Byzantine General Problem - Siddharth Chaudhry
•
0 j'aime•2,149 vues
Byzantine General Problem Reliable computer system must be able to deal with failure of one or more of its components. Whenever a failed component exhibits a type of behavior it is generally referred as Byzantine General Problem. This type of behavior is often overlooked and involves mainly sending conflicting information to different parts of system.
Signaler
Partager
Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
Analysis of mutual exclusion algorithms with the significance and need of election algorithm to solve the coordinator problem for distributed systemAnalysis of mutual exclusion algorithms with the significance and need of ele...

Analysis of mutual exclusion algorithms with the significance and need of ele...Govt. P.G. College Dharamshala
Contenu connexe
Similaire à Byzantine General Problem - Siddharth Chaudhry
Analysis of mutual exclusion algorithms with the significance and need of election algorithm to solve the coordinator problem for distributed systemAnalysis of mutual exclusion algorithms with the significance and need of ele...

Analysis of mutual exclusion algorithms with the significance and need of ele...Govt. P.G. College Dharamshala
Similaire à Byzantine General Problem - Siddharth Chaudhry (20)
Adaptive Circumstance Knowledgeable Trusted System for Security Enhancement i...

Adaptive Circumstance Knowledgeable Trusted System for Security Enhancement i...
Application of genetic algorithm in intrusion detection system

Application of genetic algorithm in intrusion detection system
PRIVACY ENHANCEMENT OF NODE IN OPPORTUNISTIC NETWORK BY USING VIRTUAL-ID

PRIVACY ENHANCEMENT OF NODE IN OPPORTUNISTIC NETWORK BY USING VIRTUAL-ID
Privacy Enhancement of Node in Opportunistic Network by Using Virtual-Id 

Privacy Enhancement of Node in Opportunistic Network by Using Virtual-Id
Analysis of mutual exclusion algorithms with the significance and need of ele...

Analysis of mutual exclusion algorithms with the significance and need of ele...
Dernier
APM Welcome
Tuesday 30 April 2024
APM North West Network Conference, Synergies Across Sectors
Presented by:
Professor Adam Boddison OBE, Chief Executive Officer, APM
Conference overview:
https://www.apm.org.uk/community/apm-north-west-branch-conference/
Content description:
APM welcome from CEO
The main conference objective was to promote the Project Management profession with interaction between project practitioners, APM Corporate members, current project management students, academia and all who have an interest in projects.APM Welcome, APM North West Network Conference, Synergies Across Sectors

APM Welcome, APM North West Network Conference, Synergies Across SectorsAssociation for Project Management
God is a creative God Gen 1:1. All that He created was “good”, could also be translated “beautiful”. God created man in His own image Gen 1:27. Maths helps us discover the beauty that God has created in His world and, in turn, create beautiful designs to serve and enrich the lives of others.
Explore beautiful and ugly buildings. Mathematics helps us create beautiful d...

Explore beautiful and ugly buildings. Mathematics helps us create beautiful d...christianmathematics
Dernier (20)
9548086042 for call girls in Indira Nagar with room service

9548086042 for call girls in Indira Nagar with room service
BAG TECHNIQUE Bag technique-a tool making use of public health bag through wh...

BAG TECHNIQUE Bag technique-a tool making use of public health bag through wh...
Measures of Central Tendency: Mean, Median and Mode

Measures of Central Tendency: Mean, Median and Mode
Call Girls in Dwarka Mor Delhi Contact Us 9654467111

Call Girls in Dwarka Mor Delhi Contact Us 9654467111
APM Welcome, APM North West Network Conference, Synergies Across Sectors

APM Welcome, APM North West Network Conference, Synergies Across Sectors
Explore beautiful and ugly buildings. Mathematics helps us create beautiful d...

Explore beautiful and ugly buildings. Mathematics helps us create beautiful d...
Disha NEET Physics Guide for classes 11 and 12.pdf

Disha NEET Physics Guide for classes 11 and 12.pdf
Beyond the EU: DORA and NIS 2 Directive's Global Impact

Beyond the EU: DORA and NIS 2 Directive's Global Impact
Byzantine General Problem - Siddharth Chaudhry
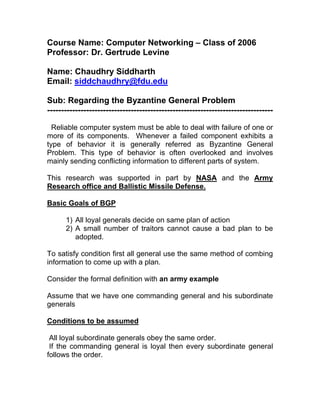
- 1. Course Name: Computer Networking – Class of 2006 Professor: Dr. Gertrude Levine Name: Chaudhry Siddharth Email: siddchaudhry@fdu.edu Sub: Regarding the Byzantine General Problem --------------------------------------------------------------------------------- Reliable computer system must be able to deal with failure of one or more of its components. Whenever a failed component exhibits a type of behavior it is generally referred as Byzantine General Problem. This type of behavior is often overlooked and involves mainly sending conflicting information to different parts of system. This research was supported in part by NASA and the Army Research office and Ballistic Missile Defense. Basic Goals of BGP 1) All loyal generals decide on same plan of action 2) A small number of traitors cannot cause a bad plan to be adopted. To satisfy condition first all general use the same method of combing information to come up with a plan. Consider the formal definition with an army example Assume that we have one commanding general and his subordinate generals Conditions to be assumed All loyal subordinate generals obey the same order. If the commanding general is loyal then every subordinate general follows the order.
- 2. Problem 1) Oral message can be easily changed. 2) No Solution works unless more than 2/3rd of general are loyal 3) Even with 3 generals one traitor makes the protocol fail. Understanding the Problem through Figures.
- 3. Solution for Oral Messages
- 4. We have assume the following conditions for Oral Messaging: 1) Every message which is sent is delivered correctly. We assume that traitor is not capable to interfere communication between two generals 2) Receiver has knowledge of who have sent the message. Traitors are not capable to confuse the message by sending extra message 3) Absence can be detected Default message is “Retreat” The ALGORITHM for Oral message is as follows:
- 5. What if we are not fully connected? What are Practical Implications of this algorithm?
- 6. The Conclusion is as Follows Reference: “http://homes.cerias.purdue.edu/~crisn/courses/cs590T/cs590T_lect4 _byzantine_generals.pdf”
