IEEE PROJECTS 2013 for me
•
1 j'aime•941 vues
JAVA IEEE 2013 - 2014 IEEE PROJECT TITLES FOR STUDENTS B.E.,B.TECH.,M.E,M.TECH.,M.PHIL.,M.S.,MCA,M.S.,MBA AND DIPLOMA PROJECTS USING JAVA
Signaler
Partager
Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
Recommandé
A trigger identification service for defending reactive jammers in wireless sensor networkA trigger identification service for defending reactive jammers in wireless s...

A trigger identification service for defending reactive jammers in wireless s...JPINFOTECH JAYAPRAKASH
Hasbe a hierarchical attribute based solution for flexible and scalable access control in cloud computing PPTHasbe a hierarchical attribute based solution for flexible and scalable acces...

Hasbe a hierarchical attribute based solution for flexible and scalable acces...JPINFOTECH JAYAPRAKASH
Contenu connexe
Tendances
Tendances (16)
SEAD: Source Encrypted Authentic Data for Wireless Sensor Networks

SEAD: Source Encrypted Authentic Data for Wireless Sensor Networks
En vedette
A trigger identification service for defending reactive jammers in wireless sensor networkA trigger identification service for defending reactive jammers in wireless s...

A trigger identification service for defending reactive jammers in wireless s...JPINFOTECH JAYAPRAKASH
Hasbe a hierarchical attribute based solution for flexible and scalable access control in cloud computing PPTHasbe a hierarchical attribute based solution for flexible and scalable acces...

Hasbe a hierarchical attribute based solution for flexible and scalable acces...JPINFOTECH JAYAPRAKASH
Enabling dynamic data and indirect mutual trust for cloud computing storage systemsEnabling dynamic data and indirect mutual trust for cloud computing storage s...

Enabling dynamic data and indirect mutual trust for cloud computing storage s...JPINFOTECH JAYAPRAKASH
Adaptive membership functions for hand written character recognition by voronoi-based image zoningAdaptive membership functions for hand written character recognition by voron...

Adaptive membership functions for hand written character recognition by voron...JPINFOTECH JAYAPRAKASH
En vedette (15)
A trigger identification service for defending reactive jammers in wireless s...

A trigger identification service for defending reactive jammers in wireless s...
Hasbe a hierarchical attribute based solution for flexible and scalable acces...

Hasbe a hierarchical attribute based solution for flexible and scalable acces...
Enabling dynamic data and indirect mutual trust for cloud computing storage s...

Enabling dynamic data and indirect mutual trust for cloud computing storage s...
Adaptive membership functions for hand written character recognition by voron...

Adaptive membership functions for hand written character recognition by voron...
A gossip protocol for dynamic resource management in large cloud environments

A gossip protocol for dynamic resource management in large cloud environments
Similaire à IEEE PROJECTS 2013 for me
Similaire à IEEE PROJECTS 2013 for me (20)
ieee 2013 best project titles with latest techniques

ieee 2013 best project titles with latest techniques
IEEE JAVA DOTNET ANDROID PROJECT TITLES 2014 - 2015 

IEEE JAVA DOTNET ANDROID PROJECT TITLES 2014 - 2015
VTU Final Year Engineering Project Title List for Computer Science Engineerin...

VTU Final Year Engineering Project Title List for Computer Science Engineerin...
VTU Computer Science Engineering & Information Science Engineering Project Ti...

VTU Computer Science Engineering & Information Science Engineering Project Ti...
IEEE projects java and dotnet for BE BTECH ME MTECH MCA MCS Diploma

IEEE projects java and dotnet for BE BTECH ME MTECH MCA MCS Diploma
Ieee 2013 java project titles richbraintechnologies

Ieee 2013 java project titles richbraintechnologies
Dernier
APM Welcome
Tuesday 30 April 2024
APM North West Network Conference, Synergies Across Sectors
Presented by:
Professor Adam Boddison OBE, Chief Executive Officer, APM
Conference overview:
https://www.apm.org.uk/community/apm-north-west-branch-conference/
Content description:
APM welcome from CEO
The main conference objective was to promote the Project Management profession with interaction between project practitioners, APM Corporate members, current project management students, academia and all who have an interest in projects.APM Welcome, APM North West Network Conference, Synergies Across Sectors

