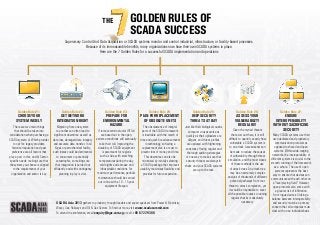
7 Golden Rules of Scada Success [Infographic]
- 1. The Golden Rules of SCADA Success Supervisory Control And Data Acquisition or SCADA systems monitor and control industrial, infrastructure, or facility-based processes. Because of its immeasurable benefits, many organizations now have their own SCADA systems in place. Here are the 7 Golden Rules for a successful SCADA implementation and operations Golden Rule #1: Golden Rule #2: Choose your system wisely Get network integration right There are two main things that should be taken into consideration when purchasing a SCADA system: a) Which provider to opt for: legacy providers, historical reputation and peer preference are all factors that play a part in this; and b) Sectorspecific needs: making sure that the system you choose is aligned to the requirements of your organisation and sector is key. Migrating from one system to another can often lead to significant downtime as well as data loss, damaged data integrity and accurate data transfer. In oil & gas or petrochemical facility, such losses could be detrimental to consumers or potentially catastrophic, so making sure that integration is carried out efficiently and with contingency planning in play is vital. Golden Rule #3: Prepare for environmental hazard If remote terminal units (RTUs) are based out in the open, extreme conditions will eventually take their toll. Improving the durability of SCADA equipment is paramount for regions such as Asia with scorching temperatures during the day, cold nights and abrasive and inhospitable conditions. For maximum performance, periodic maintenance should be carried out in-line with a 10 – 15 year equipment lifespan. Golden Rule #4: Golden Rule #5: Plan for replacement of obsolete units Keep security threats at bay The obsolescence of integral parts of the SCADA framework is inevitable with the march of time and quick-fire advancements in technology, so having a replacement plan is a must to prevent loss of money and time. This downtime can also be minimized by initially selecting a SCADA package that improves usability, maximises flexibility and provides for future expansion. Just like their biological cousins, computer viruses evolve as quickly as their uploaders are diligent, and threat profiles are updated with frightening constancy. Having regular and thorough auditing strategies is one way to make sure that security threats are always in check and your SCADA systems are up to the task. SCADA Asia 2013 gathers top industry thought leaders and expert speakers from Power & Electricity, Water, Gas, Railways and Oil & Gas Sectors. To find out more, visit www.scadasummit.com To attend the conference, email enquiry@iqpc.com.sg or call +65 6722 9388. Golden Rule #6: Assess your vulnerability regularly Given the myriad threats that exist out there, it is still difficult to quantify exactly how vulnerable a SCADA system is to an attack. Assessments can be made to reduce the causes of vulnerability through threat simulation, and the most classic of these methods is the use of attack trees. An attack tree may be an extremely complex analysis of thousands of different potential pathways from root threat to attack completion, yet it would be impossible to cover all the possible routes so running regular checks is absolutely necessary. Golden Rule #7: Ensure interoperability without sacrificing security Many SCADA systems use their own dedicated and proprietary communication protocols as opposed to shared and open systems. Within wide-ranging networks, the interoperability of different systems is crucial to the smooth running of the framework as a whole. The use of open systems represents the best way to ensure that devices can communicate with each other on a “level playing field.” However, open protocols also come with a greater risk of infiltration from rogue devices. Striking a balance between interoperability and security must be a primary concern that all companies must deal with on an individual basis.
