Mastère Professionnelle 2015
•
1 j'aime•575 vues
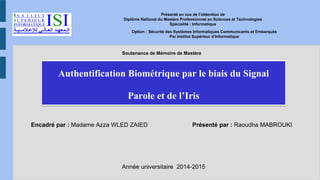
Authentification Biométrique par le biais du Signal Parole et de l’Iris Présenté par : Raoudha MABROUKI
Signaler
Partager
Signaler
Partager
Télécharger pour lire hors ligne
Recommandé
multimedia technologies Introduction

Multimedia Technologies Introduction Subject
Multimedia Technology introduction - I created these slides for my students to teach CMP 383 Multimedia Technology at Jazan Community College , Jazan University
Chapter 11 - Emerging Multimedia Technologies

This is the subject slides for the module MMS2401 - Multimedia System and Communication taught in Shepherd College of Media Technology, Affiliated with Purbanchal University.
Lecture6 audio

The document discusses digital audio and its uses in multimedia. It describes sound as pressure waves and how digital audio is captured through sampling. Sampling converts analog sound waves into discrete digital values through an analog-to-digital converter. The document also discusses common audio file formats like WAV and MIDI, which transmits instructions for musical notes rather than raw audio.
Digital Audio in Multimedia

This document discusses digital audio and summarizes key points:
1. Digital audio involves converting sound waves to numerical data that can be easily stored, manipulated and reproduced. It allows for two types of sounds - analog and digital.
2. Characteristics of digital audio include sampling rate, amplitude, channels. Common sampling rates are 11.025KHz, 22.5KHz and 44.1KHz. File size is calculated based on these characteristics.
3. Popular audio file formats include WAV, AIFF, MP3, AAC which allow for compression. MIDI stores musical data separately from audio and allows for editing of notes.
[V14] Odoo functional training Pinakin Nayi![[V14] Odoo functional training Pinakin Nayi](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[V14] Odoo functional training Pinakin Nayi](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
This document provides an overview and agenda for an Odoo 14 functional training. The training will cover key Odoo modules like CRM, sales management, and inventory. For CRM, it will discuss concepts like pipelines, sales teams, leads, and activities. For sales, it will cover order management, pricing, discounts, and reporting. For inventory, it will include adjustments, replenishment, traceability, shipping, and advanced concepts like routing and costing methods. The goal is to help understand Odoo functionality and enhance productivity. The trainer is available for any Odoo help via Skype or email.
Introduction to Dynamic Analysis of Android Application

This document introduces dynamic analysis of Android applications using DroidBox. It describes what dynamic analysis is, why it is used, and how to perform it. It then provides details on DroidBox, including what it is, how it works, how to use it, and ideas for improving it. DroidBox performs dynamic taint analysis and hooking at the application framework level to monitor app actions like information leaks, network/file I/O, and cryptography operations. The document includes code snippets showing how DroidBox was ported to Android 2.3.
Digital locker

Digital Locker is an Indian government service that provides citizens with 1GB of secure online storage linked to their Aadhaar number to store important documents digitally. It aims to minimize physical documents, ensure authenticity of documents, and make services more accessible anytime from anywhere. Key features include linking to Aadhaar, 10MB free storage, uploading documents in XML format, and secure access. Advantages are reducing fraud, corruption-free services, and anytime access, while the main disadvantage is requiring an Aadhaar card for access.
Hardware & software in multimedia

The document discusses hardware and software used in multimedia systems. It defines hardware as the physical components of a computer like the CPU, monitor, and video grabbing card. Software is defined as written instructions that control hardware like operating systems, applications, and programs. The latest hardware includes powerful computers with Intel Core i7 processors and Nvidia graphics cards, high-resolution monitors, and Nikon cameras. Popular multimedia software mentioned are Adobe Creative Cloud applications, Microsoft PowerPoint, BlueStacks for playing mobile games on PC, VirtualDJ for DJ mixing, and AVS Video Editor.
Recommandé
multimedia technologies Introduction

Multimedia Technologies Introduction Subject
Multimedia Technology introduction - I created these slides for my students to teach CMP 383 Multimedia Technology at Jazan Community College , Jazan University
Chapter 11 - Emerging Multimedia Technologies

This is the subject slides for the module MMS2401 - Multimedia System and Communication taught in Shepherd College of Media Technology, Affiliated with Purbanchal University.
Lecture6 audio

The document discusses digital audio and its uses in multimedia. It describes sound as pressure waves and how digital audio is captured through sampling. Sampling converts analog sound waves into discrete digital values through an analog-to-digital converter. The document also discusses common audio file formats like WAV and MIDI, which transmits instructions for musical notes rather than raw audio.
Digital Audio in Multimedia

This document discusses digital audio and summarizes key points:
1. Digital audio involves converting sound waves to numerical data that can be easily stored, manipulated and reproduced. It allows for two types of sounds - analog and digital.
2. Characteristics of digital audio include sampling rate, amplitude, channels. Common sampling rates are 11.025KHz, 22.5KHz and 44.1KHz. File size is calculated based on these characteristics.
3. Popular audio file formats include WAV, AIFF, MP3, AAC which allow for compression. MIDI stores musical data separately from audio and allows for editing of notes.
[V14] Odoo functional training Pinakin Nayi![[V14] Odoo functional training Pinakin Nayi](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
![[V14] Odoo functional training Pinakin Nayi](data:image/gif;base64,R0lGODlhAQABAIAAAAAAAP///yH5BAEAAAAALAAAAAABAAEAAAIBRAA7)
This document provides an overview and agenda for an Odoo 14 functional training. The training will cover key Odoo modules like CRM, sales management, and inventory. For CRM, it will discuss concepts like pipelines, sales teams, leads, and activities. For sales, it will cover order management, pricing, discounts, and reporting. For inventory, it will include adjustments, replenishment, traceability, shipping, and advanced concepts like routing and costing methods. The goal is to help understand Odoo functionality and enhance productivity. The trainer is available for any Odoo help via Skype or email.
Introduction to Dynamic Analysis of Android Application