APM Welcome, APM North West Network Conference, Synergies Across SectorsAssociation for Project Management
This presentation was provided by William Mattingly of the Smithsonian Institution, during the fourth segment of the NISO training series "AI & Prompt Design." Session Four: Structured Data and Assistants, was held on April 25, 2024.Mattingly "AI & Prompt Design: Structured Data, Assistants, & RAG"

Mattingly "AI & Prompt Design: Structured Data, Assistants, & RAG"National Information Standards Organization (NISO)
Dernier (20)
APM Welcome, APM North West Network Conference, Synergies Across Sectors

APM Welcome, APM North West Network Conference, Synergies Across Sectors
Seal of Good Local Governance (SGLG) 2024Final.pptx

Seal of Good Local Governance (SGLG) 2024Final.pptx
Mattingly "AI & Prompt Design: Structured Data, Assistants, & RAG"

Mattingly "AI & Prompt Design: Structured Data, Assistants, & RAG"
Unit-V; Pricing (Pharma Marketing Management).pptx

Unit-V; Pricing (Pharma Marketing Management).pptx
Russian Escort Service in Delhi 11k Hotel Foreigner Russian Call Girls in Delhi

Russian Escort Service in Delhi 11k Hotel Foreigner Russian Call Girls in Delhi
Ecological Succession. ( ECOSYSTEM, B. Pharmacy, 1st Year, Sem-II, Environmen...

Ecological Succession. ( ECOSYSTEM, B. Pharmacy, 1st Year, Sem-II, Environmen...
ICT Role in 21st Century Education & its Challenges.pptx

ICT Role in 21st Century Education & its Challenges.pptx
Mixin Classes in Odoo 17 How to Extend Models Using Mixin Classes

Mixin Classes in Odoo 17 How to Extend Models Using Mixin Classes
Basic Civil Engineering first year Notes- Chapter 4 Building.pptx

Basic Civil Engineering first year Notes- Chapter 4 Building.pptx
Web & Social Media Analytics Previous Year Question Paper.pdf

Web & Social Media Analytics Previous Year Question Paper.pdf
Beyond the EU: DORA and NIS 2 Directive's Global Impact

