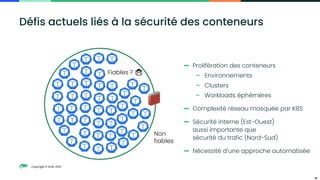
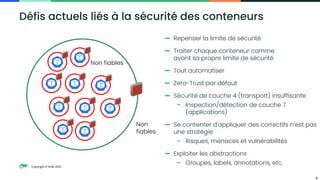
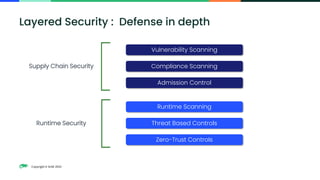
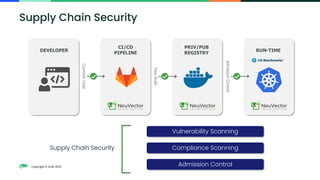
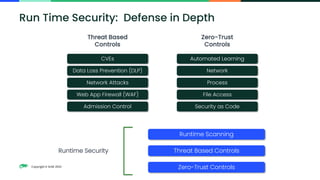
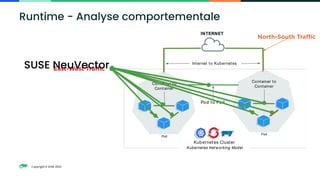
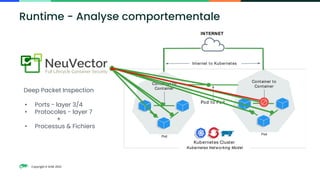
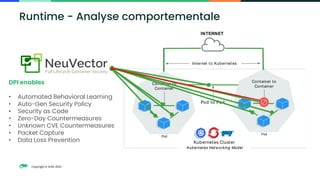
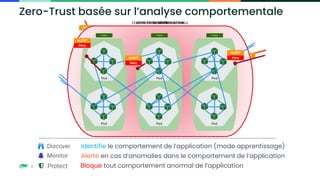
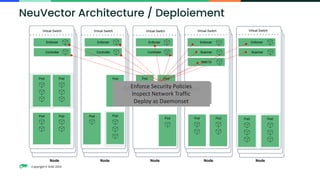
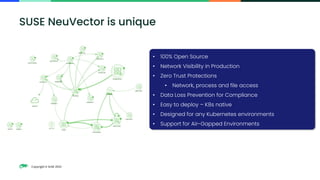
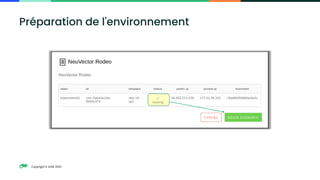
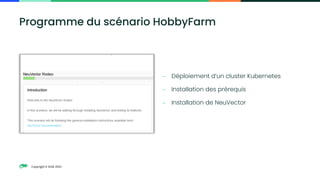
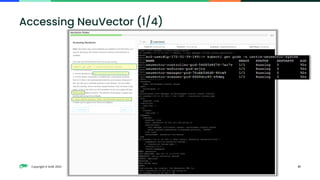
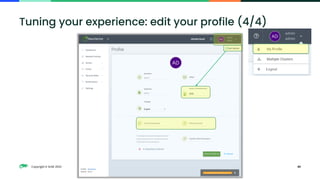
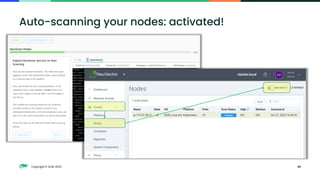
Le document présente les défis liés à la sécurité des conteneurs et les fonctionnalités de la solution NeuVector, stipulant qu'une approche de type 'zero-trust' est essentielle. Il décrit les méthodes de détection d'intrusion, la sécurité de la chaîne d'approvisionnement et les contrôles basés sur les menaces pour renforcer la sécurité. Enfin, il fournit des instructions sur le déploiement et l'utilisation de NeuVector dans des environnements Kubernetes.