Infographic Does blockchain hold the key to a new age of supply chain transparency and trust?
•
1 j'aime•126 vues
Infographic. Does blockchain hold the key to a new age of supply chain transparency and trust?. Capgemini Research
Signaler
Partager
Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
3 FAQs on COVID-19 Induced Supply Chain Disruptions

The document discusses 3 common questions about using supply chain analytics to address risks and disruptions caused by COVID-19: how analytics can help manage supply chain disruption risks, how analytics solutions can mitigate disruptions, and what strategies companies can use going forward. It then invites the reader to contact them for assistance with supply chain analytics.
Stop wire fraud aug 2016

The document summarizes Guardian Analytics' wire fraud protection solution. It discusses the rise of business email compromise (BEC) wire fraud, with funds lost increasing over 400% from 2015 to 2016. Guardian Analytics protects customers of the Fiserv wire transfer platform WireXchange through real-time risk scoring of wire transactions. This solution has successfully prevented millions of dollars in fraudulent wires for various banks and credit unions. The document promotes Guardian Analytics' fraud detection capabilities and provides customer testimonials and a diagram of how its real-time wire monitoring works integrated with the WireXchange system.
Guardian analytics vs. actimize 2016

This document summarizes the capabilities of Guardian Analytics' machine learning and behavioral analytics solutions for financial fraud detection compared to Actimize. It states that Guardian Analytics offers omni-channel visibility, behavioral analytics that require no rules, and machine learning that continuously updates models without human intervention. It also provides rapid deployment, flexible hosting options, visual analytics, and integrates risk data from multiple sources. In contrast, it describes Actimize as having poor user interfaces, requiring extensive rule maintenance, long deployments, and high costs.
State of The Industry Presented By Grapeshot, Digiday Programmatic Summit, Ma...

This document summarizes the findings of a state of the industry report on the relationship between media agencies and trading desks. It finds that while many agencies and trading desks have an ambivalent relationship, transparency breeds trust. It also shows that most clients' top need is brand safety and content protection. Additionally, it reveals that trading desks hold more power over targeting and optimization decisions than agency buying teams.
Cybersecurity's Impact on Innovation

Most small and mid-sized tech and healthcare companies are maintaining or increasing their cybersecurity resources this year in preparation for inevitable cyber attacks. While half are increasing spending, most are investing in active response capabilities rather than infrastructure. Only a small minority of companies express high confidence in the security of their information, and many see serious business disruption risks from cyber attacks.
Strengths & Skills

Brian Michalicka outlines his experience simplifying processes, discovering new markets, establishing performance guarantees, and uncovering significant new business opportunities despite minimal market share. He emphasizes the importance of believing in solutions, focusing on customers, earning the right to advance through involvement, and achieving connectedness through understanding and providing for roles across healthcare silos and industries.
State of The Industry, Digiday Publishing Summit Key Biscayne, September 20th...

This document summarizes the state of the online publishing industry in 2016 according to a survey. The key findings are:
1) While technologies like DSPs and DMPs are growing, publishers remain split on solutions with lack of consensus in the industry.
2) Advertisers are primarily asking publishers about inventory quality, viewability, brand lift, and other direct response metrics.
3) The top hurdles publishers face in growing revenue are advertiser education, deal execution, internal conflicts, and exchange/SSP management.
4) Audience extension has become a major focus, with 74% of publishers offering it on about half their campaigns and 1/3 attributing at least 20% of revenue
Firms flock to Managed Security Services as cyber security pains increase

Cyber security trends in the UK
Enterprises today are faced with three key challenges:
- Implementing new SMAC technologies to support the business, as part of their digital transformation programs, but while keeping it secure;
- Responding to the increasing and changing threat landscape of targeted attacks;
- Achieving and retaining compliance with an increasing number of rules and regulations.
How do enterprises respond, in the context of a nationwide shortage in cyber security skills? Our hypothesis for this study was that enterprises are struggling to cope with the increase in workload, and are increasingly offloading (some of) their security provision to outsourcing providers as Managed Security Services (MSS). We surveyed 230 decision makers in large companies (1000+ employees) in the UK, to understand their motivations and drivers with regard to cyber security provision.
This study deals with the following questions:
- What do companies understand about the growing cyber threat landscape?
- How are companies meeting their resource challenges in cyber security?
- How are they using external providers to meet resource challenges?
- What are the drivers and inhibitors for using external cyber security providers?
- What alternative approaches to external cyber security provision being considered?
- Which services do companies expect from a cyber security provider?
- What are the capabilities and attributes of a credible cyber security provider?
Recommandé
3 FAQs on COVID-19 Induced Supply Chain Disruptions

The document discusses 3 common questions about using supply chain analytics to address risks and disruptions caused by COVID-19: how analytics can help manage supply chain disruption risks, how analytics solutions can mitigate disruptions, and what strategies companies can use going forward. It then invites the reader to contact them for assistance with supply chain analytics.
Stop wire fraud aug 2016

The document summarizes Guardian Analytics' wire fraud protection solution. It discusses the rise of business email compromise (BEC) wire fraud, with funds lost increasing over 400% from 2015 to 2016. Guardian Analytics protects customers of the Fiserv wire transfer platform WireXchange through real-time risk scoring of wire transactions. This solution has successfully prevented millions of dollars in fraudulent wires for various banks and credit unions. The document promotes Guardian Analytics' fraud detection capabilities and provides customer testimonials and a diagram of how its real-time wire monitoring works integrated with the WireXchange system.
Guardian analytics vs. actimize 2016

This document summarizes the capabilities of Guardian Analytics' machine learning and behavioral analytics solutions for financial fraud detection compared to Actimize. It states that Guardian Analytics offers omni-channel visibility, behavioral analytics that require no rules, and machine learning that continuously updates models without human intervention. It also provides rapid deployment, flexible hosting options, visual analytics, and integrates risk data from multiple sources. In contrast, it describes Actimize as having poor user interfaces, requiring extensive rule maintenance, long deployments, and high costs.
State of The Industry Presented By Grapeshot, Digiday Programmatic Summit, Ma...

This document summarizes the findings of a state of the industry report on the relationship between media agencies and trading desks. It finds that while many agencies and trading desks have an ambivalent relationship, transparency breeds trust. It also shows that most clients' top need is brand safety and content protection. Additionally, it reveals that trading desks hold more power over targeting and optimization decisions than agency buying teams.
Cybersecurity's Impact on Innovation

Most small and mid-sized tech and healthcare companies are maintaining or increasing their cybersecurity resources this year in preparation for inevitable cyber attacks. While half are increasing spending, most are investing in active response capabilities rather than infrastructure. Only a small minority of companies express high confidence in the security of their information, and many see serious business disruption risks from cyber attacks.
Strengths & Skills

Brian Michalicka outlines his experience simplifying processes, discovering new markets, establishing performance guarantees, and uncovering significant new business opportunities despite minimal market share. He emphasizes the importance of believing in solutions, focusing on customers, earning the right to advance through involvement, and achieving connectedness through understanding and providing for roles across healthcare silos and industries.
State of The Industry, Digiday Publishing Summit Key Biscayne, September 20th...

