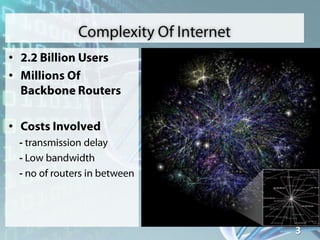
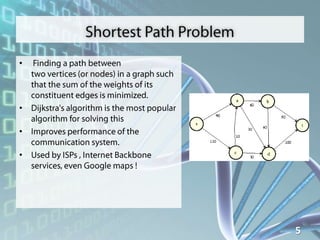
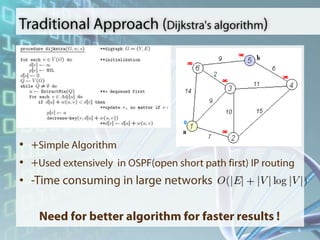
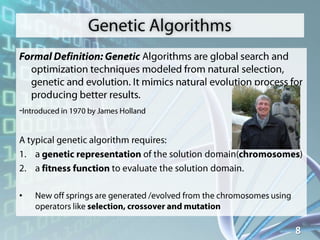
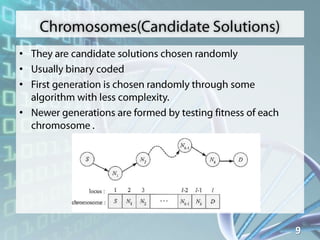
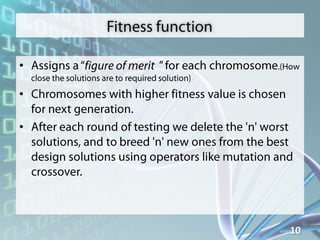
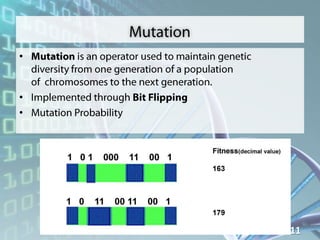
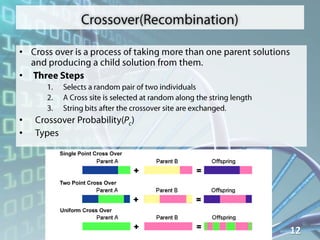
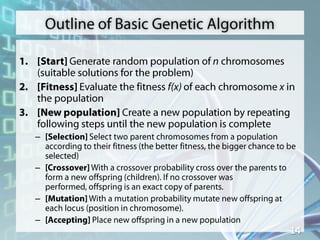
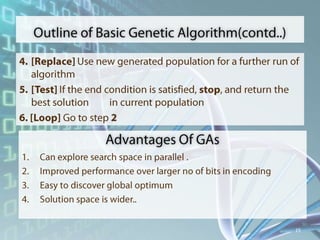
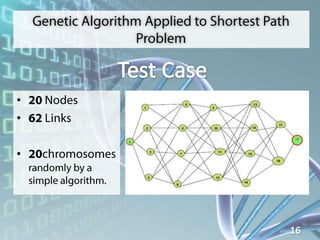
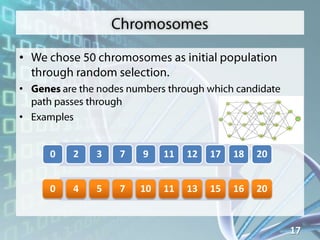
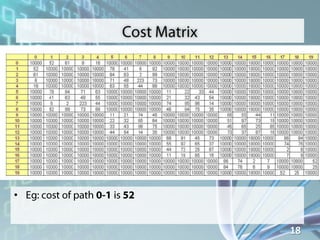
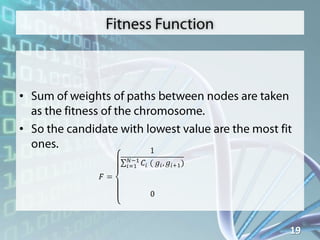
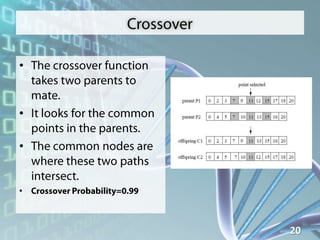
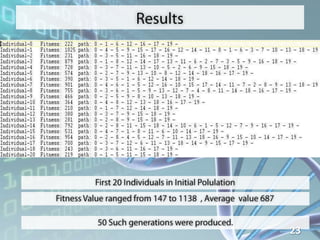
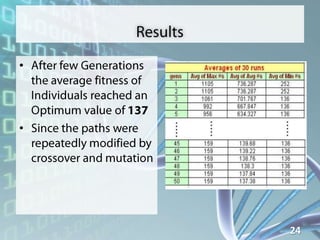
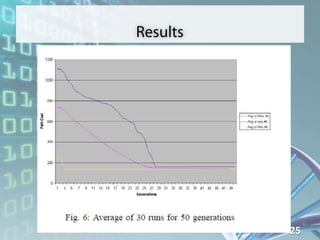
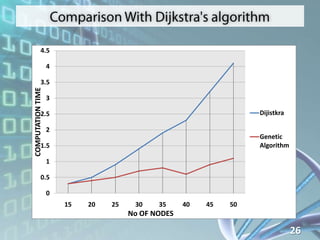
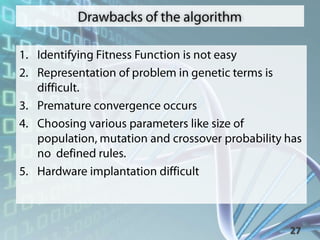
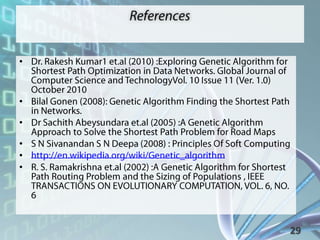
Le document semble contenir une série de données et de chiffres, probablement liés à des algorithmes et à des temps de calcul. Il mentionne des concepts comme l'algorithme de Dijkstra et des algorithmes génétiques, suggérant une analyse informatique. Cependant, la structure est fragmentée, rendant difficile une compréhension complète des thèmes abordés.