This document introduces dynamic analysis of Android applications using DroidBox. It describes what dynamic analysis is, why it is used, and how to perform it. It then provides details on DroidBox, including what it is, how it works, how to use it, and ideas for improving it. DroidBox performs dynamic taint analysis and hooking at the application framework level to monitor app actions like information leaks, network/file I/O, and cryptography operations. The document includes code snippets showing how DroidBox was ported to Android 2.3.
Digital locker

Digital Locker is an Indian government service that provides citizens with 1GB of secure online storage linked to their Aadhaar number to store important documents digitally. It aims to minimize physical documents, ensure authenticity of documents, and make services more accessible anytime from anywhere. Key features include linking to Aadhaar, 10MB free storage, uploading documents in XML format, and secure access. Advantages are reducing fraud, corruption-free services, and anytime access, while the main disadvantage is requiring an Aadhaar card for access.
Hardware & software in multimedia

The document discusses hardware and software used in multimedia systems. It defines hardware as the physical components of a computer like the CPU, monitor, and video grabbing card. Software is defined as written instructions that control hardware like operating systems, applications, and programs. The latest hardware includes powerful computers with Intel Core i7 processors and Nvidia graphics cards, high-resolution monitors, and Nikon cameras. Popular multimedia software mentioned are Adobe Creative Cloud applications, Microsoft PowerPoint, BlueStacks for playing mobile games on PC, VirtualDJ for DJ mixing, and AVS Video Editor.
Hardware & Input/Output (I/O) Devices

Hardware devices that are used to input and output data to a computer are called I/O devices. Input devices capture information from the external environment and convert it into a format that can be processed by the computer. Examples include keyboards, mice, scanners, microphones, and webcams. Output devices take the processed data from the computer and present it to the user. Common output devices are monitors, printers, speakers and plotters. Monitors display soft copy output while printers provide hard copy printouts.
Digitalization: A Challenge and An Opportunity for Banks

Today’s banking industry era is strongly defined by a word - digital. The urgency to act is only getting severe each day. Banks using digital technologies to automate processes, improve regulatory compliance, and transform the customer experience may realize a profit upside of 40% or more, while laggards that resist digital innovation will be punished by customers, financial markets, regulators, and may see up to 35% of net profit eroded, according to a McKinsey analysis.
The vital question to answer is, do we get digitalization right? Why is it getting extremely urgent to digitize?
Personal Data Protection

Data security involves keeping information private by using methods to ensure confidentiality, integrity, and availability of data. It is important for businesses that hold confidential information. Data is backed up and stored hierarchically for safety. Software uses measures like intrusion detection systems, user IDs, passwords, biometrics, encryption, and digital signatures and certificates to protect data. Downloading pirated software poses legal and ethical issues and risks to users. Developers employ serial numbers, activation keys, copy protection, and hardware keys to protect their software and encourage users to register for updates and support.
Chapter 8 : MULTIMEDIA SKILLS

A multimedia project requires a team with diverse skills, known as the multimedia skillset. These teams consist of roles like project managers, designers, programmers, writers, and specialists in areas like video and audio. Each team member has specific responsibilities to ensure the project is successfully developed, such as project managers coordinating the team and designers creating visuals and interfaces.
Proposal for pos

This document provides a proposal from SRRK IT Limited for a point of sale (POS) system. It summarizes SRRK IT's capabilities in software and web development. The proposal describes features of the POS system like barcode scanning, credit card processing, and customizable interfaces. It highlights business benefits such as easier accounting and inventory management. The document outlines SRRK IT's software development process and provides examples of current clients. It emphasizes values like integrity, respect, justice, and responsibility. In closing, it provides contact information for SRRK IT.
Odoo vs sap

For your company's growth, choosing the correct ERP at the right moment becomes critical. The most appropriate ERP can have a direct impact on a company's success, profitability, and growth.
https://www.geminatecs.com/manufacturing-management-system
Multimedia System

A multimedia system is characterized by the digital integration of various media types like text, graphics, sound, images and video. It allows for interactivity and uses computer networks for distribution. Ensuring quality of service is important for multimedia over networks due to the time sensitivity and synchronization needs of media. Compression techniques like lossy and lossless are used to reduce multimedia file sizes.
Multimedia in Healthcare.pptx

This document discusses using multimedia technologies for healthcare applications. It proposes a system for remote markerless human gait tracking over wireless networks for medical diagnosis and prognosis. The system uses video content analysis techniques like background subtraction and contextual classification to extract the human gait region from video frames without needing specialized equipment. It then jointly optimizes video encoding and wireless transmission to prioritize sending the extracted human gait region while meeting quality of service requirements over bandwidth-limited wireless networks. Experimental results using H.264 video compression demonstrate the effectiveness of the proposed remote healthcare system for applications like telemedicine.
Multimedia color in image and video

Multimedia color in image and video seminar
Mustansiriya University
Department of Education
Computer Science
Bhim app

The document summarizes information about the BHIM app, which was launched in December 2016 by the National Payments Corporation of India to facilitate e-payments directly through banks and simplify cashless transactions. BHIM allows users to send and request money, scan and pay for purchases, and view transactions. It has over 16 million downloads and supports multiple Indian languages. The app provides a secure way to transact between bank accounts but has limitations like daily transaction limits and no dedicated customer support.
Network security ppt

network security is a complicated subject,historically only tackled by well-trained and expericenced experts
Multimedia