This document summarizes the state of the online publishing industry in 2016 according to a survey. The key findings are:
1) While technologies like DSPs and DMPs are growing, publishers remain split on solutions with lack of consensus in the industry.
2) Advertisers are primarily asking publishers about inventory quality, viewability, brand lift, and other direct response metrics.
3) The top hurdles publishers face in growing revenue are advertiser education, deal execution, internal conflicts, and exchange/SSP management.
4) Audience extension has become a major focus, with 74% of publishers offering it on about half their campaigns and 1/3 attributing at least 20% of revenue
Firms flock to Managed Security Services as cyber security pains increase

Cyber security trends in the UK
Enterprises today are faced with three key challenges:
- Implementing new SMAC technologies to support the business, as part of their digital transformation programs, but while keeping it secure;
- Responding to the increasing and changing threat landscape of targeted attacks;
- Achieving and retaining compliance with an increasing number of rules and regulations.
How do enterprises respond, in the context of a nationwide shortage in cyber security skills? Our hypothesis for this study was that enterprises are struggling to cope with the increase in workload, and are increasingly offloading (some of) their security provision to outsourcing providers as Managed Security Services (MSS). We surveyed 230 decision makers in large companies (1000+ employees) in the UK, to understand their motivations and drivers with regard to cyber security provision.
This study deals with the following questions:
- What do companies understand about the growing cyber threat landscape?
- How are companies meeting their resource challenges in cyber security?
- How are they using external providers to meet resource challenges?
- What are the drivers and inhibitors for using external cyber security providers?
- What alternative approaches to external cyber security provision being considered?
- Which services do companies expect from a cyber security provider?
- What are the capabilities and attributes of a credible cyber security provider?
Automating The Cow Path

The document discusses various technologies that can be used to improve supply chain management processes, including e-procurement, electronic reverse auctions, procurement cards, inventory management systems, transportation management technologies, warehouse management systems, and the system development life cycle. It warns against simply automating existing inefficient "cow path" processes and provides tips for successful implementation of new technologies to streamline operations. Key technologies are described along with typical benefits observed, such as cost reductions from implementing e-procurement systems.
Transforming Pharmaceutical Operational Performance with Supply Chain Traceab...

This document discusses how track and trace technologies can transform pharmaceutical business performance by enabling supply chain as a strategic asset. It provides an overview of trends driving increased focus on supply chains, describes implications of track and trace on supply chain operations and security. The document also presents two case studies, one on a global pharmaceutical manufacturer and one on a leading drug store chain, analyzing potential benefits of track and trace technologies across various operational areas like inventory management, out-of-stock reduction, returns management, and more. It concludes by suggesting pharmaceutical companies need to address compliance responsibilities globally and prioritize an implementation plan to leverage investments in track and trace.
Collaborated Solutions Staying ahead of the Counterfeiters

Collaborated Solutions Staying ahead of the CounterfeitersAuthentication Solution Providers' Association (ASPA)
Integration of anti-counterfeiting solutions, physical with digital technologies play a vital role in staying ahead of the counterfeiters. While the trade of counterfeit has dramatically increased, tackling counterfeits is not impossible. For that we need to create zero tolerance position towards illegal activities (strict policy with our business partners and expect their full support in fighting any kind of illegal activities). There is a need to implemented a global strategy to efficiently combat production, trade and use of counterfeit and illegal products including awareness, training and development of anti-counterfeiting solutions. AML and Compliance Analytics 

AML and Compliance Analytics
- A Disrupting Technology for Compliance
- A New Approach to Mitigating Risk
- The Latest Tool for the Chief Compliance Officer
The Changing Last Mile

Understand how the traditional retail and delivery supply chain is undergoing huge transformation and how this affects post and parcel organizations.
How to Get Proactive about your Vendor Master Data: 4 tips for success

1) Most companies have large invoice volumes and vendor bases but manage vendor data with small teams of only 1-5 people. Continuous monitoring of vendor data over time is a key challenge due to the manual nature of most vendor registration and data maintenance processes.
2) About a third of companies do not have regular processes for cleaning vendor master data and 21% never close stale vendor accounts, increasing their risk. Poor vendor data quality has contributed to fraud incidents for 34% of respondents in the past 5 years.
3) While interest is growing in supplier portals, current usage is only 24% and integration with vendor master data is limited, with under half supporting vendor self-service. Most vendor data reporting remains managed manually
Assessing the compliance of your food supply chain--an integrated approach 

See the results of EtQ's supplier workshop and learn how to asses the compliance of your food supply chain.
Rx 360 FDANews Supplier Quality Mgt Congress Pres Rev B 97

The document discusses the challenges facing global supply chains, including counterfeiting and quality issues, and proposes the creation of Rx-360, a non-profit organization, to address these challenges through collaborative supplier evaluation, shared auditing, monitoring, and the development of new technologies. Rx-360 aims to increase confidence in supply chains and enhance patient safety by bringing together industry stakeholders to work on solutions. The document outlines Rx-360's mission, principles, operating model, and initial phases of infrastructure development, shared auditing, and technology.
equities evolution of trading.pdf

This document discusses the future of automation in equities trading based on a survey of 91 equities market participants. Key points:
- On average, 44% of equity trading volume is currently automated, though firms vary widely in their degree of automation. Most expect to increase their focus on automating processes over the next 1-3 years.
- Areas seen as most desirable for further automation include regulatory reporting, post-trade analysis, pre-trade price discovery, and post-trade processing.
- Automation is already highly developed for trade execution and order entry/staging, but regulatory requirements are driving greater automation of reporting, compliance checks, and post-trade analysis. Advanced data and cloud technologies are also enabling
Steps to Overcome Information Overload in Clinical Research

See slides from Veeva's Outsourcing Clinical Trials West Coast presentation.
This deck explores the driving forces behind the industrywide move to streamline information exchange in clinical trials. Learn about modern technologies that improve how organizations work together across the clinical environment and discover new approaches to sharing trial information with study partners.
RegTech and superannuation funds

This document discusses how RegTech is improving risk management, compliance, governance, and supervisory services for superannuation funds. It notes that regulatory changes are a major risk and that funds are finding changes overwhelming. RegTech helps address this through automating manual processes, monitoring compliance in real-time, and analyzing large datasets. The benefits of RegTech include increased efficiency, flexibility, security, and analytics capabilities. It also carries the risk of over-reliance on machines, so collaboration is important. The document provides advice on getting started with RegTech through assessing current state, options, and immediate opportunities while also considering additional risks.
On the-trail-to-traceability

The document discusses the results of a survey about traceability challenges in supply chains. It finds that while many executives express confidence in being able to trace problems up and down the supply chain, in reality most companies would take days or weeks to execute a recall. There are also low levels of automation and many concerns about risks like liability. However, upgrading traceability technology and handling recalls transparently could help build customer loyalty. Overall the challenges of compliance and complexity are significant but more companies investing in technology offers potential for improvement on the path to better traceability.
On the-trail-to-traceability

The document discusses the results of a survey about traceability challenges in supply chains. It finds that while many executives express confidence in being able to trace problems up and down the supply chain, nearly half of respondents said it would take days or weeks to execute a recall. Automation of trace processes is limited, and concerns around risks, costs, and regulatory compliance remain high. However, opportunities exist to improve traceability through technology upgrades and gain consumer loyalty by responsibly handling recalls.
Achieving GxP compliance with SAP S/4HANA in the AWS Cloud

Learn how you can achieve full GxP compliance when moving to SAP S/4HANA in the AWS Cloud. In the session, you’ll hear learnings and best practices for securing FDA approval in order to fully reap the benefits of cloud transformation.
4 Reasons Why Your Supply Chain is Broken_090215_fc

This document discusses reasons why a company's supply chain may be broken, including placing more attention on domestic versus international supply chains, products not getting to market on time due to lack of visibility and delays, and handling supply chain logistics in-house rather than partnering with a third-party logistics provider. It recommends investing more in international supply chain solutions and gaining end-to-end visibility across the global supply chain in order to improve timeliness, reduce risks and costs, and enhance decision making.
Supplier Risk: What You Don’t See Can Hurt You

Supplier risk incidents are the blind spots in your supply chain that place your organization under perennial threat. Mitigating these risks requires you to bring in not just the historical insights but also real-time information and predictive intelligence. This session features expert views as well as best practices on how to preemptively address supplier risk incidents and secure your organization from the unforeseen.
The Emerging Use of Community of Interest Networks to Manage Compliance withi...

