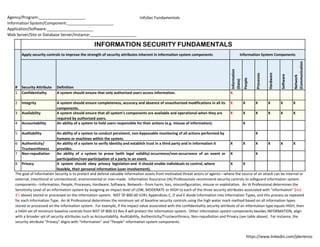
Information Security Fundamentals
•
1 j'aime•652 vues
Information Security Fundamentals
Signaler
Partager
Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
Recommandé
PAFF 6315: Management of Government Information Systems;
Fall 2015, Module OneInformation Security and Privacy - Public Sector actions, policies and regula...

Information Security and Privacy - Public Sector actions, policies and regula...The University of Texas (UTRGV)
Contenu connexe
Tendances
PAFF 6315: Management of Government Information Systems;
Fall 2015, Module OneInformation Security and Privacy - Public Sector actions, policies and regula...

Information Security and Privacy - Public Sector actions, policies and regula...The University of Texas (UTRGV)
Tendances (17)
Information Security and Privacy - Public Sector actions, policies and regula...

Information Security and Privacy - Public Sector actions, policies and regula...
Accuracy constrained privacy-preserving access control mechanism for relation...

Accuracy constrained privacy-preserving access control mechanism for relation...
En vedette
Fundamentals Matter - A Brief Introduction to Risk Analysis for Information SecurityNTXISSACSC3 - Fundamentals Matter - A Brief Introduction to Risk Analysis for...

NTXISSACSC3 - Fundamentals Matter - A Brief Introduction to Risk Analysis for...North Texas Chapter of the ISSA
En vedette (20)
NIST Policy Mapped to 800-53-800-53A-controls-and-objectives (Legal Size)

NIST Policy Mapped to 800-53-800-53A-controls-and-objectives (Legal Size)
Job aid framework-for-improving-critical-infrastructure-cybersecurity-core-jwd

Job aid framework-for-improving-critical-infrastructure-cybersecurity-core-jwd
Risk Management Framework (RMF) STEP 4- Access Security Controls - NIST SP 80...

Risk Management Framework (RMF) STEP 4- Access Security Controls - NIST SP 80...
Information Security Fundamentals - New Horizons Bulgaria

Information Security Fundamentals - New Horizons Bulgaria
NTXISSACSC3 - Fundamentals Matter - A Brief Introduction to Risk Analysis for...

NTXISSACSC3 - Fundamentals Matter - A Brief Introduction to Risk Analysis for...
(1b) Map CSC v5.0 to NIST SP 800 53 Revision 4 (security control table landsc...

(1b) Map CSC v5.0 to NIST SP 800 53 Revision 4 (security control table landsc...
(1a) map csc 5 to nist sp 800 53 rev 4 (security control table portrait) 2014...

(1a) map csc 5 to nist sp 800 53 rev 4 (security control table portrait) 2014...
Policy. FedRAMP Security Assessment Plan (SAP) Template, Policy and Procedure...

Policy. FedRAMP Security Assessment Plan (SAP) Template, Policy and Procedure...
Map Critical Security Controls (CSC) v5.0 to NIST SP 800-53 Revision 4 (Summa...

Map Critical Security Controls (CSC) v5.0 to NIST SP 800-53 Revision 4 (Summa...
Critical Security Controls v4 1 Mapped to NIST SP 800-53 Rev.4-final r6a

Critical Security Controls v4 1 Mapped to NIST SP 800-53 Rev.4-final r6a
RMF STEP 2: SELECT (NIST 800-53 Rev. 3 Controls, Enhancements and Supplementa...

RMF STEP 2: SELECT (NIST 800-53 Rev. 3 Controls, Enhancements and Supplementa...
Information System Sensitivity Level Impact Assessment (NIST SP 800-60v2r1)

Information System Sensitivity Level Impact Assessment (NIST SP 800-60v2r1)
Similaire à Information Security Fundamentals
Similaire à Information Security Fundamentals (20)
Exploring the Seven Key Attributes of Security Testing.pdf

Exploring the Seven Key Attributes of Security Testing.pdf
database-security-access-control-models-a-brief-overview-IJERTV2IS50406.pdf

database-security-access-control-models-a-brief-overview-IJERTV2IS50406.pdf
Legal and Ethical Considerations in Nursing Informatics

Legal and Ethical Considerations in Nursing Informatics
Comprehensive Analysis of Contemporary Information Security Challenges

Comprehensive Analysis of Contemporary Information Security Challenges
Plus de James W. De Rienzo
Plus de James W. De Rienzo (10)
FedRAMP 2.0 Control-Implementation-Summary (CIS) v2 1 cross-matrixed with Fed...

FedRAMP 2.0 Control-Implementation-Summary (CIS) v2 1 cross-matrixed with Fed...
NIST NVD REV 4 Security Controls Online Database Analysis

NIST NVD REV 4 Security Controls Online Database Analysis
(4) NIST SP 800-53 Revision 4 (security control enhancements omitted) 20140804

(4) NIST SP 800-53 Revision 4 (security control enhancements omitted) 20140804
(3) Map Council on CyberSecurity's Critical Security Controls (CSC) Version 5...