This document discusses graphics and multimedia technology. It covers various topics related to graphics including different types of images (raster/bitmap and vector), color, file formats, and methods for obtaining images. Specifically, it describes raster images as composed of pixels and matrices, while vector images use objects like lines and shapes. It also discusses color palettes, resolution, dithering, and scanning, digitizing, and capturing images using cameras, scanners, and software tools.
Multimedia:Multimedia compression 

This document discusses multimedia data compression. It explains that multimedia files like images, audio, and video take up significantly more storage space than text files. Data compression reduces the size of files by removing redundant data, saving storage space and allowing faster transfers. Compression is achieved through codecs, which are hardware or software that compresses and decompresses data. Compression can be lossless, allowing exact reconstruction of the original data, or lossy, which sacrifices some quality to achieve greater compression but does not allow exact reconstruction.
Multimedia Hardware

Presentation on hardware components of a typical Multimedia production system as per Industrial Technology Multimedia syllabus (NSW)
Multimedia Application Development

Multimedia refers to integrating various media types like text, graphics, audio, video digitally. Multimedia applications use a combination of media to deliver information interactively. Examples include websites, educational courseware, games. Multimedia development is the process of creating content combining different media types. It involves conceptualization, planning, production, and documentation phases. Various software are used to generate multimedia content for different applications in areas like advertising, education and entertainment.
Network security

1. Formulate a testing plan with the client to identify systems to evaluate and the scope of testing allowed.
2. Remotely or locally access the target systems to find vulnerabilities by simulating common attacks.
3. Report any found vulnerabilities to the client along with recommendations on how to remedy security issues.
rfid presentation

Here are the answers to your questions:
1. The main differences between RFID and barcodes are:
- RFID uses radio waves to transmit data while barcodes use optical scanning. RFID does not require line of sight.
- RFID tags can be read from a distance without physical contact while barcodes must be within the line of sight of a scanner.
- RFID tags can be read/written to multiple times while barcodes are read-only.
- RFID tags can store more information than barcodes.
2. Some practical applications of RFID include supply chain management, asset tracking, access control and authentication, livestock identification, toll collection on roads/bridges, library management systems, etc
Multimedia Development Lifecycle

Week 2 Lecturing
P420 - 1 CMLA
Multimedia Presentation for Public Relations
Swiss German University Indonesia
(13 September 2011)
Programming tools for developers

The document discusses various tools for programming in Python, HTML5, Java, and for rapid application development. For Python, it discusses IDEs like PyDev for Eclipse and PyCharm, as well as libraries and debugging tools part of the BeeWare toolbox. For HTML5, it discusses editors like Sublime Text, Atom, and Notepad++, and frameworks like Bootstrap and HTML5 Boilerplate. For Java, it discusses IDEs like NetBeans, Eclipse, and IntelliJ IDEA, as well as the rapid application development tool gvNIX.
Digital Locker Intro 

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive functioning. Exercise causes chemical changes in the brain that may help boost feelings of calmness, happiness and focus.
Conception et réalisation d’un système d’information pour l’automatisation du...

Conception et réalisation d’un système d’information pour l’automatisation du suivi des études d’audit géotechnique
Contenu connexe
Tendances
Hardware & Input/Output (I/O) Devices

Hardware devices that are used to input and output data to a computer are called I/O devices. Input devices capture information from the external environment and convert it into a format that can be processed by the computer. Examples include keyboards, mice, scanners, microphones, and webcams. Output devices take the processed data from the computer and present it to the user. Common output devices are monitors, printers, speakers and plotters. Monitors display soft copy output while printers provide hard copy printouts.
Digitalization: A Challenge and An Opportunity for Banks

Today’s banking industry era is strongly defined by a word - digital. The urgency to act is only getting severe each day. Banks using digital technologies to automate processes, improve regulatory compliance, and transform the customer experience may realize a profit upside of 40% or more, while laggards that resist digital innovation will be punished by customers, financial markets, regulators, and may see up to 35% of net profit eroded, according to a McKinsey analysis.
The vital question to answer is, do we get digitalization right? Why is it getting extremely urgent to digitize?
Personal Data Protection

Data security involves keeping information private by using methods to ensure confidentiality, integrity, and availability of data. It is important for businesses that hold confidential information. Data is backed up and stored hierarchically for safety. Software uses measures like intrusion detection systems, user IDs, passwords, biometrics, encryption, and digital signatures and certificates to protect data. Downloading pirated software poses legal and ethical issues and risks to users. Developers employ serial numbers, activation keys, copy protection, and hardware keys to protect their software and encourage users to register for updates and support.
Chapter 8 : MULTIMEDIA SKILLS

A multimedia project requires a team with diverse skills, known as the multimedia skillset. These teams consist of roles like project managers, designers, programmers, writers, and specialists in areas like video and audio. Each team member has specific responsibilities to ensure the project is successfully developed, such as project managers coordinating the team and designers creating visuals and interfaces.
Proposal for pos

This document provides a proposal from SRRK IT Limited for a point of sale (POS) system. It summarizes SRRK IT's capabilities in software and web development. The proposal describes features of the POS system like barcode scanning, credit card processing, and customizable interfaces. It highlights business benefits such as easier accounting and inventory management. The document outlines SRRK IT's software development process and provides examples of current clients. It emphasizes values like integrity, respect, justice, and responsibility. In closing, it provides contact information for SRRK IT.
Odoo vs sap

For your company's growth, choosing the correct ERP at the right moment becomes critical. The most appropriate ERP can have a direct impact on a company's success, profitability, and growth.
https://www.geminatecs.com/manufacturing-management-system
Multimedia System

A multimedia system is characterized by the digital integration of various media types like text, graphics, sound, images and video. It allows for interactivity and uses computer networks for distribution. Ensuring quality of service is important for multimedia over networks due to the time sensitivity and synchronization needs of media. Compression techniques like lossy and lossless are used to reduce multimedia file sizes.
Multimedia in Healthcare.pptx