The document discusses how Community of Interest (COIN) networks can be used to more efficiently manage supplier compliance documentation by allowing buyers and suppliers to post policies, procedures, certificates and other documents to a shared network, reducing duplication and improving visibility of compliance information in real-time. It notes that currently most organizations rely on inefficient manual systems to track thousands of compliance documents from numerous suppliers. COIN networks aim to address the challenges of insufficient time, budget and resources that many organizations face in effectively managing supplier compliance.
M2M report supply chain

Operational visibility, or knowing where shipments are and monitoring their environmental conditions in near real-time, is becoming critical for supply chain and transportation industries. Around 90% of respondents said improving operational visibility is important. While location information is commonly used, companies are increasingly using sensors to monitor temperature, security, and other conditions. Reasons for pursuing greater visibility include improving customer service, delivery times through data analytics, and strengthening competitiveness. A visibility gap exists across all transportation modes, especially with rail having the least information available. Those using visibility solutions report they help address challenges like timely information access.
EFT Operational Visibility Research Report

1) Around 90% of respondents saw improving operational visibility as critical or very important. Visibility gaps exist across all modes of transportation, especially with rail having the poorest visibility.
2) Companies have moved beyond just using location data and now commonly use temperature, security, and other data. Improving customer service is a key reason for deploying visibility technologies.
3) M2M technologies are growing as the preferred visibility technology, expected to surpass RFID and barcodes. Close to half of companies plan to use M2M in future deployments to gain more real-time operational insights.
Aligning Procurement and Payables to Strengthen Your Supply Chain - 56566

Why should procurement care about days payable outstanding and cash flow? Because strategies for managing cash and working capital can impact your supply chain. In this session, learn how procurement leaders are collaborating with colleagues in finance and AP to better manage cash and working capital while supporting suppliers’ cash flow needs.
Evaluación de t-MOOC universitario sobre competencias digitales docentes medi...

Evaluación de t-MOOC universitario sobre competencias digitales docentes medi...eraser Juan José Calderón
Evaluación de t-MOOC universitario sobre competencias
digitales docentes mediante juicio de expertos
según el Marco DigCompEdu.
Julio Cabero-Almenara
Universidad de Sevilla, Sevilla, España
cabero@us.es
Julio Barroso--‐Osuna
Universidad de Sevilla, Sevilla, España
jbarroso@us.es
Antonio Palacios--‐Rodríguez
Universidad de Sevilla, Sevilla, España
aprodriguez@us.es
Carmen Llorente--‐Cejudo
Universidad de Sevilla, Sevilla, España
karen@us.esCall for paper 71. Revista Comunicar

This document announces a special issue of the journal "Comunicar" on hate speech in communication. It provides details such as the issue date, submission deadline, thematic editors, and scope. The scope describes hate speech and calls for research analyzing hate speech messages, backgrounds, and intervention strategies. The document lists descriptive keywords and questions to guide submitted papers. It introduces the three thematic editors and provides their backgrounds and research interests related to communication, media, and online environments. Submission guidelines and relevant website links are also included.
Contenu connexe
Similaire à Infographic Does blockchain hold the key to a new age of supply chain transparency and trust?
Automating The Cow Path

The document discusses various technologies that can be used to improve supply chain management processes, including e-procurement, electronic reverse auctions, procurement cards, inventory management systems, transportation management technologies, warehouse management systems, and the system development life cycle. It warns against simply automating existing inefficient "cow path" processes and provides tips for successful implementation of new technologies to streamline operations. Key technologies are described along with typical benefits observed, such as cost reductions from implementing e-procurement systems.
Transforming Pharmaceutical Operational Performance with Supply Chain Traceab...

This document discusses how track and trace technologies can transform pharmaceutical business performance by enabling supply chain as a strategic asset. It provides an overview of trends driving increased focus on supply chains, describes implications of track and trace on supply chain operations and security. The document also presents two case studies, one on a global pharmaceutical manufacturer and one on a leading drug store chain, analyzing potential benefits of track and trace technologies across various operational areas like inventory management, out-of-stock reduction, returns management, and more. It concludes by suggesting pharmaceutical companies need to address compliance responsibilities globally and prioritize an implementation plan to leverage investments in track and trace.
Collaborated Solutions Staying ahead of the Counterfeiters

Collaborated Solutions Staying ahead of the CounterfeitersAuthentication Solution Providers' Association (ASPA)
Integration of anti-counterfeiting solutions, physical with digital technologies play a vital role in staying ahead of the counterfeiters. While the trade of counterfeit has dramatically increased, tackling counterfeits is not impossible. For that we need to create zero tolerance position towards illegal activities (strict policy with our business partners and expect their full support in fighting any kind of illegal activities). There is a need to implemented a global strategy to efficiently combat production, trade and use of counterfeit and illegal products including awareness, training and development of anti-counterfeiting solutions. AML and Compliance Analytics 

AML and Compliance Analytics
- A Disrupting Technology for Compliance
- A New Approach to Mitigating Risk
- The Latest Tool for the Chief Compliance Officer
The Changing Last Mile

Understand how the traditional retail and delivery supply chain is undergoing huge transformation and how this affects post and parcel organizations.
How to Get Proactive about your Vendor Master Data: 4 tips for success

1) Most companies have large invoice volumes and vendor bases but manage vendor data with small teams of only 1-5 people. Continuous monitoring of vendor data over time is a key challenge due to the manual nature of most vendor registration and data maintenance processes.
2) About a third of companies do not have regular processes for cleaning vendor master data and 21% never close stale vendor accounts, increasing their risk. Poor vendor data quality has contributed to fraud incidents for 34% of respondents in the past 5 years.
3) While interest is growing in supplier portals, current usage is only 24% and integration with vendor master data is limited, with under half supporting vendor self-service. Most vendor data reporting remains managed manually
Assessing the compliance of your food supply chain--an integrated approach 

See the results of EtQ's supplier workshop and learn how to asses the compliance of your food supply chain.
Rx 360 FDANews Supplier Quality Mgt Congress Pres Rev B 97

The document discusses the challenges facing global supply chains, including counterfeiting and quality issues, and proposes the creation of Rx-360, a non-profit organization, to address these challenges through collaborative supplier evaluation, shared auditing, monitoring, and the development of new technologies. Rx-360 aims to increase confidence in supply chains and enhance patient safety by bringing together industry stakeholders to work on solutions. The document outlines Rx-360's mission, principles, operating model, and initial phases of infrastructure development, shared auditing, and technology.
equities evolution of trading.pdf

This document discusses the future of automation in equities trading based on a survey of 91 equities market participants. Key points:
- On average, 44% of equity trading volume is currently automated, though firms vary widely in their degree of automation. Most expect to increase their focus on automating processes over the next 1-3 years.
- Areas seen as most desirable for further automation include regulatory reporting, post-trade analysis, pre-trade price discovery, and post-trade processing.
- Automation is already highly developed for trade execution and order entry/staging, but regulatory requirements are driving greater automation of reporting, compliance checks, and post-trade analysis. Advanced data and cloud technologies are also enabling
Steps to Overcome Information Overload in Clinical Research

See slides from Veeva's Outsourcing Clinical Trials West Coast presentation.
This deck explores the driving forces behind the industrywide move to streamline information exchange in clinical trials. Learn about modern technologies that improve how organizations work together across the clinical environment and discover new approaches to sharing trial information with study partners.
RegTech and superannuation funds

