Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
Recommandé
by Juanita Koilpillai, CEO & Founder, Waverley LabsSoftware Defined Perimeter - A New Paradigm for Securing Digital Infrastructu...

Software Defined Perimeter - A New Paradigm for Securing Digital Infrastructu...Government Technology & Services Coalition
Contenu connexe
Tendances
by Juanita Koilpillai, CEO & Founder, Waverley LabsSoftware Defined Perimeter - A New Paradigm for Securing Digital Infrastructu...

Software Defined Perimeter - A New Paradigm for Securing Digital Infrastructu...Government Technology & Services Coalition
Tendances (20)
Recent DDoS attack trends, and how you should respond

Recent DDoS attack trends, and how you should respond
Rethinking Security: The Cloud Infrastructure Effect

Rethinking Security: The Cloud Infrastructure Effect
Secure Cloud Hosting: Real Requirements to Protect your Data

Secure Cloud Hosting: Real Requirements to Protect your Data
The Morphing DDoS and Bot Landscape: Featuring Guest Speaker from IDC

The Morphing DDoS and Bot Landscape: Featuring Guest Speaker from IDC
Software Defined Perimeter - A New Paradigm for Securing Digital Infrastructu...

Software Defined Perimeter - A New Paradigm for Securing Digital Infrastructu...
What You're Missing With Your Current WAF Provider

What You're Missing With Your Current WAF Provider
2021 02-17 v mware-algo-sec securely accelerate your digital transformation w...

2021 02-17 v mware-algo-sec securely accelerate your digital transformation w...
Reaching PCI Nirvana: Ensure a Successful Audit & Maintain Continuous Compliance

Reaching PCI Nirvana: Ensure a Successful Audit & Maintain Continuous Compliance
Why you should replace your d do s hardware appliance

Why you should replace your d do s hardware appliance
How to Overcome Network Access Control Limitations for Better Network Security

How to Overcome Network Access Control Limitations for Better Network Security
Similaire à Verisign Cloud Mitigation
Similaire à Verisign Cloud Mitigation (20)
PLNOG16: DDOS SOLUTIONS – CUSTOMER POINT OF VIEW, Piotr Wojciechowski

PLNOG16: DDOS SOLUTIONS – CUSTOMER POINT OF VIEW, Piotr Wojciechowski
PLNOG15 :DDOS Attacks & Collateral Damage. Can we avoid it? Asraf Ali

PLNOG15 :DDOS Attacks & Collateral Damage. Can we avoid it? Asraf Ali
PLNOG15 :DDOS Attacks & Collateral Damage. Can we avoid it? Asraf Ali

PLNOG15 :DDOS Attacks & Collateral Damage. Can we avoid it? Asraf Ali
BKNIX Peering Forum 2017 : DDoS Attack Trend and Defense Strategy

BKNIX Peering Forum 2017 : DDoS Attack Trend and Defense Strategy
Network security, Anti-DDoS and other Internet-side protections: Encryption i...

Network security, Anti-DDoS and other Internet-side protections: Encryption i...
SecurityDAM - Hybrid DDoS Protection for MSSPs and Enterprises (Infosecurity ...

SecurityDAM - Hybrid DDoS Protection for MSSPs and Enterprises (Infosecurity ...
Rethinking Security: Corsa Red Armor Network Security Enforcement

Rethinking Security: Corsa Red Armor Network Security Enforcement
ciso-platform-annual-summit-2013-Hp enterprise security overview

ciso-platform-annual-summit-2013-Hp enterprise security overview
Disaster recovery solutions and datacentre replacements

Disaster recovery solutions and datacentre replacements
From liability to asset, the role you should be playing in your security arch...

From liability to asset, the role you should be playing in your security arch...
DNS DDoS mitigation using Amazon Route 53 and AWS Shield

DNS DDoS mitigation using Amazon Route 53 and AWS Shield
Plus de Juniper Networks
Plus de Juniper Networks (20)
Real AI. Real Results. Mist AI Customer Testimonials.

Real AI. Real Results. Mist AI Customer Testimonials.
Are you able to deliver reliable experiences for connected devices

Are you able to deliver reliable experiences for connected devices
Securing IoT at Scale Requires a Holistic Approach

Securing IoT at Scale Requires a Holistic Approach
Smart Solutions for Smart Communities: What's Next & Who's Responsible?

