engineering organization
Breaches Without Borders: 2015 Year in Review from IBM X-Force
- 1. Breaches Without Borders: 2015 Year in Review Malware crossing We saw several incidents of malware crossing borders into new regions in 2015, which requires significant investment and sophistication for the cybercrime gangs to execute: July August September November December Dyre Trojan appears in Spain Tinba sets sights on Romania Gozi moves into Bulgaria Shifu spreads to the UK Tinba hits Russia Dyre retools for Australia Dridex aims at new Australian targets Zeus Chtonik enables a screen grabber in Australia URLZone 2 re-emerges in the cybercrime arena, targets the UK, Poland, Hungary Rovnix invades Japan October Malware leaps across target countries are indicative of increasing sophistication and organization in crime rings because they require more than simple changes to configuration files. Does your security earn a passing grade? Cybercriminals moved to the top of the class in 2015, but a failure in security fundamentals put the industry at risk with massive breaches of highly sensitive data. Attack types Brute force Watering hole Physical access Phishing SQLi Malvertising Misconfig. DDoS Malware Undisclosed January February March April May June July August September October November December The year opened with the first of five healthcare mega-breaches. Sensitive personal info leaked from a dating website provided attackers high value data used for extortion and other social engineering attacks. Misconfigured NoSQL databases publicly exposed over 210M records from companies spanning several industries. Size of circle estimates relative impact of incident in terms of cost to business, based on publicly disclosed information regarding leaked records and financial losses. Breaches without borders Also notable was the number of high-profile incidents around the world with significant breaches in Canada, Australia, the United Kingdom, France, Turkey and Japan. Canada • Popular dating and social community websites were breached, exposing sensitive personal data. Carbanak Global Heist • More than USD1B stolen from 100+ banks in 30 countries. Japan • Over 1M private citizen records exposed personal information. France • Phishing emails started a chain of events that led to 11 TV channels to be off air for 19+ hours. Turkey • 50M+ Turkish citizens had their national identity information leaked. Australia and the United Kingdom • Millions of customer records leaked from large retail chain. Is your security keeping pace with the growing sophistication of cybercrime organizations? To learn more, visit ibm.com/security/xforce © Copyright IBM Corporation 2016. IBM, the IBM logo, ibm.com and X-Force are trademarks of International Business Machines Corp., registered in many jurisdictions worldwide. Other product and service names might be trademarks of IBM or other companies. A current list of IBM trademarks is available on the Web at “Copyright and trademark information” at www.ibm.com/legal/copytrade. Source: IBM X-Force Threat Intelligence Report - 2016