This document discusses how RegTech is improving risk management, compliance, governance, and supervisory services for superannuation funds. It notes that regulatory changes are a major risk and that funds are finding changes overwhelming. RegTech helps address this through automating manual processes, monitoring compliance in real-time, and analyzing large datasets. The benefits of RegTech include increased efficiency, flexibility, security, and analytics capabilities. It also carries the risk of over-reliance on machines, so collaboration is important. The document provides advice on getting started with RegTech through assessing current state, options, and immediate opportunities while also considering additional risks.
On the-trail-to-traceability

The document discusses the results of a survey about traceability challenges in supply chains. It finds that while many executives express confidence in being able to trace problems up and down the supply chain, in reality most companies would take days or weeks to execute a recall. There are also low levels of automation and many concerns about risks like liability. However, upgrading traceability technology and handling recalls transparently could help build customer loyalty. Overall the challenges of compliance and complexity are significant but more companies investing in technology offers potential for improvement on the path to better traceability.
On the-trail-to-traceability

The document discusses the results of a survey about traceability challenges in supply chains. It finds that while many executives express confidence in being able to trace problems up and down the supply chain, nearly half of respondents said it would take days or weeks to execute a recall. Automation of trace processes is limited, and concerns around risks, costs, and regulatory compliance remain high. However, opportunities exist to improve traceability through technology upgrades and gain consumer loyalty by responsibly handling recalls.
Achieving GxP compliance with SAP S/4HANA in the AWS Cloud

Learn how you can achieve full GxP compliance when moving to SAP S/4HANA in the AWS Cloud. In the session, you’ll hear learnings and best practices for securing FDA approval in order to fully reap the benefits of cloud transformation.
4 Reasons Why Your Supply Chain is Broken_090215_fc

This document discusses reasons why a company's supply chain may be broken, including placing more attention on domestic versus international supply chains, products not getting to market on time due to lack of visibility and delays, and handling supply chain logistics in-house rather than partnering with a third-party logistics provider. It recommends investing more in international supply chain solutions and gaining end-to-end visibility across the global supply chain in order to improve timeliness, reduce risks and costs, and enhance decision making.
Supplier Risk: What You Don’t See Can Hurt You

Supplier risk incidents are the blind spots in your supply chain that place your organization under perennial threat. Mitigating these risks requires you to bring in not just the historical insights but also real-time information and predictive intelligence. This session features expert views as well as best practices on how to preemptively address supplier risk incidents and secure your organization from the unforeseen.
The Emerging Use of Community of Interest Networks to Manage Compliance withi...

The document discusses how Community of Interest (COIN) networks can be used to more efficiently manage supplier compliance documentation by allowing buyers and suppliers to post policies, procedures, certificates and other documents to a shared network, reducing duplication and improving visibility of compliance information in real-time. It notes that currently most organizations rely on inefficient manual systems to track thousands of compliance documents from numerous suppliers. COIN networks aim to address the challenges of insufficient time, budget and resources that many organizations face in effectively managing supplier compliance.
M2M report supply chain

Operational visibility, or knowing where shipments are and monitoring their environmental conditions in near real-time, is becoming critical for supply chain and transportation industries. Around 90% of respondents said improving operational visibility is important. While location information is commonly used, companies are increasingly using sensors to monitor temperature, security, and other conditions. Reasons for pursuing greater visibility include improving customer service, delivery times through data analytics, and strengthening competitiveness. A visibility gap exists across all transportation modes, especially with rail having the least information available. Those using visibility solutions report they help address challenges like timely information access.
EFT Operational Visibility Research Report

1) Around 90% of respondents saw improving operational visibility as critical or very important. Visibility gaps exist across all modes of transportation, especially with rail having the poorest visibility.
2) Companies have moved beyond just using location data and now commonly use temperature, security, and other data. Improving customer service is a key reason for deploying visibility technologies.
3) M2M technologies are growing as the preferred visibility technology, expected to surpass RFID and barcodes. Close to half of companies plan to use M2M in future deployments to gain more real-time operational insights.
Aligning Procurement and Payables to Strengthen Your Supply Chain - 56566

Why should procurement care about days payable outstanding and cash flow? Because strategies for managing cash and working capital can impact your supply chain. In this session, learn how procurement leaders are collaborating with colleagues in finance and AP to better manage cash and working capital while supporting suppliers’ cash flow needs.
Similaire à Infographic Does blockchain hold the key to a new age of supply chain transparency and trust? (20)
Transforming Pharmaceutical Operational Performance with Supply Chain Traceab...

Transforming Pharmaceutical Operational Performance with Supply Chain Traceab...
Collaborated Solutions Staying ahead of the Counterfeiters

Collaborated Solutions Staying ahead of the Counterfeiters
How to Get Proactive about your Vendor Master Data: 4 tips for success

How to Get Proactive about your Vendor Master Data: 4 tips for success
Assessing the compliance of your food supply chain--an integrated approach 

Assessing the compliance of your food supply chain--an integrated approach
Rx 360 FDANews Supplier Quality Mgt Congress Pres Rev B 97

Rx 360 FDANews Supplier Quality Mgt Congress Pres Rev B 97
Steps to Overcome Information Overload in Clinical Research

Steps to Overcome Information Overload in Clinical Research
Achieving GxP compliance with SAP S/4HANA in the AWS Cloud

Achieving GxP compliance with SAP S/4HANA in the AWS Cloud
4 Reasons Why Your Supply Chain is Broken_090215_fc

4 Reasons Why Your Supply Chain is Broken_090215_fc
The Emerging Use of Community of Interest Networks to Manage Compliance withi...

The Emerging Use of Community of Interest Networks to Manage Compliance withi...
Aligning Procurement and Payables to Strengthen Your Supply Chain - 56566

Aligning Procurement and Payables to Strengthen Your Supply Chain - 56566
Plus de eraser Juan José Calderón
Evaluación de t-MOOC universitario sobre competencias digitales docentes medi...

Evaluación de t-MOOC universitario sobre competencias digitales docentes medi...eraser Juan José Calderón
Evaluación de t-MOOC universitario sobre competencias
digitales docentes mediante juicio de expertos
según el Marco DigCompEdu.
Julio Cabero-Almenara
Universidad de Sevilla, Sevilla, España
cabero@us.es
Julio Barroso--‐Osuna
Universidad de Sevilla, Sevilla, España
jbarroso@us.es
Antonio Palacios--‐Rodríguez
Universidad de Sevilla, Sevilla, España
aprodriguez@us.es
Carmen Llorente--‐Cejudo
Universidad de Sevilla, Sevilla, España
karen@us.esCall for paper 71. Revista Comunicar

This document announces a special issue of the journal "Comunicar" on hate speech in communication. It provides details such as the issue date, submission deadline, thematic editors, and scope. The scope describes hate speech and calls for research analyzing hate speech messages, backgrounds, and intervention strategies. The document lists descriptive keywords and questions to guide submitted papers. It introduces the three thematic editors and provides their backgrounds and research interests related to communication, media, and online environments. Submission guidelines and relevant website links are also included.
Editorial of the JBBA Vol 4, Issue 1, May 2021. Naseem Naqvi, 

Editorial of the JBBA Vol 4, Issue 1, May 2021. Naseem Naqvi, FBBA FRCP FHEA MSc MAcadMEd
REGULATION OF THE EUROPEAN PARLIAMENT AND OF THE COUNCIL LAYING DOWN HARMONIS...

REGULATION OF THE EUROPEAN PARLIAMENT AND OF THE COUNCIL LAYING DOWN HARMONIS...eraser Juan José Calderón
Proposal for a
REGULATION OF THE EUROPEAN PARLIAMENT AND OF THE COUNCIL
LAYING DOWN HARMONISED RULES ON ARTIFICIAL INTELLIGENCE
(ARTIFICIAL INTELLIGENCE ACT) AND AMENDING CERTAIN UNION
LEGISLATIVE ACTS
Predicting Big Data Adoption in Companies With an Explanatory and Predictive ...

