Bss - oss - Ericsson
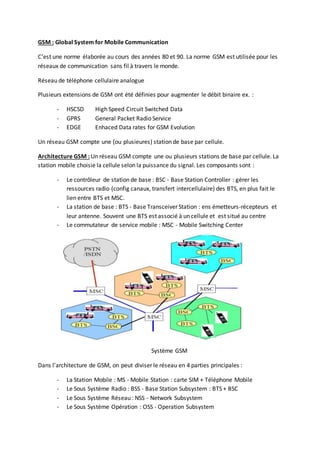
- 1. GSM : Global System for Mobile Communication C’est une norme élaborée au cours des années 80 et 90. La norme GSM est utilisée pour les réseaux de communication sans fil à travers le monde. Réseau de téléphone cellulaire analogue Plusieurs extensions de GSM ont été définies pour augmenter le débit binaire ex. : - HSCSD High Speed Circuit Switched Data - GPRS General Packet Radio Service - EDGE Enhaced Data rates for GSM Evolution Un réseau GSM compte une (ou plusieures) station de base par cellule. Architecture GSM : Un réseau GSM compte une ou plusieurs stations de base par cellule. La station mobile choisie la cellule selon la puissance du signal. Les composants sont : - Le contrôleur de station de base : BSC - Base Station Controller : gérer les ressources radio (config canaux, transfert intercellulaire) des BTS, en plus fait le lien entre BTS et MSC. - La station de base : BTS - Base Transceiver Station : ens émetteurs-récepteurs et leur antenne. Souvent une BTS est associé à un cellule et est situé au centre - Le commutateur de service mobile : MSC - Mobile Switching Center Système GSM Dans l’architecture de GSM, on peut diviser le réseau en 4 parties principales : - La Station Mobile : MS - Mobile Station : carte SIM + Téléphone Mobile - Le Sous Système Radio : BSS - Base Station Subsystem : BTS + BSC - Le Sous Système Réseau : NSS - Network Subsystem - Le Sous Système Opération : OSS - Operation Subsystem
- 2. Architecture GSM BSS : (BusinessSupportSystems)- Système de SupportFonctionnel("Métier"). Le terme Business Support System ou BSS est un terme généraliste récent qui fait référence aux solutions métier, qui traitent avec les clients, le maintien des processus tels que la prise de commandes, le traitement des factures, et la collecte des paiements. Les deux systèmes sont souvent abrégés ensemble BSS/OSS ou simplement B/OSS. Progiciels qui les activités orientées client : Facturation, Gestion de commandes, Gestion de la relation client CRM, Automatisation de centre d’appel sont toutes des applications BSS BSS peut également englober la facette des applications OSS orientées client comme la gestion des incidents et le service d’assurance La relation basic entre OSS et BSS ou OSS a passé des commandes de services et fourniture des information de service assurance à la couche BSS Historiquement, le terme OSS a été utilisé pour inclure à la fois des réseaux et des systèmes d'entreprise. Il est encore parfois utilisé dans ce sens, ce qui peut provoquer une certaine confusion. Lorsqu'il est utilisé de cette façon, le terme OSS peut être considérée comme comprenant le domaine BSS.
- 3. OSS pourrait être traduit en français par Système de Support Opérationnel pour le différencier de BSS (Business Support Systems), Système de Support Fonctionnel ("Métier"). Le Support Opérationnel et le Support Fonctionnel faisant actuellement consensus pour désigner les fonctions des employés qui s'occupent de ces systèmes (cf. requêtes Google). OSS : OperationsSupportSystem - OperationalSupportSystem Un OSS est l'ensemble des composants opérationnels ou les systèmes informatiques utilisés par un opérateur de télécommunications. Elle est synonyme de maintenance opérationnelle dans le domaine des télécommunications. Le terme OSS est habituellement synonyme de systèmes de réseaux informatiques qui comprend : le réseau de télécommunications lui-même et le maintien des processus tels que la maintenance du réseau. Le maintien des processus, avec ou sans automatisation, est assuré par des composants logiciels back-office qui travaillent en interaction les uns avec les autres et qui sont utilisés dans différents services : provisioning le recensement la performance et Qualité de service la gestion de la sécurité l'inventaire l'installation et la configuration des composants réseau la gestion des erreurs réseaux.
