Le document est un assemblage complexe de symboles et de caractères, indiquant un contenu potentiellement chiffré ou obfusqué. Il ne fournit pas d'informations claires ou interprétables sur un sujet spécifique. Aucune thématique ou idée principale n'est identifiable.




























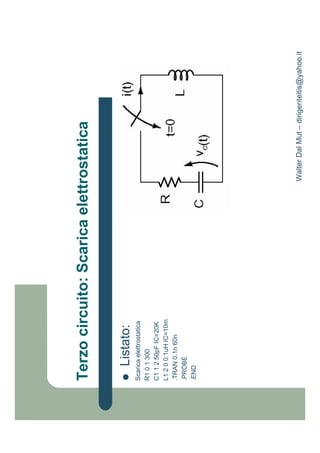



















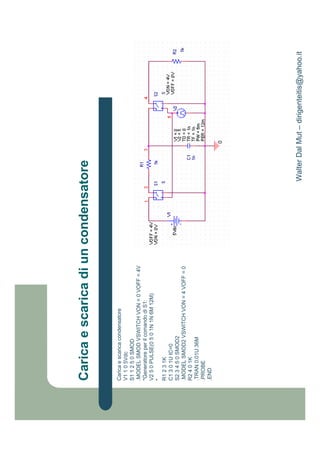











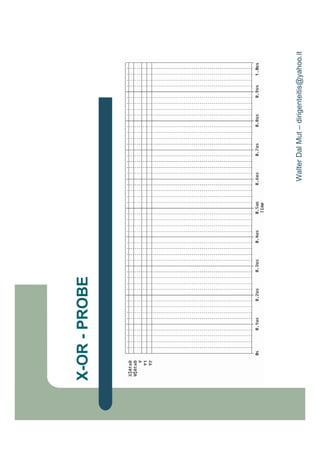
![&
@ 5
** ;
@DK * M
" ;
@D
@ D ;] ] + 5](https://image.slidesharecdn.com/pspicev91-110501090424-phpapp02/85/Pspice-v-9_1-71-320.jpg)

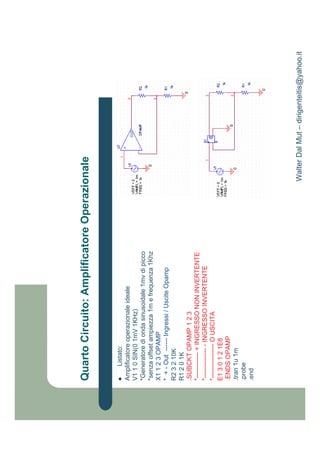
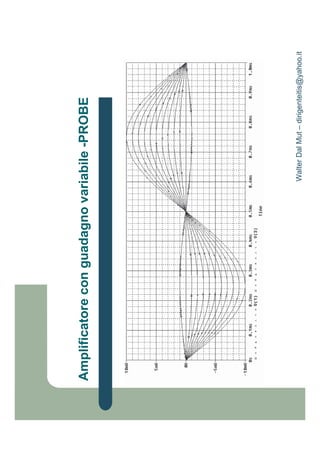
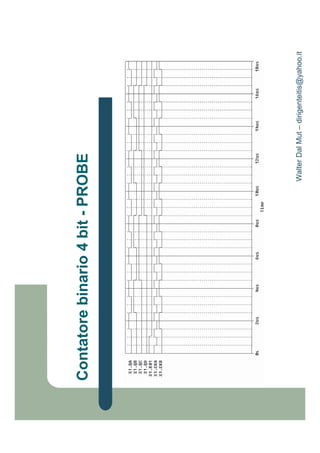
![0 7!
I * + O)&
4& & : I! & % : & &-#
H& & 0 &-
H0 0 , &:-
H, ) : '::
N& ) 0 2 . , 8IO)&
4 2 : &24
4 . : &24
@ D ;] ] > 1]! ]@ 5 ] ] + 5
I! "! &:: & & "/
1HI% &8 &
H9D"
"%](https://image.slidesharecdn.com/pspicev91-110501090424-phpapp02/85/Pspice-v-9_1-73-320.jpg)








