Generate Random Numbers and Improve Entropy in Linux Systems
•Télécharger en tant que ODP, PDF•
0 j'aime•287 vues
Random number generators in Linux and BSD
Signaler
Partager
Signaler
Partager
Recommandé
Contenu connexe
En vedette
En vedette (20)
Algorithms for Computer Games - lecture slides 2009

Algorithms for Computer Games - lecture slides 2009
Random number generation (in C++) – past, present and potential future 

Random number generation (in C++) – past, present and potential future
(SEC401) Encryption Key Storage with AWS KMS at Okta

(SEC401) Encryption Key Storage with AWS KMS at Okta
Similaire à Generate Random Numbers and Improve Entropy in Linux Systems
HC-4021, Efficient scheduling of OpenMP and OpenCL™ workloads on Accelerated ...

HC-4021, Efficient scheduling of OpenMP and OpenCL™ workloads on Accelerated ...AMD Developer Central
Similaire à Generate Random Numbers and Improve Entropy in Linux Systems (20)
The entropic principle: /dev/u?random and NetBSD by Taylor R Campbell

The entropic principle: /dev/u?random and NetBSD by Taylor R Campbell
Because "use urandom" isn't everything: a deep dive into CSPRNGs in Operating...

Because "use urandom" isn't everything: a deep dive into CSPRNGs in Operating...
CODE BLUE 2014 : Embedded Security in The Land of the Rising Sun by BEN SCHMI...

CODE BLUE 2014 : Embedded Security in The Land of the Rising Sun by BEN SCHMI...
Much ado about randomness. What is really a random number?

Much ado about randomness. What is really a random number?
Common Support Issues And How To Troubleshoot Them - Michael Hackett, Vikhyat...

Common Support Issues And How To Troubleshoot Them - Michael Hackett, Vikhyat...
A BEGINNER’S JOURNEY INTO THE WORLD OF HARDWARE HACKING

A BEGINNER’S JOURNEY INTO THE WORLD OF HARDWARE HACKING
HC-4021, Efficient scheduling of OpenMP and OpenCL™ workloads on Accelerated ...

HC-4021, Efficient scheduling of OpenMP and OpenCL™ workloads on Accelerated ...
inside-linux-kernel-rng-presentation-sept-13-2022.pdf

inside-linux-kernel-rng-presentation-sept-13-2022.pdf
Lightweight Virtualization with Linux Containers and Docker | YaC 2013

Lightweight Virtualization with Linux Containers and Docker | YaC 2013
Lightweight Virtualization with Linux Containers and Docker I YaC 2013

Lightweight Virtualization with Linux Containers and Docker I YaC 2013
OSDC 2015: Roland Kammerer | DRBD9: Managing High-Available Storage in Many-N...

OSDC 2015: Roland Kammerer | DRBD9: Managing High-Available Storage in Many-N...
Filip palian mateuszkocielski. simplest ownage human observed… routers

Filip palian mateuszkocielski. simplest ownage human observed… routers
Plus de ivoelenchev
Plus de ivoelenchev (6)
Dernier
Top Rated Pune Call Girls Daund ⟟ 6297143586 ⟟ Call Me For Genuine Sex Servi...

Top Rated Pune Call Girls Daund ⟟ 6297143586 ⟟ Call Me For Genuine Sex Servi...Call Girls in Nagpur High Profile
Dwarka Sector 26 Call Girls | Delhi | 9999965857 🫦 Vanshika Verma More Our Se...

Dwarka Sector 26 Call Girls | Delhi | 9999965857 🫦 Vanshika Verma More Our Se...Call Girls In Delhi Whatsup 9873940964 Enjoy Unlimited Pleasure
Dernier (20)
Top Rated Pune Call Girls Daund ⟟ 6297143586 ⟟ Call Me For Genuine Sex Servi...

Top Rated Pune Call Girls Daund ⟟ 6297143586 ⟟ Call Me For Genuine Sex Servi...
VIP 7001035870 Find & Meet Hyderabad Call Girls LB Nagar high-profile Call Girl

VIP 7001035870 Find & Meet Hyderabad Call Girls LB Nagar high-profile Call Girl
Call Girls In Ashram Chowk Delhi 💯Call Us 🔝8264348440🔝

Call Girls In Ashram Chowk Delhi 💯Call Us 🔝8264348440🔝
DDoS In Oceania and the Pacific, presented by Dave Phelan at NZNOG 2024

DDoS In Oceania and the Pacific, presented by Dave Phelan at NZNOG 2024
✂️ 👅 Independent Andheri Escorts With Room Vashi Call Girls 💃 9004004663

✂️ 👅 Independent Andheri Escorts With Room Vashi Call Girls 💃 9004004663
Chennai Call Girls Porur Phone 🍆 8250192130 👅 celebrity escorts service

Chennai Call Girls Porur Phone 🍆 8250192130 👅 celebrity escorts service
Challengers I Told Ya ShirtChallengers I Told Ya Shirt

Challengers I Told Ya ShirtChallengers I Told Ya Shirt
Lucknow ❤CALL GIRL 88759*99948 ❤CALL GIRLS IN Lucknow ESCORT SERVICE❤CALL GIRL

Lucknow ❤CALL GIRL 88759*99948 ❤CALL GIRLS IN Lucknow ESCORT SERVICE❤CALL GIRL
FULL ENJOY Call Girls In Mayur Vihar Delhi Contact Us 8377087607

FULL ENJOY Call Girls In Mayur Vihar Delhi Contact Us 8377087607
Dwarka Sector 26 Call Girls | Delhi | 9999965857 🫦 Vanshika Verma More Our Se...