Beyond the EU: DORA and NIS 2 Directive's Global Impact
IEEE PROJECTS 2013 for me
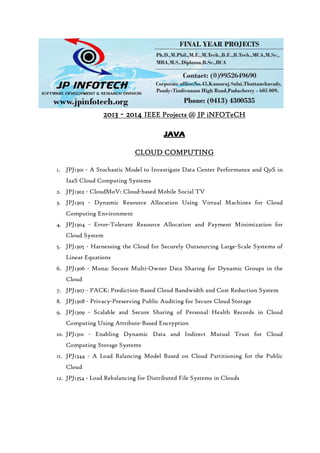
- 1. 2013201320132013 ---- 2014201420142014 IEEE ProjectsIEEE ProjectsIEEE ProjectsIEEE Projects @@@@ JP iNFOTeCHJP iNFOTeCHJP iNFOTeCHJP iNFOTeCH JAVAJAVAJAVAJAVA CLOUD COMPUTINGCLOUD COMPUTINGCLOUD COMPUTINGCLOUD COMPUTING 1. JPJ1301 - A Stochastic Model to Investigate Data Center Performance and QoS in IaaS Cloud Computing Systems 2. JPJ1302 - CloudMoV: Cloud-based Mobile Social TV 3. JPJ1303 - Dynamic Resource Allocation Using Virtual Machines for Cloud Computing Environment 4. JPJ1304 - Error-Tolerant Resource Allocation and Payment Minimization for Cloud System 5. JPJ1305 - Harnessing the Cloud for Securely Outsourcing Large-Scale Systems of Linear Equations 6. JPJ1306 - Mona: Secure Multi-Owner Data Sharing for Dynamic Groups in the Cloud 7. JPJ1307 - PACK: Prediction-Based Cloud Bandwidth and Cost Reduction System 8. JPJ1308 - Privacy-Preserving Public Auditing for Secure Cloud Storage 9. JPJ1309 - Scalable and Secure Sharing of Personal Health Records in Cloud Computing Using Attribute-Based Encryption 10. JPJ1310 - Enabling Dynamic Data and Indirect Mutual Trust for Cloud Computing Storage Systems 11. JPJ1344 - A Load Balancing Model Based on Cloud Partitioning for the Public Cloud 12. JPJ1354 - Load Rebalancing for Distributed File Systems in Clouds
- 2. 13. JPJ1359 – Optimizing Cloud Resources for Delivering IPTV Services Through Virtualization 14. JPJ1363 – Privacy Preserving Delegated Access Control in Public Clouds KNOWLEDGE AND DATA ENGINEERINGKNOWLEDGE AND DATA ENGINEERINGKNOWLEDGE AND DATA ENGINEERINGKNOWLEDGE AND DATA ENGINEERING 15. JPJ1311 - A Fast Clustering-Based Feature Subset Selection Algorithm for High- Dimensional Data 16. JPJ1312 - A New Algorithm for Inferring User Search Goals with Feedback Sessions 17. JPJ1313 - Annotating Search Results from Web Databases 18. JPJ1314 - Anomaly Detection via Online Over-Sampling Principal Component Analysis 19. JPJ1315 - Distributed Processing of Probabilistic Top-k Queries in Wireless Sensor Networks 20. JPJ1316- m-Privacy for Collaborative Data Publishing 21. JPJ1317 - Protecting Sensitive Labels in Social Network Data Anonymization 22. JPJ1318 - Tweet Analysis for Real-Time Event Detection and Earthquake Reporting System Development 23. JPJ1345 - Document Clustering for Forensic Analysis: An Approach for Improving Computer Inspection 24. JPJ1346 - A Method for Mining Infrequent Causal Associations and Its Application in Finding Adverse Drug Reaction Signal Pairs 25. JPJ1347 - Clustering Sentence-Level Text Using a Novel Fuzzy Relational Clustering Algorithm
- 3. 26. JPJ1358 - Crowdsourcing Predictors of Behavioral Outcomes 27. JPJ1362 - Facilitating Document Annotation using Content and Querying Value 28. JPJ1365 - A Generalized Flow-Based Method for Analysis of Implicit Relationships on Wikipedia 29. JPJ1366 - A System to Filter Unwanted Messages from OSN User Walls 30. JPJ1367 - Anonymization of Centralized and Distributed Social Networks by Sequential Clustering 31. JPJ1370 - Intrusion Detection Technique by using K-means, Fuzzy Neural Network and SVM classifiers. (CONFERENCE PAPER) SECURE COMPUTINGSECURE COMPUTINGSECURE COMPUTINGSECURE COMPUTING 32. JPJ1319 - EAACK—A Secure Intrusion-Detection System for MANETs 33. JPJ1320 - Identity-Based Secure Distributed Data Storage Schemes 34. JPJ1321 - Modeling the Pairwise Key Predistribution Scheme in the Presence of Unreliable Links 35. JPJ1322 - NICE: Network Intrusion Detection and Countermeasure Selection in Virtual Network Systems 36. JPJ1323 - Privacy Preserving Data Sharing With Anonymous ID Assignment 37. JPJ1324 - Securing Class Initialization in Java-like Languages 38. JPJ1325 - Security Analysis of a Single Sign-On Mechanism for Distributed Computer Networks 39. JPJ1326 -SORT: A Self-ORganizing Trust Model for Peer-to-Peer Systems 40. JPJ1327 - WARNINGBIRD: A Near Real-time Detection System for Suspicious URLs in Twitter Stream 41. JPJ1348 - Two tales of privacy in online social networks