Predicting Big Data Adoption in Companies With an Explanatory and Predictive ...eraser Juan José Calderón
Predicting Big Data Adoption in Companies With an Explanatory and Predictive Model
Predecir la adopción de Big Data en empresas con un modelo explicativo y predictivo. @currovillarejo @jpcabrera71 @gutiker y @fliebcInnovar con blockchain en las ciudades: Ideas para lograrlo, casos de uso y a...

Innovar con blockchain en las ciudades: Ideas para lograrlo, casos de uso y a...eraser Juan José Calderón
Innovar con blockchain en las ciudades: Ideas para lograrlo, casos de uso y aplicaciones en Las Rozas. AgendaInnovar con blockchain en las ciudades: Ideas para lograrlo, casos de uso y a...

Innovar con blockchain en las ciudades: Ideas para lograrlo, casos de uso y a...eraser Juan José Calderón
La jornada analizó casos reales de uso de blockchain y sus posibilidades en Las Rozas a través de varias mesas redondas. Se presentó el proyecto DeConfianza que usa blockchain para dar transparencia a la compra de viviendas. También se discutió el potencial de la identidad digital soberana basada en blockchain y algunas aplicaciones posibles en Las Rozas como la gestión energética. Las Rozas fue elogiado como un espacio para probar innovaciones como blockchain.Ética y Revolución Digital . revista Diecisiete nº 4. 2021

Ética y Revolución Digital
Revista Diecisiete nº 4 2021. Investigación Interdisciplinar para los Objetivos de Desarrollo Sostenible.
PANORAMA
Ética y Derecho en la Revolución Digital
Txetxu Ausín y Margarita Robles Carrillo
artículoS
¿Cuarta Revolución Industrial? El reto de la digitalización y sus consecuencias ambientales y antropológicas
Joaquín Fernández Mateo
Hacia una ética del ecosistema híbrido del espacio físico y el ciberespacio
Ángel Gómez de Ágreda y Claudio Feijóo
Aprendizaje-Servicio y Agenda 2030 en la formación de ingenieros de la tecnología inteligente
Angeles Manjarrés y Simon Pickin
Tecnología Humanitaria como catalizadora de una nueva arquitectura de Acción Exterior en España: Horizonte 2030
Raquel Esther Jorge Ricart
Revolución digital, tecnooptimismo y educación
Ricardo Riaza
Desafíos éticos en la aplicación de la inteligencia artificial a los sistemas de defensa
Juan A. Moliner González
notas y colaboraciones
Hacerse viral: las actividades artísticas y su respuesta ante los retos que impone la transformación digital
Marta Pérez Ibáñez
Salud digital: una oportunidad y un imperativo ético
Joan Bigorra Llosas y Laura Sampietro-Colom
El futuro digital del sector energético
Beatriz Crisóstomo Merino y María Luz Cruz Aparicio
Innovación y transformación digital en las ONG. La visión de Acción contra el Hambre
Víctor Giménez Sánchez de la Blanca
El impacto de la inteligencia artificial en la Sociedad y su aplicación en el sector financiero
María Asunción Gilsanz Muñoz
La ética en los estudios de ingeniería
Rafael Miñano Rubio y Gonzalo Génova Fuster
An ethical and sustainable future of work
David Pastor-Escuredo, Gianni Giacomelli, Julio Lumbreras y Juan Garbajosa
Los datos en una administración pública digital - Perspectiva Uruguay
María Laura Rodríguez Mendaro
Ciudades y digitalización: construyendo desde la ética
David Pastor-Escuredo, Celia Fernandez-Aller, Jesus Salgado, Leticia Izquierdo y María Ángeles Huerta
#StopBigTechGoverningBigTech . More than 170 Civil Society Groups Worldwide O...

#StopBigTechGoverningBigTech . More than 170 Civil Society Groups Worldwide O...eraser Juan José Calderón
#StopBigTechGoverningBigTech: More than 170 Civil Society Groups Worldwide Oppose Plans for a
Big Tech Dominated Body for Global Digital Governance.
Not only in developing countries but also in the US and EU, calls for stronger regulation of Big Tech
are rising. At the precise point when we should be shaping global norms to regulate Big Tech, plans
have emerged for an ‘empowered’ global digital governance body that will evidently be dominated
by Big Tech. Adding vastly to its already overweening power, this new Body would help Big Tech
resist effective regulation, globally and at national levels. Indeed, we face the unbelievable prospect
of ‘a Big Tech led body for Global Governance of Big Tech’. PACTO POR LA CIENCIA Y LA INNOVACIÓN 8 de febrero de 2021

Este documento presenta un pacto por la ciencia y la innovación en España. Propone aumentar la inversión pública en I+D+I gradualmente hasta alcanzar el 1.25% del PIB en 2030 para alcanzar los niveles de inversión de la UE. También compromete dotar de autonomía a las entidades financiadoras de I+D+I y consolidar una carrera pública estable para los investigadores.
Expert Panel of the European Blockchain Observatory and Forum

The document announces the expert panel members of the European Blockchain Observatory and Forum. It lists over 100 experts from academia and industry across Europe who will advise on strengthening the European blockchain ecosystem. The experts come from a variety of backgrounds including law, technology, finance, government, and consulting.
Desigualdades educativas derivadas del COVID-19 desde una perspectiva feminis...

Desigualdades educativas derivadas del COVID-19 desde una perspectiva feminis...eraser Juan José Calderón
Desigualdades educativas derivadas del COVID-19 desde una perspectiva feminista. Análisis de los discursos de profesionales de la educación madrileña.
Melani Penna Tosso * Mercedes Sánchez SáinzCristina Mateos CasadoUniversidad Complutense de Madrid, España
Objetivos: Especificar las principales dificultades percibidas por las profesoras y los departamentos y equipos de orientación en relación con la atención a las diversidades en la actual situación de pandemia generada por el COVID-19. Exponer las prácticas educativas implementadas por dichas profesionales para disminuir las desigualdades. Visibilizar desigualdades de género que se dan en el ámbito educativo, relacionadas con la situación de pandemia entre el alumnado, el profesorado y las familias, desde una perspectiva feminista. Analizar las propuestas de cambio que proponen estas profesionales de la educación ante posibles repeticiones de situaciones de emergencia similares.
Resultados: Los docentes se han visto sobrecargados por el trabajo en confinamiento, en general el tiempo de trabajo ha tomado las casas, los espacios familiares, el tiempo libre y los fines de semana. Las profesionales entrevistadas se ven obligadas a una conexión permanente, sin limitación horaria y con horarios condicionados por las familias del alumnado. Se distinguen dos períodos bien diferenciados, en que los objetivos pasaron de ser emocionales a académicos. Como problemática general surge la falta de coordinación dentro los centros educativos.
Método: Análisis de entrevistas semiestructuradas a través de la metodología de análisis crítico de discurso.
Fuente de datos: Entrevistas
Autores: Melani Penna Tosso, Mercedes Sánchez Sáinz y Cristina Mateos Casado
Año: 2020
Institución: Universidad Complutense de Madrid
País al que refiere el análisis: España
Tipo de publicación: Revista arbitrada"Experiencias booktuber: Más allá del libro y de la pantalla"

"Experiencias booktuber: Más allá del libro y de la pantalla"
Maria Del Mar Suárez
Cristina Alcaraz Andreu
University of Barcelona
2020, R. Roig-Vila (Coord.), J. M. Antolí Martínez & R. Díez Ros (Eds.), XARXES-INNOVAESTIC 2020. Llibre d’actes / REDES-INNOVAESTIC 2020. Libro de actas (pp. 479-480). Alacant: Universitat d'Alacant. ISBN: 978-84-09-20651-3.
The impact of digital influencers on adolescent identity building.