Dwarka Sector 26 Call Girls | Delhi | 9999965857 🫦 Vanshika Verma More Our Se...
Call Girls in Mayur Vihar ✔️ 9711199171 ✔️ Delhi ✔️ Enjoy Call Girls With Our...

Call Girls in Mayur Vihar ✔️ 9711199171 ✔️ Delhi ✔️ Enjoy Call Girls With Our...
Hot Call Girls |Delhi |Hauz Khas ☎ 9711199171 Book Your One night Stand

Hot Call Girls |Delhi |Hauz Khas ☎ 9711199171 Book Your One night Stand
Call Girls In Sukhdev Vihar Delhi 💯Call Us 🔝8264348440🔝

Call Girls In Sukhdev Vihar Delhi 💯Call Us 🔝8264348440🔝
All Time Service Available Call Girls Mg Road 👌 ⏭️ 6378878445

All Time Service Available Call Girls Mg Road 👌 ⏭️ 6378878445
Radiant Call girls in Dubai O56338O268 Dubai Call girls

Radiant Call girls in Dubai O56338O268 Dubai Call girls
10.pdfMature Call girls in Dubai +971563133746 Dubai Call girls

10.pdfMature Call girls in Dubai +971563133746 Dubai Call girls
Call Girls In Model Towh Delhi 💯Call Us 🔝8264348440🔝

Call Girls In Model Towh Delhi 💯Call Us 🔝8264348440🔝
VIP 7001035870 Find & Meet Hyderabad Call Girls Dilsukhnagar high-profile Cal...

VIP 7001035870 Find & Meet Hyderabad Call Girls Dilsukhnagar high-profile Cal...
Networking in the Penumbra presented by Geoff Huston at NZNOG

Networking in the Penumbra presented by Geoff Huston at NZNOG
Generate Random Numbers and Improve Entropy in Linux Systems
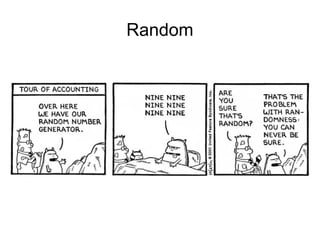
- 1. Random
- 2. Random numbers in AWK ● awk 'BEGIN{srand();print int(rand()*(65000))}'
- 3. 1204
- 4. 21
- 5. 21
- 6. Random numbers and shuf ● shuf -i 2000-65000 -n 1
- 7. 7
- 8. 7
- 9. 7
- 10. True Randomness
- 11. True Randomness ● counters that detect radioactive decay ● the timing of actual movements of a hard disk read/write head ● webcam/audio static noise
- 12. dev/random ● od -A n -N 2 -t u2 /dev/random ● od -A n -N 2 -t u2 /dev/urandom
- 13. man urandom A read from the /dev/urandom device will not block waiting for more entropy. As a result, if there is not sufficient entropy in the entropy pool, the returned values are theoretically vulnerable to a cryptographic attack on the algorithms used by the driver. Knowledge of how to do this is not available in the current unclassified literature, but it is theoretically possible that such an attack may exist. If this is a concern in your application, use /dev/random instead.
- 14. Random vs URandom ● URandom is a pseudo random number generator ● Random is a true random number generator
- 17. What about entropy running low? ● It doesn't matter. ● The underlying cryptographic building blocks are designed such that an attacker cannot predict the outcome, as long as there was enough randomness (256 bits).
- 18. Why is Re-seeding so important? ● If you've got more randomness just lying around, by all means use it!
- 19. man urandom If you are unsure about whether you should use /dev/random or /dev/urandom, then probably you want to use the latter. As a general rule, /dev/urandom should be used for everything except long-lived GPG/SSL/SSH keys.
- 20. Not everything is perfect ● On Linux, unlike FreeBSD, /dev/urandom never blocks. ● Linux's /dev/urandom happily gives you not- so-random numbers before the kernel even had the chance to gather entropy. ● FreeBSD doesn't have the distinction between /dev/random and /dev/urandom, both are the same device.
- 21. Not everything is perfect ● Linux distributions save some random numbers when booting up the system (but after they have gathered some entropy, since the startup script doesn't run immediately after switching on the machine) into a seed file that is read next time the machine is booting. ● Linux has implemented a new syscall, originally introduced by OpenBSD as getentropy(2): getrandom(2). This syscall does the right thing: blocking until it has gathered enough initial entropy, and never blocking after that point.
- 22. When is low entropy a problem? ● It used to be a problem for devices with no interface for human interaction when the entropy collector relied solely on than ● Today, virtual machines can have this issue if they are being cloned or restored to a checkpoint.
- 23. The end. 42