This document discusses using multimedia technologies for healthcare applications. It proposes a system for remote markerless human gait tracking over wireless networks for medical diagnosis and prognosis. The system uses video content analysis techniques like background subtraction and contextual classification to extract the human gait region from video frames without needing specialized equipment. It then jointly optimizes video encoding and wireless transmission to prioritize sending the extracted human gait region while meeting quality of service requirements over bandwidth-limited wireless networks. Experimental results using H.264 video compression demonstrate the effectiveness of the proposed remote healthcare system for applications like telemedicine.
Multimedia color in image and video

Multimedia color in image and video seminar
Mustansiriya University
Department of Education
Computer Science
Bhim app

The document summarizes information about the BHIM app, which was launched in December 2016 by the National Payments Corporation of India to facilitate e-payments directly through banks and simplify cashless transactions. BHIM allows users to send and request money, scan and pay for purchases, and view transactions. It has over 16 million downloads and supports multiple Indian languages. The app provides a secure way to transact between bank accounts but has limitations like daily transaction limits and no dedicated customer support.
Network security ppt

network security is a complicated subject,historically only tackled by well-trained and expericenced experts
Multimedia

This document discusses graphics and multimedia technology. It covers various topics related to graphics including different types of images (raster/bitmap and vector), color, file formats, and methods for obtaining images. Specifically, it describes raster images as composed of pixels and matrices, while vector images use objects like lines and shapes. It also discusses color palettes, resolution, dithering, and scanning, digitizing, and capturing images using cameras, scanners, and software tools.
Multimedia:Multimedia compression 

This document discusses multimedia data compression. It explains that multimedia files like images, audio, and video take up significantly more storage space than text files. Data compression reduces the size of files by removing redundant data, saving storage space and allowing faster transfers. Compression is achieved through codecs, which are hardware or software that compresses and decompresses data. Compression can be lossless, allowing exact reconstruction of the original data, or lossy, which sacrifices some quality to achieve greater compression but does not allow exact reconstruction.
Multimedia Hardware

Presentation on hardware components of a typical Multimedia production system as per Industrial Technology Multimedia syllabus (NSW)
Multimedia Application Development

Multimedia refers to integrating various media types like text, graphics, audio, video digitally. Multimedia applications use a combination of media to deliver information interactively. Examples include websites, educational courseware, games. Multimedia development is the process of creating content combining different media types. It involves conceptualization, planning, production, and documentation phases. Various software are used to generate multimedia content for different applications in areas like advertising, education and entertainment.
Network security

1. Formulate a testing plan with the client to identify systems to evaluate and the scope of testing allowed.
2. Remotely or locally access the target systems to find vulnerabilities by simulating common attacks.
3. Report any found vulnerabilities to the client along with recommendations on how to remedy security issues.
rfid presentation

Here are the answers to your questions:
1. The main differences between RFID and barcodes are:
- RFID uses radio waves to transmit data while barcodes use optical scanning. RFID does not require line of sight.
- RFID tags can be read from a distance without physical contact while barcodes must be within the line of sight of a scanner.
- RFID tags can be read/written to multiple times while barcodes are read-only.
- RFID tags can store more information than barcodes.
2. Some practical applications of RFID include supply chain management, asset tracking, access control and authentication, livestock identification, toll collection on roads/bridges, library management systems, etc
Multimedia Development Lifecycle

Week 2 Lecturing
P420 - 1 CMLA
Multimedia Presentation for Public Relations
Swiss German University Indonesia
(13 September 2011)
Programming tools for developers

The document discusses various tools for programming in Python, HTML5, Java, and for rapid application development. For Python, it discusses IDEs like PyDev for Eclipse and PyCharm, as well as libraries and debugging tools part of the BeeWare toolbox. For HTML5, it discusses editors like Sublime Text, Atom, and Notepad++, and frameworks like Bootstrap and HTML5 Boilerplate. For Java, it discusses IDEs like NetBeans, Eclipse, and IntelliJ IDEA, as well as the rapid application development tool gvNIX.
Digital Locker Intro 

The document discusses the benefits of exercise for mental health. Regular physical activity can help reduce anxiety and depression and improve mood and cognitive functioning. Exercise causes chemical changes in the brain that may help boost feelings of calmness, happiness and focus.
Tendances (20)
Digitalization: A Challenge and An Opportunity for Banks

Digitalization: A Challenge and An Opportunity for Banks
En vedette
Conception et réalisation d’un système d’information pour l’automatisation du...

Conception et réalisation d’un système d’information pour l’automatisation du suivi des études d’audit géotechnique
RADIUS

RADIUS (Remote Authentication Dial In User Service) is a protocol that provides authentication, authorization and accounting functionality. It is commonly used for remote access to networks using modems or VPNs. The RADIUS protocol uses UDP and runs on ports 1812 and 1813. It operates on a client-server model where the client is typically a network access server and the server handles authentication requests from clients. RADIUS provides basic security through MD5 hashing of packets and a shared secret between clients and servers. However, it is vulnerable to sniffing and spoofing attacks.
Aide à la Planification Cellulaire dans un Réseau LTE (4G)