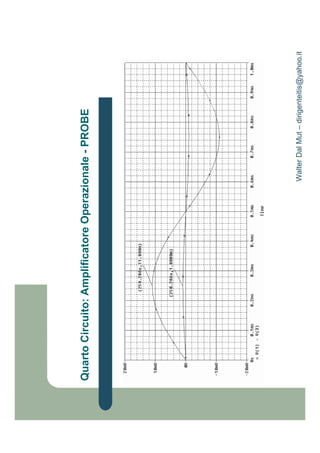
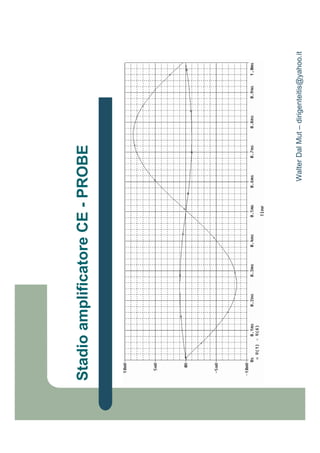
![8)+*
3 ;
EL NF N
"N 9H
N& , E& O):(
N0 0 ) E0 O):(
N, E& E0 E O),0
N) 0 O):)
N2 N , O):)
+& : 24
+0 N : 2+
@ D ;] ] > 1]! ]@ 5 ] ] + 5
1HI% &% &8
H9D"
"%](https://image.slidesharecdn.com/pspicev91-110501090424-phpapp02/85/Pspice-v-9_1-82-320.jpg)
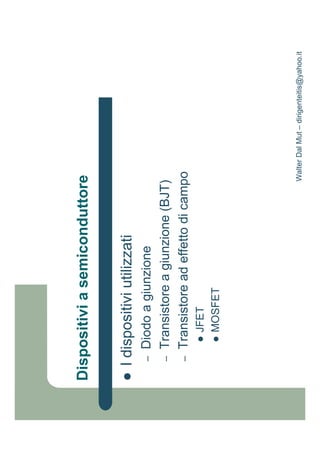
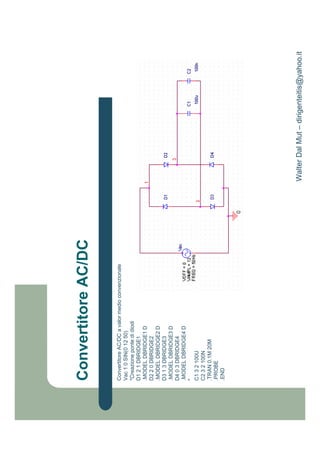
![!
! 5
T 8D!-1 O)',I !-I> !-D> H:&> H:0>
TF6I>9 6D>9 6!>9 6 >9
N& 0 6& , , 6& 60 6, 6) O)',I
T1 5
4 ,: @ : 2 &8 2 & &8 :#
T! S
4 S 0 : 8@ " : 2 : &% &% : 28 &8#
@ D ;] ] > 1]! ]@ 5 ] + 5
1HI% : &8 &(8
H9D"
"%](https://image.slidesharecdn.com/pspicev91-110501090424-phpapp02/85/Pspice-v-9_1-84-320.jpg)
![9
/ ! + RI#
N& 0 6& , , 6& 60 6, 6) O)',I
T1 5
4 ,: @ : 2 &8 2 & &8 :#
T! S
4 S 0 : 8@ " : 2 : &% &% : 2 & #
T! +
H& 6& ) &.-
H0 60 ) (-
H, 6, ) )-
H) 6) ) 0-
N0 : ) . O 2 8IO)&
H2 ) 2 &-
4F . : &24
4 O : &24
@D
;] ] > 1]! ]@ 5 ]
] + 5
1HI% : & &(
H9D"
"%](https://image.slidesharecdn.com/pspicev91-110501090424-phpapp02/85/Pspice-v-9_1-86-320.jpg)
