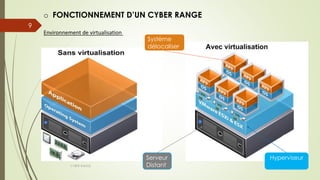
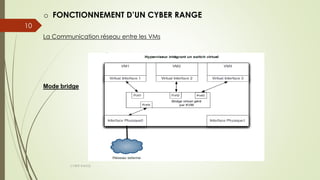
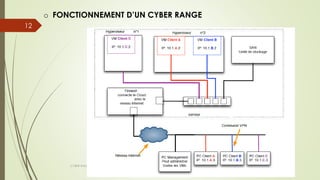
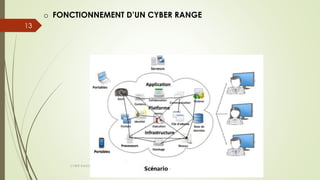
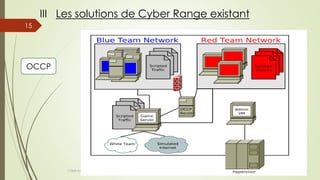
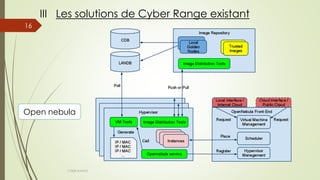
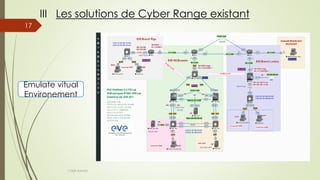
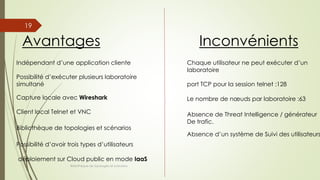
Le document présente une analyse des cyber ranges, détaillant leur fonctionnement, les technologies sous-jacentes, et les solutions disponibles sur le marché. Il décrit les conditions d'entraînement réalistes qu'ils offrent et les divers scénarios de simulation. En outre, il aborde les avantages et inconvénients de leur utilisation en environnement de virtualisation.