Les réseaux de télécommunications ont pris de plus en plus d'importance dans notre vie quotidienne. Pour satisfaire au mieux les besoins et les intérêts des clients, les opérateurs doivent pouvoir offrir, au meilleur prix, des services d'excellente qualité. C'est dans ce cadre que s'inscrit le problème de planification cellulaire des réseaux qui consiste à optimiser les coûts engendréspar l'installation et l'utilisation du système. Une planification bien effectuée a pour effet de réduire le temps de mise en marche, le coût des dépenses d'investissement ainsi que le coût des dépenses opérationnelles.
Le réseau mobile est aujourd'hui un domaine en pleine effervescence. Pendant la dernière décennie, les évolutions de télécommunications ont explosé une nouvelle gamme de service qui a écarté les services classiques afin de satisfaire l’augmentation du nombre des utilisateurs et les exigences de taux de données élevés.
Cette motivation laisse les générations mobiles se succéder et se développer, de la technologie GSM vers un système de paquets tout IP optimisé dénommé Long Term Evolution (LTE).
L’opérateur se trouve, devant ces technologies, obligé de répondre à la croissance continue du trafic, avec une faible latence, une meilleure fiabilité, et une meilleure efficacité spectrale par rapport aux précédentes générations. Ces exigences ont stimulé les évolutions des réseaux pour mettre aujourd’hui le premier pas vers la quatrième génération avec LTE.
A ce stade, l’opérateur doit réduire le coût d’investissement et augmenter la qualité de service pour assurer la rentabilité.
Pour le faire il doit passer par les phases primordiales : dimensionnement et planification de système radio mobile, qui consiste à déterminer l'ensemble des composantes matérielles et logicielles de ces systèmes, les positionner, les interconnecter et les utiliser de façon optimale, en respectant, entre autres, une série de contraintes de qualité de service.
De façon générale, le problème de planification fait intervenir plusieurs sous-problèmes avec chacun un niveau de complexité différent. Dans ce travail, le sous-problème qui est traité concerne l'affectation des cellules aux commutateurs. Ce problème consiste à déterminer un modèle d'affectation qui permet de minimiser le coût d'investissement des équipements du réseau 4G, tout en maximisant l'utilisation faite des équipements du réseau 3G déjà en place.
Ainsi, la solution proposée est un modèle qui décrit la marche à suivre lors de la planification initiale d’un réseau LTE qui se base sur la planification et le dimensionnement des zones de suivi ou Tracking Area.
Dans ce projet, nous allons donc effectuer une planification et un dimensionnement des zones Tracking Area.
Memoire de fin d'etude . marketing evenementiel : cas de la cellule de commun...

Ferhane Fethi. Marketing Evenementiel : Du festif au strategique . Memoire de licence en sciences commerciales option marketing . Université d'Oran- Algérie . 2008
Ppt memoire de fin d'étude Marketing de contenu Master 1

L’époque du produit roi est belle et bien terminée, désormais, c’est le client qui doit
requérir toute notre attention. L’acquisition coûte cher : nous devons donc, à chaque étape
de notre réflexion de marketing online, réfléchir à ses besoins et à ses attentes en fonction
de sa situation dans le processus de décision d’achat, pour mieux l’attirer vers notre produit
et le convertir d’un client potentiel au client acheteur.
L’évolution d’internet a permis la création de nouveaux outils, notamment les réseaux
sociaux, pour les entreprises pour élargir leur clientèle cible.
Afin de ne pas faire uniquement une analyse sur les réseaux sociaux
« webmarketing », nous allons porter notre étude sur l’application du marketing de
contenu au sein des entreprises. Ce contenu qui permettra la création du trafic, la
fidélisation des cibles et aussi la conversion des leads en clients. Un contenu riche aura
donc pour mission de servir leur intérêt et de les aider à progresser dans leur parcours de
décision d’achat.
La thématique de ce mémoire permet de voir non seulement ce qui a déjà été fait par les
entreprises par rapport aux réseaux sociaux, mais aussi saisir des opportunités en élaborant
une stratégie marketing de contenu de valeur.
Présentation mageco

Pour finir mes études de mastère professionnel en Ingénierie des Systèmes d’Information à la Faculté des Sciences de Monastir. J’ai effectué un stage de 5 mois dans une société Tuniso-Belge situé à Monastir.
Ils m’ont confié le sujet suivant :
Conception et Développement d’une plateforme Mobile d’assistance et de planification pour les agents commerciaux (Mageco).
MOOC ANALYSE FINANCIERE 1_SESSION LIVE #1

Support de la session LIVE#1 du MOOC Analyse financière 2 organisé par le FIRST FINANCE INSTITUTE
Présentation Projet de fin d'études

Mise en place d'une plateforme SAP BI autour de SAP MM :
- Définition des processus métier logistique autour de SAP MM
- Définition des tableaux de bords pour la mesure de performance et contrôle
- Définition des cubes MM dans SAP BI pour l'élaboration des tableaux de bords et KPI
- Réalisation des requetes
- Réalisation des tableaux de bords et KPI
- Dataquality (données BI et données système source SAP)
- Mesure de l'éfficacité des résultats (tableaux de bords et KPI)
- Mise en production
contact :Salaheddine.bentalba@gmail.com
La blockchain pour les nuls - Petit déjeuner OCTO Technology & d'Alverny

Cette présentation a réalisée le 08/12/2016 lors d'un petit-déjeuner organisé par le cabinet d'avocat d'Alverny sur le thème "La blockchain pour les nuls - Décryptage d'une technologie".
Cet événement aura été l'occasion de présenter des insights importants pour bien comprendre les enjeux et le mode de fonctionnement de la blockchain (Bitcoin et Ethereum principalement).
En vedette (20)
Conception et réalisation d’un système d’information pour l’automatisation du...

Conception et réalisation d’un système d’information pour l’automatisation du...
Aide à la Planification Cellulaire dans un Réseau LTE (4G)

Aide à la Planification Cellulaire dans un Réseau LTE (4G)
Réalisation d’un système d’information pour la gestion automatique des ventes...

Réalisation d’un système d’information pour la gestion automatique des ventes...
Memoire de fin d'etude . marketing evenementiel : cas de la cellule de commun...