Smart Solutions for Smart Communities: What's Next & Who's Responsible?
SDN and NFV: Transforming the Service Provider Organization

SDN and NFV: Transforming the Service Provider Organization
Navigating the Uncertain World Facing Service Providers - Juniper's Perspective

Navigating the Uncertain World Facing Service Providers - Juniper's Perspective
High performance data center computing using manageable distributed computing

High performance data center computing using manageable distributed computing
Dernier
Dernier (20)
Choosing the Right FDO Deployment Model for Your Application _ Geoffrey at In...

Choosing the Right FDO Deployment Model for Your Application _ Geoffrey at In...
Long journey of Ruby Standard library at RubyKaigi 2024

Long journey of Ruby Standard library at RubyKaigi 2024
Extensible Python: Robustness through Addition - PyCon 2024

Extensible Python: Robustness through Addition - PyCon 2024
The Value of Certifying Products for FDO _ Paul at FIDO Alliance.pdf

The Value of Certifying Products for FDO _ Paul at FIDO Alliance.pdf
Microsoft CSP Briefing Pre-Engagement - Questionnaire

Microsoft CSP Briefing Pre-Engagement - Questionnaire
Easier, Faster, and More Powerful – Alles Neu macht der Mai -Wir durchleuchte...

Easier, Faster, and More Powerful – Alles Neu macht der Mai -Wir durchleuchte...
Behind the Scenes From the Manager's Chair: Decoding the Secrets of Successfu...

Behind the Scenes From the Manager's Chair: Decoding the Secrets of Successfu...
Introduction to FDO and How It works Applications _ Richard at FIDO Alliance.pdf

Introduction to FDO and How It works Applications _ Richard at FIDO Alliance.pdf
Simplified FDO Manufacturing Flow with TPMs _ Liam at Infineon.pdf

Simplified FDO Manufacturing Flow with TPMs _ Liam at Infineon.pdf
Breaking Down the Flutterwave Scandal What You Need to Know.pdf

Breaking Down the Flutterwave Scandal What You Need to Know.pdf
FDO for Camera, Sensor and Networking Device – Commercial Solutions from VinC...

FDO for Camera, Sensor and Networking Device – Commercial Solutions from VinC...
PLAI - Acceleration Program for Generative A.I. Startups

PLAI - Acceleration Program for Generative A.I. Startups
Continuing Bonds Through AI: A Hermeneutic Reflection on Thanabots

Continuing Bonds Through AI: A Hermeneutic Reflection on Thanabots
State of the Smart Building Startup Landscape 2024!

State of the Smart Building Startup Landscape 2024!
TEST BANK For, Information Technology Project Management 9th Edition Kathy Sc...

TEST BANK For, Information Technology Project Management 9th Edition Kathy Sc...
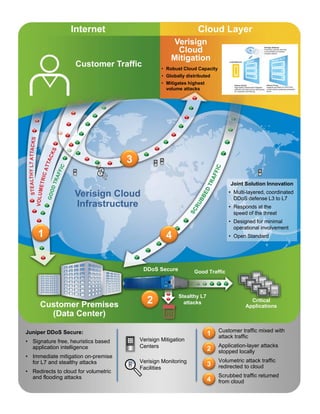
Verisign Cloud Mitigation
- 1. Customer Traffic Verisign Cloud Mitigation Verisign Cloud Infrastructure Customer Premises (Data Center) Internet Cloud Layer Juniper DDoS Secure: • Signature free, heuristics based application intelligence • Immediate mitigation on-premise for L7 and stealthy attacks • Redirects to cloud for volumetric and flooding attacks Stealthy L7 attacks Joint Solution Innovation • Multi-layered, coordinated DDoS defense L3 to L7 • Responds at the speed of the threat • Designed for minimal operational involvement • Open Standard1 2 1 2 3 Customer traffic mixed with attack traffic Application-layer attacks stopped locally Volumetric attack traffic redirected to cloud Scrubbed traffic returned from cloud Verisign Mitigation Centers Good Traffic • Robust Cloud Capacity • Globally distributed • Mitigates highest volume attacks Critical Applications DDoS Secure Verisign Monitoring Facilities 3 4 4
