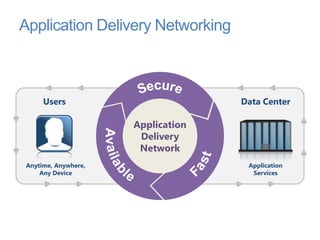
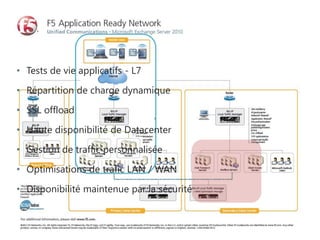
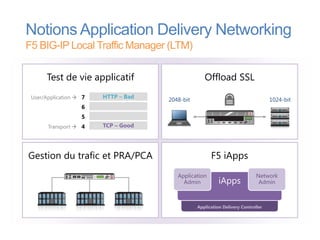
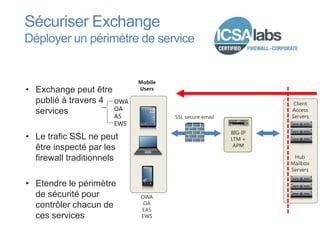
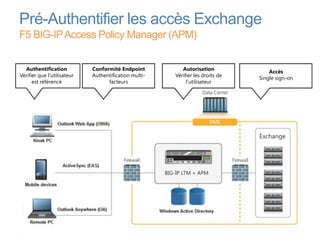
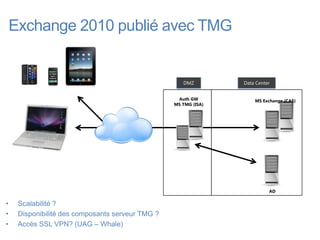
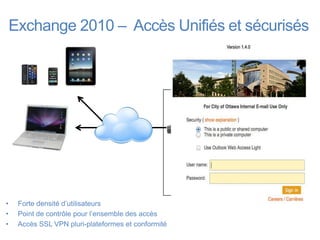
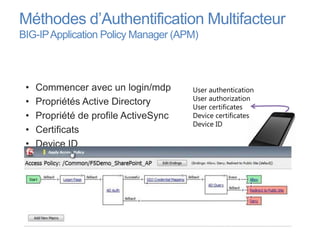
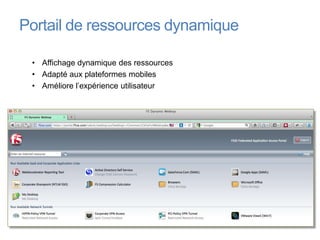
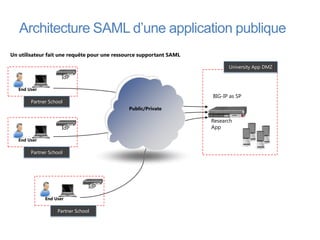
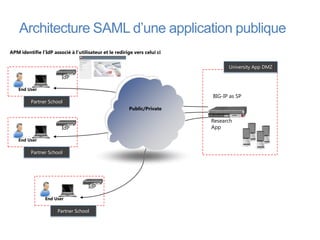
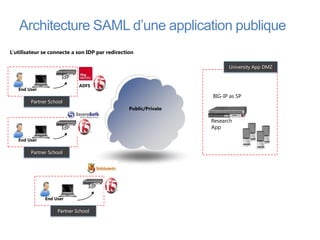
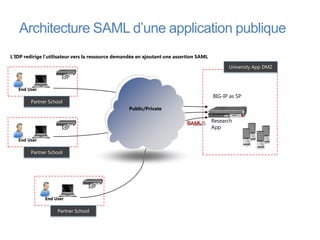
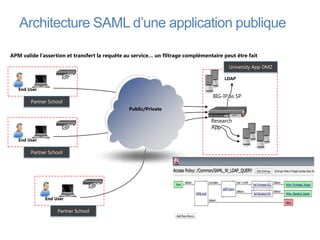
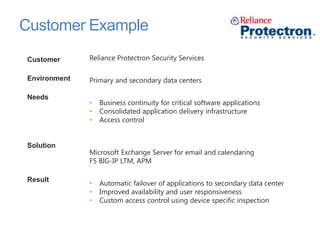
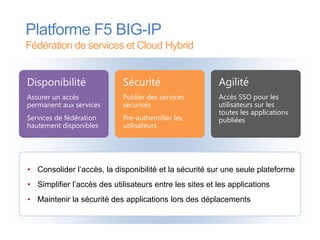
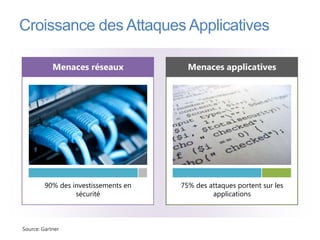
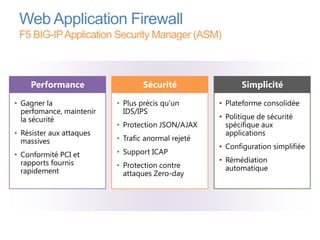
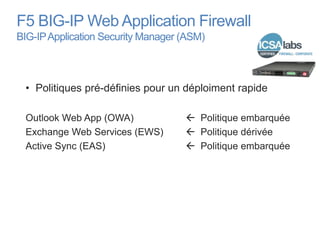
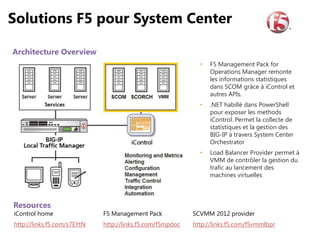
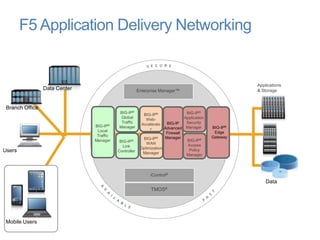
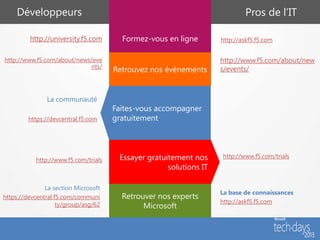
Le document présente les solutions de F5 pour faciliter le déploiement des applications Microsoft et améliorer la mobilité, en mettant l'accent sur la sécurité et la disponibilité. F5 propose des produits comme le BIG-IP pour optimiser la livraison d'applications, gérer le trafic et assurer une authentification sécurisée pour des services tels que Microsoft Exchange. Il aborde également des statistiques clés sur l'importance croissante du cloud computing et des applications mobiles dans l'infrastructure des entreprises d'ici 2020.