Memoire de fin d'etude . marketing evenementiel : cas de la cellule de commun...
Ppt memoire de fin d'étude Marketing de contenu Master 1

Ppt memoire de fin d'étude Marketing de contenu Master 1
La blockchain pour les nuls - Petit déjeuner OCTO Technology & d'Alverny

La blockchain pour les nuls - Petit déjeuner OCTO Technology & d'Alverny
Similaire à Mastère Professionnelle 2015
Présentation SOPHOS EVENEMENT Le Datacenter "Next-Generation" - NUTANIX - ACR...

Comment Acropolis et Sophos sécurisent votre Cloud ?
Présentation de Ludovic Peny, Sales Engineer, Sophos.
Introduction to NI, LabVIEW, ELVIS and Planet NI

Presentation by Serges Lemo at the Ecole National Superieure Polytechnique de Yaounde during a seminar on Virtual Instrumentation.
This presentation introduces National Instruments, LabVIEW and NI ELVIS assuming no prior knowledge.
This presentation also introduces the Planet NI initiative, its goals and how it can help those developing countries.
Périphériques non-Windows et SCCM – Intégrations et management

Scénarios de prise en charge des périphériques non Windows dans SCCM grâce au SP1 et à l’intégration d’inTune.
App211 techdays 2013 Windows 8 concevoir des applications efficaces et perfor...

Présentation lors des Techdays à Paris au Palais des congrès les 12,13 et 14 Février 2013.
Chap XIII : calcul scientifique avec python

Les mathématiques appliquées et le calcul scientifique jouent un rôle croissant comme outils non évitables pour l’élaboration de recherches scientifiques et dans la conception de processus industriels. Le calcul scientifique reste pour toujours l’étape première de la voie du développement culturel et technique d’un pays donné.
Par ailleurs, le niveau de complexité des systèmes, généralement manipulés par les êtres humains que nous sommes, est très élevé à un niveau où toute avancée intellectuelle engendrera des retombés au niveau industriel tant que tous les processus de l’économie en dépendent.
En contre partie, la majorité des produits technologiques sont juste la solution immédiate de bon nombre de résolutions de requête de la vie courante. L'avènement de l'informatique et de ses produits, les langages de programmation de tout bord, de l'Internet et des télécommunications, à chacun ses infrastructures et ses protocoles, a révolutionné les méthodologies de travail des équipes et laboratoires de recherches. Les langages de développement informatique des outils et suites logiciels sont d’un grand secours aux travaux de modélisation et de simulation des processus.
Les mathématiques appliquées et l'informatique sont les moyens de conception (Modélisation et Simulation), plus encore, ils sont les vecteurs qui ont provoqué une amélioration nette dans les pratiques de tous les jours et aussi dans la vitesse de mise en œuvre de moyens exploitables.
Les langage de programmation, comme le C/C++, le FORTRAN ou le Python ont joué un grand rôle dans le cours de développement de beaucoup de procédés (Modélisation) et ont facilité la compréhension de beaucoup phénomènes (Simulation).
Rapport home handicap

c'est un système de commande vocale dédié aux personnes handicapés afin de les aider a bien contrôler leur maison sans avoir besoin de quelqu'un.
Plus près, plus près… NFC et la communication à proximité dans Windows 8 et W...

Les scénarios permis par le NFC et la communication à proximité en général sont extrêmement variés, de la lecture/écriture de tags à la communication entre terminaux. Windows Phone 8 et Windows 8 disposant de contrôleurs NFC et Bluetooth, ouvrent la porte de ces nouveaux scénarios aux développeurs. Et si maintenant on commençait à jouer un peu avec ? Nous vous présenterons comment tirer parti de ces nouvelles API dans vos applications.
Mise en place d’un laboratoire de sécurité « Scénarios d’Attaques et Détectio...

De nos jours l’internet est devenue une source d’informations (business, réseaux sociaux…), avec des systèmes d’informations qui sont de plus en plus ouverts sur Internet. Ceux-ci présentent quelques failles de sécurité dont la mise en place des mesures sécuritaires devient une condition nécessaire, mais pas suffisante pour se protéger des risques présents sur la toile internet.
Comment interconnecter des réseaux ?
Comment permettre à des réseaux d’échanger des informations et limiter les risques liés à ces échanges ?
Nous avons mis en place un laboratoire de sécurité qui permet de faire des tests et détections d’intrusions. Le travail sait fait en deux parties.
D’abord la mise en place du laboratoire ensuite l’interconnexion avec des sites distants.
Matinée6 solutions professionnelles de sécurité KES

Matinée d'échanges avec les entreprises de la RDC autour du thème de la sécurité informatique en partenariat avec Kaspersky Lab.
Support formation vidéo : Préparez votre certification Sophos UTM v9.5 Engine...

Découvrez et maîtrisez la solution UTM de Sophos et préparez-vous à la certification Sophos Engineer et Architect.
Cette formation vise à vous permettre de :
- Connaitre la gamme de produits de Sophos
- Comprendre le fonctionnement de Sophos UTM
- Comprendre les différents modes de déploiement
- Préparer le terrain pour déployer Sophos UTM
- Configurer et paramétrer les différents modules de sécurité
- Découvrir les nouveautés de la version 9.5
- Administrer la solution
- Préparation à la certification Sophos Engineer et Architect
Suivez la formation vidéo complète par ici :
https://www.smartnskilled.com/tutoriel/formation-en-ligne-preparez-votre-certification-sophos-utm-v9-5-engineer-et-architect
Conception applications 3 écrans sur Windows 8/WP8/Xbox 360

Le nombre de type de périphérique se multipliant, vous êtes amené à développer votre application plusieurs fois. Utilisez cet écosystème pour ajouter des fonctionnalités à vos applications. Cette session présente la réalisation d’un prototype d’application video multi écran Xbox / Windows 8 / Windows Phone 8 utilisant Player Framework.
Similaire à Mastère Professionnelle 2015 (20)
Présentation SOPHOS EVENEMENT Le Datacenter "Next-Generation" - NUTANIX - ACR...