The impact of digital influencers on adolescent identity building
IROCAMM - Intenational Review Of Communication And Marketing Mix @unisevilla
Open educational resources (OER) in the Spanish universities

Recursos educativos abiertos (REA) en las universidades españolas. Open educational resources (OER) in the Spanish universities. Gema Santos-Hermosa; Eva Estupinyà; Brigit Nonó-Rius; Lidón París-Folch; Jordi Prats-Prat
El modelo flipped classroom: un reto para una enseñanza centrada en el alumno

El modelo flipped classroom: un reto para una enseñanza centrada en el alumnoeraser Juan José Calderón
Este documento presenta el índice del número 391 de la Revista de Educación, correspondiente a enero-marzo de 2021. La revista es un medio de difusión de investigaciones y avances en educación publicado por el Ministerio de Educación de España. El número presentado es monotemático y se centra en el modelo de enseñanza conocido como "flipped classroom". Incluye 7 artículos en la sección monográfica sobre este tema y una sección de investigaciones.Pensamiento propio e integración transdisciplinaria en la epistémica social. ...

Pensamiento propio e integración transdisciplinaria en la epistémica social. ...eraser Juan José Calderón
This document discusses using one's own thinking as a pedagogical strategy to promote critical thinking, leadership, and humanism in university students. It describes teaching an epistemology course where collaborative dynamics and transdisciplinary integration were used to develop students' cognitive abilities and social construction of knowledge. The strategy began with collaborative practice in the classroom and concluded with students publishing a reflective journal.Escuela de Robótica de Misiones. Un modelo de educación disruptiva.

Escuela de Robótica de Misiones. Un modelo de educación disruptiva. 2019, Ed21. Fundación Santillana.
Carola Aideé Silvero
María Aurelia Escalada
Colaboradores:
Alejandro Piscitelli
Flavia Morales
Julio Alonso
La Universidad española Frente a la pandemia. Actuaciones de Crue Universidad...

La Universidad española Frente a la pandemia. Actuaciones de Crue Universidad...eraser Juan José Calderón
Este documento resume el contexto internacional de la pandemia de COVID-19 y sus efectos en la educación superior a nivel mundial. Se cerraron universidades en 185 países, afectando al 90% de los estudiantes. Las instituciones tuvieron que adaptar rápidamente la enseñanza a la modalidad online. Organismos internacionales como la UNESCO y el Banco Mundial publicaron recomendaciones para garantizar la continuidad educativa y mitigar los impactos sociales y económicos a corto y largo plazo. Además, asociacionesCovid-19 and IoT: Some Perspectives on the Use of IoT Technologies in Prevent...

Covid-19 and IoT: Some Perspectives on the Use of IoT Technologies in Prevent...eraser Juan José Calderón
Covid-19 and IoT: Some Perspectives on the Use of
IoT Technologies in Preventing and Monitoring
COVID-19 Like Infectious Diseases & Lessons
Learned and Impact of Pandemic on IoTPlus de eraser Juan José Calderón (20)
Evaluación de t-MOOC universitario sobre competencias digitales docentes medi...

Evaluación de t-MOOC universitario sobre competencias digitales docentes medi...
Editorial of the JBBA Vol 4, Issue 1, May 2021. Naseem Naqvi, 

Editorial of the JBBA Vol 4, Issue 1, May 2021. Naseem Naqvi,
REGULATION OF THE EUROPEAN PARLIAMENT AND OF THE COUNCIL LAYING DOWN HARMONIS...

REGULATION OF THE EUROPEAN PARLIAMENT AND OF THE COUNCIL LAYING DOWN HARMONIS...
Predicting Big Data Adoption in Companies With an Explanatory and Predictive ...

Predicting Big Data Adoption in Companies With an Explanatory and Predictive ...
Innovar con blockchain en las ciudades: Ideas para lograrlo, casos de uso y a...

Innovar con blockchain en las ciudades: Ideas para lograrlo, casos de uso y a...
Innovar con blockchain en las ciudades: Ideas para lograrlo, casos de uso y a...

Innovar con blockchain en las ciudades: Ideas para lograrlo, casos de uso y a...
Ética y Revolución Digital . revista Diecisiete nº 4. 2021

Ética y Revolución Digital . revista Diecisiete nº 4. 2021
#StopBigTechGoverningBigTech . More than 170 Civil Society Groups Worldwide O...

#StopBigTechGoverningBigTech . More than 170 Civil Society Groups Worldwide O...
PACTO POR LA CIENCIA Y LA INNOVACIÓN 8 de febrero de 2021

PACTO POR LA CIENCIA Y LA INNOVACIÓN 8 de febrero de 2021
Expert Panel of the European Blockchain Observatory and Forum

Expert Panel of the European Blockchain Observatory and Forum
Desigualdades educativas derivadas del COVID-19 desde una perspectiva feminis...

Desigualdades educativas derivadas del COVID-19 desde una perspectiva feminis...
"Experiencias booktuber: Más allá del libro y de la pantalla"

"Experiencias booktuber: Más allá del libro y de la pantalla"
The impact of digital influencers on adolescent identity building.

The impact of digital influencers on adolescent identity building.
Open educational resources (OER) in the Spanish universities

Open educational resources (OER) in the Spanish universities
El modelo flipped classroom: un reto para una enseñanza centrada en el alumno

El modelo flipped classroom: un reto para una enseñanza centrada en el alumno
Pensamiento propio e integración transdisciplinaria en la epistémica social. ...

Pensamiento propio e integración transdisciplinaria en la epistémica social. ...
Escuela de Robótica de Misiones. Un modelo de educación disruptiva.

Escuela de Robótica de Misiones. Un modelo de educación disruptiva.
La Universidad española Frente a la pandemia. Actuaciones de Crue Universidad...

La Universidad española Frente a la pandemia. Actuaciones de Crue Universidad...
Covid-19 and IoT: Some Perspectives on the Use of IoT Technologies in Prevent...

Covid-19 and IoT: Some Perspectives on the Use of IoT Technologies in Prevent...
Dernier
5th LF Energy Power Grid Model Meet-up Slides

5th Power Grid Model Meet-up
It is with great pleasure that we extend to you an invitation to the 5th Power Grid Model Meet-up, scheduled for 6th June 2024. This event will adopt a hybrid format, allowing participants to join us either through an online Mircosoft Teams session or in person at TU/e located at Den Dolech 2, Eindhoven, Netherlands. The meet-up will be hosted by Eindhoven University of Technology (TU/e), a research university specializing in engineering science & technology.
Power Grid Model
The global energy transition is placing new and unprecedented demands on Distribution System Operators (DSOs). Alongside upgrades to grid capacity, processes such as digitization, capacity optimization, and congestion management are becoming vital for delivering reliable services.
Power Grid Model is an open source project from Linux Foundation Energy and provides a calculation engine that is increasingly essential for DSOs. It offers a standards-based foundation enabling real-time power systems analysis, simulations of electrical power grids, and sophisticated what-if analysis. In addition, it enables in-depth studies and analysis of the electrical power grid’s behavior and performance. This comprehensive model incorporates essential factors such as power generation capacity, electrical losses, voltage levels, power flows, and system stability.
Power Grid Model is currently being applied in a wide variety of use cases, including grid planning, expansion, reliability, and congestion studies. It can also help in analyzing the impact of renewable energy integration, assessing the effects of disturbances or faults, and developing strategies for grid control and optimization.
What to expect
For the upcoming meetup we are organizing, we have an exciting lineup of activities planned:
-Insightful presentations covering two practical applications of the Power Grid Model.
-An update on the latest advancements in Power Grid -Model technology during the first and second quarters of 2024.
-An interactive brainstorming session to discuss and propose new feature requests.
-An opportunity to connect with fellow Power Grid Model enthusiasts and users.
UiPath Test Automation using UiPath Test Suite series, part 6