- 4. Composants télécoms essentiels OSS/BSS : CDR : Call Detail Record (callingnumber,callednumber,time duration,Date &time,…) 1. CRM : Gestiondescontacts Gestiondescommandes Centre d’appel Fidélité/Rétention 2. Provisionning/Service Fulfillment :systèmespourfournirduservice auclient Service d’activation NetworkInventory Workforce management (Gestionressource humaine)
- 5. 3. Retail BillingSystem ( système de facturationde detail ) Rating: Rate each EDR withcorrespondingrate Billing:Calcultate the fixedcharges… Bill Production :Produce andprintde invoice Collection&Payment:can be part of BillingSystemoradedicatedsystem 4. Data Collection Exchange : ex.Ericsson:AXE,AXD. Huawei:UNO,CDMA BilligFilesTypes: AMA- AutomaticMessage Accounting(EDRs…),METER. Front Collector(FC) Function: donnéesde sondage,stockage,… Central AccessNetwokServer(CANS) : 5. Mediation Ensemble de functionde traitementsqui sontappliquésauEDRs Fournirlesdonnéesauendsystem(Billing,assurance revenue,warehouse,…) Fonctionde mediation:Collection&archive,parsing,appliquerBRs (Normalisation, filtration,duplicate,…) Auditing&Reporting :Reporting,Errorprocessing 6. SS7 Monitoring SS7 Protocol : switches SS7 Monitoringsolutions:Monitorthe signal entre switchesetgénérerrapportEDR 7. Revenue Assurance :Detectionetcorrectiondesécartsenlessystèmesdesopérateurs Testcall generator Faud Management 8. InterconnectBillingSystems Types Of BillingSystems 1. Offline –Postpaif: Network Mediator 2. Online –Prepaid: 3. Interconnect: Facture desconnexionentre opérateurs Rating,Dicounting,Billing,Reorting 4. Convergentsystems:
- 6. Fluxtypique de système de facturation (Typical flowof billing system) : Commande clientetelleestactivée dansle réseau Clienteffectue sonappel etl’utilisationestreçue,mediatedetcalculé Clientfacturé etfacture dispatché Payement Gestionde recouvrementde ladette M2M : Machine to Machine Permetaudispositif utilisantGSMde s’entre envoyé de messageetexécuterlestaches demandéesdanscesmessages.Etpermetaussi aux humainsd’utiliseràdistance leurssmartphone OSS and BSS relationship: La relation basic entre OSS et BSS ou OSS a passé des commandes de services et fourniture des informations de service assurance à la couche BSS est souvent appelée : « Orders Down, Faults Up » Si on a destachesback office,ondoitavoiraussi destachesfrontoffice,eneffetyona. En plusde précision,ellessontappeléesBSS.Ce sontunensembledistinctd’applicationsqui supporte les activitéscommerciales,recettesetactivitésorienté client. BSS Ericsson : BusinessSupportSystemsofferingsenable effective andcustomercentricbusinessoperations, allowingfornewbusinessmodelsandinnovativeserviceofferings.
- 7. Our CSIportfolioisspearheadedbythe BSSTransformationthatisstreamliningtechnology, processesandorganizationtoconsolidate andevolve BSS,inordertoachieve superiorcustomer experience,businessefficiencyandoptimization. Our offeringsinclude Revenue Management,M-Commerce,CustomerRelationshipManagementas well asBig Data Analytics/BusinessIntelligence solutiondomains,encompassingEricssonBSS productsand Partnerecosystem. 1. BSS transformation BSS transformationconsidersthe e2e systemintegrationandsolutionperspective of aBusiness transformationtoensure customers needsare addressedthroughpropertargetsolutionand transitionroadmap. SI BSS Transformationdeliverablesare: - Requirementtraceabilitymatrix withfitgapanalysis - Target e2e integrationarchitecture - BSS Transitionarchitecture - Informationarchitecture - TransformationroadmapandRelease strategy - BusinessTransitionandMigrationstrategy. 2. Business intelligence andDataAnalytics Data AnalyticsandBusinessIntelligence capabilitiesare keyenablersforthe Enterprise-wide Optimization,GrowthandInnovationinitiatives,suchasCustomerExperience andValue,Data MonetizationandEnterpr.Performance. We engage througha consultative,use case drivenapproach,helpingoperatortorapidlyrealize value ineachstepof the way,whentransforming intoafuture data andanalyticsdrivencompany. Our offeringarchitectureisgearedtowardsdata-drivenvaluecreation,andbasedonthree main horizontal layers: - Data / InformationFoundationlayer - Insightlayer(Analytics/Visualization) - Value Realizationlayer(Applications)Our"datatovalue"value propositionispackagedintothree offeringareas: - Enterprise DWHand BI - BigData AnalyticsandReal-time BI - AdvancedAnalyticsandOpt.Appl. 3. Customer RelationshipManagement EricssonCustomerRelationshipManagementsolutionsenableoperatorstoperformthe daytoday interactionandsupportwiththe customers,whileatthe same time keepinga360 degree view of the client,inorderto customize thatinteractiontothe clientvalue, preferencesandpotential.