Présentation SOPHOS EVENEMENT Le Datacenter "Next-Generation" - NUTANIX - ACR...
Périphériques non-Windows et SCCM – Intégrations et management

Périphériques non-Windows et SCCM – Intégrations et management
App211 techdays 2013 Windows 8 concevoir des applications efficaces et perfor...

App211 techdays 2013 Windows 8 concevoir des applications efficaces et perfor...
Etude des aspects de sécurité Android & Audit d'une application Android

Etude des aspects de sécurité Android & Audit d'une application Android
Plus près, plus près… NFC et la communication à proximité dans Windows 8 et W...

Plus près, plus près… NFC et la communication à proximité dans Windows 8 et W...
Mise en place d’un laboratoire de sécurité « Scénarios d’Attaques et Détectio...

Mise en place d’un laboratoire de sécurité « Scénarios d’Attaques et Détectio...
Matinée6 solutions professionnelles de sécurité KES

Matinée6 solutions professionnelles de sécurité KES
Aiuc formation-installation-et-administration-de-cisco-unity-connection

Aiuc formation-installation-et-administration-de-cisco-unity-connection
Cy9808 formation-les-fondamentaux-de-la-securite-informatique

Cy9808 formation-les-fondamentaux-de-la-securite-informatique
Support formation vidéo : Préparez votre certification Sophos UTM v9.5 Engine...

Support formation vidéo : Préparez votre certification Sophos UTM v9.5 Engine...
Conception applications 3 écrans sur Windows 8/WP8/Xbox 360

Conception applications 3 écrans sur Windows 8/WP8/Xbox 360
Plus de Rawdha MABROUKI
Rawdha mabrouki cv - english

This document is a resume for Rawdha MABROUKI summarizing her education, skills, experience and projects as a Microsoft Dynamics Ax Software Engineer. She has a degree in computer engineering and a professional master's in computer science. Her skills include Power BI, SSRS reporting, and customizing modules in Dynamics Ax. She has worked on projects customizing Ax, developing reports, and creating applications for various clients.
Steps for creating a report

This document outlines the steps to create an SSRS report for Ax including: 1) identifying fields, 2) creating a temporary table, 3) creating classes, 4) adding parameters, 5) building the project, and 6) deploying the report to SQL Server Reporting Services and adding an output menu item.
Conception et développement de la gestion de visa sous Dynamics Ax R2

gestion des dossiers de Visa des employés
Plus de Rawdha MABROUKI (6)
Conception et développement de la gestion de visa sous Dynamics Ax R2

Conception et développement de la gestion de visa sous Dynamics Ax R2
Dernier
Comment aborder le changement climatique dans son métier, volet adaptation

Comment aborder le changement climatique dans son métier, volet adaptationInstitut de l'Elevage - Idele
Manon Bourasseau, animatrice caprine CIVAM Haut Bocage
Romain Lesne, conseiller caprin ARDEPAL
Caroline Sauvageot, IDELEAlternative - Complément au Tramway et 3ème lien de la ville de Québec 

An update of this presentation has been done with Slide 16 that has been updated and 17 has been added, only.
Cette présentation a été ajournée avec la diapo 16 qui a été modifié et la 17 qui a été ajouté.
Voir ici
https://www.slideshare.net/slideshow/alternative-au-tramway-de-la-ville-de-quebec-rev1-sum-pdf/269691794
CDPQ Infra dévoile un plan de mobilité de 15 G$ sur 15 ans pour la région de Québec. Une alternative plus économique et rapide, ne serait-elle pas posssible?
- Valoriser les infrastructures ferroviaires du CN, en créant un Réseau Express Métropolitain (REM) plutôt qu'un nouveau tramway ou une combinaison des 2.
- Optimiser l'utilisation des rails pour un transport combiné des marchandises et des personnes, en accordant une priorité aux déplacements des personnes aux heures de pointes.
- Intégrer un téléphérique transrives comme 3ème lien urbain dédiés aux piétons et cyclistes avec correspondance avec le REM.
- Le 3 ème lien routier est repensé en intégrant un tunnel routier qui se prolonge avec le nouveau pont de l'Île d'Orléans et quelques réaménagemet de ses chausées.
https://www.linkedin.com/in/bedarddaniel/
English:
CDPQ Infra unveils a $15 billion, 15-year mobility plan for the Quebec region. Wouldn't a more economical and faster alternative be possible?
Leverage CN's railway infrastructure by creating a Metropolitan Express Network (REM) instead of a new tramway or a combination of both.
Optimize the use of rails for combined freight and passenger transport, giving priority to passenger travel during peak hours.
Integrate a cross-river cable car as a third urban link dedicated to pedestrians and cyclists, with connections to the REM.
Rethink the third road link by integrating a road tunnel that extends with the new Île d'Orléans bridge and some reconfiguration of its lanes.
https://www.linkedin.com/in/bedarddaniel/
1er webinaire INOSYS Réseaux d’élevage Ovins Viande

Présenté par Vincent BELLET, Marie MIQUEL, Gilles SAGET et Maxime MAROIS - IDELE
Quelles rotations dans les systèmes caprins de Nouvelle-Aquitaine et Pays de ...