- 4. 42. JPJ1361 - Secure Encounter-based Mobile Social Networks: Requirements, Designs, and Tradeoffs. 43. JPJ1364 - Twitsper: Tweeting Privately 44. JPJ1371 - Combining Cryptographic Primitives to Prevent Jamming Attacks in Wireless Networks (CONFERENCE PAPER) NETWORKINGNETWORKINGNETWORKINGNETWORKING 45. JPJ1328 - A Highly Scalable Key Pre-Distribution Scheme for Wireless Sensor Networks 46. JPJ1329 - Delay-Based Network Utility Maximization 47. JPJ1330 - Dynamic Control of Coding for Progressive Packet Arrivals in DTNs 48. JPJ1349 - Minimum Cost Blocking Problem in Multi-path Wireless Routing Protocols 49. JPJ1350 - On the Node Clone Detection in Wireless Sensor Networks 50. JPJ1351 - Opportunistic MANETs: Mobility Can Make Up for Low Transmission Power 51. JPJ1352 - Back-Pressure-Based Packet-by-Packet Adaptive Routing in Communication Networks 52. JPJ1353- Fast Transmission to Remote Cooperative Groups: A New Key Management Paradigm 53. JPJ1360 - Participatory Privacy: Enabling Privacy in Participatory Sensing
- 5. PARALLEL AND DISTRIBUTED SYSTEMSPARALLEL AND DISTRIBUTED SYSTEMSPARALLEL AND DISTRIBUTED SYSTEMSPARALLEL AND DISTRIBUTED SYSTEMS 54. JPJ1331 - A Secure Protocol for Spontaneous Wireless Ad Hoc Networks Creation 55. JPJ1332 - Security Analysis of a Privacy-Preserving Decentralized Key-Policy Attribute-Based Encryption Scheme 56. JPJ1333 - IP-Geolocation Mapping for Moderately Connected Internet Regions 57. JPJ1334 - Optimal Client-Server Assignment for Internet Distributed Systems MOBILE COMPUTINGMOBILE COMPUTINGMOBILE COMPUTINGMOBILE COMPUTING 58. JPJ1335 - Content Sharing over Smartphone-Based Delay-Tolerant Networks 59. JPJ1336 - DCIM: Distributed Cache Invalidation Method for Maintaining Cache Consistency in Wireless Mobile Networks 60. JPJ1337 - Discovery and Verification of Neighbor Positions in Mobile Ad Hoc Networks 61. JPJ1338 - Efficient Rekeying Framework for Secure Multicast with Diverse- Subscription-Period Mobile Users 62. JPJ1355 - Toward a Statistical Framework for Source Anonymity in Sensor Networks 63. JPJ1356 - Mobile Relay Configuration in Data-Intensive Wireless Sensor Networks 64. JPJ1357 - Vampire Attacks: Draining Life from Wireless Ad Hoc Sensor Networks 65. JPJ1368 - Toward Privacy Preserving and Collusion Resistance in a Location Proof Updating System
- 6. PATTERNPATTERNPATTERNPATTERN ANALYSIS AND MACHINE INTELLIGENCEANALYSIS AND MACHINE INTELLIGENCEANALYSIS AND MACHINE INTELLIGENCEANALYSIS AND MACHINE INTELLIGENCE 66. JPJ1339 - A Framework for Mining Signatures from Event Sequences and Its Applications in Healthcare Data SERVICES COMPUTINGSERVICES COMPUTINGSERVICES COMPUTINGSERVICES COMPUTING 67. JPJ1340 - A Decentralized Service Discovery Approach on Peer-to-Peer Networks 68. JPJ1341 - Personalized QoS-Aware Web Service Recommendation and Visualization 69. JPJ1342 - Privacy-Enhanced Web Service Composition SOFTWARE ENGINEERINGSOFTWARE ENGINEERINGSOFTWARE ENGINEERINGSOFTWARE ENGINEERING 70. JPJ1343 - Whole Test Suite Generation MULTIMEDIAMULTIMEDIAMULTIMEDIAMULTIMEDIA 71. JPJ1369 - Understanding the External Links of Video Sharing Sites: Measurement and Analysis
