CHIME LEAD New York 2014 "Case Studies from the Field: Putting Cyber Security Strategies into Action"
CHIME LEAD New York 2014 "Case Studies from the Field: Putting Cyber Security Strategies into Action" Learn from those in the trenches who have deployed effective cyber strategies in their organizations, foiled attacks and managed breach situations. Learn approaches for success and pitfalls to avoid by exploring the experience of others with deployment and management of cyber security strategies and plans. Learning Objectives: Identify successes, challenges and lessons learned with implementation of cyber strategies Identify success strategies for gaining the C Suite support and ways cyber security can be integrated into the organization's culture and work processes. Identify best practices with anticipating new and emerging threats and ways to maintain a proactive position instead of reactive Identify approaches for breach preparation and breach management Featured Speakers: Neal Ganguly, MBA, FCHIME, FHIMSS, CHCIO VP & CIO JFK Health System Miroslav Belote Director of IT – Infrastructure and Information Security Officer JFK Health System Nassar Nizami CISO Yale-New Haven Health System
Recommandé
Recommandé
Contenu connexe
Tendances
Tendances (11)
Similaire à CHIME LEAD New York 2014 "Case Studies from the Field: Putting Cyber Security Strategies into Action"
Similaire à CHIME LEAD New York 2014 "Case Studies from the Field: Putting Cyber Security Strategies into Action" (20)
Plus de Health IT Conference – iHT2
Plus de Health IT Conference – iHT2 (20)
Dernier
Dernier (20)
CHIME LEAD New York 2014 "Case Studies from the Field: Putting Cyber Security Strategies into Action"
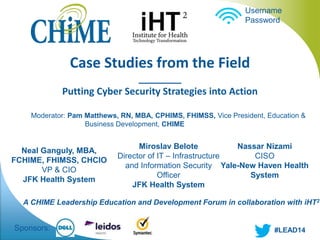
- 1. Moderator: Pam Matthews, RN, MBA, CPHIMS, FHIMSS, Vice President, Education & Business Development, CHIME Neal Ganguly, MBA, FCHIME, FHIMSS, CHCIO VP & CIO JFK Health System Username Password A CHIME Leadership Education and Development Forum in collaboration with iHT2 #LEAD14 Case Studies from the Field ________ Putting Cyber Security Strategies into Action Miroslav Belote Director of IT – Infrastructure and Information Security Officer JFK Health System Sponsors: Nassar Nizami CISO Yale-New Haven Health System
- 2. Case Studies from the Field ________ Putting Cyber Security Strategies into Action ● Speaker: Nassar Nizami, CISO, Yale-New Haven Health System ● A CHIME Leadership Education and Development Forum in collaboration with iHT2 #LEAD14
- 3. Yale New Haven Health System Who We Are • Four Member Delivery Network • Multiple Clinical Affiliations • Affiliated with Yale University • Destination Hospital for Patients Throughout the United States • Currently Going Through an Affiliation and Acquisition Period
- 5. Application Inventory • Inventory of applications in a spreadsheet with key information • Information we are interested in Information we require
- 7. Data Loss Prevention Email Desktop/ Laptops Web File shares Cloud Mobile Devices
- 8. Exact Data Match • Patten based matches • Common • xxx-xx-xxx • Potential SSN • False Positives • Exact Data Match • Match on known and indexed data • First Name, Last Name, MRN from EMR • First Name, Last Name,, Employee ID from HR system • False positives decrease significantly
- 9. Desktop/Laptop • Client installed on desktops and laptops • Scans for • Files copied to removable media • Internet traffic • Local drive scan • Pattern based matching (HIPAA Policies) • Data scanned when copied to removable media
- 10. Desktop Challenges Computer Slow Down Hardware Refresh Complete Desktop Scan Selective Scan Good Support for Windows OS Support Lacking for non-Windows OS
- 11. Web • Dedicated servers for HTTP • ~80% of our overall traffic • Dedicated servers to scan select protocols like FTP, IRC etc. • Traditionally not been a problem area • Ended up blocking many protocols • Challenges: • Encrypted traffic is tough to scan • Solution requires robust proxy server infrastructure and proper certificate deployment
- 12. Email • Policy requires that the emails with PHI or sensitive information must be encrypted manually • Keyword in subject line • Require prior approval • All outbound emails are scanned for PHI • Encrypted if PHI is found EDM HIPAA Lexicons Internet Internal Network • Challenges: • Images, especially screen shots • PDF files scanned as images • Encrypted attachments • False positives • Marketing & HR
- 13. File Shares • Started with ad-hoc scanning – First 2-3 years • Periodic since last year – Scanning has improved • Several terabytes in a couple of days
- 14. File Share Management • File share permission and auditing tool – Who has access to what shares? • Thousands of shares – Many more folders and sub-folders • Integrated with DLP – Flags folders with sensitive information – Extremely helpful in prioritizing
- 15. Governance & Timeline • Acquired solution • Implemented Email & Web – Email was a quick win • Desktop – four years for 80% coverage • Committee to direct implementation
- 16. Cloud & Mobile Devices • Hosted emails, Office365, Box.net etc. • No good solution • Some vendors offer basic DLP capabilities • Scanning maybe possible if data orginiates from corporate network • No good solution • Computing capability • Different OS • Limited access to API • VPN back to corporate • Slow • Can be bypassed
- 17. Lessons Learned User Communication Skilled Team Multiple Servers Part of Solution Slowness
- 18. Lessons Learned • User communication • Dedicated & skilled team – Takes time to understand false positives • Scalability – Plan for multiple servers with lots of processing power • DLP alone is not effective tool against someone who is trying to bypass controls – Part of a solution • Desktop client may cause slowness
- 19. Next Steps/Wish List • Notification to management • Active blocking of network protocols • Incorporate SSL – Technically challenging • Apple computers • Mobile device integration • Cloud based storage • Involve business*
- 20. reference
- 21. Facts & Figures • Medical staff 5675 • Employees 18,345 • Total Licensed Beds 2130 • Inpatient Discharges 93,923 • Outpatient Visits 1,397,632 • Total Assets $3.6 billion • Net Revenue $2.6 billion
- 22. Q & A Contact Information Nassar Nizami A CHIME Leadership Education and Development Forum in collaboration with iHT2