Welcome to UiPath Test Automation using UiPath Test Suite series part 6. In this session, we will cover Test Automation with generative AI and Open AI.
UiPath Test Automation with generative AI and Open AI webinar offers an in-depth exploration of leveraging cutting-edge technologies for test automation within the UiPath platform. Attendees will delve into the integration of generative AI, a test automation solution, with Open AI advanced natural language processing capabilities.
Throughout the session, participants will discover how this synergy empowers testers to automate repetitive tasks, enhance testing accuracy, and expedite the software testing life cycle. Topics covered include the seamless integration process, practical use cases, and the benefits of harnessing AI-driven automation for UiPath testing initiatives. By attending this webinar, testers, and automation professionals can gain valuable insights into harnessing the power of AI to optimize their test automation workflows within the UiPath ecosystem, ultimately driving efficiency and quality in software development processes.
What will you get from this session?
1. Insights into integrating generative AI.
2. Understanding how this integration enhances test automation within the UiPath platform
3. Practical demonstrations
4. Exploration of real-world use cases illustrating the benefits of AI-driven test automation for UiPath
Topics covered:
What is generative AI
Test Automation with generative AI and Open AI.
UiPath integration with generative AI
Speaker:
Deepak Rai, Automation Practice Lead, Boundaryless Group and UiPath MVP
AI 101: An Introduction to the Basics and Impact of Artificial Intelligence

Imagine a world where machines not only perform tasks but also learn, adapt, and make decisions. This is the promise of Artificial Intelligence (AI), a technology that's not just enhancing our lives but revolutionizing entire industries.
TrustArc Webinar - 2024 Global Privacy Survey

How does your privacy program stack up against your peers? What challenges are privacy teams tackling and prioritizing in 2024?
In the fifth annual Global Privacy Benchmarks Survey, we asked over 1,800 global privacy professionals and business executives to share their perspectives on the current state of privacy inside and outside of their organizations. This year’s report focused on emerging areas of importance for privacy and compliance professionals, including considerations and implications of Artificial Intelligence (AI) technologies, building brand trust, and different approaches for achieving higher privacy competence scores.
See how organizational priorities and strategic approaches to data security and privacy are evolving around the globe.
This webinar will review:
- The top 10 privacy insights from the fifth annual Global Privacy Benchmarks Survey
- The top challenges for privacy leaders, practitioners, and organizations in 2024
- Key themes to consider in developing and maintaining your privacy program
20240609 QFM020 Irresponsible AI Reading List May 2024

Everything I found interesting about the irresponsible use of machine intelligence in May 2024
Columbus Data & Analytics Wednesdays - June 2024

Columbus Data & Analytics Wednesdays, June 2024 with Maria Copot 20
Generating privacy-protected synthetic data using Secludy and Milvus

During this demo, the founders of Secludy will demonstrate how their system utilizes Milvus to store and manipulate embeddings for generating privacy-protected synthetic data. Their approach not only maintains the confidentiality of the original data but also enhances the utility and scalability of LLMs under privacy constraints. Attendees, including machine learning engineers, data scientists, and data managers, will witness first-hand how Secludy's integration with Milvus empowers organizations to harness the power of LLMs securely and efficiently.
Ocean lotus Threat actors project by John Sitima 2024 (1).pptx

Ocean Lotus cyber threat actors represent a sophisticated, persistent, and politically motivated group that poses a significant risk to organizations and individuals in the Southeast Asian region. Their continuous evolution and adaptability underscore the need for robust cybersecurity measures and international cooperation to identify and mitigate the threats posed by such advanced persistent threat groups.
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

A Mix Chart displays historical data of numbers in a graphical or tabular form. The Kalyan Rajdhani Mix Chart specifically shows the results of a sequence of numbers over different periods.
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

ABSTRACT: A prima vista, un mattoncino Lego e la backdoor XZ potrebbero avere in comune il fatto di essere entrambi blocchi di costruzione, o dipendenze di progetti creativi e software. La realtà è che un mattoncino Lego e il caso della backdoor XZ hanno molto di più di tutto ciò in comune.
Partecipate alla presentazione per immergervi in una storia di interoperabilità, standard e formati aperti, per poi discutere del ruolo importante che i contributori hanno in una comunità open source sostenibile.
BIO: Sostenitrice del software libero e dei formati standard e aperti. È stata un membro attivo dei progetti Fedora e openSUSE e ha co-fondato l'Associazione LibreItalia dove è stata coinvolta in diversi eventi, migrazioni e formazione relativi a LibreOffice. In precedenza ha lavorato a migrazioni e corsi di formazione su LibreOffice per diverse amministrazioni pubbliche e privati. Da gennaio 2020 lavora in SUSE come Software Release Engineer per Uyuni e SUSE Manager e quando non segue la sua passione per i computer e per Geeko coltiva la sua curiosità per l'astronomia (da cui deriva il suo nickname deneb_alpha).
GraphRAG for Life Science to increase LLM accuracy

GraphRAG for life science domain, where you retriever information from biomedical knowledge graphs using LLMs to increase the accuracy and performance of generated answers
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Discover the seamless integration of RPA (Robotic Process Automation), COMPOSER, and APM with AWS IDP enhanced with Slack notifications. Explore how these technologies converge to streamline workflows, optimize performance, and ensure secure access, all while leveraging the power of AWS IDP and real-time communication via Slack notifications.
How to Get CNIC Information System with Paksim Ga.pptx

Pakdata Cf is a groundbreaking system designed to streamline and facilitate access to CNIC information. This innovative platform leverages advanced technology to provide users with efficient and secure access to their CNIC details.
HCL Notes and Domino License Cost Reduction in the World of DLAU

Webinar Recording: https://www.panagenda.com/webinars/hcl-notes-and-domino-license-cost-reduction-in-the-world-of-dlau/
The introduction of DLAU and the CCB & CCX licensing model caused quite a stir in the HCL community. As a Notes and Domino customer, you may have faced challenges with unexpected user counts and license costs. You probably have questions on how this new licensing approach works and how to benefit from it. Most importantly, you likely have budget constraints and want to save money where possible. Don’t worry, we can help with all of this!
We’ll show you how to fix common misconfigurations that cause higher-than-expected user counts, and how to identify accounts which you can deactivate to save money. There are also frequent patterns that can cause unnecessary cost, like using a person document instead of a mail-in for shared mailboxes. We’ll provide examples and solutions for those as well. And naturally we’ll explain the new licensing model.
Join HCL Ambassador Marc Thomas in this webinar with a special guest appearance from Franz Walder. It will give you the tools and know-how to stay on top of what is going on with Domino licensing. You will be able lower your cost through an optimized configuration and keep it low going forward.
These topics will be covered
- Reducing license cost by finding and fixing misconfigurations and superfluous accounts
- How do CCB and CCX licenses really work?
- Understanding the DLAU tool and how to best utilize it
- Tips for common problem areas, like team mailboxes, functional/test users, etc
- Practical examples and best practices to implement right away
20240607 QFM018 Elixir Reading List May 2024