- 8. While arelativelynew areaforEricsson,CRMis a keycomponentincomprehensive Customer Experience improvementinitiative,aswell asrequiredcomponenttoprovide afull BSSstackfor operatorsthat relyonEricssonrevenue managementsystems. 4. Revenue Management Revenue Managementsolutionsallowsservice providers,inreal-time, tohandle all customersand services inastreamlined,convergentprocess,coveringpre-paidandpost-paid,voice anddata, fixedandmobile, retail andwholesale. Thisofferingcontainssupportforsuccessful sales,solutioninganddeliveryof revenue management solutions. Ericsson Convergent Billing and Charging: Convergentbillingandchargingsolutionsallowsservice providerstohandle all customersand servicesinastreamlined,convergentprocess,coveringpre-paidandpost-paid,voice anddata,fixed and mobile,retailandwholesale. Thisofferingcontainssupportforsuccessful sales,solutioninganddeliveryof convergentbillingand chargingcustomersolutions. Convergentcharging&billing=CBIO= binlling+charging= postpaid+ prepaid Ericsson Billing: Billingsolutionsgivesservice providersthe convenienceof convergentbillingandcustomercare for all services,anda choice of service packagestosuittheircustomerslifestyle orbusinessneeds. Thisofferingcontainssupportforsuccessful sales,solutioninganddeliveryof billingcustomer solutions. Billing=Postpaid= BSC Alex: BSCS iX4.x forCBiO 3.x ICP 14-04 User Documentaion Chargingand BillinginOne (CBiO) 3.0.1 Ericsson Charging: Chargingsystem=Prepaid Chargingsolutionssupportsservice providerstomonetize mobiledataandincrease revenue while givinguserspersonalizedservice offerings,promotionsandindividual bonusrewardsinbothpre-paid and convergentscenarios.
- 9. Thisofferingcontainssupportforsuccessful sales,solutioninganddeliveryof chargingcustomer solutions. - Allowsthe operatorstode-coupletechnologyfrombusinessmodel (gestionde l’entprse),such online creditcontrol forbothpre- andpost-paidbusinessmodels - Providessuperiorcustomerexperiences, matching the customerlifestyles Flexible Fields:capabilitytoprovisioninFlexible filedsforend-userex.Get100 SMS in birth Attributes Use Case Rate Personal Rate String Compaignfollow up,personalization Setof Dates Birthdayoffer,Marriage offer Setof string Special Numbers Setof integer External Identities,tailoredpolicy - Gain configurability - E2E (Endto End) Businessefficiency - Deliverconvergentreal-timecharging o Optimiserbandwidth –control (bande passante ) forqualityof service o Offerswithlimitedaccessex.1hinternetaccess o - Reduce total cost of ownership - E2E solution Ericsson Rule Engine: Usedto - define the configurablelogicof the chargingsystem - Define productandcampaignsandto implementcharging,Rating,PolicyandRefills. Horizontal scalability: - Grow systembasedonneeds,addingadditional computingcapacity whenneeded CS fitswell (s’intègrebien) intootherBSScomponentsex.EricssonCatalogueManager,Telecom CRM, EricssonOrder Manager,EricssonMulti activation, EricssonMulti mediation, Ericsson MSDP Charging systemcomponents: 1. Core Compenents Upstreamintegration: CS exposesit’sinformationanddatamodel throughOpenAPIsfor north-boundsystemslike CRMandproduct cataloguessystemstointegrate withcbio UserCommunication:End usercommunicationisdone fromCSwhenitis relevantfor the customer CS offerspublicAPIcanintegratedforondemandinfos,Voice IVRforautomatedteller Keepuserinformedinreal time abouthisaccountstatus,bonusesandoffers Rule Management: CentralizedRule configurationandmanagementtool Rate-plans,refill-plans
- 10. Rating & Balance Management: Holdsthe Subscriberaccountandsubscription information PerformRating,charging,balance managementandlifecycle management PolicyManagement: MBC! Charging & SessionControl: CS provide arich setof Oline ChargingansSessionControl interfaces spanningfromSS7 carnel protocol 2. Optional Compenents VoucherManagement Module:Secure handlingof vouchers Big Data Storage Module:stockage etutilizationdatacustomerspour suivi fianancier SubscriberManagementModule: usedbyCustomerCare Ericsson Mediation: Mediationsolutionsgive service providersone convergentmediationsolutionforall businessneeds. Thisofferingcontainssupportforsuccessful sales, solutioninganddeliveryof mediationcustomer solutions. ETL charging Billing Alex: EricssonMulti Mediation7 - File andeventmediation EricssonMulti Mediation7 - Online mediation EricssonMulti Mediation