Quelles rotations dans les systèmes caprins de Nouvelle-Aquitaine et Pays de ...Institut de l'Elevage - Idele
Jérémie Jost (Idele-REDCap), Sébastien Minette (CRA NA), Manon Proust (Innoval), Théophane Soulard (Seenovia), et les conseillers/animateurs REDCapDernier (7)
Comment aborder le changement climatique dans son métier, volet adaptation

Comment aborder le changement climatique dans son métier, volet adaptation
Alternative - Complément au Tramway et 3ème lien de la ville de Québec 

Alternative - Complément au Tramway et 3ème lien de la ville de Québec
1er webinaire INOSYS Réseaux d’élevage Ovins Viande

1er webinaire INOSYS Réseaux d’élevage Ovins Viande
Quelles rotations dans les systèmes caprins de Nouvelle-Aquitaine et Pays de ...

Quelles rotations dans les systèmes caprins de Nouvelle-Aquitaine et Pays de ...
COURS ANALYSE FINANCIERE-NOGLO Méthodes d’analyses financières.pdf

COURS ANALYSE FINANCIERE-NOGLO Méthodes d’analyses financières.pdf
Mastère Professionnelle 2015
- 1. Authentification Biométrique par le biais du Signal Parole et de l’Iris Encadré par : Madame Azza WLED ZAIED Présenté par : Raoudha MABROUKI Année universitaire 2014-2015 Présenté en vue de l’obtention de Diplôme National du Mastère Professionnel en Sciences et Technologies Spécialité : Informatique Option : Sécurité des Systèmes Informatiques Communicants et Embarqués Par Institut Supérieur d’Informatique Soutenance de Mémoire de Mastère
- 2. Plan Introduction Sécurité des Systèmes Informatiques Biométrie Conception et Réalisation Interfaces utilisateur Conclusion et Perspectives 2
- 3. • Sécurité des systèmes d’information est l’ensemble des moyens techniques organisationnels, juridiques et humains; • But : conserver, rétablir, et garantir la sécurité du système informatique, • Apparition des ordinateurs => la création des systèmes biométriques informatisés, • caractéristique physique unique => la diversité des systèmes biométriques. 3 Introduction
- 4. Sécurité des systèmes informatiques (1/3) Prévention Détection des actions non autorisées Réaction 4
- 5. Interruption Interception Modification Fabrication 5 Risques de sécurité Sécurité des systèmes informatiques (2/3)
- 6. Niveau d’accès physiques Niveau d’accès logique Niveau réseau de transmission 6 Contrôle d’accès Sécurité des systèmes informatiques (3/3)
- 7. Biométrie (1/4) Copie vol oublie perte Mot de passe X - X - Badge - X X X Empreinte - - - - Supprimer Duplication Vol Oubli Perte Authentification Biométrique 7
- 8. Biométrie (2/4) Analyses biologiques • Odeur • Sang • Salive • Urine • ADN, cheveux... Analyses comportementales • Dynamique de la signature • Dynamique de frappe à la clavier • Voix • Manière de marcher Analyses morphologiques • Empreintes digitales, • Forme de la main, • Traits du visage, • IRIS • veineux de l'œil 8
- 10. Biométrie (4/4) 10 Caractéristiques du système
- 12. Méthodologie adoptée 12 Conception et Réalisation (1/10)
- 13. 13 Conception et Réalisation (3/10)
- 14. Architecture du système Biométrique 14 Conception et Réalisation (2/10)
- 15. •Authentification indépendante du Texte, •Utilisation des caractéristiques uniques, •Nombreux traits discriminants. 15 Système biométrique : Voix Conception et Réalisation (4/10)
- 16. 16 L’appareil phonatoire Le générateur : air expulsé des poumons, traverse l’appareil phonatoire comme un instrument à vent et crée la pression nécessaire à la génération d’un signal acoustique. Le vibrateur : L’air expulsé des poumons traverse la trachée pour arriver dans le larynx où se trouve les cordes vocales. L’air traversant le larynx met en vibration les cordes vocales. La fréquence de vibration des cordes vocales est modulée en fonction de leur degré de contraction. Conception et Réalisation (5/10)
- 17. 17 Le résonateur : Ces vibrations sont modifiées par le passage de l’air dans les différentes cavités qui composent le pharynx mais aussi dans les fosses nasales. Ces résonateurs influent sur le son en atténuant certaines fréquences et en amplifiant d’autres. La forme et le volume de ces cavités, spécifiques au locuteur, modifient fortement le son produit. Les modulateurs : les organes modulateurs que sont la langue, les lèvres et la mâchoire sculptent, elles produisent les phonèmes qui composent la parole. La position de ces différents organes est le mécanisme final qui permet la production de parole articulée. Certains organes impliqués dans la production de la parole se trouvent en partie visibles extérieur (lèvres, langue, position des mâchoires). L’appareil phonatoire Conception et Réalisation (6/10)
- 18. 18 Organigramme d'authentification par le biais de la voix Conception et Réalisation (7/10)
- 19. 19 Détection de l'iris Conception et Réalisation (8/10)
- 20. Organigramme d’authentification par le biais de l’iris 18 Conception et Réalisation (9/10)
- 21. Environnement Informatique Utilisé MATLAB (« matrix laboratory ») • Langage de programmation • Manipuler des matrices • Afficher des courbes et des données • Mettre en œuvre des algorithmes • Créer des interfaces utilisateurs 21 SmartDraw • Création de schémas, organigrammes de programmation • Base donnée remplie de plusieurs modèles prédéfinies, • Langage de modélisation UML et BANTAM . Conception et Réalisation (10/10)
- 22. Interface : Choix de méthode d’authentification . 22
- 25. Interface : supprimer enregistrement . 25
- 27. Conclusion & Perspectives ● Conception et réalisation d'un système de sécurité biométrique basé sur le signal parole ( monodimensionnel) et l'iris ( bidimensionnel), ● En perspective : ● Mise en place d’un système multi-agent pour le système d'authentification par signal parole, ● Utilisation de la plate forme LabView pour le traitement d'images en temps réel pour le système d'authentification par l'iris. 27
- 28. Merci de votre attention