Everything I found interesting about the Elixir programming ecosystem in May 2024
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Discover how MongoDB Atlas and vector search technology can revolutionize your application's search capabilities. This comprehensive presentation covers:
* What is Vector Search?
* Importance and benefits of vector search
* Practical use cases across various industries
* Step-by-step implementation guide
* Live demos with code snippets
* Enhancing LLM capabilities with vector search
* Best practices and optimization strategies
Perfect for developers, AI enthusiasts, and tech leaders. Learn how to leverage MongoDB Atlas to deliver highly relevant, context-aware search results, transforming your data retrieval process. Stay ahead in tech innovation and maximize the potential of your applications.
#MongoDB #VectorSearch #AI #SemanticSearch #TechInnovation #DataScience #LLM #MachineLearning #SearchTechnology
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Simplify your search for a reliable Python development partner! This list presents the top 10 trusted US providers offering comprehensive Python development services, ensuring your project's success from conception to completion.
Dernier (20)
UiPath Test Automation using UiPath Test Suite series, part 6

UiPath Test Automation using UiPath Test Suite series, part 6
AI 101: An Introduction to the Basics and Impact of Artificial Intelligence

AI 101: An Introduction to the Basics and Impact of Artificial Intelligence
20240609 QFM020 Irresponsible AI Reading List May 2024

20240609 QFM020 Irresponsible AI Reading List May 2024
Generating privacy-protected synthetic data using Secludy and Milvus

Generating privacy-protected synthetic data using Secludy and Milvus
Ocean lotus Threat actors project by John Sitima 2024 (1).pptx

Ocean lotus Threat actors project by John Sitima 2024 (1).pptx
How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf

How to Interpret Trends in the Kalyan Rajdhani Mix Chart.pdf
Cosa hanno in comune un mattoncino Lego e la backdoor XZ?

Cosa hanno in comune un mattoncino Lego e la backdoor XZ?
GraphRAG for Life Science to increase LLM accuracy

GraphRAG for Life Science to increase LLM accuracy
Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack

Let's Integrate MuleSoft RPA, COMPOSER, APM with AWS IDP along with Slack
How to Get CNIC Information System with Paksim Ga.pptx

How to Get CNIC Information System with Paksim Ga.pptx
HCL Notes and Domino License Cost Reduction in the World of DLAU

HCL Notes and Domino License Cost Reduction in the World of DLAU
Nordic Marketo Engage User Group_June 13_ 2024.pptx

Nordic Marketo Engage User Group_June 13_ 2024.pptx
Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf

Unlock the Future of Search with MongoDB Atlas_ Vector Search Unleashed.pdf
Energy Efficient Video Encoding for Cloud and Edge Computing Instances

Energy Efficient Video Encoding for Cloud and Edge Computing Instances
Your One-Stop Shop for Python Success: Top 10 US Python Development Providers

Your One-Stop Shop for Python Success: Top 10 US Python Development Providers
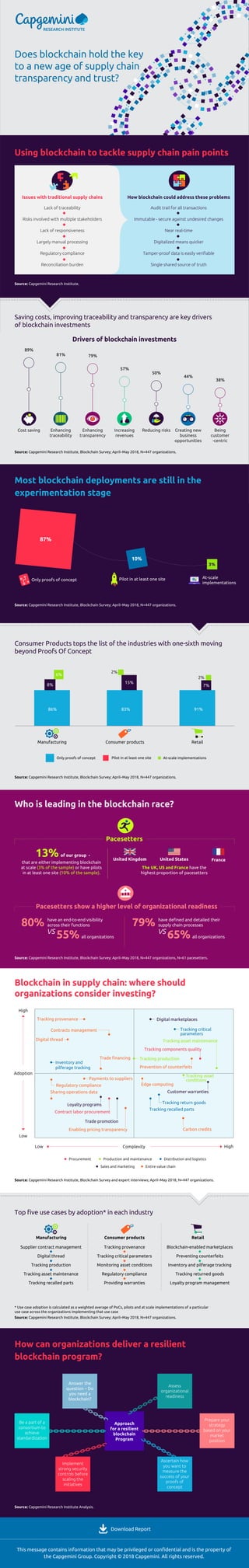
Infographic Does blockchain hold the key to a new age of supply chain transparency and trust?
- 1. United Kingdom FranceUnited States Does blockchain hold the key to a new age of supply chain transparency and trust? Saving costs, improving traceability and transparency are key drivers of blockchain investments Drivers of blockchain investments Source: Capgemini Research Institute, Blockchain Survey; April–May 2018, N=447 organizations. Source: Capgemini Research Institute, Blockchain Survey; April–May 2018, N=447 organizations. Using blockchain to tackle supply chain pain points Most blockchain deployments are still in the experimentation stage Who is leading in the blockchain race? Blockchain in supply chain: where should organizations consider investing? How can organizations deliver a resilient blockchain program? This message contains information that may be privileged or confidential and is the property of the Capgemini Group. Copyright © 2018 Capgemini. All rights reserved. Source: Capgemini Research Institute. Download Report 89% Cost saving Enhancing traceability Enhancing transparency Increasing revenues Reducing risks Creating new business opportunities Being customer -centric 81% 79% 57% 50% 44% 38% Consumer Products tops the list of the industries with one-sixth moving beyond Proofs Of Concept Pacesetters Source: Capgemini Research Institute, Blockchain Survey; April–May 2018, N=447 organizations. Source: Capgemini Research Institute, Blockchain Survey; April–May 2018, N=447 organizations, N=61 pacesetters. Source: Capgemini Research Institute, Blockchain Survey and expert interviews; April–May 2018, N=447 organizations. * Use case adoption is calculated as a weighted average of PoCs, pilots and at scale implementations of a particular use case across the organizations implementing that use case Source: Capgemini Research Institute, Blockchain Survey; April–May 2018, N=447 organizations. Source: Capgemini Research Institute Analysis. Top five use cases by adoption* in each industry Manufacturing that are either implementing blockchain at scale (3% of the sample) or have pilots in at least one site (10% of the sample). The UK, US and France have the highest proportion of pacesetters Consumer products Retail Only proofs of concept Pilot in at least one site At-scale implementations 86% 8% 2% 2% 6% 15% 7% 83% 91% Manufacturing Consumer products Retail Pilot in at least one site 87% 10% 3% Only proofs of concept At-scale implementations Pacesetters show a higher level of organizational readiness 13% of our group - have an end-to-end visibility across their functions Supplier contract management Digital thread Tracking production Tracking asset maintenance Tracking recalled parts Tracking provenance Tracking critical parameters Monitoring asset conditions Regulatory compliance Providing warranties Blockchain-enabled marketplaces Preventing counterfeits Inventory and pilferage tracking Tracking returned goods Loyalty program management vs 80% all organizations55% have defined and detailed their supply chain processes vs 79% all organizations65% Low Low High High Adoption Complexity Tracking provenance Tracking components quality Tracking production Inventory and pilferage tracking Tracking critical parameters Tracking return goods Tracking recalled parts Customer warranties Loyalty programs Tracking asset conditions Tracking asset maintenance Contracts management Prevention of counterfeits Enabling pricing transparency Contract labor procurement Digital thread Sharing operations data Carbon credits Trade financing Regulatory compliance Payments to suppliers Edge computing Digital marketplaces Trade promotion Procurement Production and maintenance Distribution and logistics Sales and marketing Entire value chain Approach for a resilient blockchain Program Be a part of a consortium to achieve standardization Implement strong security controls before scaling the initiatives Ascertain how you want to measure the success of your proofs of concept Assess organizational readiness Prepare your strategy based on your market position Answer the question – Do you need a blockchain? Issues with traditional supply chains Lack of traceability Risks involved with multiple stakeholders Lack of responsiveness Largely manual processing Regulatory compliance Reconciliation burden How blockchain could address these problems Audit trail for all transactions Immutable - secure against undesired changes Near real-time Digitalized means quicker Tamper-proof data is easily verifiable Single shared source of truth
