CRC in Data Communication DC19
•Télécharger en tant que PPT, PDF•
3 j'aime•1,917 vues
Signaler
Partager
Signaler
Partager
Recommandé
Contenu connexe
Tendances
Tendances (16)
Similaire à CRC in Data Communication DC19
Similaire à CRC in Data Communication DC19 (20)
Plus de koolkampus
Plus de koolkampus (17)
Transmission of Digital Data(Data Communication) DC11

Transmission of Digital Data(Data Communication) DC11
Analog to Digital Encoding in Data Communication DC9

Analog to Digital Encoding in Data Communication DC9
Analog to Analog Modulation in Data Communication DC10

Analog to Analog Modulation in Data Communication DC10
Authentication Application in Network Security NS4

Authentication Application in Network Security NS4
Dernier
Dernier (20)
State of the Smart Building Startup Landscape 2024!

State of the Smart Building Startup Landscape 2024!
(Explainable) Data-Centric AI: what are you explaininhg, and to whom?

(Explainable) Data-Centric AI: what are you explaininhg, and to whom?
How Red Hat Uses FDO in Device Lifecycle _ Costin and Vitaliy at Red Hat.pdf

How Red Hat Uses FDO in Device Lifecycle _ Costin and Vitaliy at Red Hat.pdf
Portal Kombat : extension du réseau de propagande russe

Portal Kombat : extension du réseau de propagande russe
FDO for Camera, Sensor and Networking Device – Commercial Solutions from VinC...

FDO for Camera, Sensor and Networking Device – Commercial Solutions from VinC...
Microsoft CSP Briefing Pre-Engagement - Questionnaire

Microsoft CSP Briefing Pre-Engagement - Questionnaire
Continuing Bonds Through AI: A Hermeneutic Reflection on Thanabots

Continuing Bonds Through AI: A Hermeneutic Reflection on Thanabots
Long journey of Ruby Standard library at RubyKaigi 2024

Long journey of Ruby Standard library at RubyKaigi 2024
Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...

Event-Driven Architecture Masterclass: Integrating Distributed Data Stores Ac...
WebRTC and SIP not just audio and video @ OpenSIPS 2024

WebRTC and SIP not just audio and video @ OpenSIPS 2024
Event-Driven Architecture Masterclass: Engineering a Robust, High-performance...

Event-Driven Architecture Masterclass: Engineering a Robust, High-performance...
Where to Learn More About FDO _ Richard at FIDO Alliance.pdf

Where to Learn More About FDO _ Richard at FIDO Alliance.pdf
Your enemies use GenAI too - staying ahead of fraud with Neo4j

Your enemies use GenAI too - staying ahead of fraud with Neo4j
Simplified FDO Manufacturing Flow with TPMs _ Liam at Infineon.pdf

Simplified FDO Manufacturing Flow with TPMs _ Liam at Infineon.pdf
Using IESVE for Room Loads Analysis - UK & Ireland

Using IESVE for Room Loads Analysis - UK & Ireland
Easier, Faster, and More Powerful – Notes Document Properties Reimagined

Easier, Faster, and More Powerful – Notes Document Properties Reimagined
CRC in Data Communication DC19
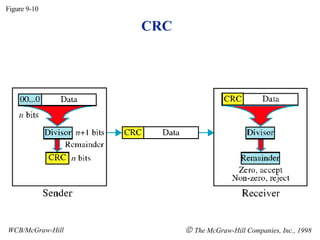
- 1. CRC Figure 9-10 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998
- 2. Binary Division Figure 9-11 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998
- 3. Polynomial Figure 9-12 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998
- 4. Figure 9-13 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Polynomial and Divisor
- 5. Standard Polynomials Figure 9-14 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998
- 6. Checksum Figure 9-15 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998
- 7. Figure 9-16 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Data Unit and Checksum
- 8. Error Correction Figure 9-17 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998
- 9. Hamming Code Figure 9-18 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998
- 10. Figure 9-19 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Hamming Code
- 11. Figure 9-19-continued WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Hamming Code
- 12. Figure 9-20 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Example of Hamming Code
- 13. Single-bit error Figure 9-21 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998
- 14. Figure 9-22 WCB/McGraw-Hill The McGraw-Hill Companies, Inc., 1998 Error Detection