(3) Map Council on CyberSecurity's Critical Security Controls (CSC) Version 5...
(2) map csc 5 to nist sp 800 53 rev 4 (controls & enhancements) 20140804

(2) map csc 5 to nist sp 800 53 rev 4 (controls & enhancements) 20140804
Information Assurance, A DISA CCRI Conceptual Framework

Information Assurance, A DISA CCRI Conceptual Framework
Dernier
💉💊+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHABI}}+971581248768
+971581248768 Mtp-Kit (500MG) Prices » Dubai [(+971581248768**)] Abortion Pills For Sale In Dubai, UAE, Mifepristone and Misoprostol Tablets Available In Dubai, UAE CONTACT DR.Maya Whatsapp +971581248768 We Have Abortion Pills / Cytotec Tablets /Mifegest Kit Available in Dubai, Sharjah, Abudhabi, Ajman, Alain, Fujairah, Ras Al Khaimah, Umm Al Quwain, UAE, Buy cytotec in Dubai +971581248768''''Abortion Pills near me DUBAI | ABU DHABI|UAE. Price of Misoprostol, Cytotec” +971581248768' Dr.DEEM ''BUY ABORTION PILLS MIFEGEST KIT, MISOPROTONE, CYTOTEC PILLS IN DUBAI, ABU DHABI,UAE'' Contact me now via What's App…… abortion Pills Cytotec also available Oman Qatar Doha Saudi Arabia Bahrain Above all, Cytotec Abortion Pills are Available In Dubai / UAE, you will be very happy to do abortion in Dubai we are providing cytotec 200mg abortion pill in Dubai, UAE. Medication abortion offers an alternative to Surgical Abortion for women in the early weeks of pregnancy. We only offer abortion pills from 1 week-6 Months. We then advise you to use surgery if its beyond 6 months. Our Abu Dhabi, Ajman, Al Ain, Dubai, Fujairah, Ras Al Khaimah (RAK), Sharjah, Umm Al Quwain (UAQ) United Arab Emirates Abortion Clinic provides the safest and most advanced techniques for providing non-surgical, medical and surgical abortion methods for early through late second trimester, including the Abortion By Pill Procedure (RU 486, Mifeprex, Mifepristone, early options French Abortion Pill), Tamoxifen, Methotrexate and Cytotec (Misoprostol). The Abu Dhabi, United Arab Emirates Abortion Clinic performs Same Day Abortion Procedure using medications that are taken on the first day of the office visit and will cause the abortion to occur generally within 4 to 6 hours (as early as 30 minutes) for patients who are 3 to 12 weeks pregnant. When Mifepristone and Misoprostol are used, 50% of patients complete in 4 to 6 hours; 75% to 80% in 12 hours; and 90% in 24 hours. We use a regimen that allows for completion without the need for surgery 99% of the time. All advanced second trimester and late term pregnancies at our Tampa clinic (17 to 24 weeks or greater) can be completed within 24 hours or less 99% of the time without the need surgery. The procedure is completed with minimal to no complications. Our Women's Health Center located in Abu Dhabi, United Arab Emirates, uses the latest medications for medical abortions (RU-486, Mifeprex, Mifegyne, Mifepristone, early options French abortion pill), Methotrexate and Cytotec (Misoprostol). The safety standards of our Abu Dhabi, United Arab Emirates Abortion Doctors remain unparalleled. They consistently maintain the lowest complication rates throughout the nation. Our Physicians and staff are always available to answer questions and care for women in one of the most difficult times in their lives. The decision to have an abortion at the Abortion Cl+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...?#DUbAI#??##{{(☎️+971_581248768%)**%*]'#abortion pills for sale in dubai@
Dernier (20)
Boost Fertility New Invention Ups Success Rates.pdf

Boost Fertility New Invention Ups Success Rates.pdf
ICT role in 21st century education and its challenges

ICT role in 21st century education and its challenges
Powerful Google developer tools for immediate impact! (2023-24 C)

Powerful Google developer tools for immediate impact! (2023-24 C)
Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood

Polkadot JAM Slides - Token2049 - By Dr. Gavin Wood
Connector Corner: Accelerate revenue generation using UiPath API-centric busi...

Connector Corner: Accelerate revenue generation using UiPath API-centric busi...
Navi Mumbai Call Girls 🥰 8617370543 Service Offer VIP Hot Model

Navi Mumbai Call Girls 🥰 8617370543 Service Offer VIP Hot Model
Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...

Mastering MySQL Database Architecture: Deep Dive into MySQL Shell and MySQL R...
Apidays New York 2024 - The value of a flexible API Management solution for O...

Apidays New York 2024 - The value of a flexible API Management solution for O...
Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...

Web Form Automation for Bonterra Impact Management (fka Social Solutions Apri...
Why Teams call analytics are critical to your entire business

Why Teams call analytics are critical to your entire business
Apidays New York 2024 - Accelerating FinTech Innovation by Vasa Krishnan, Fin...

Apidays New York 2024 - Accelerating FinTech Innovation by Vasa Krishnan, Fin...
EMPOWERMENT TECHNOLOGY GRADE 11 QUARTER 2 REVIEWER

EMPOWERMENT TECHNOLOGY GRADE 11 QUARTER 2 REVIEWER
Axa Assurance Maroc - Insurer Innovation Award 2024

Axa Assurance Maroc - Insurer Innovation Award 2024
Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving

Repurposing LNG terminals for Hydrogen Ammonia: Feasibility and Cost Saving
Strategies for Landing an Oracle DBA Job as a Fresher

Strategies for Landing an Oracle DBA Job as a Fresher
TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery

TrustArc Webinar - Unlock the Power of AI-Driven Data Discovery
+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...

+971581248768>> SAFE AND ORIGINAL ABORTION PILLS FOR SALE IN DUBAI AND ABUDHA...
